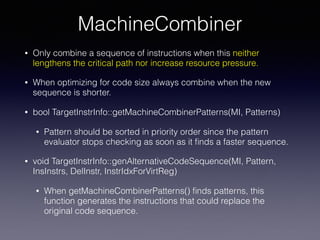
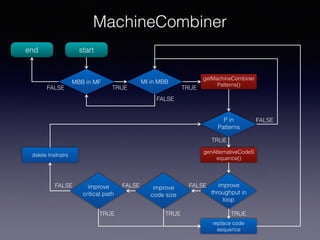
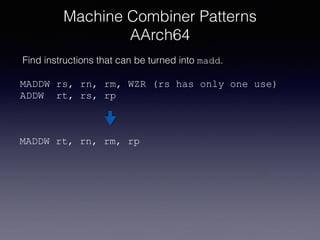
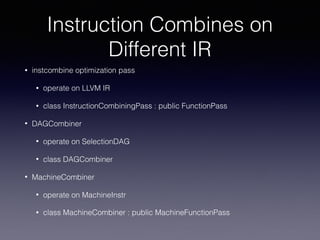
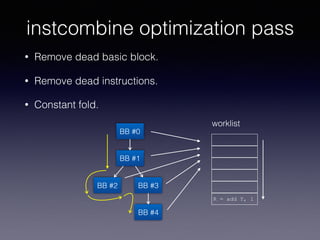
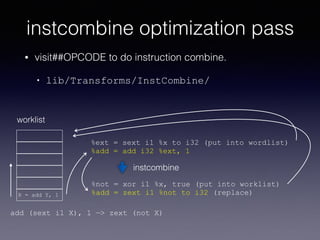
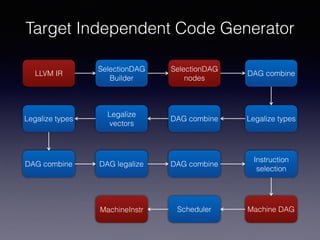
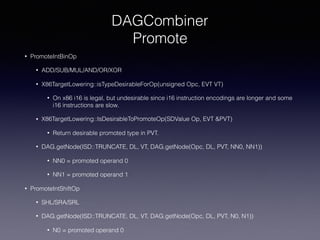
The document outlines the LLVM instruction combining process, focusing on various optimization passes including instcombine, dagcombiner, and machinecombiner. It details strategies for combining instructions to improve performance, such as removing dead code, constant folding, and optimizing for critical paths in different architectures. Additionally, it discusses specific transformations and rules that enable target-independent and dependent combining of instructions to achieve efficient code generation.





![2014-08-07 Gerolf Hoflehner
e4fa341 MachineCombiner Pass for selecting faster instruction
sequence on AArch64
2015-06-10 Sanjay Patel
c826b54 [x86] Add a reassociation optimization to increase ILP
via the MachineCombiner pass
2015-07-15 Hal Finkel
8913d18 [PowerPC] Use the MachineCombiner to reassociate fadd/
fmul
2015-09-21 15:09 Chad Rosier
c5d4530 [Machine Combiner] Refactor machine reassociation code
to be target-independent.
MachineCombiner](https://image.slidesharecdn.com/instructioncombineinllvm-171220043732/85/Instruction-Combine-in-LLVM-12-320.jpg)