2013 ieee java project titles for cse, it and mca
•
1 like•772 views
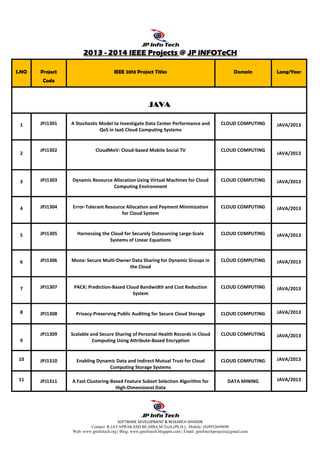
JAVA IEEE 2013 - 2014 IEEE PROJECT TITLES FOR STUDENTS B.E.,B.TECH.,M.E,M.TECH.,M.PHIL.,M.S.,MCA,M.S.,MBA AND DIPLOMA PROJECTS USING JAVA
Report
Share
Report
Share
Download to read offline
Recommended
ieee projects for cse 2013

This document provides details about final year project titles available in various domains like cloud computing, data mining, secure computing, networking, etc. for the years 2013-2014. It lists 80 IEEE Java project titles for 2013 along with their codes and domains. It also lists 5 IEEE .NET project titles for 2013. The document gives contact details of the organization and details of various services provided like payment, delivery, client support etc.
2013 ieee java project titles-lans a-informatics

Ieee projects 2013 Coimbatore ,2013 IEEE Projects for CSE ,2013 IEEE Projects for IT,2013 IEEE Projects for CSE/IT,IEEE Final Year Academic Projects,IEEE Final Year Academic Projects for CSE,IEEE Final Year Academic Projects for IT,
IEEE Final Year Academic Projects for CSE/IT,ieee projects 2013 for CSE ,ieee projects 2013 for IT,ieee projects 2013 for CSE in Coimbatore,ieee projects 2013 for IT in Coimbatore,Live Student Projects in Coimbatore,Best IEEE Projects in Coimbatore for Final Year Students ,Best IEEE Projects in Coimbatore for CSE ,Best IEEE Projects in Coimbatore for IT ,Best IEEE Projects in Coimbatore for CSE/IT,Best IEEE Projects in Coimbatore for Final Year CSE Students ,Best IEEE Projects in Coimbatore for Final Year IT Students ,Best IEEE Projects in Coimbatore for Final Year CSE / IT Students ,BE final year IEEE Projects 2013,BE CSE final year IEEE Projects 2013,BTECH final year IEEE Projects 2013,BTECH / IT final year IEEE Projects 2013,BE / BTECH final year IEEE Projects 2013,BE CSE /BTECH IT final year IEEE Projects 2013,ME final year IEEE Projects 2013,ME CSE final year IEEE Projects 2013,MTECH final year IEEE Projects 2013,MTECH / IT final year IEEE Projects 2013,ME / MTECH final year IEEE Projects 2013,ME CSE /MTECH IT final year IEEE Projects 2013,MCA final year ,IEEE Projects 2013,MCA final year projects 2013,BE final year IEEE Projects 2013,BE CSE final year IEEE Projects 2013,MSC IT ieee projects institutes in Coimbatore,
VTU Computer Science Engineering & Information Science Engineering Project Ti...

Zetta Networks is one of the pioneer in IT training companies in the country. Zetta Networks is providing quality education to IT Aspirants, Corporate giants, institutions. Zetta Networks is committed to create great software brains of high caliber, who stay ahead in technology way ahead of others.
ANALYSING THE POTENTIAL OF BLE TO SUPPORT DYNAMIC BROADCASTING SCENARIOS

In this paper, we present a novel approach for broadcasting information based on a Bluetooth Low Energy
(BLE) ibeacon technology. We propose a dynamic method that uses a combination of Wi-Fi and BLE
technology where every technology plays a part in a user discovery and broadcasting process. In such
system, a specific ibeacon device broadcasts the information when a user is in proximity. Using
experiments, we conduct a scenario where the system discovers users, disseminates information, and later
we use collected data to examine the system performance and capability. The results show that our
proposed approach has a promising potential to become a powerful tool in the discovery and broadcasting
concept that can be easily implemented and used in business environments.
IEEE PROJECTS 2013 for me

JAVA IEEE 2013 - 2014 IEEE PROJECT TITLES FOR STUDENTS B.E.,B.TECH.,M.E,M.TECH.,M.PHIL.,M.S.,MCA,M.S.,MBA AND DIPLOMA PROJECTS USING JAVA
IRJET- A Noval and Efficient Revolving Flywheel Pin Entry Method Resilient to...

The document proposes a new authentication method called the revolving flywheel PIN-entry method to prevent shoulder surfing attacks. The method uses a revolving flywheel with three layers and sections containing randomly placed numbers and colors. Users register a PIN and for authentication must enter the PIN by clicking color pads associated with the numbers on the flywheel instead of entering the actual digits. The method aims to provide secure, usable authentication in a short time period and could be applied to systems like ATMs.
Be,me ieee 2015 16 computer&inforamation science&bca,diploma,mca titles

This document provides a list of 74 academic projects available for students in various technologies like Java, networking, cloud computing, data mining, and more. The projects are designed for students in BE, ME, MCA, BCA, and diploma programs. It includes the project title, technology used and contact details of IgeekS Technologies who provide the projects.
SOFTORIX Project TitlesList

Softorix Technologies is an inventive, software and hardware-led solutions provider. With a core team of well-qualified professionals representing diverse functional areas such as Information Technology, Embedded Systems and advanced digital signal processing (DSP), we understand the students’ needs, and develop their quality of professional life by simply making the technology readily usable for them. We Practice exclusively in image processing, simulation, optimization, customization and system integration.
Our project methodology includes techniques for initiating a project, developing the requirements, making clear assignments to the project team, developing a dynamic schedule, reporting status to executives and problem solving. In today's competitive environment, students want to ensure that they are getting guidance in an organization that can meet their professional needs. With our well equipped team of solid Information Systems Professionals, who study, design, develop, enhance, customize, implement, maintain and support various aspects of Information Technology, students can be sure that Softorix is just that sort of organization.
Recommended
ieee projects for cse 2013

This document provides details about final year project titles available in various domains like cloud computing, data mining, secure computing, networking, etc. for the years 2013-2014. It lists 80 IEEE Java project titles for 2013 along with their codes and domains. It also lists 5 IEEE .NET project titles for 2013. The document gives contact details of the organization and details of various services provided like payment, delivery, client support etc.
2013 ieee java project titles-lans a-informatics

Ieee projects 2013 Coimbatore ,2013 IEEE Projects for CSE ,2013 IEEE Projects for IT,2013 IEEE Projects for CSE/IT,IEEE Final Year Academic Projects,IEEE Final Year Academic Projects for CSE,IEEE Final Year Academic Projects for IT,
IEEE Final Year Academic Projects for CSE/IT,ieee projects 2013 for CSE ,ieee projects 2013 for IT,ieee projects 2013 for CSE in Coimbatore,ieee projects 2013 for IT in Coimbatore,Live Student Projects in Coimbatore,Best IEEE Projects in Coimbatore for Final Year Students ,Best IEEE Projects in Coimbatore for CSE ,Best IEEE Projects in Coimbatore for IT ,Best IEEE Projects in Coimbatore for CSE/IT,Best IEEE Projects in Coimbatore for Final Year CSE Students ,Best IEEE Projects in Coimbatore for Final Year IT Students ,Best IEEE Projects in Coimbatore for Final Year CSE / IT Students ,BE final year IEEE Projects 2013,BE CSE final year IEEE Projects 2013,BTECH final year IEEE Projects 2013,BTECH / IT final year IEEE Projects 2013,BE / BTECH final year IEEE Projects 2013,BE CSE /BTECH IT final year IEEE Projects 2013,ME final year IEEE Projects 2013,ME CSE final year IEEE Projects 2013,MTECH final year IEEE Projects 2013,MTECH / IT final year IEEE Projects 2013,ME / MTECH final year IEEE Projects 2013,ME CSE /MTECH IT final year IEEE Projects 2013,MCA final year ,IEEE Projects 2013,MCA final year projects 2013,BE final year IEEE Projects 2013,BE CSE final year IEEE Projects 2013,MSC IT ieee projects institutes in Coimbatore,
VTU Computer Science Engineering & Information Science Engineering Project Ti...

Zetta Networks is one of the pioneer in IT training companies in the country. Zetta Networks is providing quality education to IT Aspirants, Corporate giants, institutions. Zetta Networks is committed to create great software brains of high caliber, who stay ahead in technology way ahead of others.
ANALYSING THE POTENTIAL OF BLE TO SUPPORT DYNAMIC BROADCASTING SCENARIOS

In this paper, we present a novel approach for broadcasting information based on a Bluetooth Low Energy
(BLE) ibeacon technology. We propose a dynamic method that uses a combination of Wi-Fi and BLE
technology where every technology plays a part in a user discovery and broadcasting process. In such
system, a specific ibeacon device broadcasts the information when a user is in proximity. Using
experiments, we conduct a scenario where the system discovers users, disseminates information, and later
we use collected data to examine the system performance and capability. The results show that our
proposed approach has a promising potential to become a powerful tool in the discovery and broadcasting
concept that can be easily implemented and used in business environments.
IEEE PROJECTS 2013 for me

JAVA IEEE 2013 - 2014 IEEE PROJECT TITLES FOR STUDENTS B.E.,B.TECH.,M.E,M.TECH.,M.PHIL.,M.S.,MCA,M.S.,MBA AND DIPLOMA PROJECTS USING JAVA
IRJET- A Noval and Efficient Revolving Flywheel Pin Entry Method Resilient to...

The document proposes a new authentication method called the revolving flywheel PIN-entry method to prevent shoulder surfing attacks. The method uses a revolving flywheel with three layers and sections containing randomly placed numbers and colors. Users register a PIN and for authentication must enter the PIN by clicking color pads associated with the numbers on the flywheel instead of entering the actual digits. The method aims to provide secure, usable authentication in a short time period and could be applied to systems like ATMs.
Be,me ieee 2015 16 computer&inforamation science&bca,diploma,mca titles

This document provides a list of 74 academic projects available for students in various technologies like Java, networking, cloud computing, data mining, and more. The projects are designed for students in BE, ME, MCA, BCA, and diploma programs. It includes the project title, technology used and contact details of IgeekS Technologies who provide the projects.
SOFTORIX Project TitlesList

Softorix Technologies is an inventive, software and hardware-led solutions provider. With a core team of well-qualified professionals representing diverse functional areas such as Information Technology, Embedded Systems and advanced digital signal processing (DSP), we understand the students’ needs, and develop their quality of professional life by simply making the technology readily usable for them. We Practice exclusively in image processing, simulation, optimization, customization and system integration.
Our project methodology includes techniques for initiating a project, developing the requirements, making clear assignments to the project team, developing a dynamic schedule, reporting status to executives and problem solving. In today's competitive environment, students want to ensure that they are getting guidance in an organization that can meet their professional needs. With our well equipped team of solid Information Systems Professionals, who study, design, develop, enhance, customize, implement, maintain and support various aspects of Information Technology, students can be sure that Softorix is just that sort of organization.
Main p roject list for csc it

Embedded systems , Instrumentation ,Electrical ,Automation ,Fire &safety ,Networking ,Java ,Dot Net ,Ms-Crm
Whitepaper - Software Defined Networking for the Telco Industry

is SDN (Software Defined Networking) the next big thing in Network Security, or another headache and potential skills gap for the next generation of business networks?
IRJET- A Novel Mechanism for Clone Attack Detection in Hybrid IoT Devices

This document proposes a new method called MDSClone for detecting clone attacks in hybrid IoT networks. MDSClone uses multidimensional scaling (MDS) to generate a network map based on relative distances between nodes, without requiring knowledge of node locations. This overcomes limitations of existing methods that rely on node geography or assume static networks. MDSClone can detect clones in hybrid networks containing both static and mobile nodes. It parallelizes parts of the detection process to speed up clone identification. The method is designed specifically for IoT environments where nodes may lack accurate location data and have varying mobility.
JAVA IEEE -2015

This document lists 96 Java projects from 2015 in various domains including cloud computing, data mining, networking, mobile computing, image processing, secure computing, parallel and distributed systems, and information forensics and security. The projects are numbered from J1501 to J1596 and have titles related to the corresponding domain such as "A Hybrid Cloud Approach for Secure Authorized Deduplication" and "Privacy-Preserving Public Auditing for Regenerating-Code-Based Cloud Storage". The document also provides contact information for the project provider.
IRJET- Technical Review of different Methods for Multi Factor Authentication

This document discusses various multi-factor authentication methods including smart cards, graphical passwords, risk assessment, mobile phone tokens, GPS location and timestamp, hand vein recognition, DNA recognition, and biometric authentication. It provides details on how each method works and evaluates factors like universality, uniqueness, collectability, performance and acceptability for multi-factor authentication. The document aims to review different technical approaches to implement multi-factor authentication for secure user identification.
IRJET- A Review on Colour Image Watermarking based on Wavelet and QR Decompos...

This document summarizes several digital watermarking techniques and applications. It discusses a proposed hybrid watermarking technique that combines redundant discrete wavelet transform with singular value decomposition. It also mentions using Arnold chaotic maps to scramble watermarks for added security. Several other watermarking methods are reviewed, including techniques in the pixel domain and using discrete cosine transform with singular value decomposition. Applications discussed include mobile experiences, biometric authentication, image processing, and cryptography.
Stamp enabling privacy preserving location proofs for mobile users

STAMP Enabling Privacy Preserving Location Proofs for Mobile Users
Web : http://www.lemenizinfotech.com
Web : http://ieeemaster.com
Web : http://www.lemenizinfotech.com/android-ieee-projects-2016-2017-2/
Web : http://ieeemaster.com/android-ieee-projects-2016-2017/
Address: 36, 100 Feet Road(Near Indira Gandhi Statue), Natesan Nagar, Pondicherry-605 005
Contact numbers: +91 95663 55386, 99625 88976 (0413) 420 5444
Mail : projects@lemenizinfotech.com
Mobile : 9566355386 / 9962588976
IEEE 2012 CSE & IT java_2012-13_titles

IEEE 2012 Projects,academic projects in .net,academic projects in java,b tech mini projects,btech projects,electrical projects for students,electronic engineering final year project,electronic engineering final year projects,electronic final year project,electronics students projects,embedded in chennai,embedded projects chennai,engineering final project,engineering final projects,engineering projects in chennai,engineering projects in java,final year embedded projects,final year engineering projects,final year engineering projects chennai,final year engineering projects in chennai,final year ieee projects chennai,final year it projects,final year project chennai,final year project in chennai,final year project in electronics,final year project of electronics,final year projects for it,final year projects for mca,final year projects in .net,final year projects in chennai,final year projects in electronics,final year projects in embedded systems,final year projects in it,final year projects on embedded systems,final year student project,final year student projects,ieee embedded projects,ieee projects,ieee projects chennai,ieee projects for mca,ieee projects in .net,ieee projects in chennai,ieee projects in java,ieee projects in vlsi,ieee projects on embedded systems,ieee projects titles,ieee students projects,mca academic projects,mca final project,mca final year project,mca final year project in chennai,mca projects,mca projects chennai,mca projects titles,project in vlsi,project of mca,projects for mca,projects in vlsi,student project chennai,student projects in java,vlsi in chennai,year projects,Real Time IEEE Projects,Live Projects,Embedded Live Projects,Power Electronics Projects,Power System Projects,ME Projects,M.Tech Projects,VLSI Final Year projects,Embedded final Year Projects,Real Time Embedded Projects,Real Time Software Projects,Live Java Projects,Dot net Projects in Chennai,.Net Projects,B.tech projects,BE Projects,Real Time Project MBA, Real Time Project BE,Project Work BE,Real Time Project MCA,Real Time Project BE Electronic,Computer Software Training Embedded Systems, Real Time Project,Computer Project Work,Real Time Project IT,Embedded Training,Real Time Project Me,Project Work Ieee Based,Real Time Project B Tech,Project Work MCA,Project Work Computer Science,Project Work M E,Engineering Project Consultants,Real Time Project MSC,Real Time Project M Tech,Real Time Project Bio Medical,Project Consultants For Electronic,Project Work B Tech,Real Time Project BE Electrical,Real Time Project Dot Net,Real Time Project BCA,Project Work M Phil,Real Time Project M Phil,Project Work Embedded System,Real Time Project Embedded System,Project Work M Tech,Project Engineering,Real Time Project Java,Real Time Project PHD,Project Work IT,Real Time Project Networking,Real Time Project BSc,Real Time Project Matlab,Computer Software Training Embedded Network,Project Work Java,Real Time Project Vlsi,Real Time Project Animation,Project Work HTML,Real
IRJET - Image Watermarking using QR Code

This document presents a technique for digital image watermarking using QR codes. It aims to provide copyright protection and authentication of digital images. The technique works by encrypting an image using AES encryption and embedding the encrypted data in a QR code. The QR code is then hidden behind a cover image using steganography. This makes it difficult for unauthorized users to detect the hidden watermark or tamper with the encrypted image data. The document discusses related work on image watermarking and steganography techniques. It also provides details of the proposed system architecture, classification of digital watermarking techniques, the AES encryption algorithm used, and potential applications of the presented image watermarking approach.
Inside TorrentLocker (Cryptolocker) Malware C&C Server 

CryptoLocker was a ransomware trojan which targeted computers running Microsoft Windows and was first observed by Dell SecureWorks in September 2013. CryptoLocker propagated via infected email attachments, and via an existing botnet; when activated, the malware encrypts certain types of files stored on local and mounted network drives using RSA public-key cryptography, with the private key stored only on the malware's control servers. The malware then displays a message, which offers to decrypt the data if a payment (through either Bitcoin or a pre-paid cash voucher) is made by a stated deadline, and threatened to delete the private key if the deadline passes. If the deadline is not met, the malware offered to decrypt data via an online service provided by the malware's operators, for a significantly higher price in Bitcoin
Explore the new 2014 TorrentLocker and get inside his C&C server
IRJET- A Survey on Private Messaging based on QR Code using Visual Secret Sha...

This document proposes a visual secret sharing scheme to encode secret QR codes into shares to improve security. The secret message is first encrypted then divided into shares that are encoded as valid QR codes. Only by recombining an authorized set of shares can the secret be recovered. This approach aims to resist attacks while maintaining the readability of QR codes. The proposed scheme is experimentally proven to be feasible and low cost. It could enhance the security of transmitting private information via QR codes.
Efficient algorithms for neighbor discovery in wireless networks

E1. The paper proposes and analyzes several algorithms for neighbor discovery in wireless networks. It presents an ALOHA-like algorithm for when nodes cannot detect collisions and a receiver feedback-based algorithm when they can.
E2. It then analyzes neighbor discovery in a multihop setting, establishing an upper bound on the running time of the ALOHA-like algorithm and a lower bound on the running time of any randomized algorithm.
E3. The paper aims to develop algorithms that do not require nodes to know the number of neighbors or be synchronized, and that allow asynchronous starting and determine when to terminate discovery.
Distributed cooperative caching in social wireless networks

This paper proposes cooperative caching strategies to minimize content provisioning costs in social wireless networks (SWNETs). SWNETs consist of mobile devices that share common interests in electronic content. The paper develops models of the network, services, and pricing, and uses these to create two caching strategies: Split Cache, which optimally places objects for networks with homogeneous demands, and Distributed Benefit, which minimizes costs for heterogeneous networks. Analytical and simulation results show that these strategies reduce costs. An Android prototype validates the results. Selfish user behaviors are also analyzed.
final year ieee projects in pondicherry

This document lists 71 IEEE projects from 2013 available for students through JP Infotech. The projects cover a wide range of domains including cloud computing, data mining, secure computing, networking, mobile computing, and more. They are designed to support students with journal and conference publications, document and presentation reviews, assignments, mock interviews, certification, and placement assistance. Students can also submit their own projects for support.
A highly scalable key pre distribution scheme for wireless sensor networks

This document proposes a new scalable key management scheme for wireless sensor networks (WSNs) using unital design theory. Existing key pre-distribution schemes suffer from low scalability or degraded performance metrics like storage overhead and resiliency for large networks. The proposed scheme aims to enhance scalability without degrading other metrics. It introduces a naive mapping from unital design to key pre-distribution showing high scalability. It also proposes an enhanced unital-based scheme maintaining good key sharing probability while further improving scalability. Analysis shows the approach outperforms existing schemes in criteria like storage overhead, energy consumption, scalability, and resiliency.
Back pressure-based packet-by-packet adaptive routing in communication networks

Back pressure-based packet-by-packet adaptive routing in communication networksJPINFOTECH JAYAPRAKASH
This document proposes a new adaptive routing algorithm built upon the widely studied back-pressure algorithm. It decouples the routing and scheduling components by designing a probabilistic routing table to route packets to per-destination queues, while scheduling decisions in wireless networks use "shadow queues". This reduces implementation complexity and delay compared to existing back-pressure algorithms. The approach can also optimize routing-coding tradeoffs in networks using simple network coding.Identity based secure distributed data storage schemes

This document proposes two identity-based secure distributed data storage schemes. The schemes allow a file owner to independently decide access permissions for receivers without help from a private key generator. When a receiver queries the system, they can only access one of the owner's files, not all files. The schemes also protect against collusion attacks where receivers cannot obtain the owner's secret key even if they compromise proxy servers. The first scheme provides confidentiality against chosen plaintext attacks, while the second achieves security against chosen ciphertext attacks. To the best of the authors' knowledge, this is the first scheme that allows file-level access control and protects against collusion attacks in the standard model.
2013 14 ieee ece project titles - jp infotech

EMBEDDED / ROBOTICS IEEE 2013 - 2014 IEEE PROJECT TITLES FOR STUDENTS B.E.,B.TECH.,M.E,M.TECH.,M.PHIL.,M.S.,MCA,M.S.,MBA AND DIPLOMA PROJECTS USING EMBEDDED / ROBOTICS
Privacy preserving delegated access control in public clouds

This document proposes a new approach called two layer encryption (TLE) to delegate fine-grained access control enforcement to public clouds while preserving data and user privacy. Under TLE, the data owner performs coarse-grained encryption and the cloud performs fine-grained re-encryption based on access control policies. This addresses limitations of existing approaches where the data owner must re-encrypt data whenever user credentials change. The TLE approach also keeps user identity attributes and data confidential from the cloud.
Proteus multiflow diversity routing for wireless networks with cooperative tr...

Proteus multiflow diversity routing for wireless networks with cooperative tr...JPINFOTECH JAYAPRAKASH
This paper proposes a routing protocol called Proteus for wireless networks using cooperative transmissions. Proteus aims to improve network performance by leveraging virtual MISO links through cooperative transmissions. It makes two key algorithmic decisions - the number of cooperating transmitters per link and the cooperation strategy. Proteus is evaluated using NS2 simulations and shown to improve throughput by 15-300% depending on node density by optimizing these decisions.IEEE PROJECTS FOR ECE 2013 2014

IEEE PROJECTS FOR ECE 2013 2014, 2013 - 2014 IEEE PROJECTS FOR ME,M.TECH,B.E,B.TECH BOTH SIMULATION AND HARDWARE PROJECT TITLES WITH LATEST TECHNIQUES AND CONCEPTS FOR FINAL YEAR STUDENT PROJECTS USING EMBEDDED AND ROBOTICS
More Related Content
What's hot
Main p roject list for csc it

Embedded systems , Instrumentation ,Electrical ,Automation ,Fire &safety ,Networking ,Java ,Dot Net ,Ms-Crm
Whitepaper - Software Defined Networking for the Telco Industry

is SDN (Software Defined Networking) the next big thing in Network Security, or another headache and potential skills gap for the next generation of business networks?
IRJET- A Novel Mechanism for Clone Attack Detection in Hybrid IoT Devices

This document proposes a new method called MDSClone for detecting clone attacks in hybrid IoT networks. MDSClone uses multidimensional scaling (MDS) to generate a network map based on relative distances between nodes, without requiring knowledge of node locations. This overcomes limitations of existing methods that rely on node geography or assume static networks. MDSClone can detect clones in hybrid networks containing both static and mobile nodes. It parallelizes parts of the detection process to speed up clone identification. The method is designed specifically for IoT environments where nodes may lack accurate location data and have varying mobility.
JAVA IEEE -2015

This document lists 96 Java projects from 2015 in various domains including cloud computing, data mining, networking, mobile computing, image processing, secure computing, parallel and distributed systems, and information forensics and security. The projects are numbered from J1501 to J1596 and have titles related to the corresponding domain such as "A Hybrid Cloud Approach for Secure Authorized Deduplication" and "Privacy-Preserving Public Auditing for Regenerating-Code-Based Cloud Storage". The document also provides contact information for the project provider.
IRJET- Technical Review of different Methods for Multi Factor Authentication

This document discusses various multi-factor authentication methods including smart cards, graphical passwords, risk assessment, mobile phone tokens, GPS location and timestamp, hand vein recognition, DNA recognition, and biometric authentication. It provides details on how each method works and evaluates factors like universality, uniqueness, collectability, performance and acceptability for multi-factor authentication. The document aims to review different technical approaches to implement multi-factor authentication for secure user identification.
IRJET- A Review on Colour Image Watermarking based on Wavelet and QR Decompos...

This document summarizes several digital watermarking techniques and applications. It discusses a proposed hybrid watermarking technique that combines redundant discrete wavelet transform with singular value decomposition. It also mentions using Arnold chaotic maps to scramble watermarks for added security. Several other watermarking methods are reviewed, including techniques in the pixel domain and using discrete cosine transform with singular value decomposition. Applications discussed include mobile experiences, biometric authentication, image processing, and cryptography.
Stamp enabling privacy preserving location proofs for mobile users

STAMP Enabling Privacy Preserving Location Proofs for Mobile Users
Web : http://www.lemenizinfotech.com
Web : http://ieeemaster.com
Web : http://www.lemenizinfotech.com/android-ieee-projects-2016-2017-2/
Web : http://ieeemaster.com/android-ieee-projects-2016-2017/
Address: 36, 100 Feet Road(Near Indira Gandhi Statue), Natesan Nagar, Pondicherry-605 005
Contact numbers: +91 95663 55386, 99625 88976 (0413) 420 5444
Mail : projects@lemenizinfotech.com
Mobile : 9566355386 / 9962588976
IEEE 2012 CSE & IT java_2012-13_titles

IEEE 2012 Projects,academic projects in .net,academic projects in java,b tech mini projects,btech projects,electrical projects for students,electronic engineering final year project,electronic engineering final year projects,electronic final year project,electronics students projects,embedded in chennai,embedded projects chennai,engineering final project,engineering final projects,engineering projects in chennai,engineering projects in java,final year embedded projects,final year engineering projects,final year engineering projects chennai,final year engineering projects in chennai,final year ieee projects chennai,final year it projects,final year project chennai,final year project in chennai,final year project in electronics,final year project of electronics,final year projects for it,final year projects for mca,final year projects in .net,final year projects in chennai,final year projects in electronics,final year projects in embedded systems,final year projects in it,final year projects on embedded systems,final year student project,final year student projects,ieee embedded projects,ieee projects,ieee projects chennai,ieee projects for mca,ieee projects in .net,ieee projects in chennai,ieee projects in java,ieee projects in vlsi,ieee projects on embedded systems,ieee projects titles,ieee students projects,mca academic projects,mca final project,mca final year project,mca final year project in chennai,mca projects,mca projects chennai,mca projects titles,project in vlsi,project of mca,projects for mca,projects in vlsi,student project chennai,student projects in java,vlsi in chennai,year projects,Real Time IEEE Projects,Live Projects,Embedded Live Projects,Power Electronics Projects,Power System Projects,ME Projects,M.Tech Projects,VLSI Final Year projects,Embedded final Year Projects,Real Time Embedded Projects,Real Time Software Projects,Live Java Projects,Dot net Projects in Chennai,.Net Projects,B.tech projects,BE Projects,Real Time Project MBA, Real Time Project BE,Project Work BE,Real Time Project MCA,Real Time Project BE Electronic,Computer Software Training Embedded Systems, Real Time Project,Computer Project Work,Real Time Project IT,Embedded Training,Real Time Project Me,Project Work Ieee Based,Real Time Project B Tech,Project Work MCA,Project Work Computer Science,Project Work M E,Engineering Project Consultants,Real Time Project MSC,Real Time Project M Tech,Real Time Project Bio Medical,Project Consultants For Electronic,Project Work B Tech,Real Time Project BE Electrical,Real Time Project Dot Net,Real Time Project BCA,Project Work M Phil,Real Time Project M Phil,Project Work Embedded System,Real Time Project Embedded System,Project Work M Tech,Project Engineering,Real Time Project Java,Real Time Project PHD,Project Work IT,Real Time Project Networking,Real Time Project BSc,Real Time Project Matlab,Computer Software Training Embedded Network,Project Work Java,Real Time Project Vlsi,Real Time Project Animation,Project Work HTML,Real
IRJET - Image Watermarking using QR Code

This document presents a technique for digital image watermarking using QR codes. It aims to provide copyright protection and authentication of digital images. The technique works by encrypting an image using AES encryption and embedding the encrypted data in a QR code. The QR code is then hidden behind a cover image using steganography. This makes it difficult for unauthorized users to detect the hidden watermark or tamper with the encrypted image data. The document discusses related work on image watermarking and steganography techniques. It also provides details of the proposed system architecture, classification of digital watermarking techniques, the AES encryption algorithm used, and potential applications of the presented image watermarking approach.
Inside TorrentLocker (Cryptolocker) Malware C&C Server 

CryptoLocker was a ransomware trojan which targeted computers running Microsoft Windows and was first observed by Dell SecureWorks in September 2013. CryptoLocker propagated via infected email attachments, and via an existing botnet; when activated, the malware encrypts certain types of files stored on local and mounted network drives using RSA public-key cryptography, with the private key stored only on the malware's control servers. The malware then displays a message, which offers to decrypt the data if a payment (through either Bitcoin or a pre-paid cash voucher) is made by a stated deadline, and threatened to delete the private key if the deadline passes. If the deadline is not met, the malware offered to decrypt data via an online service provided by the malware's operators, for a significantly higher price in Bitcoin
Explore the new 2014 TorrentLocker and get inside his C&C server
IRJET- A Survey on Private Messaging based on QR Code using Visual Secret Sha...

This document proposes a visual secret sharing scheme to encode secret QR codes into shares to improve security. The secret message is first encrypted then divided into shares that are encoded as valid QR codes. Only by recombining an authorized set of shares can the secret be recovered. This approach aims to resist attacks while maintaining the readability of QR codes. The proposed scheme is experimentally proven to be feasible and low cost. It could enhance the security of transmitting private information via QR codes.
What's hot (11)
Whitepaper - Software Defined Networking for the Telco Industry

Whitepaper - Software Defined Networking for the Telco Industry
IRJET- A Novel Mechanism for Clone Attack Detection in Hybrid IoT Devices

IRJET- A Novel Mechanism for Clone Attack Detection in Hybrid IoT Devices
IRJET- Technical Review of different Methods for Multi Factor Authentication

IRJET- Technical Review of different Methods for Multi Factor Authentication
IRJET- A Review on Colour Image Watermarking based on Wavelet and QR Decompos...

IRJET- A Review on Colour Image Watermarking based on Wavelet and QR Decompos...
Stamp enabling privacy preserving location proofs for mobile users

Stamp enabling privacy preserving location proofs for mobile users
Inside TorrentLocker (Cryptolocker) Malware C&C Server 

Inside TorrentLocker (Cryptolocker) Malware C&C Server
IRJET- A Survey on Private Messaging based on QR Code using Visual Secret Sha...

IRJET- A Survey on Private Messaging based on QR Code using Visual Secret Sha...
Viewers also liked
Efficient algorithms for neighbor discovery in wireless networks

E1. The paper proposes and analyzes several algorithms for neighbor discovery in wireless networks. It presents an ALOHA-like algorithm for when nodes cannot detect collisions and a receiver feedback-based algorithm when they can.
E2. It then analyzes neighbor discovery in a multihop setting, establishing an upper bound on the running time of the ALOHA-like algorithm and a lower bound on the running time of any randomized algorithm.
E3. The paper aims to develop algorithms that do not require nodes to know the number of neighbors or be synchronized, and that allow asynchronous starting and determine when to terminate discovery.
Distributed cooperative caching in social wireless networks

This paper proposes cooperative caching strategies to minimize content provisioning costs in social wireless networks (SWNETs). SWNETs consist of mobile devices that share common interests in electronic content. The paper develops models of the network, services, and pricing, and uses these to create two caching strategies: Split Cache, which optimally places objects for networks with homogeneous demands, and Distributed Benefit, which minimizes costs for heterogeneous networks. Analytical and simulation results show that these strategies reduce costs. An Android prototype validates the results. Selfish user behaviors are also analyzed.
final year ieee projects in pondicherry

This document lists 71 IEEE projects from 2013 available for students through JP Infotech. The projects cover a wide range of domains including cloud computing, data mining, secure computing, networking, mobile computing, and more. They are designed to support students with journal and conference publications, document and presentation reviews, assignments, mock interviews, certification, and placement assistance. Students can also submit their own projects for support.
A highly scalable key pre distribution scheme for wireless sensor networks

This document proposes a new scalable key management scheme for wireless sensor networks (WSNs) using unital design theory. Existing key pre-distribution schemes suffer from low scalability or degraded performance metrics like storage overhead and resiliency for large networks. The proposed scheme aims to enhance scalability without degrading other metrics. It introduces a naive mapping from unital design to key pre-distribution showing high scalability. It also proposes an enhanced unital-based scheme maintaining good key sharing probability while further improving scalability. Analysis shows the approach outperforms existing schemes in criteria like storage overhead, energy consumption, scalability, and resiliency.
Back pressure-based packet-by-packet adaptive routing in communication networks

Back pressure-based packet-by-packet adaptive routing in communication networksJPINFOTECH JAYAPRAKASH
This document proposes a new adaptive routing algorithm built upon the widely studied back-pressure algorithm. It decouples the routing and scheduling components by designing a probabilistic routing table to route packets to per-destination queues, while scheduling decisions in wireless networks use "shadow queues". This reduces implementation complexity and delay compared to existing back-pressure algorithms. The approach can also optimize routing-coding tradeoffs in networks using simple network coding.Identity based secure distributed data storage schemes

This document proposes two identity-based secure distributed data storage schemes. The schemes allow a file owner to independently decide access permissions for receivers without help from a private key generator. When a receiver queries the system, they can only access one of the owner's files, not all files. The schemes also protect against collusion attacks where receivers cannot obtain the owner's secret key even if they compromise proxy servers. The first scheme provides confidentiality against chosen plaintext attacks, while the second achieves security against chosen ciphertext attacks. To the best of the authors' knowledge, this is the first scheme that allows file-level access control and protects against collusion attacks in the standard model.
2013 14 ieee ece project titles - jp infotech

EMBEDDED / ROBOTICS IEEE 2013 - 2014 IEEE PROJECT TITLES FOR STUDENTS B.E.,B.TECH.,M.E,M.TECH.,M.PHIL.,M.S.,MCA,M.S.,MBA AND DIPLOMA PROJECTS USING EMBEDDED / ROBOTICS
Privacy preserving delegated access control in public clouds

This document proposes a new approach called two layer encryption (TLE) to delegate fine-grained access control enforcement to public clouds while preserving data and user privacy. Under TLE, the data owner performs coarse-grained encryption and the cloud performs fine-grained re-encryption based on access control policies. This addresses limitations of existing approaches where the data owner must re-encrypt data whenever user credentials change. The TLE approach also keeps user identity attributes and data confidential from the cloud.
Proteus multiflow diversity routing for wireless networks with cooperative tr...

Proteus multiflow diversity routing for wireless networks with cooperative tr...JPINFOTECH JAYAPRAKASH
This paper proposes a routing protocol called Proteus for wireless networks using cooperative transmissions. Proteus aims to improve network performance by leveraging virtual MISO links through cooperative transmissions. It makes two key algorithmic decisions - the number of cooperating transmitters per link and the cooperation strategy. Proteus is evaluated using NS2 simulations and shown to improve throughput by 15-300% depending on node density by optimizing these decisions.IEEE PROJECTS FOR ECE 2013 2014

IEEE PROJECTS FOR ECE 2013 2014, 2013 - 2014 IEEE PROJECTS FOR ME,M.TECH,B.E,B.TECH BOTH SIMULATION AND HARDWARE PROJECT TITLES WITH LATEST TECHNIQUES AND CONCEPTS FOR FINAL YEAR STUDENT PROJECTS USING EMBEDDED AND ROBOTICS
Participatory privacy enabling privacy in participatory sensing

The document discusses privacy issues in participatory sensing and proposes a privacy-enhanced participatory sensing infrastructure called PEPSI. Participatory sensing allows mobile users to share sensor data, but existing systems do not provide adequate privacy protections. PEPSI uses cryptographic tools to allow query/report matching by a service provider while guaranteeing privacy for mobile nodes and query submitters. It aims to provide provable privacy by design and defines clear privacy properties.
Network assisted mobile computing with optimal uplink query processing

1) The document proposes a network-assisted mobile computing system where mid-network nodes can lease processing power to mobile devices to reduce latency and battery usage when processing queries.
2) It studies the tradeoff between battery usage, processing latency, transmission latency, and leasing costs to determine the optimal processing policy for allocating work across devices.
3) The proposed system divides query processing across the mobile station, relay nodes, and application server to minimize costs based on leasing, latency, and battery usage considerations.
Toward fine grained, unsupervised, scalable performance diagnosis for product...

Toward fine grained, unsupervised, scalable performance diagnosis for product...JPINFOTECH JAYAPRAKASH
Toward fine grained, unsupervised, scalable performance diagnosis for production cloud computing systemsTowards secure multi keyword top-k retrieval over encrypted cloud data

The document proposes a two-round searchable encryption scheme to enable secure multi-keyword top-k retrieval over encrypted cloud data. Existing searchable encryption schemes only support boolean keyword search and do not consider relevance. The proposed Two-Round Searchable Encryption scheme uses homomorphic encryption and a vector space model to enable users to participate in ranking while most computation is done on the server side ciphertext only. This guarantees security without sacrificing efficiency.
Using fuzzy logic control to provide intelligent traffic management service f...

Using fuzzy logic control to provide intelligent traffic management service f...JPINFOTECH JAYAPRAKASH
This paper proposes a distributed traffic management framework that uses fuzzy logic control. Routers are deployed with intelligent data rate controllers to manage increasing internet traffic. Unlike other explicit traffic control protocols that estimate network parameters, the fuzzy logic controller can directly measure router queue size. This avoids issues from parameter estimation while reducing computation and memory usage. The queue size is used to proactively regulate source sending rates, increasing resilience to congestion. Simulation results show the new scheme achieves better performance than existing protocols relying on network parameter estimation.Facilitating document annotation using content and querying value

Facilitating document annotation using content and querying value
A rank correlation based detection against distributed reflection do s attacks

A rank correlation based detection against distributed reflection do s attacksJPINFOTECH JAYAPRAKASH
This document proposes a Rank Correlation Based Detection (RCD) algorithm to detect Distributed Reflection Denial of Service (DRDoS) attacks in a protocol-independent manner. RCD analyzes the inherent rank correlation between responsive traffic flows stimulated by the same attacking flow. Preliminary simulations show RCD can efficiently differentiate reflection flows from legitimate ones, providing a usable indicator for DRDoS detection. The algorithm uses Spearman's Rank Correlation as it is more suitable than Pearson's correlation for the nonlinear traffic patterns and outliers introduced during DRDoS attacks.Secure mining of association rules in horizontally distributed databases

This document proposes a new protocol for securely mining association rules from horizontally distributed databases. It summarizes an existing protocol from Kantarcioglu and Clifton, which leaks excess information. The proposed protocol uses novel secure multi-party algorithms to compute unions and test set inclusions privately. It offers enhanced privacy and is more efficient than the existing protocol in terms of communication rounds, cost, and computation.
Viewers also liked (19)
Efficient algorithms for neighbor discovery in wireless networks

Efficient algorithms for neighbor discovery in wireless networks
Distributed cooperative caching in social wireless networks

Distributed cooperative caching in social wireless networks
A highly scalable key pre distribution scheme for wireless sensor networks

A highly scalable key pre distribution scheme for wireless sensor networks
Back pressure-based packet-by-packet adaptive routing in communication networks

Back pressure-based packet-by-packet adaptive routing in communication networks
Identity based secure distributed data storage schemes

Identity based secure distributed data storage schemes
Privacy preserving delegated access control in public clouds

Privacy preserving delegated access control in public clouds
Proteus multiflow diversity routing for wireless networks with cooperative tr...

Proteus multiflow diversity routing for wireless networks with cooperative tr...
Participatory privacy enabling privacy in participatory sensing

Participatory privacy enabling privacy in participatory sensing
Network assisted mobile computing with optimal uplink query processing

Network assisted mobile computing with optimal uplink query processing
Toward fine grained, unsupervised, scalable performance diagnosis for product...

Toward fine grained, unsupervised, scalable performance diagnosis for product...
Towards secure multi keyword top-k retrieval over encrypted cloud data

Towards secure multi keyword top-k retrieval over encrypted cloud data
Using fuzzy logic control to provide intelligent traffic management service f...

Using fuzzy logic control to provide intelligent traffic management service f...
Facilitating document annotation using content and querying value

Facilitating document annotation using content and querying value
A rank correlation based detection against distributed reflection do s attacks

A rank correlation based detection against distributed reflection do s attacks
Secure mining of association rules in horizontally distributed databases

Secure mining of association rules in horizontally distributed databases
Similar to 2013 ieee java project titles for cse, it and mca
2013 IEEE PROJECT TITLES FOR CSE

2013 IEEE PROJECT TITLES FOR CSE, 2013-2014 IEEE PROJECT TITLES, IEEE PROJECTS IN PONDICHERRY, 2013 M.E. PROJECT TITLES, 2013 IEEE M.TECH. PROJECTS, 2013 IEEE MCA PROJECTS, 2013 IEEE M.PHIL PROJECTS, 2013 APPLICATION PROJECT TITLES
2013 2014 ieee dotnet project titles

DOT NET IEEE 2013 - 2014 IEEE PROJECT TITLES FOR STUDENTS B.E.,B.TECH.,M.E,M.TECH.,M.PHIL.,M.S.,MCA,M.S.,MBA AND DIPLOMA PROJECTS USING C#.NET, ASP.NET, .NET, DOTNET, DOT NET
2015 2016 ieee java project titles

2015 ieee projects, 2015 ieee java projects, 2015 ieee dotnet projects, 2015 ieee android projects, 2015 ieee matlab projects, 2015 ieee embedded projects, 2015 ieee robotics projects, 2015 ieee NS2 projects, 2015 IEEE EEE PROJECTS, 2015 IEEE POWER ELECTRONICS PROJECTS, bulk ieee projects 2015, 2015 me projects with future enhancement, ieee projects in chennai, ieee projects chennai, ieee project centers in chennai, ieee 2015 projects in chennai, ieee project chennai, ieee project center in chennai, best ieee project center in chennai, ieee 2015 projects for cse, 2015 ieee cse projects, 2015 ieee it projects, 2015 ieee ece projects, 2015 ieee mca projects, 2015 ieee mphil projects, pondicherry ieee projects, best project centre in pondicherry, bulk ieee projects, jpinfotech ieee projects, jp infotech pondicherry, latest ieee projects, ieee projects for mtech, ieee projects for btech, ieee projects for mphil, ieee projects for be, ieee projects, student projects, students ieee projects, ieee proejcts india, ms projects, bits pilani ms projects, uk ms projects, ms ieee projects, ieee android real time projects, 2015 mtech projects, 2015 mphil projects, 2015 ieee projects with source code, pondicherry mtech projects, jpinfotech ieee projects, ieee projects, 2015 ieee project source code, journal paper publication guidance, conference paper publication guidance, ieee project, free ieee project, ieee projects for students., 2015 ieee omnet++ projects, ieee 2015 oment++ project, innovative ieee projects, latest ieee projects, 2015 latest ieee projects, ieee cloud computing projects, 2015 ieee cloud computing projects, 2015 ieee networking projects, ieee networking projects, 2015 ieee data mining projects, ieee data mining projects, 2015 ieee network security projects, ieee network security projects, 2015 ieee image processing projects, ieee image processing projects, ieee parallel and distributed system projects, ieee information security projects, 2015 wireless networking projects ieee, 2015 ieee web service projects, ns2 projects in chennai, ieee 2015 vlsi projects
ieee projects 2015,ieee 2015 projects,ieee project 2015,2015 ieee projects,ieee projects for it 2015, ieee projects 2015-2015, ieee projects in 2015, ieee projects 2015 for it, ieee project titles 2015, ieee projects for 2015, 2015 ieee project titles, ieee 2015 project titles, latest ieee projects 2015, ieee dotnet projects 2015, ieee project in 2015, ieee projects for cse, ieee projects for cse 2015, ieee projects for cse 2015,
ieee projects 2015 for cse
ieee projects in chennai, ieee projects chennai, ieee project centers in chennai, ieee 2015 projects in chennai, ieee project chennai, ieee project center in chennai, best ieee project center in chennai, chennai ieee projects, final year ieee projects in chennai, best ieee project centres in chennai, ieee project centres in chennai, ieee project in chennai, ieee final year projects in chennai
VTU Final Year Engineering Project Title List for Computer Science Engineerin...

Zetta Networks is one of the pioneer in IT training companies in the country. Zetta Networks is providing quality education to IT Aspirants, Corporate giants, institutions. Zetta Networks is committed to create great software brains of high caliber, who stay ahead in technology way ahead of others.
2012 13 ieee java titles - jp infotech

2012 ieee projects, 2012 ieee java projects, 2012 ieee dotnet projects, 2012 ieee android projects, 2012 ieee matlab projects, 2012 ieee embedded projects, 2012 ieee robotics projects, 2012 IEEE EEE PROJECTS, 2012 IEEE POWER ELECTRONICS PROJECTS, ieee 2012 android projects, ieee 2012 java projects, ieee 2012 dotnet projects, 2012 ieee mtech projects, 2012 ieee btech projects, 2012 ieee be projects, ieee 2012 projects for cse, 2012 ieee cse projects, 2012 ieee it projects, 2012 ieee ece projects, 2012 ieee mca projects, 2012 ieee mphil projects, pondicherry ieee projects, best project centre in pondicherry, bulk ieee projects, jpinfotech ieee projects, jp infotech pondicherry, latest ieee projects, ieee projects for mtech, ieee projects for btech, ieee projects for mphil, ieee projects for be, ieee projects, student projects, students ieee projects, ieee proejcts india, ms projects, bits pilani ms projects, uk ms projects, ms ieee projects, ieee android real time projects, 2012 mtech projects, 2012 mphil projects, 2012 ieee projects with source code, pondicherry mtech projects, jpinfotech ieee projects, ieee projects, 2012 ieee project source code, journal paper publication guidance, conference paper publication guidance, ieee project, free ieee project, ieee projects for students., 2012 ieee omnet++ projects, ieee 2012 oment++ project, innovative ieee projects, latest ieee projects, 2012 latest ieee projects, ieee cloud computing projects, 2012 ieee cloud computing projects, 2012 ieee networking projects, ieee networking projects, 2012 ieee data mining projects, ieee data mining projects, 2012 ieee network security projects, ieee network security projects, 2012 ieee image processing projects, ieee image processing projects, ieee parallel and distributed system projects, ieee information security projects, 2012 wireless networking projects ieee, 2012 ieee web service projects, 2012 ieee soa projects, ieee 2012 vlsi projects
Java IEEE 2015 titles

SMART PRO TECHNOLOGIES provides a list of 48 Java projects completed in 2015 across various domains including data mining, cloud computing, networking, mobile computing, and secure computing. The projects address topics such as opinion mining, quality of service in cloud computing, keyword search, publish/subscribe systems, encrypted data search, denial of service attacks, wireless routing, and privacy techniques. SMART PRO TECHNOLOGIES is located in Kadapa, India and can be contacted by phone or email.
2013 ieee dotnet project titles - lans a informatics

Ieee projects 2013 Coimbatore ,2013 IEEE Projects for CSE ,2013 IEEE Projects for IT,2013 IEEE Projects for CSE/IT,IEEE Final Year Academic Projects,IEEE Final Year Academic Projects for CSE,IEEE Final Year Academic Projects for IT,
IEEE Final Year Academic Projects for CSE/IT,ieee projects 2013 for CSE ,ieee projects 2013 for IT,ieee projects 2013 for CSE in Coimbatore,ieee projects 2013 for IT in Coimbatore,Live Student Projects in Coimbatore,Best IEEE Projects in Coimbatore for Final Year Students ,Best IEEE Projects in Coimbatore for CSE ,Best IEEE Projects in Coimbatore for IT ,Best IEEE Projects in Coimbatore for CSE/IT,Best IEEE Projects in Coimbatore for Final Year CSE Students ,Best IEEE Projects in Coimbatore for Final Year IT Students ,Best IEEE Projects in Coimbatore for Final Year CSE / IT Students ,BE final year IEEE Projects 2013,BE CSE final year IEEE Projects 2013,BTECH final year IEEE Projects 2013,BTECH / IT final year IEEE Projects 2013,BE / BTECH final year IEEE Projects 2013,BE CSE /BTECH IT final year IEEE Projects 2013,ME final year IEEE Projects 2013,ME CSE final year IEEE Projects 2013,MTECH final year IEEE Projects 2013,MTECH / IT final year IEEE Projects 2013,ME / MTECH final year IEEE Projects 2013,ME CSE /MTECH IT final year IEEE Projects 2013,MCA final year ,IEEE Projects 2013,MCA final year projects 2013,BE final year IEEE Projects 2013,BE CSE final year IEEE Projects 2013,MSC IT ieee projects institutes in Coimbatore,
Book Finalized

This document provides an overview of project guidance and titles from Softorix Technologies Pvt. Ltd. for 2009. It introduces Java and .NET, and provides research paper titles in various domains like data mining, image processing, network security, and more. It also lists application oriented paper titles in Java and .NET with topics like file sharing, resource management, and fault prediction in object-oriented systems.
2013 14-java-project-titles-me-tech-pantech

We at Pantech ProEd provide assistance in academic projects based on IEEE standard journals and transactions. Our services cater to all the domains belonging to Circuit branches and Information and Communication engineering branches.
Our methodology of execution and delivery is state - of -art, in essence a professionally designed, intensively tested, work flow model is applied.
Our Project support services caters to the following courses,
1) B.E / B.Tech (EEE/ECE/CSE/IT)
2) M.E (Power Systems)
3) M.E (Power Electronics & Drives)
4) M.E (High Voltage Engineering)
5) M.E (Electrical Drives & Embedded Control)
6) M.E (Control & Instrumentation Engineering)
7) M.E (Embedded System Technologies)
8) M.E (Applied Electronics)
9) M.E (Communication Systems)
10) M.E (VLSI Design)
11) M.E (Medical Electronics)
12) M.E (CSE)
13) M.E (Software Engineering)
14) M.E (Multimedia Technology)
15) M.Tech (Information Technology)
16) M.C.A
17) M.E (Systems Engineering and Operations Research)
18) M.E (Communication and Networking)
19) M.E (Avionics)
20) M.E. (Mobile Pervasive and Computing)
21) M.E. (Network Engineering)
22) M.E (Computer & Communication)
2013 14-java-project-titles-me-tech-pantech

This document contains a list of 84 topics related to various fields including cloud computing, mobile computing, data engineering, artificial intelligence, and web services. Each topic is assigned a unique identifier code beginning with "PSJAV" along with a brief description. Contact information is also provided for Pantech ProEd Private Limited.
Networking java titles Adrit Solution

We are providing training on IEEE 2016-17 projects for Ph.D Scalars, M.Tech, B.E, MCA, BCA and Diploma students for
all branches for their academic projects.
For more details call us or watsapp us @ 7676768124 0r 9545252155
Email your base papers to "adritsolutions@gmail.co.in"
We are providing IEEE projects on
1) Cloud Computing, Data Mining, BigData Projects Using JAva
2) Image Processing and Video Procesing (MATLAB) , Signal Processing
3) NS2 (Wireless Sensor, MANET, VANET)
4) ANDRIOD APPS
5) JAVA, JEE, J2EE, J2ME
6) Mechanical Design projects
7) Embedded Systems and IoT Projects
8) VLSI- Verilog Projects (ModelSim and Xilinx using FPGA)
For More details Please Visit us at
Adrit Solutions
Near Maruthi Mandir
#42/5, 18th Cross, 21st Main
Vijaynagar
Bangalore.
2014 2015 ieee java projects titles list globalsoft technologies

To Get any Project for CSE, IT ECE, EEE Contact Me @ 09666155510, 09849539085 or mail us - ieeefinalsemprojects@gmail.com-Visit Our Website: www.globalsofttechnologies.org
Ieee 2014 2015 java projects titles list globalsoft technologies

To Get any Project for CSE, IT ECE, EEE Contact Me @ 09666155510, 09849539085 or mail us - ieeefinalsemprojects@gmail.com-Visit Our Website: www.globalsofttechnologies.org
Ieee 2014 2015 java projects titles list globalsoft technologies

To Get any Project for CSE, IT ECE, EEE Contact Me @ 09666155510, 09849539085 or mail us - ieeefinalsemprojects@gmail.com-Visit Our Website: www.globalsofttechnologies.org
2014 2015 ieee java projects titles list globalsoft technologies

To Get any Project for CSE, IT ECE, EEE Contact Me @ 09666155510, 09849539085 or mail us - ieeefinalsemprojects@gmail.com-Visit Our Website: www.globalsofttechnologies.org
2014 2015 ieee java projects titles list globalsoft technologies

The document lists 52 mobile computing projects and 63 cloud computing projects available from GlobalSoft Technologies. The projects are related to domains like mobile networks, wireless networks, cloud computing, and focus on technologies like Java. They address various topics such as energy efficiency, security, privacy, resource allocation, and more. Project codes start with GSTJCC for cloud computing projects and GSTJMC for mobile computing projects, followed by a number.
Ieee 2014 2015 java projects titles list globalsoft technologies

To Get any Project for CSE, IT ECE, EEE Contact Me @ 09666155510, 09849539085 or mail us - ieeefinalsemprojects@gmail.com-Visit Our Website: www.globalsofttechnologies.org
2014 2015 ieee java projects globalsoft technologies

To Get any Project for CSE, IT ECE, EEE Contact Me @ 09666155510, 09849539085 or mail us - ieeefinalsemprojects@gmail.com-Visit Our Website: www.finalyearprojects.org
2014 ieee java projects titles globalsoft technologies

To Get any Project for CSE, IT ECE, EEE Contact Me @ 09666155510, 09849539085 or mail us - ieeefinalsemprojects@gmail.com-Visit Our Website: www.finalyearprojects.org
2014 ieee java projects titles globalsoft technologies

To Get any Project for CSE, IT ECE, EEE Contact Me @ 09666155510, 09849539085 or mail us - ieeefinalsemprojects@gmail.com-Visit Our Website: www.finalyearprojects.org
Similar to 2013 ieee java project titles for cse, it and mca (20)
VTU Final Year Engineering Project Title List for Computer Science Engineerin...

VTU Final Year Engineering Project Title List for Computer Science Engineerin...
2013 ieee dotnet project titles - lans a informatics

2013 ieee dotnet project titles - lans a informatics
2014 2015 ieee java projects titles list globalsoft technologies

2014 2015 ieee java projects titles list globalsoft technologies
Ieee 2014 2015 java projects titles list globalsoft technologies

Ieee 2014 2015 java projects titles list globalsoft technologies
Ieee 2014 2015 java projects titles list globalsoft technologies

Ieee 2014 2015 java projects titles list globalsoft technologies
2014 2015 ieee java projects titles list globalsoft technologies

2014 2015 ieee java projects titles list globalsoft technologies
2014 2015 ieee java projects titles list globalsoft technologies

2014 2015 ieee java projects titles list globalsoft technologies
Ieee 2014 2015 java projects titles list globalsoft technologies

Ieee 2014 2015 java projects titles list globalsoft technologies
2014 2015 ieee java projects globalsoft technologies

2014 2015 ieee java projects globalsoft technologies
2014 ieee java projects titles globalsoft technologies

2014 ieee java projects titles globalsoft technologies
2014 ieee java projects titles globalsoft technologies

2014 ieee java projects titles globalsoft technologies
Recently uploaded
Natural birth techniques - Mrs.Akanksha Trivedi Rama University

Natural birth techniques - Mrs.Akanksha Trivedi Rama UniversityAkanksha trivedi rama nursing college kanpur.
Natural birth techniques are various type such as/ water birth , alexender method, hypnosis, bradley method, lamaze method etcBBR 2024 Summer Sessions Interview Training

Qualitative research interview training by Professor Katrina Pritchard and Dr Helen Williams
Exploiting Artificial Intelligence for Empowering Researchers and Faculty, In...

Exploiting Artificial Intelligence for Empowering Researchers and Faculty, In...Dr. Vinod Kumar Kanvaria
Exploiting Artificial Intelligence for Empowering Researchers and Faculty,
International FDP on Fundamentals of Research in Social Sciences
at Integral University, Lucknow, 06.06.2024
By Dr. Vinod Kumar KanvariaBÀI TẬP BỔ TRỢ TIẾNG ANH 8 CẢ NĂM - GLOBAL SUCCESS - NĂM HỌC 2023-2024 (CÓ FI...

BÀI TẬP BỔ TRỢ TIẾNG ANH 8 CẢ NĂM - GLOBAL SUCCESS - NĂM HỌC 2023-2024 (CÓ FI...Nguyen Thanh Tu Collection
https://app.box.com/s/y977uz6bpd3af4qsebv7r9b7s21935vdISO/IEC 27001, ISO/IEC 42001, and GDPR: Best Practices for Implementation and...

Denis is a dynamic and results-driven Chief Information Officer (CIO) with a distinguished career spanning information systems analysis and technical project management. With a proven track record of spearheading the design and delivery of cutting-edge Information Management solutions, he has consistently elevated business operations, streamlined reporting functions, and maximized process efficiency.
Certified as an ISO/IEC 27001: Information Security Management Systems (ISMS) Lead Implementer, Data Protection Officer, and Cyber Risks Analyst, Denis brings a heightened focus on data security, privacy, and cyber resilience to every endeavor.
His expertise extends across a diverse spectrum of reporting, database, and web development applications, underpinned by an exceptional grasp of data storage and virtualization technologies. His proficiency in application testing, database administration, and data cleansing ensures seamless execution of complex projects.
What sets Denis apart is his comprehensive understanding of Business and Systems Analysis technologies, honed through involvement in all phases of the Software Development Lifecycle (SDLC). From meticulous requirements gathering to precise analysis, innovative design, rigorous development, thorough testing, and successful implementation, he has consistently delivered exceptional results.
Throughout his career, he has taken on multifaceted roles, from leading technical project management teams to owning solutions that drive operational excellence. His conscientious and proactive approach is unwavering, whether he is working independently or collaboratively within a team. His ability to connect with colleagues on a personal level underscores his commitment to fostering a harmonious and productive workplace environment.
Date: May 29, 2024
Tags: Information Security, ISO/IEC 27001, ISO/IEC 42001, Artificial Intelligence, GDPR
-------------------------------------------------------------------------------
Find out more about ISO training and certification services
Training: ISO/IEC 27001 Information Security Management System - EN | PECB
ISO/IEC 42001 Artificial Intelligence Management System - EN | PECB
General Data Protection Regulation (GDPR) - Training Courses - EN | PECB
Webinars: https://pecb.com/webinars
Article: https://pecb.com/article
-------------------------------------------------------------------------------
For more information about PECB:
Website: https://pecb.com/
LinkedIn: https://www.linkedin.com/company/pecb/
Facebook: https://www.facebook.com/PECBInternational/
Slideshare: http://www.slideshare.net/PECBCERTIFICATION
Community pharmacy- Social and preventive pharmacy UNIT 5

Covered community pharmacy topic of the subject Social and preventive pharmacy for Diploma and Bachelor of pharmacy
LAND USE LAND COVER AND NDVI OF MIRZAPUR DISTRICT, UP

This Dissertation explores the particular circumstances of Mirzapur, a region located in the
core of India. Mirzapur, with its varied terrains and abundant biodiversity, offers an optimal
environment for investigating the changes in vegetation cover dynamics. Our study utilizes
advanced technologies such as GIS (Geographic Information Systems) and Remote sensing to
analyze the transformations that have taken place over the course of a decade.
The complex relationship between human activities and the environment has been the focus
of extensive research and worry. As the global community grapples with swift urbanization,
population expansion, and economic progress, the effects on natural ecosystems are becoming
more evident. A crucial element of this impact is the alteration of vegetation cover, which plays a
significant role in maintaining the ecological equilibrium of our planet.Land serves as the foundation for all human activities and provides the necessary materials for
these activities. As the most crucial natural resource, its utilization by humans results in different
'Land uses,' which are determined by both human activities and the physical characteristics of the
land.
The utilization of land is impacted by human needs and environmental factors. In countries
like India, rapid population growth and the emphasis on extensive resource exploitation can lead
to significant land degradation, adversely affecting the region's land cover.
Therefore, human intervention has significantly influenced land use patterns over many
centuries, evolving its structure over time and space. In the present era, these changes have
accelerated due to factors such as agriculture and urbanization. Information regarding land use and
cover is essential for various planning and management tasks related to the Earth's surface,
providing crucial environmental data for scientific, resource management, policy purposes, and
diverse human activities.
Accurate understanding of land use and cover is imperative for the development planning
of any area. Consequently, a wide range of professionals, including earth system scientists, land
and water managers, and urban planners, are interested in obtaining data on land use and cover
changes, conversion trends, and other related patterns. The spatial dimensions of land use and
cover support policymakers and scientists in making well-informed decisions, as alterations in
these patterns indicate shifts in economic and social conditions. Monitoring such changes with the
help of Advanced technologies like Remote Sensing and Geographic Information Systems is
crucial for coordinated efforts across different administrative levels. Advanced technologies like
Remote Sensing and Geographic Information Systems
9
Changes in vegetation cover refer to variations in the distribution, composition, and overall
structure of plant communities across different temporal and spatial scales. These changes can
occur natural.
বাংলাদেশ অর্থনৈতিক সমীক্ষা (Economic Review) ২০২৪ UJS App.pdf

বাংলাদেশের অর্থনৈতিক সমীক্ষা ২০২৪ [Bangladesh Economic Review 2024 Bangla.pdf] কম্পিউটার , ট্যাব ও স্মার্ট ফোন ভার্সন সহ সম্পূর্ণ বাংলা ই-বুক বা pdf বই " সুচিপত্র ...বুকমার্ক মেনু 🔖 ও হাইপার লিংক মেনু 📝👆 যুক্ত ..
আমাদের সবার জন্য খুব খুব গুরুত্বপূর্ণ একটি বই ..বিসিএস, ব্যাংক, ইউনিভার্সিটি ভর্তি ও যে কোন প্রতিযোগিতা মূলক পরীক্ষার জন্য এর খুব ইম্পরট্যান্ট একটি বিষয় ...তাছাড়া বাংলাদেশের সাম্প্রতিক যে কোন ডাটা বা তথ্য এই বইতে পাবেন ...
তাই একজন নাগরিক হিসাবে এই তথ্য গুলো আপনার জানা প্রয়োজন ...।
বিসিএস ও ব্যাংক এর লিখিত পরীক্ষা ...+এছাড়া মাধ্যমিক ও উচ্চমাধ্যমিকের স্টুডেন্টদের জন্য অনেক কাজে আসবে ...
The simplified electron and muon model, Oscillating Spacetime: The Foundation...

Discover the Simplified Electron and Muon Model: A New Wave-Based Approach to Understanding Particles delves into a groundbreaking theory that presents electrons and muons as rotating soliton waves within oscillating spacetime. Geared towards students, researchers, and science buffs, this book breaks down complex ideas into simple explanations. It covers topics such as electron waves, temporal dynamics, and the implications of this model on particle physics. With clear illustrations and easy-to-follow explanations, readers will gain a new outlook on the universe's fundamental nature.
How to Manage Your Lost Opportunities in Odoo 17 CRM

Odoo 17 CRM allows us to track why we lose sales opportunities with "Lost Reasons." This helps analyze our sales process and identify areas for improvement. Here's how to configure lost reasons in Odoo 17 CRM
How to Build a Module in Odoo 17 Using the Scaffold Method

Odoo provides an option for creating a module by using a single line command. By using this command the user can make a whole structure of a module. It is very easy for a beginner to make a module. There is no need to make each file manually. This slide will show how to create a module using the scaffold method.
How to Make a Field Mandatory in Odoo 17

In Odoo, making a field required can be done through both Python code and XML views. When you set the required attribute to True in Python code, it makes the field required across all views where it's used. Conversely, when you set the required attribute in XML views, it makes the field required only in the context of that particular view.
Walmart Business+ and Spark Good for Nonprofits.pdf

"Learn about all the ways Walmart supports nonprofit organizations.
You will hear from Liz Willett, the Head of Nonprofits, and hear about what Walmart is doing to help nonprofits, including Walmart Business and Spark Good. Walmart Business+ is a new offer for nonprofits that offers discounts and also streamlines nonprofits order and expense tracking, saving time and money.
The webinar may also give some examples on how nonprofits can best leverage Walmart Business+.
The event will cover the following::
Walmart Business + (https://business.walmart.com/plus) is a new shopping experience for nonprofits, schools, and local business customers that connects an exclusive online shopping experience to stores. Benefits include free delivery and shipping, a 'Spend Analytics” feature, special discounts, deals and tax-exempt shopping.
Special TechSoup offer for a free 180 days membership, and up to $150 in discounts on eligible orders.
Spark Good (walmart.com/sparkgood) is a charitable platform that enables nonprofits to receive donations directly from customers and associates.
Answers about how you can do more with Walmart!"
Recently uploaded (20)
Natural birth techniques - Mrs.Akanksha Trivedi Rama University

Natural birth techniques - Mrs.Akanksha Trivedi Rama University
Exploiting Artificial Intelligence for Empowering Researchers and Faculty, In...

Exploiting Artificial Intelligence for Empowering Researchers and Faculty, In...
BÀI TẬP BỔ TRỢ TIẾNG ANH 8 CẢ NĂM - GLOBAL SUCCESS - NĂM HỌC 2023-2024 (CÓ FI...

BÀI TẬP BỔ TRỢ TIẾNG ANH 8 CẢ NĂM - GLOBAL SUCCESS - NĂM HỌC 2023-2024 (CÓ FI...
ISO/IEC 27001, ISO/IEC 42001, and GDPR: Best Practices for Implementation and...

ISO/IEC 27001, ISO/IEC 42001, and GDPR: Best Practices for Implementation and...
Community pharmacy- Social and preventive pharmacy UNIT 5

Community pharmacy- Social and preventive pharmacy UNIT 5
LAND USE LAND COVER AND NDVI OF MIRZAPUR DISTRICT, UP

LAND USE LAND COVER AND NDVI OF MIRZAPUR DISTRICT, UP
বাংলাদেশ অর্থনৈতিক সমীক্ষা (Economic Review) ২০২৪ UJS App.pdf

বাংলাদেশ অর্থনৈতিক সমীক্ষা (Economic Review) ২০২৪ UJS App.pdf
Digital Artefact 1 - Tiny Home Environmental Design

Digital Artefact 1 - Tiny Home Environmental Design
The simplified electron and muon model, Oscillating Spacetime: The Foundation...

The simplified electron and muon model, Oscillating Spacetime: The Foundation...
How to Manage Your Lost Opportunities in Odoo 17 CRM

How to Manage Your Lost Opportunities in Odoo 17 CRM
How to Build a Module in Odoo 17 Using the Scaffold Method

How to Build a Module in Odoo 17 Using the Scaffold Method
Pride Month Slides 2024 David Douglas School District

Pride Month Slides 2024 David Douglas School District
Walmart Business+ and Spark Good for Nonprofits.pdf

Walmart Business+ and Spark Good for Nonprofits.pdf
2013 ieee java project titles for cse, it and mca
- 1. SOFTWARE DEVELOPMENT & RESEARCH DIVISION Contact: R.JAYAPRAKASH BE,MBA,M.Tech.(Ph.D.), Mobile: (0)9952649690 Web: www.jpinfotech.org | Blog: www.jpinfotech.blogspot.com | Email: jpinfotechprojects@gmail.com 2012012012013333 ---- 2014201420142014 IEEE ProjectsIEEE ProjectsIEEE ProjectsIEEE Projects @@@@ JP iNFOTeCHJP iNFOTeCHJP iNFOTeCHJP iNFOTeCH S.NO Project Code IEEE 2013 Project Titles Domain Lang/Year JAVAJAVAJAVAJAVA 1 JPJ1301 A Stochastic Model to Investigate Data Center Performance and QoS in IaaS Cloud Computing Systems CLOUD COMPUTING JAVA/2013 2 JPJ1302 CloudMoV: Cloud-based Mobile Social TV CLOUD COMPUTING JAVA/2013 3 JPJ1303 Dynamic Resource Allocation Using Virtual Machines for Cloud Computing Environment CLOUD COMPUTING JAVA/2013 4 JPJ1304 Error-Tolerant Resource Allocation and Payment Minimization for Cloud System CLOUD COMPUTING JAVA/2013 5 JPJ1305 Harnessing the Cloud for Securely Outsourcing Large-Scale Systems of Linear Equations CLOUD COMPUTING JAVA/2013 6 JPJ1306 Mona: Secure Multi-Owner Data Sharing for Dynamic Groups in the Cloud CLOUD COMPUTING JAVA/2013 7 JPJ1307 PACK: Prediction-Based Cloud Bandwidth and Cost Reduction System CLOUD COMPUTING JAVA/2013 8 JPJ1308 Privacy-Preserving Public Auditing for Secure Cloud Storage CLOUD COMPUTING JAVA/2013 9 JPJ1309 Scalable and Secure Sharing of Personal Health Records in Cloud Computing Using Attribute-Based Encryption CLOUD COMPUTING JAVA/2013 10 JPJ1310 Enabling Dynamic Data and Indirect Mutual Trust for Cloud Computing Storage Systems CLOUD COMPUTING JAVA/2013 11 JPJ1311 A Fast Clustering-Based Feature Subset Selection Algorithm for High-Dimensional Data DATA MINING JAVA/2013
- 2. SOFTWARE DEVELOPMENT & RESEARCH DIVISION Contact: R.JAYAPRAKASH BE,MBA,M.Tech.(Ph.D.), Mobile: (0)9952649690 Web: www.jpinfotech.org | Blog: www.jpinfotech.blogspot.com | Email: jpinfotechprojects@gmail.com 12 JPJ1312 A New Algorithm for Inferring User Search Goals with Feedback Sessions DATA MINING JAVA/2013 13 JPJ1313 Annotating Search Results from Web Databases DATA MINING JAVA/2013 14 JPJ1314 Anomaly Detection via Online Over-Sampling Principal Component Analysis DATA MINING JAVA/2013 15 JPJ1315 Distributed Processing of Probabilistic Top-k Queries in Wireless Sensor Networks DATA MINING JAVA/2013 16 JPJ1316 m-Privacy for Collaborative Data Publishing DATA MINING JAVA/2013 17 JPJ1317 Protecting Sensitive Labels in Social Network Data Anonymization DATA MINING JAVA/2013 18 JPJ1318 Tweet Analysis for Real-Time Event Detection and Earthquake Reporting System Development DATA MINING JAVA/2013 19 JPJ1319 EAACK—A Secure Intrusion-Detection System for MANETs SECURE COMPUTING JAVA/2013 20 JPJ1320 Identity-Based Secure Distributed Data Storage Schemes SECURE COMPUTING JAVA/2013 21 JPJ1321 Modeling the Pairwise Key Predistribution Scheme in the Presence of Unreliable Links SECURE COMPUTING JAVA/2013 22 JPJ1322 NICE: Network Intrusion Detection and Countermeasure Selection in Virtual Network Systems SECURE COMPUTING JAVA/2013 23 JPJ1323 Privacy Preserving Data Sharing With Anonymous ID Assignment SECURE COMPUTING JAVA/2013 24 JPJ1324 Securing Class Initialization in Java-like Languages SECURE COMPUTING JAVA/2013 25 JPJ1325 Security Analysis of a Single Sign-On Mechanism for Distributed Computer Networks SECURE COMPUTING JAVA/2013
- 3. SOFTWARE DEVELOPMENT & RESEARCH DIVISION Contact: R.JAYAPRAKASH BE,MBA,M.Tech.(Ph.D.), Mobile: (0)9952649690 Web: www.jpinfotech.org | Blog: www.jpinfotech.blogspot.com | Email: jpinfotechprojects@gmail.com 26 JPJ1326 SORT: A Self-ORganizing Trust Model for Peer-to-Peer Systems SECURE COMPUTING JAVA/2013 27 JPJ1327 WARNINGBIRD: A Near Real-time Detection System for Suspicious URLs in Twitter Stream SECURE COMPUTING JAVA/2013 28 JPJ1328 A Highly Scalable Key Pre-Distribution Scheme for Wireless Sensor Networks NETWORKING JAVA/2013 29 JPJ1329 Delay-Based Network Utility Maximization NETWORKING JAVA/2013 30 JPJ1330 Dynamic Control of Coding for Progressive Packet Arrivals in DTNs NETWORKING JAVA/2013 31 JPJ1331 A Secure Protocol for Spontaneous Wireless Ad Hoc Networks Creation PARALLEL & DISTRIBUTED SYSTEMS JAVA/2013 32 JPJ1332 Security Analysis of a Privacy-Preserving Decentralized Key-Policy Attribute-Based Encryption Scheme PARALLEL & DISTRIBUTED SYSTEMS JAVA/2013 33 JPJ1333 IP-Geolocation Mapping for Moderately Connected Internet Regions PARALLEL & DISTRIBUTED SYSTEMS JAVA/2013 34 JPJ1334 Optimal Client-Server Assignment for Internet Distributed Systems PARALLEL & DISTRIBUTED SYSTEMS JAVA/2013 35 JPJ1335 Content Sharing over Smartphone-Based Delay-Tolerant Networks MOBILE COMPUTING JAVA/2013 36 JPJ1336 DCIM: Distributed Cache Invalidation Method for Maintaining Cache Consistency in Wireless Mobile Networks MOBILE COMPUTING JAVA/2013 37 JPJ1337 Discovery and Verification of Neighbor Positions in Mobile Ad Hoc Networks MOBILE COMPUTING JAVA/2013 38 JPJ1338 Efficient Rekeying Framework for Secure Multicast with Diverse- Subscription-Period Mobile Users MOBILE COMPUTING JAVA/2013 39 JPJ1339 A Framework for Mining Signatures from Event Sequences and Its Applications in Healthcare Data PATTERN ANALYSIS & MACHINE JAVA/2013
- 4. SOFTWARE DEVELOPMENT & RESEARCH DIVISION Contact: R.JAYAPRAKASH BE,MBA,M.Tech.(Ph.D.), Mobile: (0)9952649690 Web: www.jpinfotech.org | Blog: www.jpinfotech.blogspot.com | Email: jpinfotechprojects@gmail.com INTELLIGENCE 40 JPJ1340 A Decentralized Service Discovery Approach on Peer-to-Peer Networks SERVICE COMPUTING (WEB SERVICE) JAVA/2013 41 JPJ1341 Personalized QoS-Aware Web Service Recommendation and Visualization SERVICE COMPUTING (WEB SERVICE) JAVA/2013 42 JPJ1342 Privacy-Enhanced Web Service Composition SERVICE COMPUTING (WEB SERVICE) JAVA/2013 43 JPJ1343 Whole Test Suite Generation SOFTWARE ENGINEERING JAVA/2013 44 JPJ1344 A Load Balancing Model Based on Cloud Partitioning for the Public Cloud CLOUD COMPUTING JAVA/2013 45 JPJ1345 Document Clustering for Forensic Analysis: An Approach for Improving Computer Inspection DATA MINING JAVA/2013 46 JPJ1346 A Method for Mining Infrequent Causal Associations and Its Application in Finding Adverse Drug Reaction Signal Pairs DATA MINING JAVA/2013 47 JPJ1347 Clustering Sentence-Level Text Using a Novel Fuzzy Relational Clustering Algorithm DATA MINING JAVA/2013 48 JPJ1348 Two tales of privacy in online social networks SECURE COMPUTING JAVA/2013 49 JPJ1349 Minimum Cost Blocking Problem in Multi-path Wireless Routing Protocols NETWORKING JAVA/2013 50 JPJ1350 On the Node Clone Detection in Wireless Sensor Networks NETWORKING JAVA/2013 51 JPJ1351 Opportunistic MANETs: Mobility Can Make Up for Low Transmission Power NETWORKING JAVA/2013 52 JPJ1352 Back-Pressure-Based Packet-by-Packet Adaptive Routing in Communication Networks NETWORKING JAVA/2013 53 JPJ1353 Fast Transmission to Remote Cooperative Groups: A New Key Management Paradigm NETWORKING JAVA/2013 54 JPJ1354 Load Rebalancing for Distributed File Systems in Clouds CLOUD COMPUTING JAVA/2013 JPJ1355 Toward a Statistical Framework for Source Anonymity in Sensor MOBILE COMPUTING JAVA/2013
- 5. SOFTWARE DEVELOPMENT & RESEARCH DIVISION Contact: R.JAYAPRAKASH BE,MBA,M.Tech.(Ph.D.), Mobile: (0)9952649690 Web: www.jpinfotech.org | Blog: www.jpinfotech.blogspot.com | Email: jpinfotechprojects@gmail.com 55 Networks 56 JPJ1356 Mobile Relay Configuration in Data-Intensive Wireless Sensor Networks MOBILE COMPUTING JAVA/2013 57 JPJ1357 Vampire Attacks: Draining Life from Wireless Ad Hoc Sensor Networks MOBILE COMPUTING JAVA/2013 58 JPJ1358 Crowdsourcing Predictors of Behavioral Outcomes DATA MINING JAVA/2013 59 JPJ1359 Optimizing Cloud Resources for Delivering IPTV Services Through Virtualization CLOUD COMPUTING JAVA/2013 60 JPJ1360 Participatory Privacy: Enabling Privacy in Participatory Sensing NETWORKING JAVA/2013 61 JPJ1361 Secure Encounter-based Mobile Social Networks: Requirements, Designs, and Tradeoffs SECURE COMPUTING JAVA/2013 62 JPJ1362 Facilitating Document Annotation using Content and Querying Value DATA MINING JAVA/2013 63 JPJ1363 Privacy Preserving Delegated Access Control in Public Clouds CLOUD COMPUTING JAVA/2013 64 JPJ1364 Twitsper: Tweeting Privately SECURE COMPUTING JAVA/2013 65 JPJ1365 A Generalized Flow-Based Method for Analysis of Implicit Relationships on Wikipedia DATA MINING JAVA/2013 66 JPJ1366 A System to Filter Unwanted Messages from OSN User Walls DATA MINING JAVA/2013 67 JPJ1367 Anonymization of Centralized and Distributed Social Networks by Sequential Clustering DATA MINING JAVA/2013 68 JPJ1368 Toward Privacy Preserving and Collusion Resistance in a Location Proof Updating System MOBILE COMPUTING JAVA/2013 69 JPJ1369 Understanding the External Links of Video Sharing Sites: Measurement and Analysis MULTIMEDIA JAVA/2013 70 JPJ1370 Intrusion Detection Technique by using K-means, Fuzzy Neural Network and SVM classifiers. DATA MINING (CONFERENCE) JAVA/2013 71 JPJ1371 Combining Cryptographic Primitives to Prevent Jamming Attacks in Wireless Networks SECURE COMPUTING (CONFERENCE) JAVA/2013
- 6. SOFTWARE DEVELOPMENT & RESEARCH DIVISION Contact: R.JAYAPRAKASH BE,MBA,M.Tech.(Ph.D.), Mobile: (0)9952649690 Web: www.jpinfotech.org | Blog: www.jpinfotech.blogspot.com | Email: jpinfotechprojects@gmail.com PROJECT SUPPORTS FOR STUDENTS: JOURNAL PUBLICATIONS / CONFERENCE PUBLICATIONS REVIEW DOCUMENTS AND PPTS 100% LIVE EXPLANATION PROJECT ASSIGNMENTS VIVA-VOCE QUESTIONS & ANSWERS VALID TRAINEE CERTIFICATION 100% PLACEMENT SUPPORT Own Projects are also welcomed.
