Ieee 2012 dot net projects list
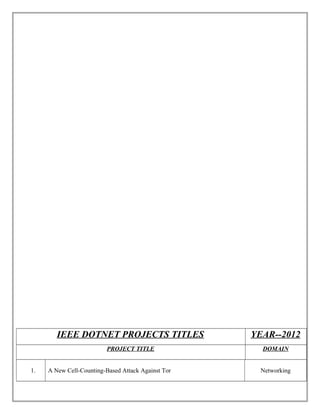
- 1. IEEE DOTNET PROJECTS TITLES YEAR--2012 PROJECT TITLE DOMAIN 1. A New Cell-Counting-Based Attack Against Tor Networking
- 2. 2. Defenses Against Large Scale Online Password Guessing Attacks By Using Persuasive Click Points Data Mining 3. A Novel Anti Phishing Framework Based On Visual Cryptography Distributed And Parallel Systems 4. A Probabilistic Model Of Visual Cryptography Scheme With Dynamic Group Information Forensics And Security
- 3. 5. A Query Formulation Language For The Data Web Data Mining 6. A Secure Erasure Code-Based Cloud Storage System With Secure Data Forwarding Parallel And Distributed Systems 7. Ample: An Adaptive Traffic Engineering System Based On Virtual Routing Topologies Networking
- 4. 8. Automatic Reconfiguration For Large-Scale Reliable Storage Systems Dependable And Secure Computing 9. Automatic Reconfiguration For Large-Scale Reliable Storage Systems Dependable And Secure Computing 10. Catching Packet Droppers And Modifiers In Wireless Sensor Networks Parallel And Distributed Systems
- 5. 11. Cloud Computing Security: From Single To Multi-Clouds System Sciences 12. Cooperative Download In Vehicular Environments Mobile Computing 13. Design And Implementation Of Tarf: A Trust-Aware Routing Framework For Wsns Dependable And Secure Computing
- 6. 14. Distributed Throughput Maximization In Wireless Networks Via Random Power Allocation Mobile Computing 15. Efficient Audit Service Outsourcing For Data Integrity In Clouds Cloud Computing 16. Enhanced Data Security Model For Cloud Computing Cloud And Mobile Computing
- 7. 17. Ensuring Distributed Accountability For Data Sharing In The Cloud Dependable And Secure Computing 18. Es-Mpich2: A Message Passing Interface With Enhanced Security Dependable And Secure Computing 19. Efficient Multidimensional Fuzzy Search For Personal Information Management Systems Data Mining
- 8. 20. Fairtorrent: A Deficit-Based Distributed Algorithm To Ensure Fairness In Peer-To-Peer Systems Networking 21. Grouping-Enhanced Resilient Probabilistic En-Route Filtering Of Injected False Data In Wsns Parallel And Distributed Systems, 22. Hasbe: A Hierarchical Attribute-Based Solution For Flexible And Scalable Access Control In Cloud Computing Information Forensics And Security
- 9. 23. Horizontal Aggregations In Sql To Prepare Data Sets For Data Mining Analysis Data Mining 24. Improving Aggregate Recommendation Diversity Using Ranking-Based Techniques Data Mining 25. Mining Web Graphs For Recommendations Data Mining
- 10. 26. Multiple Exposure Fusion For High Dynamic Range Image Acquisition Image Processing 27. On The Security And Efficiency Of Content Distribution Via Network Coding Dependable And Secure Computing 28. Optimal Power Allocation In Multi-Relay Mimo Cooperative Networks: Theory And Algorithms Selected Areas In Communications
- 11. 29. Optimal Source-Based Filtering Of Malicious Traffic Networking 30. Organizing User Search Histories Data Mining 31. Outsourced Similarity Search On Metric Data Assets Data Mining
- 12. 32. Protecting Location Privacy In Sensor Networks Against A Global Eavesdropper Mobile Computing, 33. Query Planning For Continuous Aggregation Queries Over A Network Of Data Aggregators Data Mining 34. Revisiting Defenses Against Large-Scale Online Password Guessing Attacks Dependable And Secure Computing
- 13. 35. Scalable Learning Of Collective Behavior Data Mining 36. Secure And Efficient Handover Authentication Based On Bilinear Pairing Functions Wireless Communications 37. Semi Supervised Biased Maximum Margin Analysis For Interactive Image Retrieval Image Processing,
- 14. 38. Smile Detection By Boosting Pixel Differences Image Processing 39. Spoc: A Secure And Privacy-Preserving Opportunistic Computing Framework For Mobile-Healthcare Emergency Parallel And Distributed Systems 40. The Three-Tier Security Scheme In Wireless Sensor Networks With Mobile Sinks Parallel And Distributed Systems
- 15. 41. Topology Control In Mobile Ad Hoc Networks With Cooperative Communications Wireless Networking 42. Toward Reliable Data Delivery For Highly Dynamic Mobile Ad Hoc Networks Mobile Computing 43. Towards Secure And Dependable Storage Services In Cloud Computing Cloud Computing
- 16. 44. Tree-Based Mining For Discovering Patterns Of Human Interaction In Meetings Data Mining 45. Becan: A Bandwidth-Efficient Cooperative Authentication Scheme For Filtering Injected False Data In Wireless Sensor Networks Parallel And Distributed Systems 46. Compressed-Sensing-Enabled Video Streaming For Wireless Multimedia Sensor Networks Multimedia
- 17. 47. Scalable And Secure Sharing Of Personal Health Records In Cloud Computing Using Attribute-Based Encryption Cloud Computing 48. Robust Face-Name Graph Matching For Movie Character Identification Multimedia 49. Securing Node Capture Attacks For Hierarchical Data Aggregation In Wireless Sensor Networks Wireless Networking
- 18. 50. Optimal service pricing for a cloud cache Cloud Computing 51. Personalized Ontology Model for Web Information Gathering Data Mining 52. The World in a Nutshell Concise Range Queries Data Mining
