How workplace surveillance works katrina hunos
•Download as DOC, PDF•
0 likes•112 views
Report
Share
Report
Share
Recommended
A smart, location based time and

Over the years the process of manual attendance has been carried out which is not only time consuming
but also provides erroneous result. Automated time and attendance monitoring system provides many
benefits to organizations. This reduces the need of pen and paper based manual attendance tracking
system. Following this thought, we have proposed a smart location based time and attendance tracking
system which is implemented on android mobile application on smartphone reducing the need of additional
biometric scanner device. The location of an organization has a specific location, which can be determine
by the GPS. Each employee’s location can be determined by the GPS using smartphone. This location is
defined as a key of time and attendance tracking in our paper.
A SMART, LOCATION BASED TIME AND ATTENDANCE TRACKING SYSTEM USING ANDROID APP...

Over the years the process of manual attendance has been carried out which is not only time consuming
but also provides erroneous result. Automated time and attendance monitoring system provides many
benefits to organizations. This reduces the need of pen and paper based manual attendance tracking
system. Following this thought, we have proposed a smart location based time and attendance tracking
system which is implemented on android mobile application on smartphone reducing the need of additional
biometric scanner device. The location of an organization has a specific location, which can be determine
by the GPS. Each employee’s location can be determined by the GPS using smartphone. This location is
defined as a key of time and attendance tracking in our paper.
A SMART, LOCATION BASED TIME AND ATTENDANCE TRACKING SYSTEM USING ANDROID APP...

Over the years the process of manual attendance has been carried out which is not only time consuming
but also provides erroneous result. Automated time and attendance monitoring system provides many
benefits to organizations. This reduces the need of pen and paper based manual attendance tracking
system. Following this thought, we have proposed a smart location based time and attendance tracking
system which is implemented on android mobile application on smartphone reducing the need of additional
biometric scanner device. The location of an organization has a specific location, which can be determine
by the GPS. Each employee’s location can be determined by the GPS using smartphone. This location is
defined as a key of time and attendance tracking in our paper.
Recommended
A smart, location based time and

Over the years the process of manual attendance has been carried out which is not only time consuming
but also provides erroneous result. Automated time and attendance monitoring system provides many
benefits to organizations. This reduces the need of pen and paper based manual attendance tracking
system. Following this thought, we have proposed a smart location based time and attendance tracking
system which is implemented on android mobile application on smartphone reducing the need of additional
biometric scanner device. The location of an organization has a specific location, which can be determine
by the GPS. Each employee’s location can be determined by the GPS using smartphone. This location is
defined as a key of time and attendance tracking in our paper.
A SMART, LOCATION BASED TIME AND ATTENDANCE TRACKING SYSTEM USING ANDROID APP...

Over the years the process of manual attendance has been carried out which is not only time consuming
but also provides erroneous result. Automated time and attendance monitoring system provides many
benefits to organizations. This reduces the need of pen and paper based manual attendance tracking
system. Following this thought, we have proposed a smart location based time and attendance tracking
system which is implemented on android mobile application on smartphone reducing the need of additional
biometric scanner device. The location of an organization has a specific location, which can be determine
by the GPS. Each employee’s location can be determined by the GPS using smartphone. This location is
defined as a key of time and attendance tracking in our paper.
A SMART, LOCATION BASED TIME AND ATTENDANCE TRACKING SYSTEM USING ANDROID APP...

Over the years the process of manual attendance has been carried out which is not only time consuming
but also provides erroneous result. Automated time and attendance monitoring system provides many
benefits to organizations. This reduces the need of pen and paper based manual attendance tracking
system. Following this thought, we have proposed a smart location based time and attendance tracking
system which is implemented on android mobile application on smartphone reducing the need of additional
biometric scanner device. The location of an organization has a specific location, which can be determine
by the GPS. Each employee’s location can be determined by the GPS using smartphone. This location is
defined as a key of time and attendance tracking in our paper.
A SMART, LOCATION BASED TIME AND ATTENDANCE TRACKING SYSTEM USING ANDROID APP...

Over the years the process of manual attendance has been carried out which is not only time consuming but also provides erroneous result. Automated time and attendance monitoring system provides many benefits to organizations. This reduces the need of pen and paper based manual attendance tracking system. Following this thought, we have proposed a smart location based time and attendance tracking system which is implemented on android mobile application on smartphone reducing the need of additional biometric scanner device. The location of an organization has a specific location, which can be determine by the GPS. Each employee’s location can be determined by the GPS using smartphone. This location is defined as a key of time and attendance tracking in our paper.
A SMART, LOCATION BASED TIME AND ATTENDANCE TRACKING SYSTEM USING ANDROID APP...

Over the years the process of manual attendance has been carried out which is not only time consuming
but also provides erroneous result. Automated time and attendance monitoring system provides many
benefits to organizations. This reduces the need of pen and paper based manual attendance tracking
system. Following this thought, we have proposed a smart location based time and attendance tracking
system which is implemented on android mobile application on smartphone reducing the need of additional
biometric scanner device. The location of an organization has a specific location, which can be determine
by the GPS. Each employee’s location can be determined by the GPS using smartphone. This location is
defined as a key of time and attendance tracking in our paper.
Network Security and Spoofing Attacks

Nowadays it is very common to hear from people that internet network is the largest engineering system,
and something that we cannot imagine life without.
"Inter- application vulnerabilities. hunting for bugs in secure applications"...

For the last couple of years I have been participating in various public and private bug bounty programmes including United Airlines, ING, RBS, EU or Synack. Usually these programmes are run by security-mature companies which take a lot of effort to make sure that their applications are secure. So how is that even possible that they are still vulnerable to well-known issues like XSS or IDOR which should not exist in 2019 anymore? Presentation will share information about common “inter-application” vulnerabilities encountered during testing process and emphasize the need of appropriate security testing at each stage of system life cycle. During 45 minutes long talk I will present several real-life examples of "inter-application" vulnerabilities, explain the root causes of these issues and propose steps which could be taken to avoid these vulnerabilities in the future.
What is security testing and why it is so important?

Security Testing is described as a type of Software Testing that assures software systems and applications are free from any vulnerabilities, threats, risks that may cause a big loss. Security testing of any system is about uncovering all likely loopholes and weaknesses of the system which might end up in a loss of information, revenue, repute at the hands of the employees or outsiders of the Organization.
IRJET- Preventing Phishing Attack using Evolutionary Algorithms

https://www.irjet.net/archives/V6/i3/IRJET-V6I3731.pdf
Test execution

Test execution is the process of executing the code and comparing the expected and actual results. Following factors need to be considered for a test execution process − Based on a risk, select a subset of test suite to be executed for this cycle. Assign the test cases in each test suite to testers for execution.
Welcome to International Journal of Engineering Research and Development (IJERD)

http://www.ijerd.com
Achievement summary during 2017 start with intro about IT depart.docx

Achievement summary during 2017: start with intro about IT department and how they are trying to support the company and making their work very efficiently and effectively by implementing these system and then listed these system
In 2017 we used three system:
1- Q-time: the attendance system and install biometric devices in most of the work location and al of them are connecting to our network router.
by implementing this system, this help the employee to make permission, apply for vacation from the website and his/ her managers will approve and will reflect in the time sheet report .no need to send email to HR or to their managers , it saving time and smooth the process.
Also, it helps HR team to process timesheet in a very easy way and it will not take time from them like before as they doing it manually.
Us as an IT department we worked so hard to implement this system and enforce the HR requirements. during this project we had many meetings with the developers to make sure that they understood HR requirements
2-EDGE HRMS: We have been starting a new HRMS instead of the old system. old system was a server based but this is a web based and we can access from anywhere and anytime. for payroll and started this project in May 2017, we go live in sep 2017. in this system, hr can add new employees, change PAF, close PAF, and leave application . we have just implemented the workflow process for some feature and that’s will help us to minimize the paper and get management approval very quick regardless where are they as they can enter and approve the vacation and other activities that required their approval.
3- vehicle Fleet Management System: explain this system it is a company vehicle tracking system.
4- Ticketing system: we have been started using ticketing system to support employees and handle their request in very smooth way. ( spicework) write about this and the feature. how it works.
this is also helping us to measure the performance of the departments by generating a monthly report and check how many tickets did we close and what was the request and who was handling this from IT department. Also, monthly report will be shared with our manager to check IT department performance
Something we do not do it now as department but we are going to do in 2018:
1- documented everything as department each stff of IT department has to documented evry process and procdure he is doing and make it available in the server so every one of the team will have access and see what happened. in case of some one is absent it easy for us to know what he is doing and complete his work rather than asking him about the password or how to do this. everything will be documented. such as how to install windows from th scratch, how to restore a laptop, how to configure IP phones and etc. this will help us to reduce dependency on one employee to do the task. all staff should know how to do department tasks.
2- clear the IT payment every mo.
Fingerprint Alert System A Solution for Effective Management System

This document gives a write up about the necessity of a device, one which is the Management System of employees. Nowadays, maintaining punctuality has become a tedious job for employees. We know that the presence of an employee in an office is collected from the fingerprint or biometric system, as per the technical reviews we are clear that it is a time bound machine.. A biometric device is a security identification and authentication device. Such devices use automated methods verifying or recognising the identity of a living person based on a physiological behavioral characteristic. These characteristics include fingerprints, or facial images, iris and voice recognition. In this report we are introducing a solution for this problem, a Fingerprint Alert System. Rafi. P | Thoukheer Ibnu Ali Ashraf. A "Fingerprint Alert System: A Solution for Effective Management System" Published in International Journal of Trend in Scientific Research and Development (ijtsrd), ISSN: 2456-6470, Volume-6 | Issue-7 , December 2022, URL: https://www.ijtsrd.com/papers/ijtsrd52414.pdf Paper URL: https://www.ijtsrd.com/computer-science/other/52414/fingerprint-alert-system-a-solution-for-effective-management-system/rafi-p
Security testing

Security Testing is a process to determine that an information system protects data and maintains functionality as intended.
0x01 - Newton's Third Law: Static vs. Dynamic Abusers

f you offer a service on the web, odds are that someone will abuse it. Be it an API, a SaaS, a PaaS, or even a static website, someone somewhere will try to figure out a way to use it to their own needs. In this talk we'll compare measures that are effective against static attackers and how to battle a dynamic attacker who adapts to your counter-measures.
About the Speaker
===============
Diogo Sousa, Engineering Manager @ Canonical
An opinionated individual with an interest in cryptography and its intersection with secure software development.
Competition and Regulation in Professional Services – KLEINER – June 2024 OEC...

Competition and Regulation in Professional Services – KLEINER – June 2024 OEC...OECD Directorate for Financial and Enterprise Affairs
This presentation by Morris Kleiner (University of Minnesota), was made during the discussion “Competition and Regulation in Professions and Occupations” held at the Working Party No. 2 on Competition and Regulation on 10 June 2024. More papers and presentations on the topic can be found out at oe.cd/crps.
This presentation was uploaded with the author’s consent.More Related Content
Similar to How workplace surveillance works katrina hunos
A SMART, LOCATION BASED TIME AND ATTENDANCE TRACKING SYSTEM USING ANDROID APP...

Over the years the process of manual attendance has been carried out which is not only time consuming but also provides erroneous result. Automated time and attendance monitoring system provides many benefits to organizations. This reduces the need of pen and paper based manual attendance tracking system. Following this thought, we have proposed a smart location based time and attendance tracking system which is implemented on android mobile application on smartphone reducing the need of additional biometric scanner device. The location of an organization has a specific location, which can be determine by the GPS. Each employee’s location can be determined by the GPS using smartphone. This location is defined as a key of time and attendance tracking in our paper.
A SMART, LOCATION BASED TIME AND ATTENDANCE TRACKING SYSTEM USING ANDROID APP...

Over the years the process of manual attendance has been carried out which is not only time consuming
but also provides erroneous result. Automated time and attendance monitoring system provides many
benefits to organizations. This reduces the need of pen and paper based manual attendance tracking
system. Following this thought, we have proposed a smart location based time and attendance tracking
system which is implemented on android mobile application on smartphone reducing the need of additional
biometric scanner device. The location of an organization has a specific location, which can be determine
by the GPS. Each employee’s location can be determined by the GPS using smartphone. This location is
defined as a key of time and attendance tracking in our paper.
Network Security and Spoofing Attacks

Nowadays it is very common to hear from people that internet network is the largest engineering system,
and something that we cannot imagine life without.
"Inter- application vulnerabilities. hunting for bugs in secure applications"...

For the last couple of years I have been participating in various public and private bug bounty programmes including United Airlines, ING, RBS, EU or Synack. Usually these programmes are run by security-mature companies which take a lot of effort to make sure that their applications are secure. So how is that even possible that they are still vulnerable to well-known issues like XSS or IDOR which should not exist in 2019 anymore? Presentation will share information about common “inter-application” vulnerabilities encountered during testing process and emphasize the need of appropriate security testing at each stage of system life cycle. During 45 minutes long talk I will present several real-life examples of "inter-application" vulnerabilities, explain the root causes of these issues and propose steps which could be taken to avoid these vulnerabilities in the future.
What is security testing and why it is so important?

Security Testing is described as a type of Software Testing that assures software systems and applications are free from any vulnerabilities, threats, risks that may cause a big loss. Security testing of any system is about uncovering all likely loopholes and weaknesses of the system which might end up in a loss of information, revenue, repute at the hands of the employees or outsiders of the Organization.
IRJET- Preventing Phishing Attack using Evolutionary Algorithms

https://www.irjet.net/archives/V6/i3/IRJET-V6I3731.pdf
Test execution

Test execution is the process of executing the code and comparing the expected and actual results. Following factors need to be considered for a test execution process − Based on a risk, select a subset of test suite to be executed for this cycle. Assign the test cases in each test suite to testers for execution.
Welcome to International Journal of Engineering Research and Development (IJERD)

http://www.ijerd.com
Achievement summary during 2017 start with intro about IT depart.docx

Achievement summary during 2017: start with intro about IT department and how they are trying to support the company and making their work very efficiently and effectively by implementing these system and then listed these system
In 2017 we used three system:
1- Q-time: the attendance system and install biometric devices in most of the work location and al of them are connecting to our network router.
by implementing this system, this help the employee to make permission, apply for vacation from the website and his/ her managers will approve and will reflect in the time sheet report .no need to send email to HR or to their managers , it saving time and smooth the process.
Also, it helps HR team to process timesheet in a very easy way and it will not take time from them like before as they doing it manually.
Us as an IT department we worked so hard to implement this system and enforce the HR requirements. during this project we had many meetings with the developers to make sure that they understood HR requirements
2-EDGE HRMS: We have been starting a new HRMS instead of the old system. old system was a server based but this is a web based and we can access from anywhere and anytime. for payroll and started this project in May 2017, we go live in sep 2017. in this system, hr can add new employees, change PAF, close PAF, and leave application . we have just implemented the workflow process for some feature and that’s will help us to minimize the paper and get management approval very quick regardless where are they as they can enter and approve the vacation and other activities that required their approval.
3- vehicle Fleet Management System: explain this system it is a company vehicle tracking system.
4- Ticketing system: we have been started using ticketing system to support employees and handle their request in very smooth way. ( spicework) write about this and the feature. how it works.
this is also helping us to measure the performance of the departments by generating a monthly report and check how many tickets did we close and what was the request and who was handling this from IT department. Also, monthly report will be shared with our manager to check IT department performance
Something we do not do it now as department but we are going to do in 2018:
1- documented everything as department each stff of IT department has to documented evry process and procdure he is doing and make it available in the server so every one of the team will have access and see what happened. in case of some one is absent it easy for us to know what he is doing and complete his work rather than asking him about the password or how to do this. everything will be documented. such as how to install windows from th scratch, how to restore a laptop, how to configure IP phones and etc. this will help us to reduce dependency on one employee to do the task. all staff should know how to do department tasks.
2- clear the IT payment every mo.
Fingerprint Alert System A Solution for Effective Management System

This document gives a write up about the necessity of a device, one which is the Management System of employees. Nowadays, maintaining punctuality has become a tedious job for employees. We know that the presence of an employee in an office is collected from the fingerprint or biometric system, as per the technical reviews we are clear that it is a time bound machine.. A biometric device is a security identification and authentication device. Such devices use automated methods verifying or recognising the identity of a living person based on a physiological behavioral characteristic. These characteristics include fingerprints, or facial images, iris and voice recognition. In this report we are introducing a solution for this problem, a Fingerprint Alert System. Rafi. P | Thoukheer Ibnu Ali Ashraf. A "Fingerprint Alert System: A Solution for Effective Management System" Published in International Journal of Trend in Scientific Research and Development (ijtsrd), ISSN: 2456-6470, Volume-6 | Issue-7 , December 2022, URL: https://www.ijtsrd.com/papers/ijtsrd52414.pdf Paper URL: https://www.ijtsrd.com/computer-science/other/52414/fingerprint-alert-system-a-solution-for-effective-management-system/rafi-p
Security testing

Security Testing is a process to determine that an information system protects data and maintains functionality as intended.
Similar to How workplace surveillance works katrina hunos (20)
A SMART, LOCATION BASED TIME AND ATTENDANCE TRACKING SYSTEM USING ANDROID APP...

A SMART, LOCATION BASED TIME AND ATTENDANCE TRACKING SYSTEM USING ANDROID APP...
A SMART, LOCATION BASED TIME AND ATTENDANCE TRACKING SYSTEM USING ANDROID APP...

A SMART, LOCATION BASED TIME AND ATTENDANCE TRACKING SYSTEM USING ANDROID APP...
Bug_Busters_Hackathon_AICoE_UniversityofDelaware.pptx

Bug_Busters_Hackathon_AICoE_UniversityofDelaware.pptx
"Inter- application vulnerabilities. hunting for bugs in secure applications"...

"Inter- application vulnerabilities. hunting for bugs in secure applications"...
What is security testing and why it is so important?

What is security testing and why it is so important?
IRJET- Preventing Phishing Attack using Evolutionary Algorithms

IRJET- Preventing Phishing Attack using Evolutionary Algorithms
Welcome to International Journal of Engineering Research and Development (IJERD)

Welcome to International Journal of Engineering Research and Development (IJERD)
Achievement summary during 2017 start with intro about IT depart.docx

Achievement summary during 2017 start with intro about IT depart.docx
Fingerprint Alert System A Solution for Effective Management System

Fingerprint Alert System A Solution for Effective Management System
Recently uploaded
0x01 - Newton's Third Law: Static vs. Dynamic Abusers

f you offer a service on the web, odds are that someone will abuse it. Be it an API, a SaaS, a PaaS, or even a static website, someone somewhere will try to figure out a way to use it to their own needs. In this talk we'll compare measures that are effective against static attackers and how to battle a dynamic attacker who adapts to your counter-measures.
About the Speaker
===============
Diogo Sousa, Engineering Manager @ Canonical
An opinionated individual with an interest in cryptography and its intersection with secure software development.
Competition and Regulation in Professional Services – KLEINER – June 2024 OEC...

Competition and Regulation in Professional Services – KLEINER – June 2024 OEC...OECD Directorate for Financial and Enterprise Affairs
This presentation by Morris Kleiner (University of Minnesota), was made during the discussion “Competition and Regulation in Professions and Occupations” held at the Working Party No. 2 on Competition and Regulation on 10 June 2024. More papers and presentations on the topic can be found out at oe.cd/crps.
This presentation was uploaded with the author’s consent.somanykidsbutsofewfathers-140705000023-phpapp02.pptx

Reminiscing on my Father and what he meant in my life, and regretting that so many children suffer and have no family in their home or lives...
International Workshop on Artificial Intelligence in Software Testing

International Workshop on Artificial Intelligence in
Software Testing
Sharpen existing tools or get a new toolbox? Contemporary cluster initiatives...

UIIN Conference, Madrid, 27-29 May 2024
James Wilson, Orkestra and Deusto Business School
Emily Wise, Lund University
Madeline Smith, The Glasgow School of Art
Eureka, I found it! - Special Libraries Association 2021 Presentation

Have you ever wondered how search works while visiting an e-commerce site, internal website, or searching through other types of online resources? Look no further than this informative session on the ways that taxonomies help end-users navigate the internet! Hear from taxonomists and other information professionals who have first-hand experience creating and working with taxonomies that aid in navigation, search, and discovery across a range of disciplines.
Getting started with Amazon Bedrock Studio and Control Tower

Getting started with Amazon Bedrock Studio and Control Tower
Acorn Recovery: Restore IT infra within minutes

Introducing Acorn Recovery as a Service, a simple, fast, and secure managed disaster recovery (DRaaS) by IP ServerOne. A DR solution that helps restore your IT infra within minutes.
Obesity causes and management and associated medical conditions

Obesity causes and management and associated medical conditionsFaculty of Medicine And Health Sciences
Causes and management of obesity and associated medical conditions Doctoral Symposium at the 17th IEEE International Conference on Software Test...

Doctoral Symposium at the 17th IEEE International Conference on Software Test...Sebastiano Panichella
Doctoral Symposium at the
17th IEEE International Conference on Software Testing, Verification and Validation
(ICST 2024)Announcement of 18th IEEE International Conference on Software Testing, Verif...

Announcement of 18th IEEE International Conference on Software Testing, Verif...Sebastiano Panichella
Announcement of 18th IEEE International Conference on Software Testing, Verification and Validation (ICST) 2025, Napoli, ItalyRecently uploaded (13)
0x01 - Newton's Third Law: Static vs. Dynamic Abusers

0x01 - Newton's Third Law: Static vs. Dynamic Abusers
Competition and Regulation in Professional Services – KLEINER – June 2024 OEC...

Competition and Regulation in Professional Services – KLEINER – June 2024 OEC...
somanykidsbutsofewfathers-140705000023-phpapp02.pptx

somanykidsbutsofewfathers-140705000023-phpapp02.pptx
International Workshop on Artificial Intelligence in Software Testing

International Workshop on Artificial Intelligence in Software Testing
Sharpen existing tools or get a new toolbox? Contemporary cluster initiatives...

Sharpen existing tools or get a new toolbox? Contemporary cluster initiatives...
Eureka, I found it! - Special Libraries Association 2021 Presentation

Eureka, I found it! - Special Libraries Association 2021 Presentation
Getting started with Amazon Bedrock Studio and Control Tower

Getting started with Amazon Bedrock Studio and Control Tower
Bitcoin Lightning wallet and tic-tac-toe game XOXO

Bitcoin Lightning wallet and tic-tac-toe game XOXO
Obesity causes and management and associated medical conditions

Obesity causes and management and associated medical conditions
Doctoral Symposium at the 17th IEEE International Conference on Software Test...

Doctoral Symposium at the 17th IEEE International Conference on Software Test...
Announcement of 18th IEEE International Conference on Software Testing, Verif...

Announcement of 18th IEEE International Conference on Software Testing, Verif...
How workplace surveillance works katrina hunos
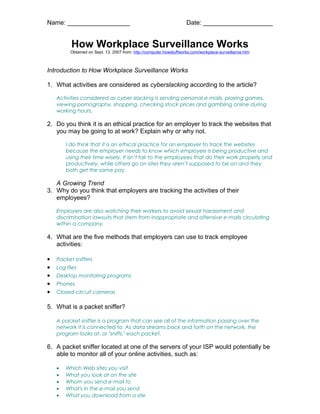
- 1. Name: __________________ Date: ____________________ How Workplace Surveillance Works Obtained on Sept. 13, 2007 from: http://computer.howstuffworks.com/workplace-surveillance.htm Introduction to How Workplace Surveillance Works 1. What activities are considered as cyberslacking according to the article? Activities considered as cyber slacking is sending personal e-mails, playing games, viewing pornography, shopping, checking stock prices and gambling online during working hours. 2. Do you think it is an ethical practice for an employer to track the websites that you may be going to at work? Explain why or why not. I do think that it is an ethical practice for an employer to track the websites because the employer needs to know which employee is being productive and using their time wisely. It isn’t fair to the employees that do their work properly and productively, while others go on sites they aren’t supposed to be on and they both get the same pay. A Growing Trend 3. Why do you think that employers are tracking the activities of their employees? Employers are also watching their workers to avoid sexual harassment and discrimination lawsuits that stem from inappropriate and offensive e-mails circulating within a company. 4. What are the five methods that employers can use to track employee activities: • Packet sniffers • Log files • Desktop monitoring programs • Phones • Closed-circuit cameras 5. What is a packet sniffer? A packet sniffer is a program that can see all of the information passing over the network it is connected to. As data streams back and forth on the network, the program looks at, or "sniffs," each packet. 6. A packet sniffer located at one of the servers of your ISP would potentially be able to monitor all of your online activities, such as: • Which Web sites you visit • What you look at on the site • Whom you send e-mail to • What's in the e-mail you send • What you download from a site
- 2. Name: __________________ Date: ____________________ • What streaming events you use, such as audio, video and Internet telephony Desktop Monitoring 7. Describe how a desktop monitoring system would monitor employees. Desktop monitoring programs have the ability to record every keystroke. When you are typing, a signal is sent from the keyboard to the application you are working in. This signal can be intercepted and either streamed back to the person who installed the monitoring program or recorded and sent back in a text file. 8. Explain how log files work? A system administrator can determine what Web sites you've accessed, whom you are sending e-mails to and receiving e-mails from and what applications are being used. 9. Where can log files be found? • Operating systems • Web browsers (in the form of a cache) • Applications (in the form of backups) • E-mail Traditional Eavesdropping 10.Describe how employers eavesdrop on their employees. Employers eavesdrop on their employees by listening through phone calls or placing a video camera in the employees work space. 11.Currently, 78 percent of all companies use some type of surveillance system. Here is a breakdown of the methods they use: • Storing and reviewing computer files: 36 percent • Video-recording employees: 15 percent • Recording and reviewing phone calls: 12 percent • Storing and reviewing voice mail: 8 percent