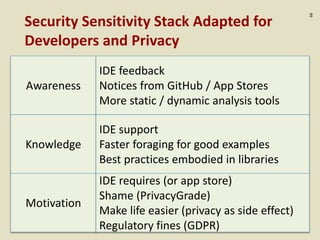
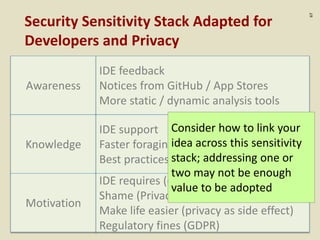
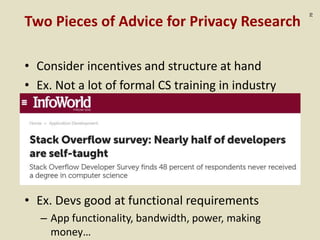
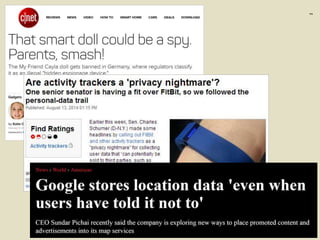
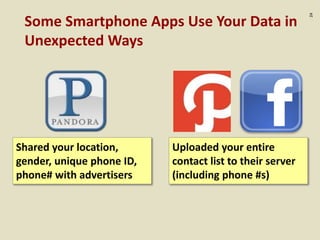
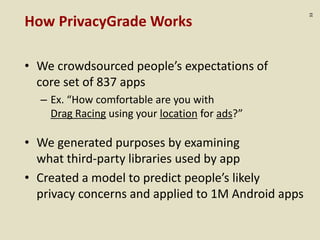
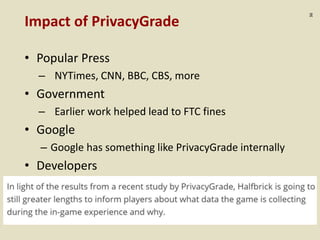
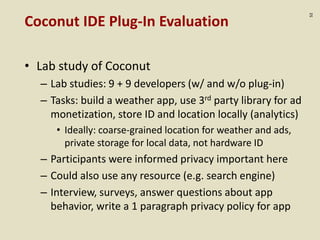
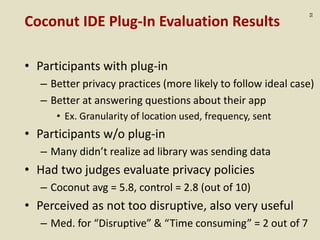
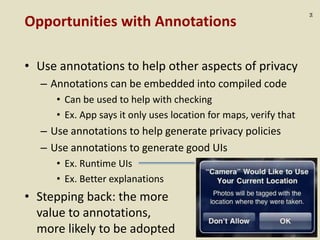
The document discusses the challenges of managing privacy in smartphone app development, emphasizing the complexity and ambiguity of privacy as a concept. It highlights the lack of common best practices for privacy, the rapid growth of technological capabilities, and the importance of improving developer knowledge and tools, such as the Coconut IDE plugin and PrivacyGrade.org. The presentation also stresses the need for developers to be better equipped with privacy guidelines and practical solutions to address these concerns effectively.
![:15
“[An analyst at Target] was able to identify about
25 products that… allowed him to assign each
shopper a ‘pregnancy prediction’ score. [H]e
could also estimate her due date to within a small
window, so Target could send coupons timed to
very specific stages of her pregnancy.” (NYTimes)](https://image.slidesharecdn.com/privacy-vlhcc-sep2018-181004155735/85/Helping-Developers-with-Privacy-15-320.jpg)





![:40
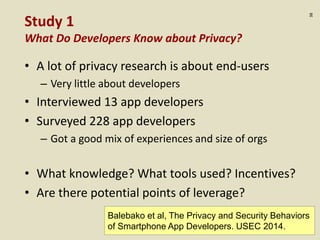
Study 1 Summary of Findings
Third-party Libraries Problematic
• Use ads and analytics to monetize
• Hard to understand their behaviors
– A few didn’t know they were using libraries
(based on inconsistent answers)
– Some didn’t know the libraries collected data
– “If either Facebook or Flurry had a privacy policy that
was short and concise and condensed into real
English rather than legalese, we definitely would
have read it.”
– In a later study we did on apps, we found 40% apps
used sensitive data only b/c of libraries [Chitkara 2017]](https://image.slidesharecdn.com/privacy-vlhcc-sep2018-181004155735/85/Helping-Developers-with-Privacy-40-320.jpg)
![:41
Study 1 Summary of Findings
Devs Don’t Know What to Do
• Low awareness of existing privacy guidelines
– Fair Information Practices, FTC guidelines, Google
– Often just ask others around them
• Low perceived value of privacy policies
– Mostly protection from lawsuits
– “I haven’t even read [our privacy policy]. I mean, it’s
just legal stuff that’s required, so I just put in there.”](https://image.slidesharecdn.com/privacy-vlhcc-sep2018-181004155735/85/Helping-Developers-with-Privacy-41-320.jpg)
![:56
PrivacyStreams Programming Model
Observation 2: Difficult for Devs to Get Sensitive Data
int sampleRate = 8000;
int bufferSize = AudioRecord.getMinBufferSize(sampleRate, AudioFormat.CHANNEL_IN_DEFAULT,
AudioFormat.ENCODING_PCM_16BIT);
AudioRecord audioRecord = new AudioRecord(MediaRecorder.AudioSource.MIC, sampleRate,
AudioFormat.CHANNEL_IN_DEFAULT, AudioFormat.ENCODING_PCM_16BIT, bufferSize);
Deal with encoding, format, etc.
audioRecord.startRecording();
long startTime = System.currentTimeMillis();
double rmsAmplitude = 0;
long bufferTotalLen = 0;
while (true) {
short[] buffer = new short[bufferSize];
int bufferLen = audioRecord.read(buffer, 0, bufferSize);
for (int i=0; i < bufferLen; i++) {
rmsAmplitude += (double) buffer[i] * buffer[i] / 10000;
}
bufferTotalLen += bufferLen;
long currentTime = System.currentTimeMillis();
if (currentTime - startTime > DURATION) {
break;
}
}
Process raw data
while (true) {
// …
try {
Thread.sleep(INTERVAL);
} catch (InterruptedException e) {
e.printStackTrace();
}
}
Handle threads
if (ContextCompat.checkSelfPermission(this.context,
Manifest.permission.RECORD_AUDIO)
!= PackageManager.PERMISSION_GRANTED) {
Log.d("Task0", "Permission denied.");
ActivityCompat.requestPermissions(thisActivity,
new String[]{Manifest.permission.READ_CONTACTS}, 1);
return;
} Handle permissions](https://image.slidesharecdn.com/privacy-vlhcc-sep2018-181004155735/85/Helping-Developers-with-Privacy-56-320.jpg)