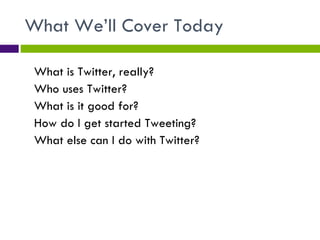
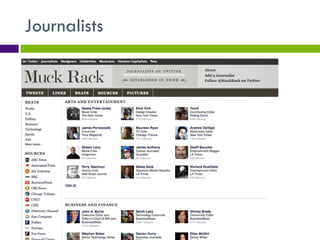
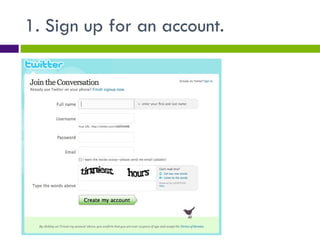
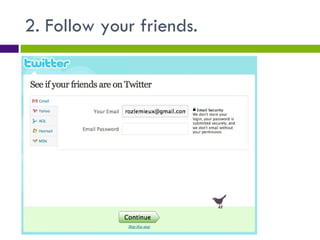
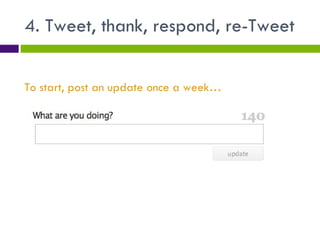
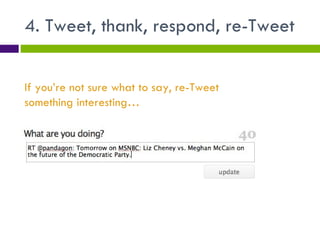
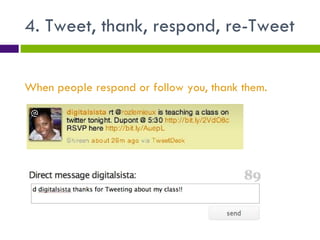
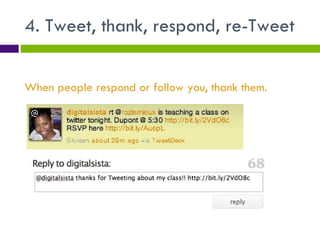
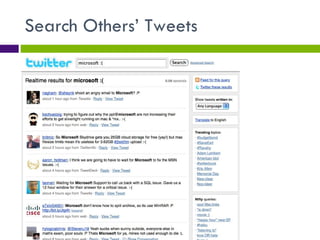
Twitter is a social media platform that allows users to post short messages called tweets. It has grown rapidly in recent years and is used by journalists, politicians, celebrities, advocates and ordinary people to share information and stay connected. The document provides an introduction to Twitter and advice on how to get started, including signing up for an account, following others, downloading apps, posting regular tweets, responding to others, and using search and analytics tools.