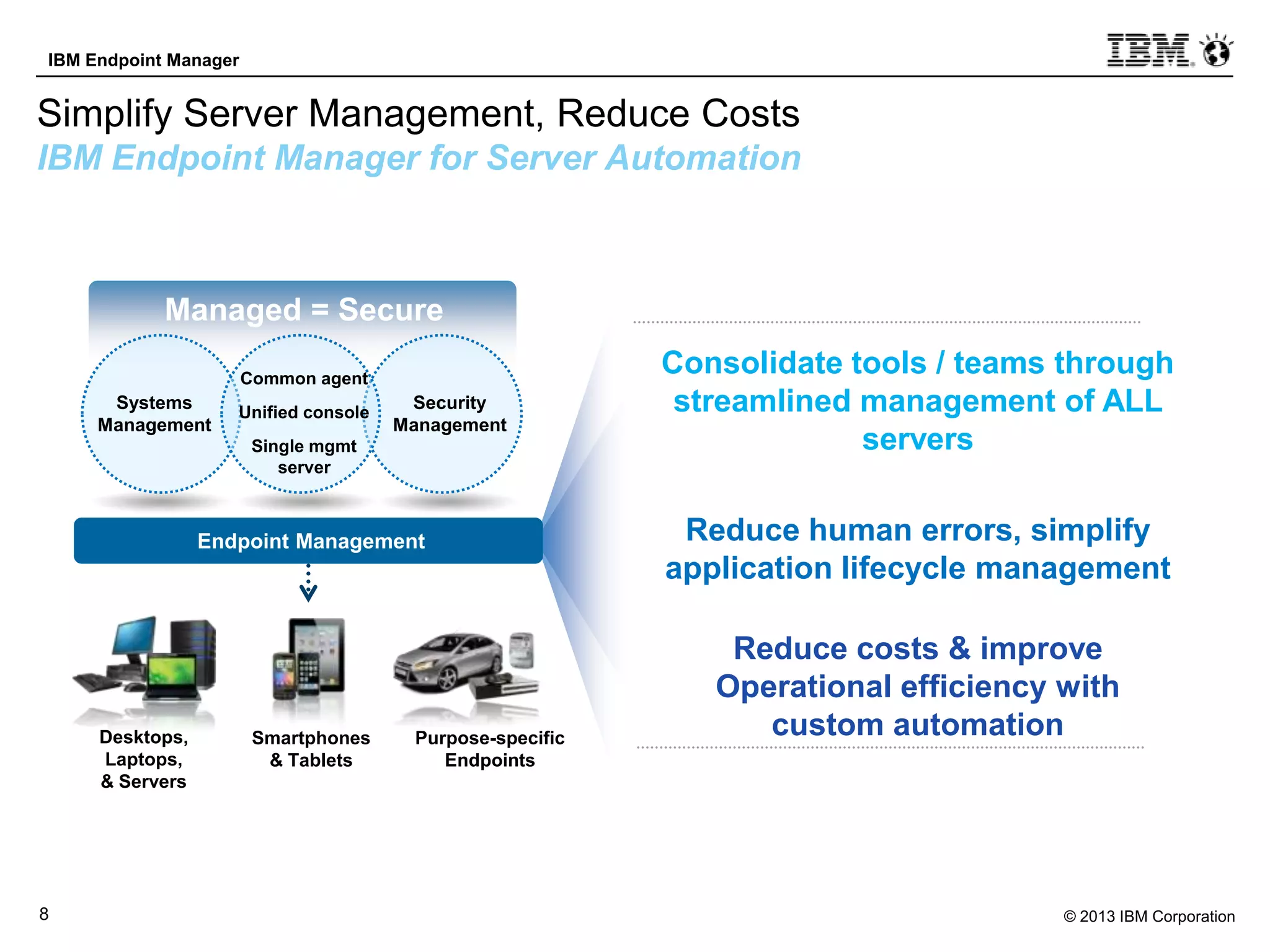
IBM Endpoint Manager provides automated server management capabilities through a single console, agent, and server that can manage up to 250,000 endpoints. It allows users to consolidate server management tools and teams, reduce human errors through simplified application lifecycle management, and lower costs by improving operational efficiency with custom automation plans that can be reused. The solution supports both physical and virtual servers across various operating systems.
![© 2012 IBM Corporation
IBM Endpoint Manager for
Server Automation
Product Introduction and Overview
[NAME], [TITLE]
[DATE]](https://image.slidesharecdn.com/customeroverviewiemforserverautomation31may2013-final-130531112005-phpapp01/75/IBM-Endpoint-Manager-for-Server-Automation-presentation-1-2048.jpg)