How to whitelist a email in a gmail
•Download as DOCX, PDF•
0 likes•4 views
Ensure important emails never get marked as spam by whitelisting them in Gmail. Follow our easy guide to learn how.” Is there anything else you need help with?
Report
Share
Report
Share
Recommended
Green Hectares Rural Tech Factsheet – Gmail

The factsheet designed to accompany the Gmail presentation. Green Hectares offers this content as part of an initiative to enable rural communities with technology.
Resolve Gmail Customer’s Issues in iPhone/iPad

How to resolve Gmail common issues in iPhone/ iPad? Need to fix your common Gmail issues? Find the 9 most prominent issues and their solutions here.
The Ultimate Guide To Hacking Gmail - Tips & Tricks For Marketers

These awesome tips & tricks will help you to hack your Gmail inbox to spend less time working & more time living!
Google slideshare tips by NEWOLDSTAMP

\All you need to know about the revamped Gmail. Best ways to organize Gmail, tips and tricks after the update.
Buy Old Gmail Accounts - Old Or New, 100% PVA Verified Accounts

Buy Gmail Account in bulk with instant delivery We offer aged old gmail accounts for sale, 100 secure and verified accounts with unique IPs
Glossary of important email marketing terms

Just go through the glossary of important Email marketing terms that You should know. Important terms used in Email marketing.
Gmail sign in, How to login to Gmail quickly

Sign in to the world's most popular email service: Gmail. Log in to your account or sign up at www.gmail.com to create a new account
Recommended
Green Hectares Rural Tech Factsheet – Gmail

The factsheet designed to accompany the Gmail presentation. Green Hectares offers this content as part of an initiative to enable rural communities with technology.
Resolve Gmail Customer’s Issues in iPhone/iPad

How to resolve Gmail common issues in iPhone/ iPad? Need to fix your common Gmail issues? Find the 9 most prominent issues and their solutions here.
The Ultimate Guide To Hacking Gmail - Tips & Tricks For Marketers

These awesome tips & tricks will help you to hack your Gmail inbox to spend less time working & more time living!
Google slideshare tips by NEWOLDSTAMP

\All you need to know about the revamped Gmail. Best ways to organize Gmail, tips and tricks after the update.
Buy Old Gmail Accounts - Old Or New, 100% PVA Verified Accounts

Buy Gmail Account in bulk with instant delivery We offer aged old gmail accounts for sale, 100 secure and verified accounts with unique IPs
Glossary of important email marketing terms

Just go through the glossary of important Email marketing terms that You should know. Important terms used in Email marketing.
Gmail sign in, How to login to Gmail quickly

Sign in to the world's most popular email service: Gmail. Log in to your account or sign up at www.gmail.com to create a new account
Introduction to Gmail - Instructions

Step-by-step instructions from our "Introduction to Gmail" course.
Learn all about Gmail, a free email service, set-up an account, and learn the basics of creating, sending, and forwarding a message.
10 Ways to Hack your Email Marketing

Here is a speech and presentation I gave at Inboundcon 2016 on October 6, 2016 in Toronto, Canada. Hope you enjoy!
Online Safety Data Privacy and Email Basics Digital Literacy Fundamentals.pptx

Online Safety Data Privacy and Email Basics Digital Literacy Fundamentals.pptxExcellence Foundation for South Sudan
Online Safety Data Privacy and Email Basics Digital Literacy Fundamentals a presentation by Ulak Matthew Thomas, a lecturer at Starford International University in Juba South Sudan InboundCon 2016: 10 Tricks to Growth Hack your Email Marketing - Jeff Goldenberg

While many marketing channels come and go, email marketing has been a mainstay for the past 15 years, thanks to high conversion rates and maximum personalization potential. Let Jeff Goldenberg, the Head of Growth at Borrowell and co-author of The Growth Hacker’s Guide to the Galaxy teach you tips and tricks on how to use email marketing to acquire, engage and retain your customers. This hyper-actionable talk will give you insights on how the best email marketers grow their lists, automate their work flows, nurture their leads, convert leads to customers, and turn customers into evangelists.
Jeff Goldenberg is the Head of Growth at Borrowell, a leading Canadian online marketplace lender. Jeff has been leading B2C startups for the past 15 years. He is the co-author of The Growth Hacker’s Guide to the Galaxy – 100 Proven growth hacks for the digital marketer. He is a sought after expert and speaker in the areas of digital marketing, growth hacking and business development for innovative, high-growth companies. He is an Entrepreneur-in-Residence at MaRS Discovery District as well as a mentor at the TechStars/Startup Next accelerator and 500 Startups Disto Dojo. Find him at www.jeffgoldenberg.net
My E-mail appears as spam | The 7 major reasons | Part 5#17

My E-mail appears as spam | The 7 major reasons | Part 5#17
http://o365info.com/my-e-mail-appears-as-spam-the-7-major-reasons-part-5-17
Review three major reasons, that could lead to a scenario, in which E-mail that is sent from our organization identified as spam mail:
1. E-mail content, 2. Violation of the SMTP standards, 3. Bulk\Mass mail
Eyal Doron | o365info.com
Stay Out of Spam Folder

This is very useful document provided by Sendgrid team. How to avoid reaching your email in spam folder. Hope this will be helpfull to you also. We (http://mystockalarm.com) are using Sendgrid transaction email service and we are happy until now. You can check with them for transaction and marketing emails.
Top email services providers to streamline your communication.pdf

Are you looking for an email service provider to help streamline your communication? Look no further! Here are the top email services providers to help you stay connected and organized.
Check out our list of the top email services providers to help you get the job done. With these services you can easily manage your emails and keep your communication sorted out.
https://www.webmaxy.co/egrowth/best-email-services-providers/
To get started, click the link below and take a 7 days free trial:
https://accounts.webmaxy.co/performance/register
Top email services providers to streamline your communication.pdf

Are you looking for an email service provider to help streamline your communication? Look no further! Here are the top email services providers to help you stay connected and organized.
Check out our list of the top email services providers to help you get the job done. With these services you can easily manage your emails and keep your communication sorted out.
https://www.webmaxy.co/egrowth/best-email-services-providers/
To get started, click the link below and take a 7 days free trial:
https://accounts.webmaxy.co/performance/register
A Simple Guide To Connect Your cPanel Email to Gmail .pdf

This blog will help you understand the nitty-gritty of connecting your cPanel email account to Gmail and also validate it for flawless communications.
Optimizing gmail

email has become the cornerstone of personal and professional communications
We can enhance output to next level by organizing, searching, and automating email
How to Create Gmail Account - Short Tutorials

Get to know the basic things about gmail account through shorttutorials.com
The 8-biggest-mistakes-email-marketers-make-how-to-avoid-them-marketo

The 8-biggest-mistakes-email-marketers-make-how-to-avoid-them-marketoMaria Pau, Intl' Best Selling Author, Multiple Award-Winning Coach
The 8-biggest-mistakes-email-marketers-make-how-to-avoid-them-By MarketoThe Complete Guide to B2B Email Marketing

The Complete Guide to B2B Email MarketingMaria Pau, Intl' Best Selling Author, Multiple Award-Winning Coach
The Complete Guide to B2B Email Marketing: Create more effective B2B email campaigns with these six steps:
By Sales Force-Pardot
Complete Guide to B2B Email Marketing will walk you through the entire process of creating effective,targeted emails — from planning and designing to sending and optimizing — in six straightforward steps:
Step 1: Authentication & Deliverability
Step 2: Template Design
Step 3: Email Content
Step 4: Testing & Optimization
Step 5: Sending Best Practices
Step 6: Tracking & Reporting
Take a Guided Tour with Pardot:
http://www2.pardot.com/interactive-guided-tour?url_called=70130000000mARf Email Deliverability

Email deliverability is on a lot of email marketers’ minds during the holidays because of increased volume from almost all senders.
Although delivery is important for seasonal email campaigns, delivering smarter is vital all year round. It’s more important than ever to make sure your messages not only get delivered, but also make it into the inbox where they can be seen and acted upon.
Following are copious notes about the recent shakeups at Gmail and Yahoo, as well as everyday delivery challenges. Inside this notebook are ideas and best practices for optimizing your inbox placement during the holidays
and all year long.
Included:
• Changes at Gmail and Yahoo
• What changes took place
• How they affect you (and the email industry)
• Whether you should react – and how
• Engagement as the key to the inbox
• How personalization and targeting improve delivery rates
• The effect of user engagement on your deliverability
• When it’s time to say good-bye
PHP Frameworks: I want to break free (IPC Berlin 2024)

In this presentation, we examine the challenges and limitations of relying too heavily on PHP frameworks in web development. We discuss the history of PHP and its frameworks to understand how this dependence has evolved. The focus will be on providing concrete tips and strategies to reduce reliance on these frameworks, based on real-world examples and practical considerations. The goal is to equip developers with the skills and knowledge to create more flexible and future-proof web applications. We'll explore the importance of maintaining autonomy in a rapidly changing tech landscape and how to make informed decisions in PHP development.
This talk is aimed at encouraging a more independent approach to using PHP frameworks, moving towards a more flexible and future-proof approach to PHP development.
State of ICS and IoT Cyber Threat Landscape Report 2024 preview

The IoT and OT threat landscape report has been prepared by the Threat Research Team at Sectrio using data from Sectrio, cyber threat intelligence farming facilities spread across over 85 cities around the world. In addition, Sectrio also runs AI-based advanced threat and payload engagement facilities that serve as sinks to attract and engage sophisticated threat actors, and newer malware including new variants and latent threats that are at an earlier stage of development.
The latest edition of the OT/ICS and IoT security Threat Landscape Report 2024 also covers:
State of global ICS asset and network exposure
Sectoral targets and attacks as well as the cost of ransom
Global APT activity, AI usage, actor and tactic profiles, and implications
Rise in volumes of AI-powered cyberattacks
Major cyber events in 2024
Malware and malicious payload trends
Cyberattack types and targets
Vulnerability exploit attempts on CVEs
Attacks on counties – USA
Expansion of bot farms – how, where, and why
In-depth analysis of the cyber threat landscape across North America, South America, Europe, APAC, and the Middle East
Why are attacks on smart factories rising?
Cyber risk predictions
Axis of attacks – Europe
Systemic attacks in the Middle East
Download the full report from here:
https://sectrio.com/resources/ot-threat-landscape-reports/sectrio-releases-ot-ics-and-iot-security-threat-landscape-report-2024/
More Related Content
Similar to How to whitelist a email in a gmail
Introduction to Gmail - Instructions

Step-by-step instructions from our "Introduction to Gmail" course.
Learn all about Gmail, a free email service, set-up an account, and learn the basics of creating, sending, and forwarding a message.
10 Ways to Hack your Email Marketing

Here is a speech and presentation I gave at Inboundcon 2016 on October 6, 2016 in Toronto, Canada. Hope you enjoy!
Online Safety Data Privacy and Email Basics Digital Literacy Fundamentals.pptx

Online Safety Data Privacy and Email Basics Digital Literacy Fundamentals.pptxExcellence Foundation for South Sudan
Online Safety Data Privacy and Email Basics Digital Literacy Fundamentals a presentation by Ulak Matthew Thomas, a lecturer at Starford International University in Juba South Sudan InboundCon 2016: 10 Tricks to Growth Hack your Email Marketing - Jeff Goldenberg

While many marketing channels come and go, email marketing has been a mainstay for the past 15 years, thanks to high conversion rates and maximum personalization potential. Let Jeff Goldenberg, the Head of Growth at Borrowell and co-author of The Growth Hacker’s Guide to the Galaxy teach you tips and tricks on how to use email marketing to acquire, engage and retain your customers. This hyper-actionable talk will give you insights on how the best email marketers grow their lists, automate their work flows, nurture their leads, convert leads to customers, and turn customers into evangelists.
Jeff Goldenberg is the Head of Growth at Borrowell, a leading Canadian online marketplace lender. Jeff has been leading B2C startups for the past 15 years. He is the co-author of The Growth Hacker’s Guide to the Galaxy – 100 Proven growth hacks for the digital marketer. He is a sought after expert and speaker in the areas of digital marketing, growth hacking and business development for innovative, high-growth companies. He is an Entrepreneur-in-Residence at MaRS Discovery District as well as a mentor at the TechStars/Startup Next accelerator and 500 Startups Disto Dojo. Find him at www.jeffgoldenberg.net
My E-mail appears as spam | The 7 major reasons | Part 5#17

My E-mail appears as spam | The 7 major reasons | Part 5#17
http://o365info.com/my-e-mail-appears-as-spam-the-7-major-reasons-part-5-17
Review three major reasons, that could lead to a scenario, in which E-mail that is sent from our organization identified as spam mail:
1. E-mail content, 2. Violation of the SMTP standards, 3. Bulk\Mass mail
Eyal Doron | o365info.com
Stay Out of Spam Folder

This is very useful document provided by Sendgrid team. How to avoid reaching your email in spam folder. Hope this will be helpfull to you also. We (http://mystockalarm.com) are using Sendgrid transaction email service and we are happy until now. You can check with them for transaction and marketing emails.
Top email services providers to streamline your communication.pdf

Are you looking for an email service provider to help streamline your communication? Look no further! Here are the top email services providers to help you stay connected and organized.
Check out our list of the top email services providers to help you get the job done. With these services you can easily manage your emails and keep your communication sorted out.
https://www.webmaxy.co/egrowth/best-email-services-providers/
To get started, click the link below and take a 7 days free trial:
https://accounts.webmaxy.co/performance/register
Top email services providers to streamline your communication.pdf

Are you looking for an email service provider to help streamline your communication? Look no further! Here are the top email services providers to help you stay connected and organized.
Check out our list of the top email services providers to help you get the job done. With these services you can easily manage your emails and keep your communication sorted out.
https://www.webmaxy.co/egrowth/best-email-services-providers/
To get started, click the link below and take a 7 days free trial:
https://accounts.webmaxy.co/performance/register
A Simple Guide To Connect Your cPanel Email to Gmail .pdf

This blog will help you understand the nitty-gritty of connecting your cPanel email account to Gmail and also validate it for flawless communications.
Optimizing gmail

email has become the cornerstone of personal and professional communications
We can enhance output to next level by organizing, searching, and automating email
How to Create Gmail Account - Short Tutorials

Get to know the basic things about gmail account through shorttutorials.com
The 8-biggest-mistakes-email-marketers-make-how-to-avoid-them-marketo

The 8-biggest-mistakes-email-marketers-make-how-to-avoid-them-marketoMaria Pau, Intl' Best Selling Author, Multiple Award-Winning Coach
The 8-biggest-mistakes-email-marketers-make-how-to-avoid-them-By MarketoThe Complete Guide to B2B Email Marketing

The Complete Guide to B2B Email MarketingMaria Pau, Intl' Best Selling Author, Multiple Award-Winning Coach
The Complete Guide to B2B Email Marketing: Create more effective B2B email campaigns with these six steps:
By Sales Force-Pardot
Complete Guide to B2B Email Marketing will walk you through the entire process of creating effective,targeted emails — from planning and designing to sending and optimizing — in six straightforward steps:
Step 1: Authentication & Deliverability
Step 2: Template Design
Step 3: Email Content
Step 4: Testing & Optimization
Step 5: Sending Best Practices
Step 6: Tracking & Reporting
Take a Guided Tour with Pardot:
http://www2.pardot.com/interactive-guided-tour?url_called=70130000000mARf Email Deliverability

Email deliverability is on a lot of email marketers’ minds during the holidays because of increased volume from almost all senders.
Although delivery is important for seasonal email campaigns, delivering smarter is vital all year round. It’s more important than ever to make sure your messages not only get delivered, but also make it into the inbox where they can be seen and acted upon.
Following are copious notes about the recent shakeups at Gmail and Yahoo, as well as everyday delivery challenges. Inside this notebook are ideas and best practices for optimizing your inbox placement during the holidays
and all year long.
Included:
• Changes at Gmail and Yahoo
• What changes took place
• How they affect you (and the email industry)
• Whether you should react – and how
• Engagement as the key to the inbox
• How personalization and targeting improve delivery rates
• The effect of user engagement on your deliverability
• When it’s time to say good-bye
Similar to How to whitelist a email in a gmail (20)
Online Safety Data Privacy and Email Basics Digital Literacy Fundamentals.pptx

Online Safety Data Privacy and Email Basics Digital Literacy Fundamentals.pptx
InboundCon 2016: 10 Tricks to Growth Hack your Email Marketing - Jeff Goldenberg

InboundCon 2016: 10 Tricks to Growth Hack your Email Marketing - Jeff Goldenberg
My E-mail appears as spam | The 7 major reasons | Part 5#17

My E-mail appears as spam | The 7 major reasons | Part 5#17
Top email services providers to streamline your communication.pdf

Top email services providers to streamline your communication.pdf
Top email services providers to streamline your communication.pdf

Top email services providers to streamline your communication.pdf
A Simple Guide To Connect Your cPanel Email to Gmail .pdf

A Simple Guide To Connect Your cPanel Email to Gmail .pdf
The 8-biggest-mistakes-email-marketers-make-how-to-avoid-them-marketo

The 8-biggest-mistakes-email-marketers-make-how-to-avoid-them-marketo
Understanding And Mastering Email Basics: A Guide for Every Email User. 

Understanding And Mastering Email Basics: A Guide for Every Email User.
Recently uploaded
PHP Frameworks: I want to break free (IPC Berlin 2024)

In this presentation, we examine the challenges and limitations of relying too heavily on PHP frameworks in web development. We discuss the history of PHP and its frameworks to understand how this dependence has evolved. The focus will be on providing concrete tips and strategies to reduce reliance on these frameworks, based on real-world examples and practical considerations. The goal is to equip developers with the skills and knowledge to create more flexible and future-proof web applications. We'll explore the importance of maintaining autonomy in a rapidly changing tech landscape and how to make informed decisions in PHP development.
This talk is aimed at encouraging a more independent approach to using PHP frameworks, moving towards a more flexible and future-proof approach to PHP development.
State of ICS and IoT Cyber Threat Landscape Report 2024 preview

The IoT and OT threat landscape report has been prepared by the Threat Research Team at Sectrio using data from Sectrio, cyber threat intelligence farming facilities spread across over 85 cities around the world. In addition, Sectrio also runs AI-based advanced threat and payload engagement facilities that serve as sinks to attract and engage sophisticated threat actors, and newer malware including new variants and latent threats that are at an earlier stage of development.
The latest edition of the OT/ICS and IoT security Threat Landscape Report 2024 also covers:
State of global ICS asset and network exposure
Sectoral targets and attacks as well as the cost of ransom
Global APT activity, AI usage, actor and tactic profiles, and implications
Rise in volumes of AI-powered cyberattacks
Major cyber events in 2024
Malware and malicious payload trends
Cyberattack types and targets
Vulnerability exploit attempts on CVEs
Attacks on counties – USA
Expansion of bot farms – how, where, and why
In-depth analysis of the cyber threat landscape across North America, South America, Europe, APAC, and the Middle East
Why are attacks on smart factories rising?
Cyber risk predictions
Axis of attacks – Europe
Systemic attacks in the Middle East
Download the full report from here:
https://sectrio.com/resources/ot-threat-landscape-reports/sectrio-releases-ot-ics-and-iot-security-threat-landscape-report-2024/
Designing Great Products: The Power of Design and Leadership by Chief Designe...

Designing Great Products: The Power of Design and Leadership by Chief Designer, Beats by Dr Dre
Epistemic Interaction - tuning interfaces to provide information for AI support

Paper presented at SYNERGY workshop at AVI 2024, Genoa, Italy. 3rd June 2024
https://alandix.com/academic/papers/synergy2024-epistemic/
As machine learning integrates deeper into human-computer interactions, the concept of epistemic interaction emerges, aiming to refine these interactions to enhance system adaptability. This approach encourages minor, intentional adjustments in user behaviour to enrich the data available for system learning. This paper introduces epistemic interaction within the context of human-system communication, illustrating how deliberate interaction design can improve system understanding and adaptation. Through concrete examples, we demonstrate the potential of epistemic interaction to significantly advance human-computer interaction by leveraging intuitive human communication strategies to inform system design and functionality, offering a novel pathway for enriching user-system engagements.
To Graph or Not to Graph Knowledge Graph Architectures and LLMs

Reflecting on new architectures for knowledge based systems in light of generative ai
GenAISummit 2024 May 28 Sri Ambati Keynote: AGI Belongs to The Community in O...

“AGI should be open source and in the public domain at the service of humanity and the planet.”
How world-class product teams are winning in the AI era by CEO and Founder, P...

How world-class product teams are winning in the AI era by CEO and Founder, Product School
From Siloed Products to Connected Ecosystem: Building a Sustainable and Scala...

From Siloed Products to Connected Ecosystem: Building a Sustainable and Scalable Platform by VP of Product, The New York Times
Accelerate your Kubernetes clusters with Varnish Caching

A presentation about the usage and availability of Varnish on Kubernetes. This talk explores the capabilities of Varnish caching and shows how to use the Varnish Helm chart to deploy it to Kubernetes.
This presentation was delivered at K8SUG Singapore. See https://feryn.eu/presentations/accelerate-your-kubernetes-clusters-with-varnish-caching-k8sug-singapore-28-2024 for more details.
Mission to Decommission: Importance of Decommissioning Products to Increase E...

Mission to Decommission: Importance of Decommissioning Products to Increase Enterprise-Wide Efficiency by VP Data Platform, American Express
UiPath Test Automation using UiPath Test Suite series, part 3

Welcome to UiPath Test Automation using UiPath Test Suite series part 3. In this session, we will cover desktop automation along with UI automation.
Topics covered:
UI automation Introduction,
UI automation Sample
Desktop automation flow
Pradeep Chinnala, Senior Consultant Automation Developer @WonderBotz and UiPath MVP
Deepak Rai, Automation Practice Lead, Boundaryless Group and UiPath MVP
Neuro-symbolic is not enough, we need neuro-*semantic*

Neuro-symbolic (NeSy) AI is on the rise. However, simply machine learning on just any symbolic structure is not sufficient to really harvest the gains of NeSy. These will only be gained when the symbolic structures have an actual semantics. I give an operational definition of semantics as “predictable inference”.
All of this illustrated with link prediction over knowledge graphs, but the argument is general.
Search and Society: Reimagining Information Access for Radical Futures

The field of Information retrieval (IR) is currently undergoing a transformative shift, at least partly due to the emerging applications of generative AI to information access. In this talk, we will deliberate on the sociotechnical implications of generative AI for information access. We will argue that there is both a critical necessity and an exciting opportunity for the IR community to re-center our research agendas on societal needs while dismantling the artificial separation between the work on fairness, accountability, transparency, and ethics in IR and the rest of IR research. Instead of adopting a reactionary strategy of trying to mitigate potential social harms from emerging technologies, the community should aim to proactively set the research agenda for the kinds of systems we should build inspired by diverse explicitly stated sociotechnical imaginaries. The sociotechnical imaginaries that underpin the design and development of information access technologies needs to be explicitly articulated, and we need to develop theories of change in context of these diverse perspectives. Our guiding future imaginaries must be informed by other academic fields, such as democratic theory and critical theory, and should be co-developed with social science scholars, legal scholars, civil rights and social justice activists, and artists, among others.
FIDO Alliance Osaka Seminar: The WebAuthn API and Discoverable Credentials.pdf

FIDO Alliance Osaka Seminar
From Daily Decisions to Bottom Line: Connecting Product Work to Revenue by VP...

From Daily Decisions to Bottom Line: Connecting Product Work to Revenue by VP of Product, Amplitude
GDG Cloud Southlake #33: Boule & Rebala: Effective AppSec in SDLC using Deplo...

Effective Application Security in Software Delivery lifecycle using Deployment Firewall and DBOM
The modern software delivery process (or the CI/CD process) includes many tools, distributed teams, open-source code, and cloud platforms. Constant focus on speed to release software to market, along with the traditional slow and manual security checks has caused gaps in continuous security as an important piece in the software supply chain. Today organizations feel more susceptible to external and internal cyber threats due to the vast attack surface in their applications supply chain and the lack of end-to-end governance and risk management.
The software team must secure its software delivery process to avoid vulnerability and security breaches. This needs to be achieved with existing tool chains and without extensive rework of the delivery processes. This talk will present strategies and techniques for providing visibility into the true risk of the existing vulnerabilities, preventing the introduction of security issues in the software, resolving vulnerabilities in production environments quickly, and capturing the deployment bill of materials (DBOM).
Speakers:
Bob Boule
Robert Boule is a technology enthusiast with PASSION for technology and making things work along with a knack for helping others understand how things work. He comes with around 20 years of solution engineering experience in application security, software continuous delivery, and SaaS platforms. He is known for his dynamic presentations in CI/CD and application security integrated in software delivery lifecycle.
Gopinath Rebala
Gopinath Rebala is the CTO of OpsMx, where he has overall responsibility for the machine learning and data processing architectures for Secure Software Delivery. Gopi also has a strong connection with our customers, leading design and architecture for strategic implementations. Gopi is a frequent speaker and well-known leader in continuous delivery and integrating security into software delivery.
ODC, Data Fabric and Architecture User Group

Let's dive deeper into the world of ODC! Ricardo Alves (OutSystems) will join us to tell all about the new Data Fabric. After that, Sezen de Bruijn (OutSystems) will get into the details on how to best design a sturdy architecture within ODC.
Bits & Pixels using AI for Good.........

A whirlwind tour of tech & AI for socio-environmental impact.
Recently uploaded (20)
PHP Frameworks: I want to break free (IPC Berlin 2024)

PHP Frameworks: I want to break free (IPC Berlin 2024)
State of ICS and IoT Cyber Threat Landscape Report 2024 preview

State of ICS and IoT Cyber Threat Landscape Report 2024 preview
FIDO Alliance Osaka Seminar: FIDO Security Aspects.pdf

FIDO Alliance Osaka Seminar: FIDO Security Aspects.pdf
Designing Great Products: The Power of Design and Leadership by Chief Designe...

Designing Great Products: The Power of Design and Leadership by Chief Designe...
Epistemic Interaction - tuning interfaces to provide information for AI support

Epistemic Interaction - tuning interfaces to provide information for AI support
To Graph or Not to Graph Knowledge Graph Architectures and LLMs

To Graph or Not to Graph Knowledge Graph Architectures and LLMs
GenAISummit 2024 May 28 Sri Ambati Keynote: AGI Belongs to The Community in O...

GenAISummit 2024 May 28 Sri Ambati Keynote: AGI Belongs to The Community in O...
How world-class product teams are winning in the AI era by CEO and Founder, P...

How world-class product teams are winning in the AI era by CEO and Founder, P...
From Siloed Products to Connected Ecosystem: Building a Sustainable and Scala...

From Siloed Products to Connected Ecosystem: Building a Sustainable and Scala...
Accelerate your Kubernetes clusters with Varnish Caching

Accelerate your Kubernetes clusters with Varnish Caching
Mission to Decommission: Importance of Decommissioning Products to Increase E...

Mission to Decommission: Importance of Decommissioning Products to Increase E...
UiPath Test Automation using UiPath Test Suite series, part 3

UiPath Test Automation using UiPath Test Suite series, part 3
Neuro-symbolic is not enough, we need neuro-*semantic*

Neuro-symbolic is not enough, we need neuro-*semantic*
Search and Society: Reimagining Information Access for Radical Futures

Search and Society: Reimagining Information Access for Radical Futures
FIDO Alliance Osaka Seminar: The WebAuthn API and Discoverable Credentials.pdf

FIDO Alliance Osaka Seminar: The WebAuthn API and Discoverable Credentials.pdf
FIDO Alliance Osaka Seminar: Passkeys at Amazon.pdf

FIDO Alliance Osaka Seminar: Passkeys at Amazon.pdf
From Daily Decisions to Bottom Line: Connecting Product Work to Revenue by VP...

From Daily Decisions to Bottom Line: Connecting Product Work to Revenue by VP...
GDG Cloud Southlake #33: Boule & Rebala: Effective AppSec in SDLC using Deplo...

GDG Cloud Southlake #33: Boule & Rebala: Effective AppSec in SDLC using Deplo...
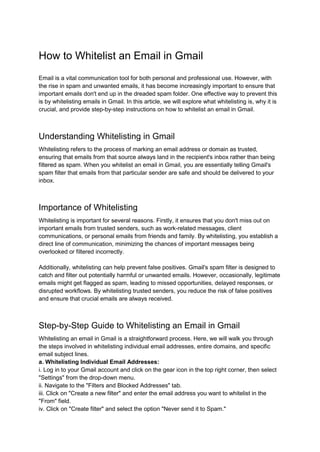
How to whitelist a email in a gmail
- 1. How to Whitelist an Email in Gmail Email is a vital communication tool for both personal and professional use. However, with the rise in spam and unwanted emails, it has become increasingly important to ensure that important emails don't end up in the dreaded spam folder. One effective way to prevent this is by whitelisting emails in Gmail. In this article, we will explore what whitelisting is, why it is crucial, and provide step-by-step instructions on how to whitelist an email in Gmail. Understanding Whitelisting in Gmail Whitelisting refers to the process of marking an email address or domain as trusted, ensuring that emails from that source always land in the recipient's inbox rather than being filtered as spam. When you whitelist an email in Gmail, you are essentially telling Gmail's spam filter that emails from that particular sender are safe and should be delivered to your inbox. Importance of Whitelisting Whitelisting is important for several reasons. Firstly, it ensures that you don't miss out on important emails from trusted senders, such as work-related messages, client communications, or personal emails from friends and family. By whitelisting, you establish a direct line of communication, minimizing the chances of important messages being overlooked or filtered incorrectly. Additionally, whitelisting can help prevent false positives. Gmail's spam filter is designed to catch and filter out potentially harmful or unwanted emails. However, occasionally, legitimate emails might get flagged as spam, leading to missed opportunities, delayed responses, or disrupted workflows. By whitelisting trusted senders, you reduce the risk of false positives and ensure that crucial emails are always received. Step-by-Step Guide to Whitelisting an Email in Gmail Whitelisting an email in Gmail is a straightforward process. Here, we will walk you through the steps involved in whitelisting individual email addresses, entire domains, and specific email subject lines. a. Whitelisting Individual Email Addresses: i. Log in to your Gmail account and click on the gear icon in the top right corner, then select "Settings" from the drop-down menu. ii. Navigate to the "Filters and Blocked Addresses" tab. iii. Click on "Create a new filter" and enter the email address you want to whitelist in the "From" field. iv. Click on "Create filter" and select the option "Never send it to Spam."
- 2. v. Finally, click on "Create filter" to save the changes. b. Whitelisting Entire Domains: i. Follow steps i and ii from the previous section. ii. Enter the domain name (e.g., example.com) in the "From" field. iii. Click on "Create filter" and select the option "Never send it to Spam." iv. Save the changes by clicking on "Create filter." c. Whitelisting Specific Email Subject Lines: i. Repeat steps i and ii from the previous sections. ii. Enter the desired email subject line in the "Has the words" field. iii. Click on "Create filter" and select the option "Never send it to Spam." iv. Save the changes by clicking on "Create filter." Advanced Tips and Tricks for Effective Whitelisting While the basic steps covered in the previous section are sufficient for most users, there are a few additional techniques and strategies to enhance your whitelisting experience in Gmail. Here are some advanced tips and tricks: a. Whitelisting with Priority Inbox: Gmail's Priority Inbox feature automatically separates important emails from the rest. By marking emails from trusted senders as important, you can ensure they are prominently displayed in your inbox. b. Utilizing Filters: Gmail's filtering options provide granular control over your inbox. You can create filters to automatically categorize emails, assign labels, and bypass the spam filter for specific senders or domains. c. Reporting Spam: Gmail's spam filter continually learns from user feedback. By reporting spam emails, especially false positives, you contribute to the system's improvement and help prevent similar emails from being misclassified in the future. Troubleshooting Common Whitelisting Issues Despite the simplicity of whitelisting in Gmail, you may encounter some issues or limitations. In this section, we address common problems and provide solutions to ensure smooth whitelisting. Conclusion Whitelisting emails in Gmail is an essential practice to ensure that important messages are delivered to your inbox. By following the step-by-step guide and implementing the advanced tips discussed in this article, you can take control of your email experience, reduce the chances of missed opportunities, and streamline your communication processes. Stay connected, stay organized, and make the most of your Gmail inbox.