IEEE PROJECTS 2013 for me
•
1 like•941 views
JAVA IEEE 2013 - 2014 IEEE PROJECT TITLES FOR STUDENTS B.E.,B.TECH.,M.E,M.TECH.,M.PHIL.,M.S.,MCA,M.S.,MBA AND DIPLOMA PROJECTS USING JAVA
Report
Share
Report
Share
Download to read offline
Recommended
final year ieee projects in pondicherry 2013

This document lists 58 projects related to various topics including cloud computing, data engineering, secure computing, networking, parallel and distributed systems, mobile computing, image processing, and multimedia. The projects focus on developing techniques for privacy preservation, access control, performance optimization, security, and efficient data retrieval and sharing in distributed cloud and mobile environments.
Java project 2013

IEEE PROJECTS IN CHENNAI FOR FINAL YEAR PROJECTS @ XLNC INFOTECH 9941958222— Chennai
XLNC INFOTECH IS THE BEST PROJECT CENTRES IN CHENNAI WHICH DEALS WITH THE FOLLOWING PROJECTS FOR FINAL YEAR ENGINEERING AND SCIENCE STUDENTS
*IEEE PROJECTS
*M.E PROJECTS IN ALL THE DOMAINS
*SOFTWARE ENGINEERING PROJECTS
*MATLAB BASED PROJECTS
*NS2 BASED PROJECTS
*EMBEDDED PROJECTS
*CLOUD COMPUTING PROJECTS
REAL TIME PROJECT TRAINING/FINAL YEAR ENGINEERING PROJECTS
(CSE, IT,ECE,EEE-BE/ME/MCA/MPHIL/MSC/B.SC)
We develop each and every project with our professionals. We don’t buy the projects from anybody. You can give your own ideas in developing your project.
We assist and deliver the following:-
1.Our real time project center supports with the projects that are based on the recommendations and standards of IEEE for the year 2013-2014.
2. Being the best project center in Chennai, we provide the complete documentation for M.E Projects even.
3. Each student will be guided, mentored, trained in their academic projects separately by our IT Professionals.
4. Each student will be trained in the architecture,design,development and execution of their IEEE projects.
5. Each student will be guided with tips for the project execution, VIVA and presentation
IEEE PROJECTS IN JAVA & DOTNET 2013-2014 TITLES

This document contains 166 titles for Java and .NET software projects related to various topics including cloud computing, image processing, data mining, parallel and distributed systems, dependable and secure computing, and mobile computing. It provides contact information for Temasolution, a company that can provide more details on these projects. Interested parties are instructed to send requests to info@temasolution.com or visit the listed website or email.
CREC List.docx

The document lists 57 paper titles related to various topics including cloud computing, networking, data mining, and security. The papers cover a range of technologies and approaches including decentralized service discovery, clustering algorithms, key pre-distribution schemes, load balancing models, anomaly detection, encryption, privacy preservation, and intrusion detection.
Low cost Java IEEE Projects 2013

This document lists over 40 potential 2013 IEEE Java Dotnet project titles across various domains including wireless networks, mobile computing, network security, data mining, cloud computing, parallel and distributed computing, and multimedia/image processing. The projects focus on technical topics such as wireless sensor networks, wireless mesh networks, cognitive radio networks, mobile ad hoc networks, network coding, video streaming, machine learning, data warehousing, and more. Project deliverables include an abstract, IEEE paper, presentation, report, working prototype or proof of concept, and certification. Bulk older and new projects can be provided at a low cost.
Ieee 2014 2014 java project titles

The document lists potential 2014-2015 Java project titles from the IEEE across several domains: Big Data, Cloud Computing, Data Mining, Secure Computing, Networking, Parallel & Distributed Systems, Mobile Computing, and Cloudsim. The projects focus on topics like big data analysis, cloud security and scalability, data mining techniques, privacy and anonymity in networks and databases, mobile and distributed systems, and simulating cloud infrastructure.
Shakas project titles 2014 2015

Shakas Technologies provides IEEE,NON-IEEE projects and Application projects are available. contact:9500218218
IEEE 2010 JAVA, .NET & EMBEDDED SYSTEM TITLES

Dear All, Future-tec technologies Pvt Ltd,
Offers IEEE & Non IEEE projects on all Platforms and Domains. We also support with your own titles.
Regards,
ASHA DAS.P.K
Mob:9566216611
www.future-tec.co.in
Old 52,New 62,Floor 3,Espee Complex
Brindavan Street,West Mambalam,Chennai 33
Recommended
final year ieee projects in pondicherry 2013

This document lists 58 projects related to various topics including cloud computing, data engineering, secure computing, networking, parallel and distributed systems, mobile computing, image processing, and multimedia. The projects focus on developing techniques for privacy preservation, access control, performance optimization, security, and efficient data retrieval and sharing in distributed cloud and mobile environments.
Java project 2013

IEEE PROJECTS IN CHENNAI FOR FINAL YEAR PROJECTS @ XLNC INFOTECH 9941958222— Chennai
XLNC INFOTECH IS THE BEST PROJECT CENTRES IN CHENNAI WHICH DEALS WITH THE FOLLOWING PROJECTS FOR FINAL YEAR ENGINEERING AND SCIENCE STUDENTS
*IEEE PROJECTS
*M.E PROJECTS IN ALL THE DOMAINS
*SOFTWARE ENGINEERING PROJECTS
*MATLAB BASED PROJECTS
*NS2 BASED PROJECTS
*EMBEDDED PROJECTS
*CLOUD COMPUTING PROJECTS
REAL TIME PROJECT TRAINING/FINAL YEAR ENGINEERING PROJECTS
(CSE, IT,ECE,EEE-BE/ME/MCA/MPHIL/MSC/B.SC)
We develop each and every project with our professionals. We don’t buy the projects from anybody. You can give your own ideas in developing your project.
We assist and deliver the following:-
1.Our real time project center supports with the projects that are based on the recommendations and standards of IEEE for the year 2013-2014.
2. Being the best project center in Chennai, we provide the complete documentation for M.E Projects even.
3. Each student will be guided, mentored, trained in their academic projects separately by our IT Professionals.
4. Each student will be trained in the architecture,design,development and execution of their IEEE projects.
5. Each student will be guided with tips for the project execution, VIVA and presentation
IEEE PROJECTS IN JAVA & DOTNET 2013-2014 TITLES

This document contains 166 titles for Java and .NET software projects related to various topics including cloud computing, image processing, data mining, parallel and distributed systems, dependable and secure computing, and mobile computing. It provides contact information for Temasolution, a company that can provide more details on these projects. Interested parties are instructed to send requests to info@temasolution.com or visit the listed website or email.
CREC List.docx

The document lists 57 paper titles related to various topics including cloud computing, networking, data mining, and security. The papers cover a range of technologies and approaches including decentralized service discovery, clustering algorithms, key pre-distribution schemes, load balancing models, anomaly detection, encryption, privacy preservation, and intrusion detection.
Low cost Java IEEE Projects 2013

This document lists over 40 potential 2013 IEEE Java Dotnet project titles across various domains including wireless networks, mobile computing, network security, data mining, cloud computing, parallel and distributed computing, and multimedia/image processing. The projects focus on technical topics such as wireless sensor networks, wireless mesh networks, cognitive radio networks, mobile ad hoc networks, network coding, video streaming, machine learning, data warehousing, and more. Project deliverables include an abstract, IEEE paper, presentation, report, working prototype or proof of concept, and certification. Bulk older and new projects can be provided at a low cost.
Ieee 2014 2014 java project titles

The document lists potential 2014-2015 Java project titles from the IEEE across several domains: Big Data, Cloud Computing, Data Mining, Secure Computing, Networking, Parallel & Distributed Systems, Mobile Computing, and Cloudsim. The projects focus on topics like big data analysis, cloud security and scalability, data mining techniques, privacy and anonymity in networks and databases, mobile and distributed systems, and simulating cloud infrastructure.
Shakas project titles 2014 2015

Shakas Technologies provides IEEE,NON-IEEE projects and Application projects are available. contact:9500218218
IEEE 2010 JAVA, .NET & EMBEDDED SYSTEM TITLES

Dear All, Future-tec technologies Pvt Ltd,
Offers IEEE & Non IEEE projects on all Platforms and Domains. We also support with your own titles.
Regards,
ASHA DAS.P.K
Mob:9566216611
www.future-tec.co.in
Old 52,New 62,Floor 3,Espee Complex
Brindavan Street,West Mambalam,Chennai 33
Projecttitles 2013

The document lists research projects in various areas including cloud computing, grid computing, image processing, networking, network security, data mining, software engineering, and mobile computing. For cloud computing, projects involve secure erasure coding, access control, and keyword search. Grid computing projects focus on meeting deadlines, detecting firewall anomalies, and location-based routing. Image processing areas are action recognition, blurry image classification. Networking research includes resource allocation and media streaming. Network security work centers on intrusion detection, authentication, storage reliability, and data provenance. Data mining projects look at fault tolerance, moving object analysis, and privacy-preserving classification. Software engineering examines component reconfiguration and requirements elicitation. Mobile computing focuses on traffic
Ieee 2014 java projects list 

Final year M.E IEEE PROJECTS TITLES 2014-2015 Final year IEEE PROJECTS TITLES 2014-2015 Final year M.TECH IEEE PROJECTS TITLES 2014-2015 Final year B.E IEEE
Novel secure communication protocol basepaper

This document proposes a secure communication protocol (SCP) for ad hoc networks using clustering techniques and Kerberos authentication. Key points:
M = {Nid, Knch, CHid}
- The network is divided into clusters, each with a cluster head (CH) node responsible for authentication.
Is encrypted by using public key of new node
Kun and send to new node. The new node
decrypts the message and stores Nid, Knch, CHid
information. Now the new node is authenticated
node of that cluster. The CH updates its
database with new node information.
- CHs use Kerberos authentication to generate IDs and passwords for nodes to authenticate each
2013-2014 IEEE Projects & Application Projects

B.E, B.TECH, M.TECH, M.E, MS, BSC, MSC, BCA, MCA, MBA, BBA, PHD, B.E (ECE, CSE, IT) B.TECH (ECE, CSE, IT) M.TECH (COMPUTER SCIENCE, SOFTWARE ENGINEERING, M.E (COMMUNICATION SYSTEMS, COMPUTER SCIENCE, SOFTWARE ENGINEERING) DIPLOMA (CSE, IT)
2013 2014 ieee projects titles

Typical Soft Technologies is one of the leading Software Company located in Chennai that offers best Quality projects and training to all customers.
We also deliver all the finest Projects at many Students, Companies. Our Computer Courses Provides best future for the Students. If you want any of our projects & Courses, then contact us.
Admin@typical.in
044-43555140, 093443 99926.
Original titles

The document discusses several topics related to image processing, data mining, mobile computing, and Android projects. Specifically, it lists 35 papers related to image processing techniques, data mining algorithms, protocols and optimizations for mobile and wireless networks, and Android-based applications and frameworks. The papers cover areas such as object detection, hyperspectral imaging, texture analysis, dictionary learning techniques for image processing tasks. Data mining papers discuss topics like query construction, recommendation diversity, pattern mining, and clustering algorithms. Mobile computing papers focus on medium access, opportunistic networking, localization, and traffic optimization. The Android projects propose solutions for security, context-aware policies, push notifications, gesture recognition, guides and more.
Ieee 2013 dot net projects list

Final year M.E IEEE PROJECTS TITLES 2014-2015 Final year IEEE PROJECTS TITLES 2014-2015 Final year M.TECH IEEE PROJECTS TITLES 2014-2015 Final year B.E IEEE
2013-2014 IEEE Projects titles

Typical Soft Technologies is one of the leading Software Company located in Chennai that offers best Quality projects and training to all customers.
We also deliver all the finest Projects at many Students, Companies. Our Computer Courses Provides best future for the Students. If you want any of our projects & Courses, then contact us.
Mail : admin@typical.in
044-43555140, 093443 99918 / 26.
Low cost Java 2013 IEEE projects

Bulk Projects For sale
IEEE 2009-10-11-12-13 PAPERS AVILABLE.
We are providing low cost project for final year student projects.
Solved 2010 -2011 -2012 - 2013 IEEE in all the domain
Mobile : 8940956123
E-Mail : ambitlick@gmail.com,
INNOVATIVE TITLES ARE ALSO WELLCOME TO DO WITH US
For All BE/BTech, ME/MTech, MSC/MCA/MS , and diplamo graduates
PROJECT SUPPORTS & DELIVERABLES
•Project Abstract
•IEEE Paper
•PPT / Review Details
•Project Report
•Working Procedure in Video
•Screen Shots
•Materials & Books in CD
•Project Certification
2015 application projects

This document lists 156 project titles completed between 2015-2016 related to dot net and web application projects. The projects cover a wide range of topics including cloud computing, cyber security, healthcare, networking, image processing, gaming, and more.
The three tier security scheme in wireless

However, the problem of authentication and pairwise key
establishment in sensor networks with MSs is still not solved
in the face of mobile sink replication attacks. For the basic
probabilistic [12] and q-composite [13] key predistribution
schemes, an attacker can easily obtain a large number of keys
by capturing a small fraction of the network sensor nodes,
making it possible for the attacker to take control of the
entire network by deploying a replicated mobile sink,
preloaded with some compromised keys to authenticate
and then initiate data communication with any sensor node.
Ieee 2013 java projects list 

This document lists 61 IEEE Java projects titles from the year 2013 across several domains:
1. The projects focused on topics related to cloud computing, data mining, mobile computing, networking, parallel and distributed systems, secure computing, wireless sensor networks, and image processing.
2. Specific projects aimed to improve load balancing in clouds, enable social video sharing in clouds, and address privacy and security issues in multi-cloud environments.
3. Other projects mined data for business events, protected privacy in public auditing of cloud storage, and developed frameworks for data integrity across clouds.
Ieee java projects list 

Final year M.E IEEE PROJECTS TITLES 2014-2015 Final year IEEE PROJECTS TITLES 2014-2015 Final year M.TECH IEEE PROJECTS TITLES 2014-2015 Final year B.E IEEE
Ieee 2014 dot net projects list 

Final year M.E IEEE PROJECTS TITLES 2014-2015 Final year IEEE PROJECTS TITLES 2014-2015 Final year M.TECH IEEE PROJECTS TITLES 2014-2015 Final year B.E IEEE
SEAD: Source Encrypted Authentic Data for Wireless Sensor Networks

One of the critical issues in WSNs is providing security for the secret data in military applications. It is necessary to ensure data integrity and authentication for the source data and secure end-to-end path for data transmission. Mobile sinks are suitable for data collection and localization. Mobile sinks and sensor nodes communicate with each other using their public identity, which is prone to security attacks like sink replication and node replication attack. In this work, we have proposed Source Encrypted Authentic Data algorithm (SEAD) that hides the location of mobile sink from malicious nodes. The sensed data is encrypted utilizing symmetric encryption ---Advanced Encryption Standards (AES) and tracks the location of the mobile sink. When data encounters a malicious node in a path, then data transmission path is diverted through a secure path. SEAD uses public encryption ---Elliptic Curve Cryptography (ECC) to verify the authenticity of the data. Simulation results show that the proposed algorithm ensures data integrity and node authenticity against malicious nodes. Double encryption in the proposed algorithm produces better results in comparison with the existing algorithms.
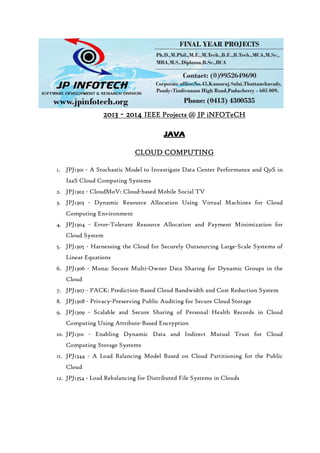
2013 2014 ieee java project titles

This document lists 71 IEEE projects from 2013 available for students through JP Infotech. The projects cover a wide range of domains including cloud computing, data mining, secure computing, networking, mobile computing, and more. Most projects are designed using the Java programming language. JP Infotech provides full support for students working on these projects, including document/presentation reviews, live explanations, assignments, mock interviews, certification, and placement assistance. Students can also propose their own projects for support.
2012 ieee android project titles

The document lists 20 Android project titles from 2012 and 16 from 2011 developed by JP Infotech. The projects cover domains such as intelligent transportation, education, language learning, healthcare, cloud computing, and security. They were published in IEEE transactions and conferences on topics including knowledge and data engineering, services computing, and mobile computing. JP Infotech provides support for publishing, presentations, assignments, job placement, and custom projects.
Sindrome compartimental expo 1

Sindrome compartimental, definicion, etiologia, fisiopatologia, clinica, giagnostico, complicaciones, tratamiento, fasciotomias
A trigger identification service for defending reactive jammers in wireless s...

A trigger identification service for defending reactive jammers in wireless s...JPINFOTECH JAYAPRAKASH
This document proposes a trigger identification service to identify sensor nodes that trigger reactive jamming attacks in wireless sensor networks. The service uses a decentralized algorithm to efficiently provide a list of trigger nodes without adding new hardware or significant message overhead. It considers various jammer and network models. Theoretical analysis and simulations validate that the framework can identify trigger nodes and help defend against reactive jamming attacks in unreliable wireless sensor networks.Hasbe a hierarchical attribute based solution for flexible and scalable acces...

Hasbe a hierarchical attribute based solution for flexible and scalable acces...JPINFOTECH JAYAPRAKASH
Hasbe a hierarchical attribute based solution for flexible and scalable access control in cloud computing PPTMore Related Content
What's hot
Projecttitles 2013

The document lists research projects in various areas including cloud computing, grid computing, image processing, networking, network security, data mining, software engineering, and mobile computing. For cloud computing, projects involve secure erasure coding, access control, and keyword search. Grid computing projects focus on meeting deadlines, detecting firewall anomalies, and location-based routing. Image processing areas are action recognition, blurry image classification. Networking research includes resource allocation and media streaming. Network security work centers on intrusion detection, authentication, storage reliability, and data provenance. Data mining projects look at fault tolerance, moving object analysis, and privacy-preserving classification. Software engineering examines component reconfiguration and requirements elicitation. Mobile computing focuses on traffic
Ieee 2014 java projects list 

Final year M.E IEEE PROJECTS TITLES 2014-2015 Final year IEEE PROJECTS TITLES 2014-2015 Final year M.TECH IEEE PROJECTS TITLES 2014-2015 Final year B.E IEEE
Novel secure communication protocol basepaper

This document proposes a secure communication protocol (SCP) for ad hoc networks using clustering techniques and Kerberos authentication. Key points:
M = {Nid, Knch, CHid}
- The network is divided into clusters, each with a cluster head (CH) node responsible for authentication.
Is encrypted by using public key of new node
Kun and send to new node. The new node
decrypts the message and stores Nid, Knch, CHid
information. Now the new node is authenticated
node of that cluster. The CH updates its
database with new node information.
- CHs use Kerberos authentication to generate IDs and passwords for nodes to authenticate each
2013-2014 IEEE Projects & Application Projects

B.E, B.TECH, M.TECH, M.E, MS, BSC, MSC, BCA, MCA, MBA, BBA, PHD, B.E (ECE, CSE, IT) B.TECH (ECE, CSE, IT) M.TECH (COMPUTER SCIENCE, SOFTWARE ENGINEERING, M.E (COMMUNICATION SYSTEMS, COMPUTER SCIENCE, SOFTWARE ENGINEERING) DIPLOMA (CSE, IT)
2013 2014 ieee projects titles

Typical Soft Technologies is one of the leading Software Company located in Chennai that offers best Quality projects and training to all customers.
We also deliver all the finest Projects at many Students, Companies. Our Computer Courses Provides best future for the Students. If you want any of our projects & Courses, then contact us.
Admin@typical.in
044-43555140, 093443 99926.
Original titles

The document discusses several topics related to image processing, data mining, mobile computing, and Android projects. Specifically, it lists 35 papers related to image processing techniques, data mining algorithms, protocols and optimizations for mobile and wireless networks, and Android-based applications and frameworks. The papers cover areas such as object detection, hyperspectral imaging, texture analysis, dictionary learning techniques for image processing tasks. Data mining papers discuss topics like query construction, recommendation diversity, pattern mining, and clustering algorithms. Mobile computing papers focus on medium access, opportunistic networking, localization, and traffic optimization. The Android projects propose solutions for security, context-aware policies, push notifications, gesture recognition, guides and more.
Ieee 2013 dot net projects list

Final year M.E IEEE PROJECTS TITLES 2014-2015 Final year IEEE PROJECTS TITLES 2014-2015 Final year M.TECH IEEE PROJECTS TITLES 2014-2015 Final year B.E IEEE
2013-2014 IEEE Projects titles

Typical Soft Technologies is one of the leading Software Company located in Chennai that offers best Quality projects and training to all customers.
We also deliver all the finest Projects at many Students, Companies. Our Computer Courses Provides best future for the Students. If you want any of our projects & Courses, then contact us.
Mail : admin@typical.in
044-43555140, 093443 99918 / 26.
Low cost Java 2013 IEEE projects

Bulk Projects For sale
IEEE 2009-10-11-12-13 PAPERS AVILABLE.
We are providing low cost project for final year student projects.
Solved 2010 -2011 -2012 - 2013 IEEE in all the domain
Mobile : 8940956123
E-Mail : ambitlick@gmail.com,
INNOVATIVE TITLES ARE ALSO WELLCOME TO DO WITH US
For All BE/BTech, ME/MTech, MSC/MCA/MS , and diplamo graduates
PROJECT SUPPORTS & DELIVERABLES
•Project Abstract
•IEEE Paper
•PPT / Review Details
•Project Report
•Working Procedure in Video
•Screen Shots
•Materials & Books in CD
•Project Certification
2015 application projects

This document lists 156 project titles completed between 2015-2016 related to dot net and web application projects. The projects cover a wide range of topics including cloud computing, cyber security, healthcare, networking, image processing, gaming, and more.
The three tier security scheme in wireless

However, the problem of authentication and pairwise key
establishment in sensor networks with MSs is still not solved
in the face of mobile sink replication attacks. For the basic
probabilistic [12] and q-composite [13] key predistribution
schemes, an attacker can easily obtain a large number of keys
by capturing a small fraction of the network sensor nodes,
making it possible for the attacker to take control of the
entire network by deploying a replicated mobile sink,
preloaded with some compromised keys to authenticate
and then initiate data communication with any sensor node.
Ieee 2013 java projects list 

This document lists 61 IEEE Java projects titles from the year 2013 across several domains:
1. The projects focused on topics related to cloud computing, data mining, mobile computing, networking, parallel and distributed systems, secure computing, wireless sensor networks, and image processing.
2. Specific projects aimed to improve load balancing in clouds, enable social video sharing in clouds, and address privacy and security issues in multi-cloud environments.
3. Other projects mined data for business events, protected privacy in public auditing of cloud storage, and developed frameworks for data integrity across clouds.
Ieee java projects list 

Final year M.E IEEE PROJECTS TITLES 2014-2015 Final year IEEE PROJECTS TITLES 2014-2015 Final year M.TECH IEEE PROJECTS TITLES 2014-2015 Final year B.E IEEE
Ieee 2014 dot net projects list 

Final year M.E IEEE PROJECTS TITLES 2014-2015 Final year IEEE PROJECTS TITLES 2014-2015 Final year M.TECH IEEE PROJECTS TITLES 2014-2015 Final year B.E IEEE
SEAD: Source Encrypted Authentic Data for Wireless Sensor Networks

One of the critical issues in WSNs is providing security for the secret data in military applications. It is necessary to ensure data integrity and authentication for the source data and secure end-to-end path for data transmission. Mobile sinks are suitable for data collection and localization. Mobile sinks and sensor nodes communicate with each other using their public identity, which is prone to security attacks like sink replication and node replication attack. In this work, we have proposed Source Encrypted Authentic Data algorithm (SEAD) that hides the location of mobile sink from malicious nodes. The sensed data is encrypted utilizing symmetric encryption ---Advanced Encryption Standards (AES) and tracks the location of the mobile sink. When data encounters a malicious node in a path, then data transmission path is diverted through a secure path. SEAD uses public encryption ---Elliptic Curve Cryptography (ECC) to verify the authenticity of the data. Simulation results show that the proposed algorithm ensures data integrity and node authenticity against malicious nodes. Double encryption in the proposed algorithm produces better results in comparison with the existing algorithms.
2013 2014 ieee java project titles

This document lists 71 IEEE projects from 2013 available for students through JP Infotech. The projects cover a wide range of domains including cloud computing, data mining, secure computing, networking, mobile computing, and more. Most projects are designed using the Java programming language. JP Infotech provides full support for students working on these projects, including document/presentation reviews, live explanations, assignments, mock interviews, certification, and placement assistance. Students can also propose their own projects for support.
What's hot (16)
SEAD: Source Encrypted Authentic Data for Wireless Sensor Networks

SEAD: Source Encrypted Authentic Data for Wireless Sensor Networks
Viewers also liked
2012 ieee android project titles

The document lists 20 Android project titles from 2012 and 16 from 2011 developed by JP Infotech. The projects cover domains such as intelligent transportation, education, language learning, healthcare, cloud computing, and security. They were published in IEEE transactions and conferences on topics including knowledge and data engineering, services computing, and mobile computing. JP Infotech provides support for publishing, presentations, assignments, job placement, and custom projects.
Sindrome compartimental expo 1

Sindrome compartimental, definicion, etiologia, fisiopatologia, clinica, giagnostico, complicaciones, tratamiento, fasciotomias
A trigger identification service for defending reactive jammers in wireless s...

A trigger identification service for defending reactive jammers in wireless s...JPINFOTECH JAYAPRAKASH
This document proposes a trigger identification service to identify sensor nodes that trigger reactive jamming attacks in wireless sensor networks. The service uses a decentralized algorithm to efficiently provide a list of trigger nodes without adding new hardware or significant message overhead. It considers various jammer and network models. Theoretical analysis and simulations validate that the framework can identify trigger nodes and help defend against reactive jamming attacks in unreliable wireless sensor networks.Hasbe a hierarchical attribute based solution for flexible and scalable acces...

Hasbe a hierarchical attribute based solution for flexible and scalable acces...JPINFOTECH JAYAPRAKASH
Hasbe a hierarchical attribute based solution for flexible and scalable access control in cloud computing PPTAndroid ieee projects 2012

2012 ieee android,ieee 2012 android projects, android titles, 2012 ieee android titles, android ieee 2012 titles, ieee project in android, best android titles, android ieee proejcts 2012, android ieee projects 2011
2012 13 eee ieee projects - jp infotech

2012 ieee projects, 2012 ieee java projects, 2012 ieee dotnet projects, 2012 ieee android projects, 2012 ieee matlab projects, 2012 ieee embedded projects, 2012 ieee robotics projects, 2012 IEEE EEE PROJECTS, 2012 IEEE POWER ELECTRONICS PROJECTS, ieee 2012 android projects, ieee 2012 java projects, ieee 2012 dotnet projects, 2012 ieee mtech projects, 2012 ieee btech projects, 2012 ieee be projects, ieee 2012 projects for cse, 2012 ieee cse projects, 2012 ieee it projects, 2012 ieee ece projects, 2012 ieee mca projects, 2012 ieee mphil projects, pondicherry ieee projects, best project centre in pondicherry, bulk ieee projects, jpinfotech ieee projects, jp infotech pondicherry, latest ieee projects, ieee projects for mtech, ieee projects for btech, ieee projects for mphil, ieee projects for be, ieee projects, student projects, students ieee projects, ieee proejcts india, ms projects, bits pilani ms projects, uk ms projects, ms ieee projects, ieee android real time projects, 2012 mtech projects, 2012 mphil projects, 2012 ieee projects with source code, pondicherry mtech projects, jpinfotech ieee projects, ieee projects, 2012 ieee project source code, journal paper publication guidance, conference paper publication guidance, ieee project, free ieee project, ieee projects for students., 2012 ieee omnet++ projects, ieee 2012 oment++ project, innovative ieee projects, latest ieee projects, 2012 latest ieee projects, ieee cloud computing projects, 2012 ieee cloud computing projects, 2012 ieee networking projects, ieee networking projects, 2012 ieee data mining projects, ieee data mining projects, 2012 ieee network security projects, ieee network security projects, 2012 ieee image processing projects, ieee image processing projects, ieee parallel and distributed system projects, ieee information security projects, 2012 wireless networking projects ieee, 2012 ieee web service projects, 2012 ieee soa projects, ieee 2012 vlsi projects
Enabling dynamic data and indirect mutual trust for cloud computing storage s...

Enabling dynamic data and indirect mutual trust for cloud computing storage s...JPINFOTECH JAYAPRAKASH
This document proposes a cloud storage scheme that allows data owners to outsource sensitive data to cloud service providers while maintaining control over the data and establishing trust between the two parties. The proposed scheme provides four key features: 1) it enables dynamic operations like modifying, inserting, deleting, and appending outsourced data blocks, 2) it ensures authorized users always receive the latest data version, 3) it establishes indirect mutual trust between the owner and cloud provider, and 4) it supports granting and revoking user access permissions. The scheme is evaluated through theoretical analysis and a prototype implementation on Amazon cloud platform.A stochastic model of multivirus dynamics

This paper proposes and analyzes a general stochastic model of multivirus spreading dynamics in networks. Existing studies mainly focus on single viruses, but this model considers multiple viruses that may compete or cooperate as they spread. The model provides analytical results to understand conditions for virus extinction, impacts when viruses can "rob" each other, and epidemic characteristics when viruses are equally powerful. Insights from this model can guide network security defense strategies.
Adaptive membership functions for hand written character recognition by voron...

Adaptive membership functions for hand written character recognition by voron...JPINFOTECH JAYAPRAKASH
The document proposes a new adaptive membership function approach for handwritten character recognition using image zoning. Existing zoning methods use static, non-adaptive membership functions that cannot model local feature distributions. The proposed system introduces adaptive membership functions selected for each zone using a genetic algorithm. It determines the optimal zoning topology and adaptive membership functions in a single process. Experimental results show it performs better than traditional zoning methods.A gossip protocol for dynamic resource management in large cloud environments

The document proposes a gossip protocol for dynamic resource management in large cloud environments. It aims to (1) ensure fair resource allocation among sites/applications, (2) dynamically adapt the allocation to load changes, and (3) scale with the number of physical machines and sites/applications. Existing gossip protocols have drawbacks like assuming static input, requiring restarts and global synchronization when input changes. The proposed protocol continuously executes on dynamic local input without global synchronization. It formally defines the resource allocation problem and provides an optimal solution without memory constraints and a heuristic solution that considers memory constraints and adaptation costs.
The China Analyst - September 2011

China is playing a crucial role in Africa's new construction boom by providing infrastructure in exchange for natural resources. Bilateral trade between China and Africa has increased dramatically from $10 billion in 2000 to over $125 billion in 2010, exceeding Africa's trade with any other partner. This trade largely consists of Chinese manufactured goods being exchanged for African raw materials. Chinese companies are actively involved in building infrastructure across Africa such as railways, roads, ports and power projects. This infrastructure development is helping to reshape Africa's business landscape and fuel economic growth, filling a gap left by decreased investment in previous decades.
Feb mar

The document provides information about workshops and events at the Independent Publishing Resource Center (IPRC) in February and March 2013. The IPRC offers resources and equipment for independent publishing including a zine library, workshops on topics like screenprinting and websites, and event space. Upcoming events include AmaZine Day on February 9th, a book release party on March 23rd, and an archive cataloging event from February 23rd to 24th. The IPRC also provides memberships that provide access to resources and discounts.
Viewers also liked (15)
A trigger identification service for defending reactive jammers in wireless s...

A trigger identification service for defending reactive jammers in wireless s...
Hasbe a hierarchical attribute based solution for flexible and scalable acces...

Hasbe a hierarchical attribute based solution for flexible and scalable acces...
Enabling dynamic data and indirect mutual trust for cloud computing storage s...

Enabling dynamic data and indirect mutual trust for cloud computing storage s...
Adaptive membership functions for hand written character recognition by voron...

Adaptive membership functions for hand written character recognition by voron...
A gossip protocol for dynamic resource management in large cloud environments

A gossip protocol for dynamic resource management in large cloud environments
Similar to IEEE PROJECTS 2013 for me
2013 2014 ieee dotnet project titles

DOT NET IEEE 2013 - 2014 IEEE PROJECT TITLES FOR STUDENTS B.E.,B.TECH.,M.E,M.TECH.,M.PHIL.,M.S.,MCA,M.S.,MBA AND DIPLOMA PROJECTS USING C#.NET, ASP.NET, .NET, DOTNET, DOT NET
CREC List.docx

The document lists 57 paper titles related to various topics including cloud computing, networking, data mining, and security. The papers cover a range of technologies and techniques including decentralized service discovery, clustering algorithms, key pre-distribution schemes, load balancing models, anomaly detection, encryption, privacy preservation, and intrusion detection.
CREC List.docx

The document lists 57 paper titles related to various topics including cloud computing, networking, data mining, and security. The papers cover a range of technologies and approaches including decentralized service discovery, clustering algorithms, key distribution schemes, load balancing models, anomaly detection, encryption, privacy preservation, and intrusion detection.
2013 IEEE PROJECT TITLES FOR CSE

2013 IEEE PROJECT TITLES FOR CSE, 2013-2014 IEEE PROJECT TITLES, IEEE PROJECTS IN PONDICHERRY, 2013 M.E. PROJECT TITLES, 2013 IEEE M.TECH. PROJECTS, 2013 IEEE MCA PROJECTS, 2013 IEEE M.PHIL PROJECTS, 2013 APPLICATION PROJECT TITLES
2013 ieee java project titles for cse, it and mca

JAVA IEEE 2013 - 2014 IEEE PROJECT TITLES FOR STUDENTS B.E.,B.TECH.,M.E,M.TECH.,M.PHIL.,M.S.,MCA,M.S.,MBA AND DIPLOMA PROJECTS USING JAVA
ieee 2013 best project titles with latest techniques

JAVA IEEE 2013 - 2014 IEEE PROJECT TITLES FOR STUDENTS B.E.,B.TECH.,M.E,M.TECH.,M.PHIL.,M.S.,MCA,M.S.,MBA AND DIPLOMA PROJECTS USING JAVA
ieee projects 2013 for m.tech.

JAVA IEEE 2013 - 2014 IEEE PROJECT TITLES FOR STUDENTS B.E.,B.TECH.,M.E,M.TECH.,M.PHIL.,M.S.,MCA,M.S.,MBA AND DIPLOMA PROJECTS USING JAVA
final year ieee projects in pondicherry

This document lists 71 IEEE projects from 2013 available for students through JP Infotech. The projects cover a wide range of domains including cloud computing, data mining, secure computing, networking, mobile computing, and more. They are designed to support students with journal and conference publications, document and presentation reviews, assignments, mock interviews, certification, and placement assistance. Students can also submit their own projects for support.
IEEE JAVA DOTNET ANDROID PROJECT TITLES 2014 - 2015 

PG Embedded Systems
www.pgembeddedsystems.com
#197 B, Surandai Road
Pavoorchatram,Tenkasi
Tirunelveli
Tamil Nadu
India 627 808
Tel:04633-251200
Mob:+91-98658-62045, +91-7598462045.
General Information and Enquiries:
g12ganesh@gmail.com
IEEE 2014 .Net & Java Projects List

This document lists 90 projects available from Logicsystems in 2014 across various technologies and domains. It provides the contact information for Arunkumar to discuss the projects further. The projects cover topics such as cloud computing, data mining, secure computing, networking, parallel and distributed systems, mobile computing, and service computing. Programming languages included are Java and .NET.
VTU Final Year Engineering Project Title List for Computer Science Engineerin...

Zetta Networks is one of the pioneer in IT training companies in the country. Zetta Networks is providing quality education to IT Aspirants, Corporate giants, institutions. Zetta Networks is committed to create great software brains of high caliber, who stay ahead in technology way ahead of others.
VTU Computer Science Engineering & Information Science Engineering Project Ti...

Zetta Networks is one of the pioneer in IT training companies in the country. Zetta Networks is providing quality education to IT Aspirants, Corporate giants, institutions. Zetta Networks is committed to create great software brains of high caliber, who stay ahead in technology way ahead of others.
2013 ieee java project titles-lans a-informatics

Ieee projects 2013 Coimbatore ,2013 IEEE Projects for CSE ,2013 IEEE Projects for IT,2013 IEEE Projects for CSE/IT,IEEE Final Year Academic Projects,IEEE Final Year Academic Projects for CSE,IEEE Final Year Academic Projects for IT,
IEEE Final Year Academic Projects for CSE/IT,ieee projects 2013 for CSE ,ieee projects 2013 for IT,ieee projects 2013 for CSE in Coimbatore,ieee projects 2013 for IT in Coimbatore,Live Student Projects in Coimbatore,Best IEEE Projects in Coimbatore for Final Year Students ,Best IEEE Projects in Coimbatore for CSE ,Best IEEE Projects in Coimbatore for IT ,Best IEEE Projects in Coimbatore for CSE/IT,Best IEEE Projects in Coimbatore for Final Year CSE Students ,Best IEEE Projects in Coimbatore for Final Year IT Students ,Best IEEE Projects in Coimbatore for Final Year CSE / IT Students ,BE final year IEEE Projects 2013,BE CSE final year IEEE Projects 2013,BTECH final year IEEE Projects 2013,BTECH / IT final year IEEE Projects 2013,BE / BTECH final year IEEE Projects 2013,BE CSE /BTECH IT final year IEEE Projects 2013,ME final year IEEE Projects 2013,ME CSE final year IEEE Projects 2013,MTECH final year IEEE Projects 2013,MTECH / IT final year IEEE Projects 2013,ME / MTECH final year IEEE Projects 2013,ME CSE /MTECH IT final year IEEE Projects 2013,MCA final year ,IEEE Projects 2013,MCA final year projects 2013,BE final year IEEE Projects 2013,BE CSE final year IEEE Projects 2013,MSC IT ieee projects institutes in Coimbatore,
IEEE Projects 2012

The document provides a list of 82 titles and keywords related to various topics in information technology including cloud computing, parallel and distributed systems, mobile computing, data mining, image processing and MATLAB, and network security. The titles involve research on efficient data processing in clouds, privacy-preserving search, data integrity proofs, load balancing, intrusion detection, and more. The keywords indicate that the research involves programming languages including Java, .NET, and NS2.
IEEE projects java and dotnet for BE BTECH ME MTECH MCA MCS Diploma

The document lists over 60 projects related to various topics including Android, Java, cloud computing, knowledge and data engineering, secure computing, networking, parallel and distributed systems, mobile computing, image processing, service computing, and multimedia. The projects involve developing applications and conducting research related to topics such as recommendation systems, location services, social networks, healthcare, cryptography, and more.
Java IEEE 2013 Projects list 

Hi,
We provide code and docs at low cost IEEE
2013,2012,2011,2010,2009-2006 Non-IEEE Projects Android in Java and
more info:
ieeeprojectsinhyd@gmail.com
Java ieee titles2016 student

The document lists 81 projects with codes from J1601 to J1681. Each project has a code, title, and domain label. The majority of the projects (around 60%) fall under the domain of Data Mining, while others are related to domains like Cloud Computing, Networking, Secure Computing, PDS, Image Processing, and Information Forensics & Security.
Ieee 2013 java project titles richbraintechnologies

This document provides contact information for Richbrain Technologies and lists over 50 potential IEEE final year project titles related to cloud computing, data mining, parallel distribution, and mobile computing. Students can contact Richbrain Technologies via phone or email to receive project guidance and assistance on topics such as load balancing in clouds, data mining algorithms, distributed systems, and routing protocols for mobile ad hoc networks.
Ieee 2013 java project titles richbrainprojects

This document lists over 50 IEEE final year projects from various domains including cloud computing, data mining, parallel distribution, and mobile computing. It provides contact information for Richbrain Technologies, which offers these projects. Titles and brief descriptions of projects in each domain are provided.
Ieee 2013 java project titles richbraintech

The document lists contact information for Richbrain Technologies and describes that they provide IEEE final year projects for students in various disciplines such as computer science, information technology, electronics and communication engineering. It then lists over 45 potential project titles related to cloud computing and data mining that students can select for their final year projects.
Similar to IEEE PROJECTS 2013 for me (20)
ieee 2013 best project titles with latest techniques

ieee 2013 best project titles with latest techniques
IEEE JAVA DOTNET ANDROID PROJECT TITLES 2014 - 2015 

IEEE JAVA DOTNET ANDROID PROJECT TITLES 2014 - 2015
VTU Final Year Engineering Project Title List for Computer Science Engineerin...

VTU Final Year Engineering Project Title List for Computer Science Engineerin...
VTU Computer Science Engineering & Information Science Engineering Project Ti...

VTU Computer Science Engineering & Information Science Engineering Project Ti...
IEEE projects java and dotnet for BE BTECH ME MTECH MCA MCS Diploma

IEEE projects java and dotnet for BE BTECH ME MTECH MCA MCS Diploma
Ieee 2013 java project titles richbraintechnologies

Ieee 2013 java project titles richbraintechnologies
Recently uploaded
Traditional Musical Instruments of Arunachal Pradesh and Uttar Pradesh - RAYH...

Traditional Musical Instruments of Arunachal Pradesh and Uttar Pradesh
ISO/IEC 27001, ISO/IEC 42001, and GDPR: Best Practices for Implementation and...

Denis is a dynamic and results-driven Chief Information Officer (CIO) with a distinguished career spanning information systems analysis and technical project management. With a proven track record of spearheading the design and delivery of cutting-edge Information Management solutions, he has consistently elevated business operations, streamlined reporting functions, and maximized process efficiency.
Certified as an ISO/IEC 27001: Information Security Management Systems (ISMS) Lead Implementer, Data Protection Officer, and Cyber Risks Analyst, Denis brings a heightened focus on data security, privacy, and cyber resilience to every endeavor.
His expertise extends across a diverse spectrum of reporting, database, and web development applications, underpinned by an exceptional grasp of data storage and virtualization technologies. His proficiency in application testing, database administration, and data cleansing ensures seamless execution of complex projects.
What sets Denis apart is his comprehensive understanding of Business and Systems Analysis technologies, honed through involvement in all phases of the Software Development Lifecycle (SDLC). From meticulous requirements gathering to precise analysis, innovative design, rigorous development, thorough testing, and successful implementation, he has consistently delivered exceptional results.
Throughout his career, he has taken on multifaceted roles, from leading technical project management teams to owning solutions that drive operational excellence. His conscientious and proactive approach is unwavering, whether he is working independently or collaboratively within a team. His ability to connect with colleagues on a personal level underscores his commitment to fostering a harmonious and productive workplace environment.
Date: May 29, 2024
Tags: Information Security, ISO/IEC 27001, ISO/IEC 42001, Artificial Intelligence, GDPR
-------------------------------------------------------------------------------
Find out more about ISO training and certification services
Training: ISO/IEC 27001 Information Security Management System - EN | PECB
ISO/IEC 42001 Artificial Intelligence Management System - EN | PECB
General Data Protection Regulation (GDPR) - Training Courses - EN | PECB
Webinars: https://pecb.com/webinars
Article: https://pecb.com/article
-------------------------------------------------------------------------------
For more information about PECB:
Website: https://pecb.com/
LinkedIn: https://www.linkedin.com/company/pecb/
Facebook: https://www.facebook.com/PECBInternational/
Slideshare: http://www.slideshare.net/PECBCERTIFICATION
Hindi varnamala | hindi alphabet PPT.pdf

हिंदी वर्णमाला पीपीटी, hindi alphabet PPT presentation, hindi varnamala PPT, Hindi Varnamala pdf, हिंदी स्वर, हिंदी व्यंजन, sikhiye hindi varnmala, dr. mulla adam ali, hindi language and literature, hindi alphabet with drawing, hindi alphabet pdf, hindi varnamala for childrens, hindi language, hindi varnamala practice for kids, https://www.drmullaadamali.com
Advanced Java[Extra Concepts, Not Difficult].docx![Advanced Java[Extra Concepts, Not Difficult].docx](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
![Advanced Java[Extra Concepts, Not Difficult].docx](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
This is part 2 of my Java Learning Journey. This contains Hashing, ArrayList, LinkedList, Date and Time Classes, Calendar Class and more.
Gender and Mental Health - Counselling and Family Therapy Applications and In...

A proprietary approach developed by bringing together the best of learning theories from Psychology, design principles from the world of visualization, and pedagogical methods from over a decade of training experience, that enables you to: Learn better, faster!
Pengantar Penggunaan Flutter - Dart programming language1.pptx

Pengantar Penggunaan Flutter - Dart programming language1.pptx
Wound healing PPT

This document provides an overview of wound healing, its functions, stages, mechanisms, factors affecting it, and complications.
A wound is a break in the integrity of the skin or tissues, which may be associated with disruption of the structure and function.
Healing is the body’s response to injury in an attempt to restore normal structure and functions.
Healing can occur in two ways: Regeneration and Repair
There are 4 phases of wound healing: hemostasis, inflammation, proliferation, and remodeling. This document also describes the mechanism of wound healing. Factors that affect healing include infection, uncontrolled diabetes, poor nutrition, age, anemia, the presence of foreign bodies, etc.
Complications of wound healing like infection, hyperpigmentation of scar, contractures, and keloid formation.
The History of Stoke Newington Street Names

Presented at the Stoke Newington Literary Festival on 9th June 2024
www.StokeNewingtonHistory.com
What is Digital Literacy? A guest blog from Andy McLaughlin, University of Ab...

What is Digital Literacy? A guest blog from Andy McLaughlin, University of Aberdeen
RHEOLOGY Physical pharmaceutics-II notes for B.pharm 4th sem students

Physical pharmaceutics notes for B.pharm students
Chapter wise All Notes of First year Basic Civil Engineering.pptx

Chapter wise All Notes of First year Basic Civil Engineering
Syllabus
Chapter-1
Introduction to objective, scope and outcome the subject
Chapter 2
Introduction: Scope and Specialization of Civil Engineering, Role of civil Engineer in Society, Impact of infrastructural development on economy of country.
Chapter 3
Surveying: Object Principles & Types of Surveying; Site Plans, Plans & Maps; Scales & Unit of different Measurements.
Linear Measurements: Instruments used. Linear Measurement by Tape, Ranging out Survey Lines and overcoming Obstructions; Measurements on sloping ground; Tape corrections, conventional symbols. Angular Measurements: Instruments used; Introduction to Compass Surveying, Bearings and Longitude & Latitude of a Line, Introduction to total station.
Levelling: Instrument used Object of levelling, Methods of levelling in brief, and Contour maps.
Chapter 4
Buildings: Selection of site for Buildings, Layout of Building Plan, Types of buildings, Plinth area, carpet area, floor space index, Introduction to building byelaws, concept of sun light & ventilation. Components of Buildings & their functions, Basic concept of R.C.C., Introduction to types of foundation
Chapter 5
Transportation: Introduction to Transportation Engineering; Traffic and Road Safety: Types and Characteristics of Various Modes of Transportation; Various Road Traffic Signs, Causes of Accidents and Road Safety Measures.
Chapter 6
Environmental Engineering: Environmental Pollution, Environmental Acts and Regulations, Functional Concepts of Ecology, Basics of Species, Biodiversity, Ecosystem, Hydrological Cycle; Chemical Cycles: Carbon, Nitrogen & Phosphorus; Energy Flow in Ecosystems.
Water Pollution: Water Quality standards, Introduction to Treatment & Disposal of Waste Water. Reuse and Saving of Water, Rain Water Harvesting. Solid Waste Management: Classification of Solid Waste, Collection, Transportation and Disposal of Solid. Recycling of Solid Waste: Energy Recovery, Sanitary Landfill, On-Site Sanitation. Air & Noise Pollution: Primary and Secondary air pollutants, Harmful effects of Air Pollution, Control of Air Pollution. . Noise Pollution Harmful Effects of noise pollution, control of noise pollution, Global warming & Climate Change, Ozone depletion, Greenhouse effect
Text Books:
1. Palancharmy, Basic Civil Engineering, McGraw Hill publishers.
2. Satheesh Gopi, Basic Civil Engineering, Pearson Publishers.
3. Ketki Rangwala Dalal, Essentials of Civil Engineering, Charotar Publishing House.
4. BCP, Surveying volume 1
How to Make a Field Mandatory in Odoo 17

In Odoo, making a field required can be done through both Python code and XML views. When you set the required attribute to True in Python code, it makes the field required across all views where it's used. Conversely, when you set the required attribute in XML views, it makes the field required only in the context of that particular view.
BÀI TẬP BỔ TRỢ TIẾNG ANH LỚP 9 CẢ NĂM - GLOBAL SUCCESS - NĂM HỌC 2024-2025 - ...

BÀI TẬP BỔ TRỢ TIẾNG ANH LỚP 9 CẢ NĂM - GLOBAL SUCCESS - NĂM HỌC 2024-2025 - ...Nguyen Thanh Tu Collection
https://app.box.com/s/tacvl9ekroe9hqupdnjruiypvm9rdaneBBR 2024 Summer Sessions Interview Training

Qualitative research interview training by Professor Katrina Pritchard and Dr Helen Williams
বাংলাদেশ অর্থনৈতিক সমীক্ষা (Economic Review) ২০২৪ UJS App.pdf

বাংলাদেশের অর্থনৈতিক সমীক্ষা ২০২৪ [Bangladesh Economic Review 2024 Bangla.pdf] কম্পিউটার , ট্যাব ও স্মার্ট ফোন ভার্সন সহ সম্পূর্ণ বাংলা ই-বুক বা pdf বই " সুচিপত্র ...বুকমার্ক মেনু 🔖 ও হাইপার লিংক মেনু 📝👆 যুক্ত ..
আমাদের সবার জন্য খুব খুব গুরুত্বপূর্ণ একটি বই ..বিসিএস, ব্যাংক, ইউনিভার্সিটি ভর্তি ও যে কোন প্রতিযোগিতা মূলক পরীক্ষার জন্য এর খুব ইম্পরট্যান্ট একটি বিষয় ...তাছাড়া বাংলাদেশের সাম্প্রতিক যে কোন ডাটা বা তথ্য এই বইতে পাবেন ...
তাই একজন নাগরিক হিসাবে এই তথ্য গুলো আপনার জানা প্রয়োজন ...।
বিসিএস ও ব্যাংক এর লিখিত পরীক্ষা ...+এছাড়া মাধ্যমিক ও উচ্চমাধ্যমিকের স্টুডেন্টদের জন্য অনেক কাজে আসবে ...
Recently uploaded (20)
Traditional Musical Instruments of Arunachal Pradesh and Uttar Pradesh - RAYH...

Traditional Musical Instruments of Arunachal Pradesh and Uttar Pradesh - RAYH...
NEWSPAPERS - QUESTION 1 - REVISION POWERPOINT.pptx

NEWSPAPERS - QUESTION 1 - REVISION POWERPOINT.pptx
B. Ed Syllabus for babasaheb ambedkar education university.pdf

B. Ed Syllabus for babasaheb ambedkar education university.pdf
ISO/IEC 27001, ISO/IEC 42001, and GDPR: Best Practices for Implementation and...

ISO/IEC 27001, ISO/IEC 42001, and GDPR: Best Practices for Implementation and...
Gender and Mental Health - Counselling and Family Therapy Applications and In...

Gender and Mental Health - Counselling and Family Therapy Applications and In...
Pengantar Penggunaan Flutter - Dart programming language1.pptx

Pengantar Penggunaan Flutter - Dart programming language1.pptx
What is Digital Literacy? A guest blog from Andy McLaughlin, University of Ab...

What is Digital Literacy? A guest blog from Andy McLaughlin, University of Ab...
RHEOLOGY Physical pharmaceutics-II notes for B.pharm 4th sem students

RHEOLOGY Physical pharmaceutics-II notes for B.pharm 4th sem students
Chapter wise All Notes of First year Basic Civil Engineering.pptx

Chapter wise All Notes of First year Basic Civil Engineering.pptx
IGCSE Biology Chapter 14- Reproduction in Plants.pdf

IGCSE Biology Chapter 14- Reproduction in Plants.pdf
BÀI TẬP BỔ TRỢ TIẾNG ANH LỚP 9 CẢ NĂM - GLOBAL SUCCESS - NĂM HỌC 2024-2025 - ...

BÀI TẬP BỔ TRỢ TIẾNG ANH LỚP 9 CẢ NĂM - GLOBAL SUCCESS - NĂM HỌC 2024-2025 - ...
বাংলাদেশ অর্থনৈতিক সমীক্ষা (Economic Review) ২০২৪ UJS App.pdf

বাংলাদেশ অর্থনৈতিক সমীক্ষা (Economic Review) ২০২৪ UJS App.pdf
IEEE PROJECTS 2013 for me
- 1. 2013201320132013 ---- 2014201420142014 IEEE ProjectsIEEE ProjectsIEEE ProjectsIEEE Projects @@@@ JP iNFOTeCHJP iNFOTeCHJP iNFOTeCHJP iNFOTeCH JAVAJAVAJAVAJAVA CLOUD COMPUTINGCLOUD COMPUTINGCLOUD COMPUTINGCLOUD COMPUTING 1. JPJ1301 - A Stochastic Model to Investigate Data Center Performance and QoS in IaaS Cloud Computing Systems 2. JPJ1302 - CloudMoV: Cloud-based Mobile Social TV 3. JPJ1303 - Dynamic Resource Allocation Using Virtual Machines for Cloud Computing Environment 4. JPJ1304 - Error-Tolerant Resource Allocation and Payment Minimization for Cloud System 5. JPJ1305 - Harnessing the Cloud for Securely Outsourcing Large-Scale Systems of Linear Equations 6. JPJ1306 - Mona: Secure Multi-Owner Data Sharing for Dynamic Groups in the Cloud 7. JPJ1307 - PACK: Prediction-Based Cloud Bandwidth and Cost Reduction System 8. JPJ1308 - Privacy-Preserving Public Auditing for Secure Cloud Storage 9. JPJ1309 - Scalable and Secure Sharing of Personal Health Records in Cloud Computing Using Attribute-Based Encryption 10. JPJ1310 - Enabling Dynamic Data and Indirect Mutual Trust for Cloud Computing Storage Systems 11. JPJ1344 - A Load Balancing Model Based on Cloud Partitioning for the Public Cloud 12. JPJ1354 - Load Rebalancing for Distributed File Systems in Clouds
- 2. 13. JPJ1359 – Optimizing Cloud Resources for Delivering IPTV Services Through Virtualization 14. JPJ1363 – Privacy Preserving Delegated Access Control in Public Clouds KNOWLEDGE AND DATA ENGINEERINGKNOWLEDGE AND DATA ENGINEERINGKNOWLEDGE AND DATA ENGINEERINGKNOWLEDGE AND DATA ENGINEERING 15. JPJ1311 - A Fast Clustering-Based Feature Subset Selection Algorithm for High- Dimensional Data 16. JPJ1312 - A New Algorithm for Inferring User Search Goals with Feedback Sessions 17. JPJ1313 - Annotating Search Results from Web Databases 18. JPJ1314 - Anomaly Detection via Online Over-Sampling Principal Component Analysis 19. JPJ1315 - Distributed Processing of Probabilistic Top-k Queries in Wireless Sensor Networks 20. JPJ1316- m-Privacy for Collaborative Data Publishing 21. JPJ1317 - Protecting Sensitive Labels in Social Network Data Anonymization 22. JPJ1318 - Tweet Analysis for Real-Time Event Detection and Earthquake Reporting System Development 23. JPJ1345 - Document Clustering for Forensic Analysis: An Approach for Improving Computer Inspection 24. JPJ1346 - A Method for Mining Infrequent Causal Associations and Its Application in Finding Adverse Drug Reaction Signal Pairs 25. JPJ1347 - Clustering Sentence-Level Text Using a Novel Fuzzy Relational Clustering Algorithm
- 3. 26. JPJ1358 - Crowdsourcing Predictors of Behavioral Outcomes 27. JPJ1362 - Facilitating Document Annotation using Content and Querying Value 28. JPJ1365 - A Generalized Flow-Based Method for Analysis of Implicit Relationships on Wikipedia 29. JPJ1366 - A System to Filter Unwanted Messages from OSN User Walls 30. JPJ1367 - Anonymization of Centralized and Distributed Social Networks by Sequential Clustering 31. JPJ1370 - Intrusion Detection Technique by using K-means, Fuzzy Neural Network and SVM classifiers. (CONFERENCE PAPER) SECURE COMPUTINGSECURE COMPUTINGSECURE COMPUTINGSECURE COMPUTING 32. JPJ1319 - EAACK—A Secure Intrusion-Detection System for MANETs 33. JPJ1320 - Identity-Based Secure Distributed Data Storage Schemes 34. JPJ1321 - Modeling the Pairwise Key Predistribution Scheme in the Presence of Unreliable Links 35. JPJ1322 - NICE: Network Intrusion Detection and Countermeasure Selection in Virtual Network Systems 36. JPJ1323 - Privacy Preserving Data Sharing With Anonymous ID Assignment 37. JPJ1324 - Securing Class Initialization in Java-like Languages 38. JPJ1325 - Security Analysis of a Single Sign-On Mechanism for Distributed Computer Networks 39. JPJ1326 -SORT: A Self-ORganizing Trust Model for Peer-to-Peer Systems 40. JPJ1327 - WARNINGBIRD: A Near Real-time Detection System for Suspicious URLs in Twitter Stream 41. JPJ1348 - Two tales of privacy in online social networks
- 4. 42. JPJ1361 - Secure Encounter-based Mobile Social Networks: Requirements, Designs, and Tradeoffs. 43. JPJ1364 - Twitsper: Tweeting Privately 44. JPJ1371 - Combining Cryptographic Primitives to Prevent Jamming Attacks in Wireless Networks (CONFERENCE PAPER) NETWORKINGNETWORKINGNETWORKINGNETWORKING 45. JPJ1328 - A Highly Scalable Key Pre-Distribution Scheme for Wireless Sensor Networks 46. JPJ1329 - Delay-Based Network Utility Maximization 47. JPJ1330 - Dynamic Control of Coding for Progressive Packet Arrivals in DTNs 48. JPJ1349 - Minimum Cost Blocking Problem in Multi-path Wireless Routing Protocols 49. JPJ1350 - On the Node Clone Detection in Wireless Sensor Networks 50. JPJ1351 - Opportunistic MANETs: Mobility Can Make Up for Low Transmission Power 51. JPJ1352 - Back-Pressure-Based Packet-by-Packet Adaptive Routing in Communication Networks 52. JPJ1353- Fast Transmission to Remote Cooperative Groups: A New Key Management Paradigm 53. JPJ1360 - Participatory Privacy: Enabling Privacy in Participatory Sensing
- 5. PARALLEL AND DISTRIBUTED SYSTEMSPARALLEL AND DISTRIBUTED SYSTEMSPARALLEL AND DISTRIBUTED SYSTEMSPARALLEL AND DISTRIBUTED SYSTEMS 54. JPJ1331 - A Secure Protocol for Spontaneous Wireless Ad Hoc Networks Creation 55. JPJ1332 - Security Analysis of a Privacy-Preserving Decentralized Key-Policy Attribute-Based Encryption Scheme 56. JPJ1333 - IP-Geolocation Mapping for Moderately Connected Internet Regions 57. JPJ1334 - Optimal Client-Server Assignment for Internet Distributed Systems MOBILE COMPUTINGMOBILE COMPUTINGMOBILE COMPUTINGMOBILE COMPUTING 58. JPJ1335 - Content Sharing over Smartphone-Based Delay-Tolerant Networks 59. JPJ1336 - DCIM: Distributed Cache Invalidation Method for Maintaining Cache Consistency in Wireless Mobile Networks 60. JPJ1337 - Discovery and Verification of Neighbor Positions in Mobile Ad Hoc Networks 61. JPJ1338 - Efficient Rekeying Framework for Secure Multicast with Diverse- Subscription-Period Mobile Users 62. JPJ1355 - Toward a Statistical Framework for Source Anonymity in Sensor Networks 63. JPJ1356 - Mobile Relay Configuration in Data-Intensive Wireless Sensor Networks 64. JPJ1357 - Vampire Attacks: Draining Life from Wireless Ad Hoc Sensor Networks 65. JPJ1368 - Toward Privacy Preserving and Collusion Resistance in a Location Proof Updating System
- 6. PATTERNPATTERNPATTERNPATTERN ANALYSIS AND MACHINE INTELLIGENCEANALYSIS AND MACHINE INTELLIGENCEANALYSIS AND MACHINE INTELLIGENCEANALYSIS AND MACHINE INTELLIGENCE 66. JPJ1339 - A Framework for Mining Signatures from Event Sequences and Its Applications in Healthcare Data SERVICES COMPUTINGSERVICES COMPUTINGSERVICES COMPUTINGSERVICES COMPUTING 67. JPJ1340 - A Decentralized Service Discovery Approach on Peer-to-Peer Networks 68. JPJ1341 - Personalized QoS-Aware Web Service Recommendation and Visualization 69. JPJ1342 - Privacy-Enhanced Web Service Composition SOFTWARE ENGINEERINGSOFTWARE ENGINEERINGSOFTWARE ENGINEERINGSOFTWARE ENGINEERING 70. JPJ1343 - Whole Test Suite Generation MULTIMEDIAMULTIMEDIAMULTIMEDIAMULTIMEDIA 71. JPJ1369 - Understanding the External Links of Video Sharing Sites: Measurement and Analysis
