Glossary_Tech_ January 23.docx
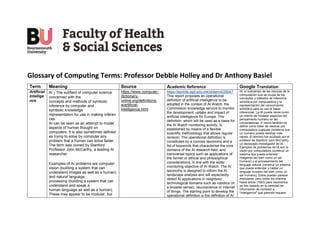
- 1. Glossary of Computing Terms: Professor Debbie Holley and Dr Anthony Basiel Term Meaning Source Academic Reference Google Translation Artificial Intellige nce AI - The subfield of computer science concerned with the concepts and methods of symbolic inference by computer and symbolic knowledge representation for use in making inferen ces. AI can be seen as an attempt to model aspects of human thought on computers. It is also sometimes defined as trying to solve by computer any problem that a human can solve faster. The term was coined by Stanford Professor John McCarthy, a leading AI researcher. Examples of AI problems are computer vision (building a system that can understand images as well as a human) and natural language processing (building a system that can understand and speak a human language as well as a human). These may appear to be modular, but https://www.computer- dictionary- online.org/definitions- a/artificial- intelligence.html https://eprints.ugd.edu.mk/id/eprint/28047 This report proposes an operational definition of artificial intelligence to be adopted in the context of AI Watch, the Commission knowledge service to monitor the development, uptake and impact of artificial intelligence for Europe. The definition, which will be used as a basis for the AI Watch monitoring activity, is established by means of a flexible scientific methodology that allows regular revision. The operational definition is constituted by a concise taxonomy and a list of keywords that characterise the core domains of the AI research field, and transversal topics such as applications of the former or ethical and philosophical considerations, in line with the wider monitoring objective of AI Watch. The AI taxonomy is designed to inform the AI landscape analysis and will expectedly detect AI applications in neighbour technological domains such as robotics (in a broader sense), neuroscience or internet of things. The starting point to develop the operational definition is the definition of AI IA: el subcampo de las ciencias de la computación que se ocupa de los conceptos y métodos de inferencia simbólica por computadora y la representación del conocimiento simbólico para su uso al hacer inferencias. La IA puede verse como un intento de modelar aspectos del pensamiento humano en las computadoras. A veces también se define como tratar de resolver por computadora cualquier problema que un humano pueda resolver más rápido. El término fue acuñado por el profesor de Stanford John McCarthy, un destacado investigador de IA. Ejemplos de problemas de IA son la visión por computadora (construir un sistema que pueda entender imágenes tan bien como un ser humano) y el procesamiento del lenguaje natural (construir un sistema que pueda entender y hablar un lenguaje humano tan bien como un ser humano). Estos pueden parecer modulares, pero todos los intentos hasta ahora (1993) para resolverlos se han basado en la cantidad de información de contexto e "inteligencia" que parecen requerir.
- 2. all attempts so far (1993) to solve them have foundered on the amount of context information and "intelligence" they seem to require. adopted by the High Level Expert Group on artificial intelligence. To derive this operational definition we have followed a mixed methodology. On one hand, we apply natural language processing methods to a large set of AI literature. On the other hand, we carry out a qualitative analysis on 55 key documents including artificial intelligence definitions from three complementary perspectives: policy, research and industry. A valuable contribution of this work is the collection of definitions developed between 1955 and 2019, and the summarisation of the main features of the concept of artificial intelligence as reflected in the relevant literature. Augmen ted reality Augmented reality (AR) is an enhanced version of the real physical world that is achieved through the use of digital visual elements, sound, or other sensory stimuli and delivered via technology. https://www.investopedi a.com/terms/a/augment ed-reality.asp https://www.sciencedirect.com/science/a rticle/pii/S1876139918302688#tbl2 “A type of virtual reality in which synthetic stimuli are superimposed on real-world objects usually to make information that is otherwise imperceptible to human senses perceptible” A technology that overlays digital computer-generated information on objects or places in the real world for the purpose of enhancing the user experience (DoD, 2018). The combination of reality and overlay of digital information designed to enhance the learning process. La realidad aumentada (AR) es una versión mejorada del mundo físico real que se logra mediante el uso de elementos visuales digitales, sonido u otros estímulos sensoriales y se entrega a través de la tecnología.
- 3. A spectrum of mixed reality simulation that is part way between the real world and the virtual world (p. 206). “A form of virtual reality that includes head-mounted displays, overlays of computer screens, wearable computers, or displays projected onto humans and manikins” (p.4). [A technology which] supplements the real world with virtual (computer- generated) objects that appear to coexist in the same space as the real world. While many researchers broaden the definition of AR beyond this vision, we define an AR system to have the following properties: combines real and virtual objects in a real environment; runs interactively, and in real time; and registers (aligns) real and virtual objects with each other.” (p.34). Avatar (in Comput ing) an icon or figure representing a particular person in a video game, internet forum, etc. "conversation is depicted in a balloon over the avatar's head" https://languages.oup.co m/google-dictionary-en/ https://jvwr-ojs- utexas.tdl.org/jvwr/article/view/283/237 An avatar is any digital representation (graphical or textual), beyond a simple label or name, that has agency (an ability to perform actions) and is controlled by a human agent in real time. un icono o figura que representa a una persona en particular en un videojuego, foro de Internet, etc. "la conversación se representa en un globo sobre la cabeza del avatar" Blockch ain * a blockchain is like a digital ledger that keeps track of every transaction made with a coin. Also, tell them that a private key is like a password that allows you to access your funds. ** a system in which a record of transactions, especially those made in * https://indianexpress.co m/article/technology/cry pto/how-to-introduce- cryptocurrency-to- parents-a-step-by-step- guide-8148671/ https://arxiv.org/abs/2102.03750 A blockchain is designed specifically to guarantee full memory of all transactions open to any anonymous user to enable the distributed validation of transactions avoiding trusted intermediaries. But the blockchain alone is meaningless without * una cadena de bloques es como un libro de contabilidad digital que realiza un seguimiento de cada transacción realizada con una moneda. Además, dígales que una clave privada es como una contraseña que le permite acceder a sus fondos.
- 4. a cryptocurrency, is maintained across computers that are linked in a peer-to- peer network. "we can actually have a look at the blockchain and see evidence of what's going on" *** a system of recording information in a way that makes it difficult or impossible to change, hack, or cheat the system. A blockchain is essentially a digital ledger of transactions that is duplicated and distributed across the entire network of computer systems on the blockchain. ** https://languages.oup.co m/google-dictionary-en/ *** https://www.euromoney. com/learning/blockchain -explained/what-is- blockchain a mechanism that safeguard the historical records of transactions from tampering attacks, this is why a STRONG DISTRIBUTED CONSENSUS PROTOCOL becomes essential. ** un sistema en el que se mantiene un registro de transacciones, especialmente aquellas realizadas en una criptomoneda, a través de computadoras que están vinculadas en una red de igual a igual. "Podemos realmente echar un vistazo a la cadena de bloques y ver evidencia de lo que está pasando" *** un sistema de registro de información de una manera que hace que sea difícil o imposible cambiar, piratear o engañar al sistema. Una cadena de bloques es esencialmente un libro de contabilidad digital de transacciones que se duplica y distribuye en toda la red de sistemas informáticos de la cadena de bloques. Cyber privacy covers the amount of online security available for personal and financial data, communications, and preferences. Internet users often attempt to increase online privacy through anti-virus software, strong password choices, turning off tracking, reviewing site security, and opting for stricter privacy settings. https://www.winston.co m/en/legal- glossary/online- privacy.html#:~:text=It% 20covers%20the%20am ount%20of,opting%20for %20stricter%20privacy %20settings. https://ieeexplore.ieee.org/abstract/d ocument/8029333 Security definitions such as semantic security do not by themselves guarantee privacy; the inferences that can be made by combining the results obtained at the end of the protocol execution with any additional knowledge that an attacker may possess could result in privacy breaches. To address this challenge, we need a sensitive information inference-based framework as the foundation for measuring privacy. Although there are attempts at coming up with a privacy solution/definition that can address different scenarios, we believe that there is no “one size fits all” solution for data privacy for many application settings. Instead, multiple cubre la cantidad de seguridad en línea disponible para datos personales y financieros, comunicaciones y preferencias. Los usuarios de Internet a menudo intentan aumentar la privacidad en línea a través de software antivirus, opciones de contraseña seguras, desactivando el seguimiento, revisando la seguridad del sitio y optando por configuraciones de privacidad más estrictas.
- 5. dimensions need to be tailored for different application domains to achieve practical solutions. As we discussed above, different domains require different definitions of data utility. Second, we need to understand the right values for privacy metrics. For example, ε=1 could be considered an appropriate risk for differentially private data mining models. Finally, the computational, storage and communication costs of given protocols need to be considered. These costs could be especially significant for privacy-preserving protocols that involve cryptography. Cyber worlds The world of intercomputer communication. (countable, computing) A real or virtual world of information in cyberspace. https://en.wiktionary.org/ wiki/cyberworld#:~:text= Noun,world%20of%20inf ormation%20in%20cybe rspace. https://ieeexplore.ieee.org/abstract/d ocument/9480910 Example of a cyber world El mundo de la comunicación intercomputadora. (contable, informática) Un mundo real o virtual de información en el ciberespacio. Cyberse curity protection against unauthorized access to, or alteration of, information and system resources including CPUs, storage devices and programs. https://www.computer- dictionary- online.org/definitions- s/security.html https://www.timreview.ca/article/835 1. “Cybersecurity consists largely of defensive methods used to detect and thwart would-be intruders.” (Kemmerer, 2003) protección contra el acceso no autorizado o la alteración de la información y los recursos del sistema, incluidas las CPU, los dispositivos de almacenamiento y los programas. La seguridad incluye:
- 6. Security includes: * confidentiality - preventing unauthorized access; integrity - preventing or detecting unauthorized modification of information. * authentication - determining whether a user is who they claim to be. * access control - ensuring that users can access the resources, and only the resources, that they are authorised to. * nonrepudiation - proof that a message came from a certain source. * availability - ensuring that a system is operational and accessible to authorised users despite hardware or software failures or attack. * privacy - allowing people to know and control how information is collected about them and how it is used. Security can also be considered in the following terms: * physical security - who can touch the system to operate or modify it, protection against the physical environment - heat, earthquake, etc. 2. “Cybersecurity entails the safeguarding of computer networks and the information they contain from penetration and from malicious damage or disruption.” (Lewis, 2006) 3. “Cyber Security involves reducing the risk of malicious attack to software, computers and networks. This includes tools used to detect break-ins, stop viruses, block malicious access, enforce authentication, enable encrypted communications, and on and on.” (Amoroso, 2006) 4. “Cybersecurity is the collection of tools, policies, security concepts, security safeguards, guidelines, risk management approaches, actions, training, best practices, assurance and technologies that can be used to protect the cyber environment and organization and user's assets.” (ITU, 2009) 5. “The ability to protect or defend the use of cyberspace from cyber- attacks.” (CNSS, 2010) 6. “The body of technologies, processes, practices and response and mitigation measures designed to protect networks, computers, programs and data from attack, damage or unauthorized access so as to ensure confidentiality, integrity and availability.” (Public Safety Canada, 2014) 7. “The art of ensuring the existence and continuity of the information society of a nation, guaranteeing * confidencialidad: prevención del acceso no autorizado; integridad: prevenir o detectar la modificación no autorizada de la información. * autenticación: determinar si un usuario es quien dice ser. * control de acceso: garantizar que los usuarios puedan acceder a los recursos, y solo a los recursos, para los que están autorizados. * no repudio - prueba de que un mensaje proviene de una determinada fuente. * disponibilidad: garantizar que un sistema esté operativo y accesible para los usuarios autorizados a pesar de las fallas o ataques de hardware o software. * privacidad: permitir que las personas sepan y controlen cómo se recopila la información sobre ellos y cómo se utiliza. La seguridad también puede considerarse en los siguientes términos: * seguridad física - quién puede tocar el sistema para operarlo o modificarlo, protección contra el entorno físico - calor, terremoto, etc. * seguridad operativa/procesal: quién está autorizado para hacer o es responsable de hacer qué y cuándo, quién puede autorizar a otros a hacer qué y quién tiene que informar qué a quién. * personal de seguridad: contratación de empleados, verificación de antecedentes, capacitación, sesiones informativas de seguridad, seguimiento y manejo de salidas. * Seguridad del sistema: controles de autenticación y acceso de usuarios, asignación de privilegios, mantenimiento de la integridad de archivos y sistemas de archivos, copias de seguridad, procesos de supervisión, mantenimiento de registros y auditoría.
- 7. * operational/procedural security - who is authorised to do or responsible for doing what and when, who can authorise others to do what and who has to report what to who. * personnel security - hiring employees, background screening, training, security briefings, monitoring and handling departures. * System security - User access and authentication controls, assignment of privilege, maintaining file and filesystem integrity, backup, monitoring processes, log-keeping, and auditing. * network security - protecting network and telecommunications equipment, protecting network servers and transmissions, combatting eavesdropping, controlling access from untrusted networks, firewalls, and intrusion detection. Encryption is one important technique used to improve data security. OWASP is the free and open application security community. and protecting, in Cyberspace, its information, assets and critical infrastructure.” (Canongia & Mandarino, 2014) 8. “The state of being protected against the criminal or unauthorized use of electronic data, or the measures taken to achieve this.” (Oxford University Press, 2014) 9. “The activity or process, ability or capability, or state whereby information and communications systems and the information contained therein are protected from and/or defended against damage, unauthorized use or modification, or exploitation.” (DHS, 2014) * seguridad de red: protección de equipos de red y telecomunicaciones, protección de servidores y transmisiones de red, lucha contra las escuchas ilegales, control de acceso desde redes no confiables, firewalls y detección de intrusos. El cifrado es una técnica importante utilizada para mejorar la seguridad de los datos. OWASP es la comunidad de seguridad de aplicaciones gratuita y abierta. Extende d reality XR is an emerging umbrella term for all the immersive technologies. The ones we already have today—augmented reality (AR), virtual reality (VR), and mixed reality (MR) plus those that are still to be created. All immersive https://www.forbes.com/ sites/bernardmarr/2019/ 08/12/what-is-extended- reality-technology-a- simple-explanation-for- https://www.mdpi.com/2075- 5309/12/12/2169 XR is an umbrella term that refers to all types of real and virtual combined environments. VR, AR, and MR are different modalities with different XR es un término general emergente para todas las tecnologías inmersivas. Los que ya tenemos hoy: realidad aumentada (AR), realidad virtual (VR) y realidad mixta (MR), además de los que aún no se han creado. Todas las tecnologías
- 8. technologies extend the reality we experience by either blending the virtual and “real” worlds or by creating a fully immersive experience. anyone/?sh=77da0a9f7 249 characteristics, but it is difficult for non- experts to distinguish them clearly because their definitions are often inconsistent and used interchangeably. inmersivas amplían la realidad que experimentamos ya sea combinando los mundos virtual y “real” o creando una experiencia totalmente inmersiva. Internet of things the interconnection via the internet of computing devices embedded in everyday objects, enabling them to send and receive data. "if one thing can prevent the internet of things from transforming the way we live and work, it will be a breakdown in security" https://languages.oup.co m/google-dictionary-en/ https://ieeexplore.ieee.org/abstract/d ocument/7373221 Sensor(s) and/or actuator(s) carrying out a specific function and that are able to communicate with other equipment. It is part of an infrastructure allowing the transport, storage, processing and access to the generated data by users or other systems. IoT is a group of infrastructures interconnecting connected objects and allowing their management, data mining and the access to the data they generate. la interconexión a través de Internet de dispositivos informáticos integrados en objetos cotidianos, lo que les permite enviar y recibir datos. "Si algo puede evitar que el internet de las cosas transforme la forma en que vivimos y trabajamos, será una falla en la seguridad" Metaver se “the metaverse” can include virtual reality—characterized by persistent virtual worlds that continue to exist even when you're not playing—as well as augmented reality that combines aspects of the digital and physical worlds. However, it doesn't require that those spaces be exclusively accessed via VR or AR. Virtual worlds—such as aspects of Fortnite that can be accessed through PCs, game consoles, and even phones—have started referring to themselves as “the metaverse.” Original term from: Crash, S., 2000. Neal Stephenson. Bantam Doubleday Dell, reprint. https://www.wired.com/s tory/what-is-the- metaverse/ https://www.mdpi.com/1999- 5903/14/11/310 “The Metaverse is a massively scaled and interoperable network of real-time rendered 3D virtual worlds which can be experienced synchronously and persistently by an effectively unlimited number of users with an individual sense of presence, and with continuity of data, such as identity, history, entitlements, objects, communications, and payments.” Crash, S., 2000. Neal Stephenson. Bantam Doubleday Dell, reprint. “el metaverso” puede incluir realidad virtual, caracterizada por mundos virtuales persistentes que continúan existiendo incluso cuando no estás jugando, así como realidad aumentada que combina aspectos de los mundos digital y físico. Sin embargo, no requiere que se acceda exclusivamente a esos espacios a través de VR o AR. Los mundos virtuales, como los aspectos de Fortnite a los que se puede acceder a través de PC, consolas de juegos e incluso teléfonos, comenzaron a referirse a sí mismos como "el metaverso".
- 9. Mixed reality is a blend of physical and digital worlds, unlocking natural and intuitive 3D human, computer, and environmental interactions. This new reality is based on advancements in computer vision, graphical processing, display technologies, input systems, and cloud computing. https://learn.microsoft.co m/en- us/windows/mixed- reality/discover/mixed- reality https://dl.acm.org/doi/pdf/10.1145/32 90605.3300767 The merging of 3D graphics with the real world and spatial registration in the physical environment. es una combinación de mundos físicos y digitales, que desbloquea interacciones humanas, informáticas y ambientales en 3D naturales e intuitivas. Esta nueva realidad se basa en los avances en visión por computadora, procesamiento gráfico, tecnologías de visualización, sistemas de entrada y computación en la nube. Snow Crash (Stephe nson 1992) a science fiction novel by American author. Its themes include history, linguistics, anthropology, archaeology, religion, computer science, politics, cryptography, memetics, and philosophy. https://tinyurl.com/snow- crash https://en.wikipedia.org/ wiki/Snow_Crash https://ieeexplore.ieee.org/abstract/d ocument/9802015 Literature review on metaverse. una novela de ciencia ficción del autor estadounidense. Sus temas incluyen historia, lingüística, antropología, arqueología, religión, informática, política, criptografía, memética y filosofía. https://tinyurl.com/snow-crash Virtual reality 1. <application> Computer simulations that use 3D graphics and devices such as the data glove to allow the user to interact with the simulation. 2. <games> A form of network interaction incorporating aspects of role-playing games, interactive theater, improvisational comedy, and "true confessions" magazines. In a virtual reality forum (such as Usenet's news:alt.callahans newsgro up or the MUD experiments on Internet and elsewhere), interaction between the participants is written like a shared novel complete with scenery, "foreground characters" that may be personae utterly unlike the people who write them, and common "background characters" manipulable by all parties. https://www.computer- dictionary- online.org/definitions- v/virtual-reality.html https://www.sciencedirect.com/scien ce/article/pii/S1876139918302688#t bl1 “The use of computer technology to create an interactive three- dimensional world in which the objects have a sense of spatial presence; virtual environment, and virtual world are synonyms for virtual reality” (Department of Defense, 2018). “A computer-generated three- dimensional environment that gives an immersion effect” (p. 40) Department of Defense (2018). Lopreiato et al. (2016). (Also known as “computer-assisted simulation, computer-based 1. <aplicación> Simulaciones por computadora que usan gráficos 3D y dispositivos como el guante de datos para permitir que el usuario interactúe con la simulación. 2. <juegos> Una forma de interacción en red que incorpora aspectos de juegos de rol, teatro interactivo, comedia de improvisación y revistas de "confesiones verdaderas". En un foro de realidad virtual (como el grupo de noticias news:alt.calllahans de Usenet o los experimentos MUD en Internet y en otros lugares), la interacción entre los participantes se escribe como una novela compartida completa con escenarios, "personajes en primer plano" que pueden ser personajes completamente diferentes las personas que los escriben y "personajes de fondo" comunes manipulables por todas las partes. La única ley de hierro es que no puedes escribir cambios irreversibles en un personaje sin el consentimiento de la persona que lo "posee", de lo contrario, todo vale.
- 10. The one iron law is that you may not write irreversible changes to a character without the consent of the person who "owns" it, otherwise, anything goes. simulation). “A computer-generated reality, which allows a learner or group of learners to experience various auditory and visual stimuli. This reality can be experienced through the use of specialized ear and eyewear.” (p. 47).INACSL Standards Committee: INACSL standards of best practice: SimulationSM Glossary. (2016). “An artificial environment which is experienced through sensory stimuli (such as sights and sounds) provided by a computer and in which one's actions partially determine what happens in the environment; also: the technology used to create or access a virtual reality.” Merriam-Webster.com. “Virtual reality is best described as a collection of technologies that allow people to interact efficiently with 3D computerised databases in real time using their natural senses and skills … It is an immersive technology” (McCloy & Stone, 2001, 912). McCloy & Stone, 2001. “Computer-generated simulation of a three-dimensional environment the user is able to view and manipulate or interact with” (p. 315).
- 11. Identify that key features of the VR environment include (a) three- dimensional imaging, (b) the ability to actively interact with the virtual environment, and (c) visual and auditory feedback and further points out that it should prevent users from perceiving any elements of the real world by being completely immersed into the virtual environment. The best example is the flight simulators where the users are part of the simulated experience. (p.392). Kilmon, Brown, Ghosh, & Mikitiuk, 2010. Mantovani, Castelnuovo, Gaggioli, & Riva, 2003. “A collection of technologies that allow people to interact efficiently with 3D computerised databases in real time using their natural senses and skills” and is described by behaviorists as, “an advanced form of human–computer interface that allows the user to interact with and become immersed in a computer- generated environment in a naturalistic fashion” (p.230). Riva, 2002. “A real or simulated environment in which a perceiver experiences telepresence” (p.75) Steuer 1992.
- 12. “A computer-generated display that allows or compels the user (or users) to have a sense of being present in an environment other than the one they are actually in and to interact with that environment” (p.25). Schroeder, 1996. Virtual worlds A virtual world is a computer-simulated representation of a world with specific spatial and physical characteristics, and users of virtual worlds interact with each other via representations of themselves called “avatars.” Modern virtual worlds differ from traditional video games in their objective. https://cs.stanford.edu/p eople/eroberts/cs201/pr ojects/2007-08/virtual- worlds/history.html#:~:te xt=in%20Virtual%20Wor lds- ,Virtual%20Worlds,video %20games%20in%20th eir%20objective. https://link.springer.com/article/10.10 07/s11423-018-9577-y Duncan et al. (2012) provide a taxonomy of virtual world usage in education. This is based on an over- extended use of the term virtual world to “encompass any online environment that allows users to play, learn or interact” (p. 950) and issues emerge with the distinctions initially drawn between MUVEs, virtual worlds and virtual learning environments (VLEs). And A synchronous, persistent network of people, represented as avatars, facilitated by networked computers (Bell 2008, p. 2) And persistent virtual environments in which people experience others as being there with them - and where they can interact with them (Schroeder 2008, p. 2) And Un mundo virtual es una representación simulada por computadora de un mundo con características espaciales y físicas específicas, y los usuarios de los mundos virtuales interactúan entre sí a través de representaciones de sí mismos llamadas "avatares". Los mundos virtuales modernos difieren de los videojuegos tradicionales en su objetivo.
- 13. Shared, simulated spaces which are inhabited and shaped by their inhabitants who are represented as avatars. These avatars mediate our experience of this space as we move, interact with objects and interact with others, with whom we construct a shared understanding of the world at that time. (Girvan 2018)