iPad Procedures (short)
•
1 like•796 views
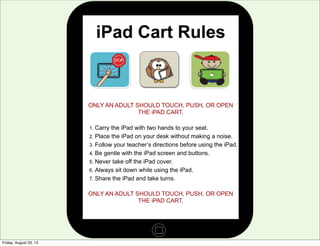
This is the short presentation on iPad procedures, which uses a poster from Common Sense Media. These procedures were put in place to keep iPads from being harmed and to practice good listening skills when using the devices.
Report
Share
Report
Share
Download to read offline
Recommended
Using iPads to be ChAPPions of Student Success

This document provides tips and strategies for managing iPads in a classroom. It suggests labeling iPads with pictures, numbers or names to assign them to students. It also recommends creating classroom rules for iPad use with students and modeling appropriate app usage. The document outlines how to lock students into specific apps using Guided Access and restrict certain device settings. It describes taking screenshots of student work and transferring items to a teacher laptop or website for sharing.
Creative Uses for iPad in the Classroom

These slides were used as part of my presentation at the Apple Store Upper West Side on December 1, 2011.
Video Games vs. Learning

This was the slideshow shared at the ICE 2014 Conference. The content within this slides was meant to get teachers thinking like game designers when creating coursework for their students. There is a lot here.
Writers Workshop Conferencing

This document provides guidance on conducting effective writing conferences. It discusses researching student writing, deciding on a teaching point, teaching the student, and recording notes. For research, teachers should learn what the student is working on and ask questions to understand their writing. When deciding on a teaching point, teachers should choose something directly responsive to the student's needs that will help them improve. Teaching should involve demonstrating, guided practice, or explaining with an example. Teachers are advised to record the lesson, student's response, and their reflection on the conference. The document also offers technology tools like apps and Google platforms for digitally recording conference notes.
Kidblog session 13-14

This document provides guidance for teachers on setting up and using a classroom blog called KidBlogs. It offers tips for establishing blogging guidelines and routines to improve students' writing skills and promote 21st century communication skills. The document outlines a 9-step plan for rolling out a classroom blog, including creating accounts, discussing guidelines with students and parents, and practicing posting and commenting. It also provides examples of posting and commenting guidelines, as well as activity ideas and resources for teachers on using blogs in the classroom.
Blogging Basics & Some Tips

This slide deck has a basic overview of what blogs are and there are some basic tips for teachers as they get started.
Blogger getting started steps

To start a blog on Blogger, create a Blogger profile by accessing Blogger and entering a display name, then click the new blog button to create a blog and name it, which allows accessing the blog's tools to build and manage the new site.
EdTech Ideas - Word Work 

This presentation was a collaborative effort between the literacy coach and edtech coach for the Tri-Creek School System's elementary schools.
Recommended
Using iPads to be ChAPPions of Student Success

This document provides tips and strategies for managing iPads in a classroom. It suggests labeling iPads with pictures, numbers or names to assign them to students. It also recommends creating classroom rules for iPad use with students and modeling appropriate app usage. The document outlines how to lock students into specific apps using Guided Access and restrict certain device settings. It describes taking screenshots of student work and transferring items to a teacher laptop or website for sharing.
Creative Uses for iPad in the Classroom

These slides were used as part of my presentation at the Apple Store Upper West Side on December 1, 2011.
Video Games vs. Learning

This was the slideshow shared at the ICE 2014 Conference. The content within this slides was meant to get teachers thinking like game designers when creating coursework for their students. There is a lot here.
Writers Workshop Conferencing

This document provides guidance on conducting effective writing conferences. It discusses researching student writing, deciding on a teaching point, teaching the student, and recording notes. For research, teachers should learn what the student is working on and ask questions to understand their writing. When deciding on a teaching point, teachers should choose something directly responsive to the student's needs that will help them improve. Teaching should involve demonstrating, guided practice, or explaining with an example. Teachers are advised to record the lesson, student's response, and their reflection on the conference. The document also offers technology tools like apps and Google platforms for digitally recording conference notes.
Kidblog session 13-14

This document provides guidance for teachers on setting up and using a classroom blog called KidBlogs. It offers tips for establishing blogging guidelines and routines to improve students' writing skills and promote 21st century communication skills. The document outlines a 9-step plan for rolling out a classroom blog, including creating accounts, discussing guidelines with students and parents, and practicing posting and commenting. It also provides examples of posting and commenting guidelines, as well as activity ideas and resources for teachers on using blogs in the classroom.
Blogging Basics & Some Tips

This slide deck has a basic overview of what blogs are and there are some basic tips for teachers as they get started.
Blogger getting started steps

To start a blog on Blogger, create a Blogger profile by accessing Blogger and entering a display name, then click the new blog button to create a blog and name it, which allows accessing the blog's tools to build and manage the new site.
EdTech Ideas - Word Work 

This presentation was a collaborative effort between the literacy coach and edtech coach for the Tri-Creek School System's elementary schools.
Gra overview

The Global Read Aloud (GRA) is a 6-week project that connects students and teachers around the world through shared reading experiences. During the GRA in October, students can read from one of four book options and then discuss and collaborate with other students online or through letters. The GRA allows students to practice 21st century skills like connecting over networks and collaborating at a distance. It also benefits teachers by allowing them to network with other professionals and learn digital tools and literacy. Common technologies used include Edmodo, Kidblog, Google Drive, Skype and Twitter.
Mac book procedures

The document outlines rules for using MacBook carts in class, including carrying devices with two hands, placing them quietly on desks, never moving them by the screen, following teacher directions, and keeping lids closed when instructed. Specific rules are to not walk around with open devices, tug on others' devices, and only open a closed device if an adult allows it. Digital citizenship and its importance are also mentioned.
Smart troubleshooting

This document was created to share some troubleshooting tips when using your SMART Board with the equipment at TCSC.
Comparing PC and Mac

These slides were created to illustrate the differences between PC and Mac. The move is focusing on PC users transferring to Macs
Zombie blog storyboard

This was the storyboard I created prior to developing the Attack of the Zombie Journal instructional video.
Integrating web-based technologies training module

Used to help introduce a online training module for teachers on integrating web-based technologies in the educational setting.
The digital storytelling initiative(final1)vb

The Digital Storytelling Initiative aims to improve literacy skills at Jane H. Ball Elementary School through the use of iPad technology. The school has a high percentage of students below grade level in reading and not passing the state English exam. The project will provide iPads loaded with reading, writing, and media apps to help 4th grade students engage in digital reading, writing, podcasting and video production. The goals are to increase English exam scores by 4 percentage points and improve digital literacy skills. A $41,468 budget will cover iPads, apps, professional development training, and evaluation of the program's effectiveness through exam scores and student surveys.
Writinginmath

Students are performing poorly on the state mathematics test, specifically in explaining the steps to solve problems. The instructional goal is for students to write clear, concise explanations for math problems using symbols, numbers, and words. A lesson plan is outlined that incorporates tools like the SMART Board and computer lab to teach a process for reading, solving, self-evaluating, and extended response writing for math problems. Formative assessment includes a pre-test, KWL chart, and summative assessment to evaluate student learning.
Infrastructure Challenges in Scaling RAG with Custom AI models

Building Retrieval-Augmented Generation (RAG) systems with open-source and custom AI models is a complex task. This talk explores the challenges in productionizing RAG systems, including retrieval performance, response synthesis, and evaluation. We’ll discuss how to leverage open-source models like text embeddings, language models, and custom fine-tuned models to enhance RAG performance. Additionally, we’ll cover how BentoML can help orchestrate and scale these AI components efficiently, ensuring seamless deployment and management of RAG systems in the cloud.
GraphRAG for Life Science to increase LLM accuracy

GraphRAG for life science domain, where you retriever information from biomedical knowledge graphs using LLMs to increase the accuracy and performance of generated answers
Fueling AI with Great Data with Airbyte Webinar

This talk will focus on how to collect data from a variety of sources, leveraging this data for RAG and other GenAI use cases, and finally charting your course to productionalization.
Video Streaming: Then, Now, and in the Future

In his public lecture, Christian Timmerer provides insights into the fascinating history of video streaming, starting from its humble beginnings before YouTube to the groundbreaking technologies that now dominate platforms like Netflix and ORF ON. Timmerer also presents provocative contributions of his own that have significantly influenced the industry. He concludes by looking at future challenges and invites the audience to join in a discussion.
Best 20 SEO Techniques To Improve Website Visibility In SERP

Boost your website's visibility with proven SEO techniques! Our latest blog dives into essential strategies to enhance your online presence, increase traffic, and rank higher on search engines. From keyword optimization to quality content creation, learn how to make your site stand out in the crowded digital landscape. Discover actionable tips and expert insights to elevate your SEO game.
Ocean lotus Threat actors project by John Sitima 2024 (1).pptx

Ocean Lotus cyber threat actors represent a sophisticated, persistent, and politically motivated group that poses a significant risk to organizations and individuals in the Southeast Asian region. Their continuous evolution and adaptability underscore the need for robust cybersecurity measures and international cooperation to identify and mitigate the threats posed by such advanced persistent threat groups.
Cosa hanno in comune un mattoncino Lego e la backdoor XZ?

ABSTRACT: A prima vista, un mattoncino Lego e la backdoor XZ potrebbero avere in comune il fatto di essere entrambi blocchi di costruzione, o dipendenze di progetti creativi e software. La realtà è che un mattoncino Lego e il caso della backdoor XZ hanno molto di più di tutto ciò in comune.
Partecipate alla presentazione per immergervi in una storia di interoperabilità, standard e formati aperti, per poi discutere del ruolo importante che i contributori hanno in una comunità open source sostenibile.
BIO: Sostenitrice del software libero e dei formati standard e aperti. È stata un membro attivo dei progetti Fedora e openSUSE e ha co-fondato l'Associazione LibreItalia dove è stata coinvolta in diversi eventi, migrazioni e formazione relativi a LibreOffice. In precedenza ha lavorato a migrazioni e corsi di formazione su LibreOffice per diverse amministrazioni pubbliche e privati. Da gennaio 2020 lavora in SUSE come Software Release Engineer per Uyuni e SUSE Manager e quando non segue la sua passione per i computer e per Geeko coltiva la sua curiosità per l'astronomia (da cui deriva il suo nickname deneb_alpha).
Your One-Stop Shop for Python Success: Top 10 US Python Development Providers

Simplify your search for a reliable Python development partner! This list presents the top 10 trusted US providers offering comprehensive Python development services, ensuring your project's success from conception to completion.
20240605 QFM017 Machine Intelligence Reading List May 2024

Everything I found interesting about machines behaving intelligently during May 2024
Unlock the Future of Search with MongoDB Atlas_ Vector Search Unleashed.pdf

Discover how MongoDB Atlas and vector search technology can revolutionize your application's search capabilities. This comprehensive presentation covers:
* What is Vector Search?
* Importance and benefits of vector search
* Practical use cases across various industries
* Step-by-step implementation guide
* Live demos with code snippets
* Enhancing LLM capabilities with vector search
* Best practices and optimization strategies
Perfect for developers, AI enthusiasts, and tech leaders. Learn how to leverage MongoDB Atlas to deliver highly relevant, context-aware search results, transforming your data retrieval process. Stay ahead in tech innovation and maximize the potential of your applications.
#MongoDB #VectorSearch #AI #SemanticSearch #TechInnovation #DataScience #LLM #MachineLearning #SearchTechnology
Removing Uninteresting Bytes in Software Fuzzing

Imagine a world where software fuzzing, the process of mutating bytes in test seeds to uncover hidden and erroneous program behaviors, becomes faster and more effective. A lot depends on the initial seeds, which can significantly dictate the trajectory of a fuzzing campaign, particularly in terms of how long it takes to uncover interesting behaviour in your code. We introduce DIAR, a technique designed to speedup fuzzing campaigns by pinpointing and eliminating those uninteresting bytes in the seeds. Picture this: instead of wasting valuable resources on meaningless mutations in large, bloated seeds, DIAR removes the unnecessary bytes, streamlining the entire process.
In this work, we equipped AFL, a popular fuzzer, with DIAR and examined two critical Linux libraries -- Libxml's xmllint, a tool for parsing xml documents, and Binutil's readelf, an essential debugging and security analysis command-line tool used to display detailed information about ELF (Executable and Linkable Format). Our preliminary results show that AFL+DIAR does not only discover new paths more quickly but also achieves higher coverage overall. This work thus showcases how starting with lean and optimized seeds can lead to faster, more comprehensive fuzzing campaigns -- and DIAR helps you find such seeds.
- These are slides of the talk given at IEEE International Conference on Software Testing Verification and Validation Workshop, ICSTW 2022.
AI-Powered Food Delivery Transforming App Development in Saudi Arabia.pdf

In this blog post, we'll delve into the intersection of AI and app development in Saudi Arabia, focusing on the food delivery sector. We'll explore how AI is revolutionizing the way Saudi consumers order food, how restaurants manage their operations, and how delivery partners navigate the bustling streets of cities like Riyadh, Jeddah, and Dammam. Through real-world case studies, we'll showcase how leading Saudi food delivery apps are leveraging AI to redefine convenience, personalization, and efficiency.
TrustArc Webinar - 2024 Global Privacy Survey

How does your privacy program stack up against your peers? What challenges are privacy teams tackling and prioritizing in 2024?
In the fifth annual Global Privacy Benchmarks Survey, we asked over 1,800 global privacy professionals and business executives to share their perspectives on the current state of privacy inside and outside of their organizations. This year’s report focused on emerging areas of importance for privacy and compliance professionals, including considerations and implications of Artificial Intelligence (AI) technologies, building brand trust, and different approaches for achieving higher privacy competence scores.
See how organizational priorities and strategic approaches to data security and privacy are evolving around the globe.
This webinar will review:
- The top 10 privacy insights from the fifth annual Global Privacy Benchmarks Survey
- The top challenges for privacy leaders, practitioners, and organizations in 2024
- Key themes to consider in developing and maintaining your privacy program
How to Get CNIC Information System with Paksim Ga.pptx

Pakdata Cf is a groundbreaking system designed to streamline and facilitate access to CNIC information. This innovative platform leverages advanced technology to provide users with efficient and secure access to their CNIC details.
More Related Content
More from Daniel Gibson
Gra overview

The Global Read Aloud (GRA) is a 6-week project that connects students and teachers around the world through shared reading experiences. During the GRA in October, students can read from one of four book options and then discuss and collaborate with other students online or through letters. The GRA allows students to practice 21st century skills like connecting over networks and collaborating at a distance. It also benefits teachers by allowing them to network with other professionals and learn digital tools and literacy. Common technologies used include Edmodo, Kidblog, Google Drive, Skype and Twitter.
Mac book procedures

The document outlines rules for using MacBook carts in class, including carrying devices with two hands, placing them quietly on desks, never moving them by the screen, following teacher directions, and keeping lids closed when instructed. Specific rules are to not walk around with open devices, tug on others' devices, and only open a closed device if an adult allows it. Digital citizenship and its importance are also mentioned.
Smart troubleshooting

This document was created to share some troubleshooting tips when using your SMART Board with the equipment at TCSC.
Comparing PC and Mac

These slides were created to illustrate the differences between PC and Mac. The move is focusing on PC users transferring to Macs
Zombie blog storyboard

This was the storyboard I created prior to developing the Attack of the Zombie Journal instructional video.
Integrating web-based technologies training module

Used to help introduce a online training module for teachers on integrating web-based technologies in the educational setting.
The digital storytelling initiative(final1)vb

The Digital Storytelling Initiative aims to improve literacy skills at Jane H. Ball Elementary School through the use of iPad technology. The school has a high percentage of students below grade level in reading and not passing the state English exam. The project will provide iPads loaded with reading, writing, and media apps to help 4th grade students engage in digital reading, writing, podcasting and video production. The goals are to increase English exam scores by 4 percentage points and improve digital literacy skills. A $41,468 budget will cover iPads, apps, professional development training, and evaluation of the program's effectiveness through exam scores and student surveys.
Writinginmath

Students are performing poorly on the state mathematics test, specifically in explaining the steps to solve problems. The instructional goal is for students to write clear, concise explanations for math problems using symbols, numbers, and words. A lesson plan is outlined that incorporates tools like the SMART Board and computer lab to teach a process for reading, solving, self-evaluating, and extended response writing for math problems. Formative assessment includes a pre-test, KWL chart, and summative assessment to evaluate student learning.
More from Daniel Gibson (8)
Integrating web-based technologies training module

Integrating web-based technologies training module
Recently uploaded
Infrastructure Challenges in Scaling RAG with Custom AI models

Building Retrieval-Augmented Generation (RAG) systems with open-source and custom AI models is a complex task. This talk explores the challenges in productionizing RAG systems, including retrieval performance, response synthesis, and evaluation. We’ll discuss how to leverage open-source models like text embeddings, language models, and custom fine-tuned models to enhance RAG performance. Additionally, we’ll cover how BentoML can help orchestrate and scale these AI components efficiently, ensuring seamless deployment and management of RAG systems in the cloud.
GraphRAG for Life Science to increase LLM accuracy

GraphRAG for life science domain, where you retriever information from biomedical knowledge graphs using LLMs to increase the accuracy and performance of generated answers
Fueling AI with Great Data with Airbyte Webinar

This talk will focus on how to collect data from a variety of sources, leveraging this data for RAG and other GenAI use cases, and finally charting your course to productionalization.
Video Streaming: Then, Now, and in the Future

In his public lecture, Christian Timmerer provides insights into the fascinating history of video streaming, starting from its humble beginnings before YouTube to the groundbreaking technologies that now dominate platforms like Netflix and ORF ON. Timmerer also presents provocative contributions of his own that have significantly influenced the industry. He concludes by looking at future challenges and invites the audience to join in a discussion.
Best 20 SEO Techniques To Improve Website Visibility In SERP

Boost your website's visibility with proven SEO techniques! Our latest blog dives into essential strategies to enhance your online presence, increase traffic, and rank higher on search engines. From keyword optimization to quality content creation, learn how to make your site stand out in the crowded digital landscape. Discover actionable tips and expert insights to elevate your SEO game.
Ocean lotus Threat actors project by John Sitima 2024 (1).pptx

Ocean Lotus cyber threat actors represent a sophisticated, persistent, and politically motivated group that poses a significant risk to organizations and individuals in the Southeast Asian region. Their continuous evolution and adaptability underscore the need for robust cybersecurity measures and international cooperation to identify and mitigate the threats posed by such advanced persistent threat groups.
Cosa hanno in comune un mattoncino Lego e la backdoor XZ?

ABSTRACT: A prima vista, un mattoncino Lego e la backdoor XZ potrebbero avere in comune il fatto di essere entrambi blocchi di costruzione, o dipendenze di progetti creativi e software. La realtà è che un mattoncino Lego e il caso della backdoor XZ hanno molto di più di tutto ciò in comune.
Partecipate alla presentazione per immergervi in una storia di interoperabilità, standard e formati aperti, per poi discutere del ruolo importante che i contributori hanno in una comunità open source sostenibile.
BIO: Sostenitrice del software libero e dei formati standard e aperti. È stata un membro attivo dei progetti Fedora e openSUSE e ha co-fondato l'Associazione LibreItalia dove è stata coinvolta in diversi eventi, migrazioni e formazione relativi a LibreOffice. In precedenza ha lavorato a migrazioni e corsi di formazione su LibreOffice per diverse amministrazioni pubbliche e privati. Da gennaio 2020 lavora in SUSE come Software Release Engineer per Uyuni e SUSE Manager e quando non segue la sua passione per i computer e per Geeko coltiva la sua curiosità per l'astronomia (da cui deriva il suo nickname deneb_alpha).
Your One-Stop Shop for Python Success: Top 10 US Python Development Providers

Simplify your search for a reliable Python development partner! This list presents the top 10 trusted US providers offering comprehensive Python development services, ensuring your project's success from conception to completion.
20240605 QFM017 Machine Intelligence Reading List May 2024

Everything I found interesting about machines behaving intelligently during May 2024
Unlock the Future of Search with MongoDB Atlas_ Vector Search Unleashed.pdf

Discover how MongoDB Atlas and vector search technology can revolutionize your application's search capabilities. This comprehensive presentation covers:
* What is Vector Search?
* Importance and benefits of vector search
* Practical use cases across various industries
* Step-by-step implementation guide
* Live demos with code snippets
* Enhancing LLM capabilities with vector search
* Best practices and optimization strategies
Perfect for developers, AI enthusiasts, and tech leaders. Learn how to leverage MongoDB Atlas to deliver highly relevant, context-aware search results, transforming your data retrieval process. Stay ahead in tech innovation and maximize the potential of your applications.
#MongoDB #VectorSearch #AI #SemanticSearch #TechInnovation #DataScience #LLM #MachineLearning #SearchTechnology
Removing Uninteresting Bytes in Software Fuzzing

Imagine a world where software fuzzing, the process of mutating bytes in test seeds to uncover hidden and erroneous program behaviors, becomes faster and more effective. A lot depends on the initial seeds, which can significantly dictate the trajectory of a fuzzing campaign, particularly in terms of how long it takes to uncover interesting behaviour in your code. We introduce DIAR, a technique designed to speedup fuzzing campaigns by pinpointing and eliminating those uninteresting bytes in the seeds. Picture this: instead of wasting valuable resources on meaningless mutations in large, bloated seeds, DIAR removes the unnecessary bytes, streamlining the entire process.
In this work, we equipped AFL, a popular fuzzer, with DIAR and examined two critical Linux libraries -- Libxml's xmllint, a tool for parsing xml documents, and Binutil's readelf, an essential debugging and security analysis command-line tool used to display detailed information about ELF (Executable and Linkable Format). Our preliminary results show that AFL+DIAR does not only discover new paths more quickly but also achieves higher coverage overall. This work thus showcases how starting with lean and optimized seeds can lead to faster, more comprehensive fuzzing campaigns -- and DIAR helps you find such seeds.
- These are slides of the talk given at IEEE International Conference on Software Testing Verification and Validation Workshop, ICSTW 2022.
AI-Powered Food Delivery Transforming App Development in Saudi Arabia.pdf

In this blog post, we'll delve into the intersection of AI and app development in Saudi Arabia, focusing on the food delivery sector. We'll explore how AI is revolutionizing the way Saudi consumers order food, how restaurants manage their operations, and how delivery partners navigate the bustling streets of cities like Riyadh, Jeddah, and Dammam. Through real-world case studies, we'll showcase how leading Saudi food delivery apps are leveraging AI to redefine convenience, personalization, and efficiency.
TrustArc Webinar - 2024 Global Privacy Survey

How does your privacy program stack up against your peers? What challenges are privacy teams tackling and prioritizing in 2024?
In the fifth annual Global Privacy Benchmarks Survey, we asked over 1,800 global privacy professionals and business executives to share their perspectives on the current state of privacy inside and outside of their organizations. This year’s report focused on emerging areas of importance for privacy and compliance professionals, including considerations and implications of Artificial Intelligence (AI) technologies, building brand trust, and different approaches for achieving higher privacy competence scores.
See how organizational priorities and strategic approaches to data security and privacy are evolving around the globe.
This webinar will review:
- The top 10 privacy insights from the fifth annual Global Privacy Benchmarks Survey
- The top challenges for privacy leaders, practitioners, and organizations in 2024
- Key themes to consider in developing and maintaining your privacy program
How to Get CNIC Information System with Paksim Ga.pptx

Pakdata Cf is a groundbreaking system designed to streamline and facilitate access to CNIC information. This innovative platform leverages advanced technology to provide users with efficient and secure access to their CNIC details.
Uni Systems Copilot event_05062024_C.Vlachos.pdf

Unlocking Productivity: Leveraging the Potential of Copilot in Microsoft 365, a presentation by Christoforos Vlachos, Senior Solutions Manager – Modern Workplace, Uni Systems
AI 101: An Introduction to the Basics and Impact of Artificial Intelligence

Imagine a world where machines not only perform tasks but also learn, adapt, and make decisions. This is the promise of Artificial Intelligence (AI), a technology that's not just enhancing our lives but revolutionizing entire industries.
Things to Consider When Choosing a Website Developer for your Website | FODUU

Choosing the right website developer is crucial for your business. This article covers essential factors to consider, including experience, portfolio, technical skills, communication, pricing, reputation & reviews, cost and budget considerations and post-launch support. Make an informed decision to ensure your website meets your business goals.
“Building and Scaling AI Applications with the Nx AI Manager,” a Presentation...

“Building and Scaling AI Applications with the Nx AI Manager,” a Presentation...Edge AI and Vision Alliance
For the full video of this presentation, please visit: https://www.edge-ai-vision.com/2024/06/building-and-scaling-ai-applications-with-the-nx-ai-manager-a-presentation-from-network-optix/
Robin van Emden, Senior Director of Data Science at Network Optix, presents the “Building and Scaling AI Applications with the Nx AI Manager,” tutorial at the May 2024 Embedded Vision Summit.
In this presentation, van Emden covers the basics of scaling edge AI solutions using the Nx tool kit. He emphasizes the process of developing AI models and deploying them globally. He also showcases the conversion of AI models and the creation of effective edge AI pipelines, with a focus on pre-processing, model conversion, selecting the appropriate inference engine for the target hardware and post-processing.
van Emden shows how Nx can simplify the developer’s life and facilitate a rapid transition from concept to production-ready applications.He provides valuable insights into developing scalable and efficient edge AI solutions, with a strong focus on practical implementation.Building Production Ready Search Pipelines with Spark and Milvus

Spark is the widely used ETL tool for processing, indexing and ingesting data to serving stack for search. Milvus is the production-ready open-source vector database. In this talk we will show how to use Spark to process unstructured data to extract vector representations, and push the vectors to Milvus vector database for search serving.
Generating privacy-protected synthetic data using Secludy and Milvus

During this demo, the founders of Secludy will demonstrate how their system utilizes Milvus to store and manipulate embeddings for generating privacy-protected synthetic data. Their approach not only maintains the confidentiality of the original data but also enhances the utility and scalability of LLMs under privacy constraints. Attendees, including machine learning engineers, data scientists, and data managers, will witness first-hand how Secludy's integration with Milvus empowers organizations to harness the power of LLMs securely and efficiently.
Recently uploaded (20)
Infrastructure Challenges in Scaling RAG with Custom AI models

Infrastructure Challenges in Scaling RAG with Custom AI models
GraphRAG for Life Science to increase LLM accuracy

GraphRAG for Life Science to increase LLM accuracy
Best 20 SEO Techniques To Improve Website Visibility In SERP

Best 20 SEO Techniques To Improve Website Visibility In SERP
Ocean lotus Threat actors project by John Sitima 2024 (1).pptx

Ocean lotus Threat actors project by John Sitima 2024 (1).pptx
Cosa hanno in comune un mattoncino Lego e la backdoor XZ?

Cosa hanno in comune un mattoncino Lego e la backdoor XZ?
Your One-Stop Shop for Python Success: Top 10 US Python Development Providers

Your One-Stop Shop for Python Success: Top 10 US Python Development Providers
20240605 QFM017 Machine Intelligence Reading List May 2024

20240605 QFM017 Machine Intelligence Reading List May 2024
Unlock the Future of Search with MongoDB Atlas_ Vector Search Unleashed.pdf

Unlock the Future of Search with MongoDB Atlas_ Vector Search Unleashed.pdf
AI-Powered Food Delivery Transforming App Development in Saudi Arabia.pdf

AI-Powered Food Delivery Transforming App Development in Saudi Arabia.pdf
How to Get CNIC Information System with Paksim Ga.pptx

How to Get CNIC Information System with Paksim Ga.pptx
AI 101: An Introduction to the Basics and Impact of Artificial Intelligence

AI 101: An Introduction to the Basics and Impact of Artificial Intelligence
Things to Consider When Choosing a Website Developer for your Website | FODUU

Things to Consider When Choosing a Website Developer for your Website | FODUU
“Building and Scaling AI Applications with the Nx AI Manager,” a Presentation...

“Building and Scaling AI Applications with the Nx AI Manager,” a Presentation...
Building Production Ready Search Pipelines with Spark and Milvus

Building Production Ready Search Pipelines with Spark and Milvus
Generating privacy-protected synthetic data using Secludy and Milvus

Generating privacy-protected synthetic data using Secludy and Milvus
iPad Procedures (short)
- 1. iPad Cart Rules ONLY AN ADULT SHOULD TOUCH, PUSH, OR OPEN THE iPAD CART. 1. Carry the iPad with two hands to your seat. 2. Place the iPad on your desk without making a noise. 3. Follow your teacher’s directions before using the iPad. 4. Be gentle with the iPad screen and buttons. 5. Never take off the iPad cover. 6. Always sit down while using the iPad. 7. Share the iPad and take turns. ONLY AN ADULT SHOULD TOUCH, PUSH, OR OPEN THE iPAD CART. Friday, August 23, 13
- 2. Friday, August 23, 13
- 3. Friday, August 23, 13
- 4. Friday, August 23, 13
- 5. Friday, August 23, 13
- 6. Friday, August 23, 13
- 7. Friday, August 23, 13
- 8. Friday, August 23, 13
- 9. Friday, August 23, 13
