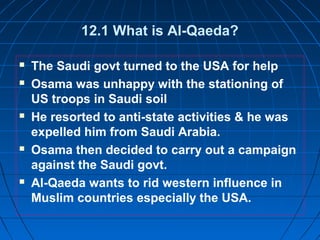
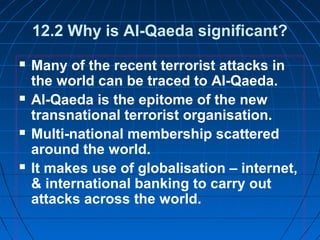
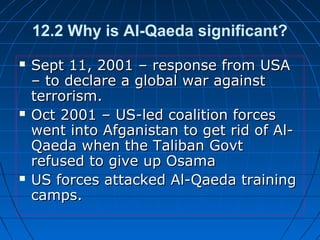
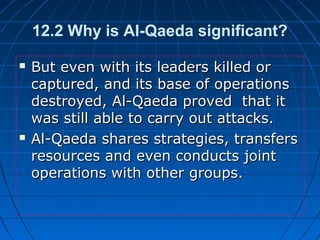
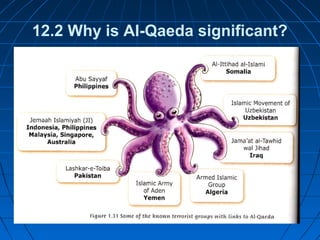
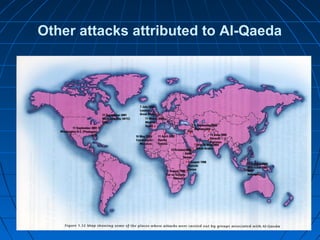
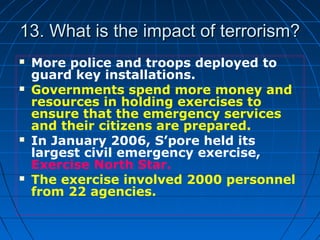
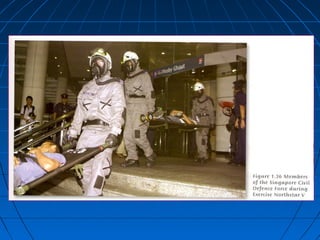
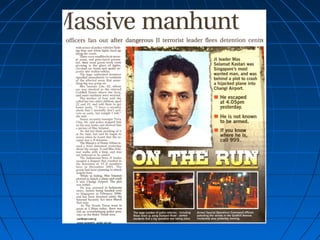
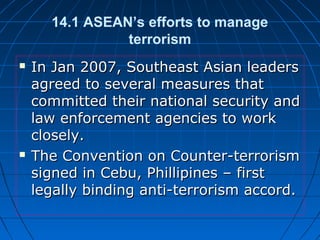
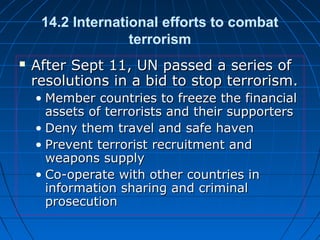
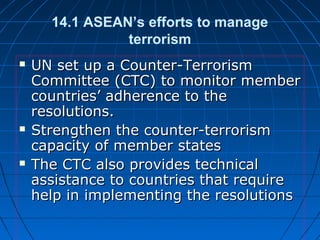
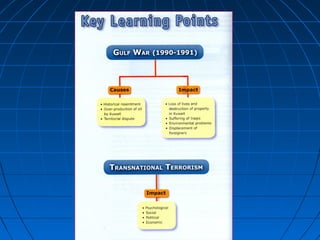
Transnational terrorism involves unlawful violence by internationally linked groups across multiple countries. It poses a significant threat as groups like Al-Qaeda have global networks and ideologies. Countries and organizations like ASEAN and the UN have implemented measures to enhance cooperation against terrorism such as intelligence sharing. However, transnational terrorism remains a challenge to manage fully due to terrorists' ability to evade capture and recruit new members by spreading their ideologies online. Both governmental and societal efforts are needed to contain transnational terrorist threats.