GhostID - A document watermarking technology
•
0 likes•208 views
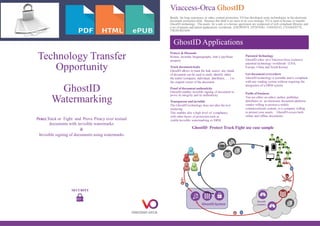
GhostID is an invisible watermarking technology that can protect, track, and prove piracy of textual documents. It embeds invisible watermarks to sign and authenticate documents, track leaks to identify traitors or original owners, and is portable to any reading system without extra DRM. Viaccess-Orca is offering the GhostID technology for license or transfer, including libraries and worldwide patents, to help editors, authors, and companies protect commercially distributed electronic documents and business assets.
Report
Share
Report
Share
Download to read offline
Recommended
Physical Security and Digital Security

Physical security involves protecting assets and information from unauthorized physical access through methods like locking doors, securing documents, using biometrics like fingerprints, ID badges, key fobs, and RFID cards. Digital security focuses on preventing harmful data and malware through antivirus software, firewalls, antispyware, and enforcing strong passwords and directory permissions. Both physical and digital security are important parts of an organization's complete security solution.
Ict encryption agt_fabio_pietrosanti

The document discusses PrivateWave's mobile voice encryption solutions. It describes PrivateGSM software that provides encryption for phone calls on smartphones using VoIP over mobile data. PrivateGSM uses the ZRTP standard to provide end-to-end encryption with human authentication and key agreement. It can also use SRTP and provide end-to-site encryption when integrated with telephony infrastructure. The document emphasizes that PrivateWave's solutions use open standards like ZRTP and SRTP to ensure the technologies are politically neutral and not subject to backdoors.
FortressFone Overview 012915

FortressFone is a secure smartphone system engineered for military-grade security. It features encrypted calls, texts, and cloud access. The system hardens the entire device to prevent hacking or data extraction from a stolen phone. It uses a secret-level approved secure SD card and "double pipe" encryption to securely establish communications channels. The system provides customers full control over their secure server and key management through proprietary technology.
Intro Micro Hardware

This document is an introduction to microcomputer hardware. It contains an overview, basic information, and details about the GNU Free Documentation License. The main topic is an introduction to microcomputer hardware, defining what it is, and providing foundational knowledge on the subject.
Physical Security and Digital Security

Physical security : as the name implies, involves protecting your assets and information from physical access by unauthorized personnel.
Physical Security

Physical security : as the name implies, involves protecting your assets and information from physical access by unauthorized personnel.
Securityand encryption

Encryption is used to hide information from unauthorized parties by translating plaintext files into ciphertext using secret codes. Cryptography involves mathematically scrambling data using keys so that only those with the necessary key can access the information. Technological advances both increased risks by making data more accessible but also reduced risks through strong encryption techniques.
Steganography

Very usefull and made with hard work . Slides are for any Level of students for doing presetation for 3-5 minutes.Proper theme is also used
Recommended
Physical Security and Digital Security

Physical security involves protecting assets and information from unauthorized physical access through methods like locking doors, securing documents, using biometrics like fingerprints, ID badges, key fobs, and RFID cards. Digital security focuses on preventing harmful data and malware through antivirus software, firewalls, antispyware, and enforcing strong passwords and directory permissions. Both physical and digital security are important parts of an organization's complete security solution.
Ict encryption agt_fabio_pietrosanti

The document discusses PrivateWave's mobile voice encryption solutions. It describes PrivateGSM software that provides encryption for phone calls on smartphones using VoIP over mobile data. PrivateGSM uses the ZRTP standard to provide end-to-end encryption with human authentication and key agreement. It can also use SRTP and provide end-to-site encryption when integrated with telephony infrastructure. The document emphasizes that PrivateWave's solutions use open standards like ZRTP and SRTP to ensure the technologies are politically neutral and not subject to backdoors.
FortressFone Overview 012915

FortressFone is a secure smartphone system engineered for military-grade security. It features encrypted calls, texts, and cloud access. The system hardens the entire device to prevent hacking or data extraction from a stolen phone. It uses a secret-level approved secure SD card and "double pipe" encryption to securely establish communications channels. The system provides customers full control over their secure server and key management through proprietary technology.
Intro Micro Hardware

This document is an introduction to microcomputer hardware. It contains an overview, basic information, and details about the GNU Free Documentation License. The main topic is an introduction to microcomputer hardware, defining what it is, and providing foundational knowledge on the subject.
Physical Security and Digital Security

Physical security : as the name implies, involves protecting your assets and information from physical access by unauthorized personnel.
Physical Security

Physical security : as the name implies, involves protecting your assets and information from physical access by unauthorized personnel.
Securityand encryption

Encryption is used to hide information from unauthorized parties by translating plaintext files into ciphertext using secret codes. Cryptography involves mathematically scrambling data using keys so that only those with the necessary key can access the information. Technological advances both increased risks by making data more accessible but also reduced risks through strong encryption techniques.
Steganography

Very usefull and made with hard work . Slides are for any Level of students for doing presetation for 3-5 minutes.Proper theme is also used
Iron Key Introduction

The IronKey is described as the world's most secure flash drive. It is tamper evident and resistant, with hardware-based encryption and key management. The IronKey enforces security policies through remote management and protects against malware with active defenses. It uses AES 256 CBC mode encryption for all classifications of data and its design allows no one to access stored information even if the device is lost or stolen.
Computer & Data Security

Here are some ways I would optimize the backup strategy:
- Only back up data directories instead of entire hard disks to reduce backup size and time.
- Stagger backups throughout the night instead of all at once to avoid overloading the network.
- Store backups offsite as well as on the NAS for disaster recovery in case the onsite storage is damaged.
- Consider cloud backup services for additional offsite storage.
- Encrypt backups for security and confidentiality.
- Test restores periodically to validate backups are working properly.
- Consider versioning backups to allow restoration of previous file versions.
- Automate verification of backups to catch any failures or corrupt backups.
- Review
Rune - Empowering User-based Security

The document discusses Rune's Vema-Cipher Platform as a solution for data encryption. It highlights weaknesses in current encryption standards and introduces Rune's approach combining Vernam cipher for unconditional security with standards-based encryption. The platform includes the Deadbolt application for encryption and Locksmith system for key and Vernam cipher pad management. It argues Rune provides a simple yet secure solution for encrypting sensitive data.
PrivateGSM - Voice Encryption Technical Overview

>PrivateGSM Security Overview
>PrivateGSM Voice Encryption Standards:
- Signaling Encryption
- Media Encryption
- End-to-End key exchange
- End-to-Site key exchange
RFID Security Module

This document provides an overview of RFID security modules and discusses various RFID tag and reader technologies. It summarizes key RFID standards like ISO/IEC 14443 and describes common tag types, including HID Prox, MIFARE Ultralight, MIFARE Classic, and DESFire EV1. It also discusses relay attacks and ways they can be mitigated using distance bounding protocols.
Encryption

This document provides an overview of encryption, including its history, types, methods, and uses. Encryption is the process of converting plain text into ciphertext using an algorithm and key. Historically, ancient Babylonian merchants used carved stones for encryption. There are several types of encryption, including manual, transparent, symmetric, and asymmetric encryption. Encryption methods are categorized as stream or block cipher encryption. Encryption is used to protect information on computers, in transit such as for wireless phones, and to facilitate confidential transactions and digital signatures.
Csi Netsec 2006 Poor Mans Guide Merdinger

The document summarizes poor man's network espionage devices and tactics that could be used by attackers. It describes small, low-cost devices like the Linksys WRT54G router, Nokia 770 phone, and Gumstix and PicoTux mini-computers that run Linux and can be used to conduct network attacks. These network espionage devices are hard to detect forensically since they use ephemeral filesystems in RAM. The document also provides examples of how these devices could be concealed on a target's network and used to conduct wireless and Bluetooth attacks, establish covert communication channels, and passively sniff network traffic. Countermeasures discussed include knowing network devices and traffic, user education, security policies, and
Phone Hacking: A lucrative, but largely hidden history

This talk explains some of the things that have been going on in the mobile phone hacking world for a number of years. SIM unlocking and other types of hacking associated with it have been extremely lucrative for many embedded systems hackers, but the topic has never really been covered by the media, whilst things like "carding" have been because of its illegality. Some of the artificial protection mechanisms such as SIMlock have actually driven hacking research, with end users actively seeking to remove the locks and pay people to do it. This hacking community has steadily evolved and merged into the rooting and jailbreaking scene, where again ordinary end users are more than willing to stump up cash to break the mechanisms to free their device, whilst unwittingly driving mobile phone theft. The ultimate result is an arms race between the hacking community and the device security engineers. A race of engineering wit and skill, combined with some war-like strategy and tactics.
Holoptica Group Presentation

This document summarizes Holoptica's security solutions for document protection including holographic technologies, nano technologies, near field communication, DNA technology, and authentication/verification platforms. It provides an overview of key personnel and describes proprietary solutions like proDOCTM security paper, holoCOMPASSTM, holoQRTM, holographic laminates, microdots, DNA taggants, and holoNFCTM. Authentication technologies like VTN and holoTRUETM are also summarized. Partnerships with organizations like the World Customs Organization and Thinfilm ASA are also mentioned.
Watch guard solution

This document discusses next generation firewalls (NGFWs) and unified threat management (UTM) solutions. It defines NGFWs as deep packet inspection firewalls that perform application-level inspection, intrusion prevention, and use intelligence from outside the firewall. UTMs are defined as security appliances that integrate firewall, antivirus, intrusion detection, and other features. The document notes that while some see NGFWs as having more features than UTMs, in reality both provide similar security capabilities. It emphasizes choosing a solution based on deployability, usability, visibility, performance, and efficacy over specific product classifications.
Data hiding in audio signals ppt

The document discusses data hiding in audio signals using watermarking techniques. It provides an introduction to watermarking and its applications. It describes the basic watermarking system as similar to a communication system. It also discusses speech processing, wavelet analysis, hiding techniques, advantages and disadvantages of audio watermarking. The document presents results from watermarking an audio signal and inserting a speech signal. It concludes that audio watermarking can be used for information tracing, tamper detection and other purposes beyond covert communication.
OmniSpotlight 05-2014

The document is an editorial from OmniSpotlight, a publication of Omnisec AG. It discusses Omnisec's new OmniCrypt VPN Client, which allows government, military, and intelligence officials to securely communicate over the internet while traveling. The client uses encryption to set up a virtual private network from a small hardware security module to the user's headquarters. This allows officials to securely access emails, files and video conferences from anywhere in the world. The editorial also provides updates on recent cyber threats such as invisible malware, credit card stealing malware, and vulnerabilities in network devices. It promotes Omnisec's security solutions and training services to help government organizations mitigate cyber threats.
Presentation Deck Dec.pdf

CoDe RTD was created to fight digital piracy and protect multimedia content. It offers three main products - Private Room for legalizing online evidence of piracy, Black Room for secure content sharing on the blockchain, and ISMA to prevent unauthorized content uploads. The presentation highlights the large economic costs of piracy, describes each product's features and technology, and positions the company to cover the entire content production and distribution chain. It also introduces the founding team and provides company contact details.
1.3-IoT Security Technologies (1).pdf

This document discusses Internet of Things (IoT) security technologies. It describes how IoT security involves protecting devices, communication pipes, platforms and applications. It outlines Huawei's "3T+1M" IoT security framework which leverages technologies, scenarios and management to provide comprehensive protection. Examples of typical IoT security cases and how Huawei addresses threats at each layer of the IoT architecture are also presented.
A Havoc Proof for Secure and Robust Audio Watermarking

The audio watermarking involves the concealment of data within a discrete audio file. Audio watermarking technology affords an opportunity to generate copies of a recording which are perceived by listeners as identical to the original but which may differ from one another on the basis of the embedded information. A highly confidential audio watermarking scheme using multiple scrambling is presented Superior to other audio watermarking techniques, the proposed scheme is self-secured by integrating multiple scrambling operations into the embedding stage. To ensure that unauthorized detection without correct secret keys is nearly impossible, the watermark is encrypted by a coded-image; certain frames are randomly selected from the total frames of the audio signal for embedding and their order of coding is further randomized. Adaptive synchronization is improves the robustness against hazardous synchronization attacks, such as random samples cropping/inserting and pitch-invariant time stretching. The efficient watermarking schemes make it impossible to be detected and robust even though the watermarking algorithm is open to the public.
Innovation in the Anti-counterfeit Technology Solution Market

ÉGIDE - one of the most promising new technologies that I have come across in the fight against counterfeits, delivering to customers and brand owners the means to verify product authenticity through a smart phone app...
WHONIX OS

Whonix is a security-focused operating system designed to be used within a host operating system. It uses Tor and virtualization to isolate and route all internet traffic through the Tor network for anonymity online. Whonix consists of two virtual machines - a Whonix Gateway that routes traffic through Tor, and a Whonix Workstation for applications. This isolation architecture enhances privacy and security by preventing leaks of the user's real IP address or system information when browsing or using applications. Whonix provides anonymity, privacy, and anti-censorship benefits to users.
Digital physical security[present]![Digital physical security[present]](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
![Digital physical security[present]](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
Physical security involves protecting assets and information from unauthorized physical access. Methods include locking doors, securing documents, using biometrics like fingerprints, ID badges, key fobs, and privacy filters to restrict access. Digital security focuses on preventing malware through antivirus software, firewalls, and antispyware to filter network traffic while also using strong user authentication like long, complex passwords and directory permissions to regulate access to information. Both physical and digital security are important to protect organizations from unauthorized access.
WISekey IoT Technologies Presentation

The document discusses WISeKey's end-to-end security framework for IoT devices and data. It provides cryptographic root keys and digital certificates to protect IoT devices and their data through authentication, confidentiality and integrity. WISeKey's solutions include VaultIC tamper-resistant chips embedded in devices, as well as a Certificate Management System and security broker that manage the lifecycle of device certificates signed by WISeKey's Certificate Authority rooted to the Swiss-based OISTE root of trust. This framework is designed to securely connect IoT devices to networks and platforms.
What is DRM, Types of DRM

The rise of digital media and modern technologies has vastly raised the copyright-owning concerns of organisations and individuals. In just a few clicks of a mouse, many copyrighted images, videos and audio files get downloaded or shared without prior permission. Modern techniques and tools have made it easy to convert media into various digital forms for easy portability and sharing
COMPUTER SECURITY

This document discusses various aspects of computer security and information protection. It describes threats like malicious code, hacking, natural disasters, and theft. It then outlines security measures used to protect systems and information, including antivirus software, firewalls, backups, cryptography, and addressing human aspects of security. The overall purpose is to explain how computer security works to protect systems and data from various internal and external threats.
Using FIDO Authenticator for IoT Devices

The document discusses using FIDO authenticators for IoT devices. It presents eWBM's biometric external FIDO authenticator and its security features. Potential applications of FIDO authentication for IoT are then described, including for device authentication over LoRa networks, drone control, and public WiFi access. The use of a BLE FIDO authenticator for personalized smart speaker services is also proposed. The conclusion recommends slimming down the FIDO client for embedded systems and achieving at least Security Level 2 certification for IoT authenticators.
More Related Content
What's hot
Iron Key Introduction

The IronKey is described as the world's most secure flash drive. It is tamper evident and resistant, with hardware-based encryption and key management. The IronKey enforces security policies through remote management and protects against malware with active defenses. It uses AES 256 CBC mode encryption for all classifications of data and its design allows no one to access stored information even if the device is lost or stolen.
Computer & Data Security

Here are some ways I would optimize the backup strategy:
- Only back up data directories instead of entire hard disks to reduce backup size and time.
- Stagger backups throughout the night instead of all at once to avoid overloading the network.
- Store backups offsite as well as on the NAS for disaster recovery in case the onsite storage is damaged.
- Consider cloud backup services for additional offsite storage.
- Encrypt backups for security and confidentiality.
- Test restores periodically to validate backups are working properly.
- Consider versioning backups to allow restoration of previous file versions.
- Automate verification of backups to catch any failures or corrupt backups.
- Review
Rune - Empowering User-based Security

The document discusses Rune's Vema-Cipher Platform as a solution for data encryption. It highlights weaknesses in current encryption standards and introduces Rune's approach combining Vernam cipher for unconditional security with standards-based encryption. The platform includes the Deadbolt application for encryption and Locksmith system for key and Vernam cipher pad management. It argues Rune provides a simple yet secure solution for encrypting sensitive data.
PrivateGSM - Voice Encryption Technical Overview

>PrivateGSM Security Overview
>PrivateGSM Voice Encryption Standards:
- Signaling Encryption
- Media Encryption
- End-to-End key exchange
- End-to-Site key exchange
RFID Security Module

This document provides an overview of RFID security modules and discusses various RFID tag and reader technologies. It summarizes key RFID standards like ISO/IEC 14443 and describes common tag types, including HID Prox, MIFARE Ultralight, MIFARE Classic, and DESFire EV1. It also discusses relay attacks and ways they can be mitigated using distance bounding protocols.
Encryption

This document provides an overview of encryption, including its history, types, methods, and uses. Encryption is the process of converting plain text into ciphertext using an algorithm and key. Historically, ancient Babylonian merchants used carved stones for encryption. There are several types of encryption, including manual, transparent, symmetric, and asymmetric encryption. Encryption methods are categorized as stream or block cipher encryption. Encryption is used to protect information on computers, in transit such as for wireless phones, and to facilitate confidential transactions and digital signatures.
Csi Netsec 2006 Poor Mans Guide Merdinger

The document summarizes poor man's network espionage devices and tactics that could be used by attackers. It describes small, low-cost devices like the Linksys WRT54G router, Nokia 770 phone, and Gumstix and PicoTux mini-computers that run Linux and can be used to conduct network attacks. These network espionage devices are hard to detect forensically since they use ephemeral filesystems in RAM. The document also provides examples of how these devices could be concealed on a target's network and used to conduct wireless and Bluetooth attacks, establish covert communication channels, and passively sniff network traffic. Countermeasures discussed include knowing network devices and traffic, user education, security policies, and
Phone Hacking: A lucrative, but largely hidden history

This talk explains some of the things that have been going on in the mobile phone hacking world for a number of years. SIM unlocking and other types of hacking associated with it have been extremely lucrative for many embedded systems hackers, but the topic has never really been covered by the media, whilst things like "carding" have been because of its illegality. Some of the artificial protection mechanisms such as SIMlock have actually driven hacking research, with end users actively seeking to remove the locks and pay people to do it. This hacking community has steadily evolved and merged into the rooting and jailbreaking scene, where again ordinary end users are more than willing to stump up cash to break the mechanisms to free their device, whilst unwittingly driving mobile phone theft. The ultimate result is an arms race between the hacking community and the device security engineers. A race of engineering wit and skill, combined with some war-like strategy and tactics.
What's hot (8)
Phone Hacking: A lucrative, but largely hidden history

Phone Hacking: A lucrative, but largely hidden history
Similar to GhostID - A document watermarking technology
Holoptica Group Presentation

This document summarizes Holoptica's security solutions for document protection including holographic technologies, nano technologies, near field communication, DNA technology, and authentication/verification platforms. It provides an overview of key personnel and describes proprietary solutions like proDOCTM security paper, holoCOMPASSTM, holoQRTM, holographic laminates, microdots, DNA taggants, and holoNFCTM. Authentication technologies like VTN and holoTRUETM are also summarized. Partnerships with organizations like the World Customs Organization and Thinfilm ASA are also mentioned.
Watch guard solution

This document discusses next generation firewalls (NGFWs) and unified threat management (UTM) solutions. It defines NGFWs as deep packet inspection firewalls that perform application-level inspection, intrusion prevention, and use intelligence from outside the firewall. UTMs are defined as security appliances that integrate firewall, antivirus, intrusion detection, and other features. The document notes that while some see NGFWs as having more features than UTMs, in reality both provide similar security capabilities. It emphasizes choosing a solution based on deployability, usability, visibility, performance, and efficacy over specific product classifications.
Data hiding in audio signals ppt

The document discusses data hiding in audio signals using watermarking techniques. It provides an introduction to watermarking and its applications. It describes the basic watermarking system as similar to a communication system. It also discusses speech processing, wavelet analysis, hiding techniques, advantages and disadvantages of audio watermarking. The document presents results from watermarking an audio signal and inserting a speech signal. It concludes that audio watermarking can be used for information tracing, tamper detection and other purposes beyond covert communication.
OmniSpotlight 05-2014

The document is an editorial from OmniSpotlight, a publication of Omnisec AG. It discusses Omnisec's new OmniCrypt VPN Client, which allows government, military, and intelligence officials to securely communicate over the internet while traveling. The client uses encryption to set up a virtual private network from a small hardware security module to the user's headquarters. This allows officials to securely access emails, files and video conferences from anywhere in the world. The editorial also provides updates on recent cyber threats such as invisible malware, credit card stealing malware, and vulnerabilities in network devices. It promotes Omnisec's security solutions and training services to help government organizations mitigate cyber threats.
Presentation Deck Dec.pdf

CoDe RTD was created to fight digital piracy and protect multimedia content. It offers three main products - Private Room for legalizing online evidence of piracy, Black Room for secure content sharing on the blockchain, and ISMA to prevent unauthorized content uploads. The presentation highlights the large economic costs of piracy, describes each product's features and technology, and positions the company to cover the entire content production and distribution chain. It also introduces the founding team and provides company contact details.
1.3-IoT Security Technologies (1).pdf

This document discusses Internet of Things (IoT) security technologies. It describes how IoT security involves protecting devices, communication pipes, platforms and applications. It outlines Huawei's "3T+1M" IoT security framework which leverages technologies, scenarios and management to provide comprehensive protection. Examples of typical IoT security cases and how Huawei addresses threats at each layer of the IoT architecture are also presented.
A Havoc Proof for Secure and Robust Audio Watermarking

The audio watermarking involves the concealment of data within a discrete audio file. Audio watermarking technology affords an opportunity to generate copies of a recording which are perceived by listeners as identical to the original but which may differ from one another on the basis of the embedded information. A highly confidential audio watermarking scheme using multiple scrambling is presented Superior to other audio watermarking techniques, the proposed scheme is self-secured by integrating multiple scrambling operations into the embedding stage. To ensure that unauthorized detection without correct secret keys is nearly impossible, the watermark is encrypted by a coded-image; certain frames are randomly selected from the total frames of the audio signal for embedding and their order of coding is further randomized. Adaptive synchronization is improves the robustness against hazardous synchronization attacks, such as random samples cropping/inserting and pitch-invariant time stretching. The efficient watermarking schemes make it impossible to be detected and robust even though the watermarking algorithm is open to the public.
Innovation in the Anti-counterfeit Technology Solution Market

ÉGIDE - one of the most promising new technologies that I have come across in the fight against counterfeits, delivering to customers and brand owners the means to verify product authenticity through a smart phone app...
WHONIX OS

Whonix is a security-focused operating system designed to be used within a host operating system. It uses Tor and virtualization to isolate and route all internet traffic through the Tor network for anonymity online. Whonix consists of two virtual machines - a Whonix Gateway that routes traffic through Tor, and a Whonix Workstation for applications. This isolation architecture enhances privacy and security by preventing leaks of the user's real IP address or system information when browsing or using applications. Whonix provides anonymity, privacy, and anti-censorship benefits to users.
Digital physical security[present]![Digital physical security[present]](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
![Digital physical security[present]](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
Physical security involves protecting assets and information from unauthorized physical access. Methods include locking doors, securing documents, using biometrics like fingerprints, ID badges, key fobs, and privacy filters to restrict access. Digital security focuses on preventing malware through antivirus software, firewalls, and antispyware to filter network traffic while also using strong user authentication like long, complex passwords and directory permissions to regulate access to information. Both physical and digital security are important to protect organizations from unauthorized access.
WISekey IoT Technologies Presentation

The document discusses WISeKey's end-to-end security framework for IoT devices and data. It provides cryptographic root keys and digital certificates to protect IoT devices and their data through authentication, confidentiality and integrity. WISeKey's solutions include VaultIC tamper-resistant chips embedded in devices, as well as a Certificate Management System and security broker that manage the lifecycle of device certificates signed by WISeKey's Certificate Authority rooted to the Swiss-based OISTE root of trust. This framework is designed to securely connect IoT devices to networks and platforms.
What is DRM, Types of DRM

The rise of digital media and modern technologies has vastly raised the copyright-owning concerns of organisations and individuals. In just a few clicks of a mouse, many copyrighted images, videos and audio files get downloaded or shared without prior permission. Modern techniques and tools have made it easy to convert media into various digital forms for easy portability and sharing
COMPUTER SECURITY

This document discusses various aspects of computer security and information protection. It describes threats like malicious code, hacking, natural disasters, and theft. It then outlines security measures used to protect systems and information, including antivirus software, firewalls, backups, cryptography, and addressing human aspects of security. The overall purpose is to explain how computer security works to protect systems and data from various internal and external threats.
Using FIDO Authenticator for IoT Devices

The document discusses using FIDO authenticators for IoT devices. It presents eWBM's biometric external FIDO authenticator and its security features. Potential applications of FIDO authentication for IoT are then described, including for device authentication over LoRa networks, drone control, and public WiFi access. The use of a BLE FIDO authenticator for personalized smart speaker services is also proposed. The conclusion recommends slimming down the FIDO client for embedded systems and achieving at least Security Level 2 certification for IoT authenticators.
Staying Safe - Overview of FREE Encryption Tools

FREE tools that you can use to maintain your privacy online, and discuss which ones are best for your needs.
Security and privacy - what does it mean to you in your everyday life? It used to be hard to use the tools that safeguard your identity and your information online. You had to be a pretty technical person - the good news is that it has gotten easier to be secure in your online persona.
Rfid presentation

RFID technology allows for automatic identification of movable items using radio waves. BCDS is an Australian company that has implemented various RFID solutions including asset tracking, visitor tracking, animal tracking, healthcare solutions, and more. RFID systems consist of tags that can be attached to items and readers that can read tag data remotely without line of sight. RFID finds many uses including tracking animals, manufacturing/warehousing, defense applications, and document tracking. The presentation discusses these applications and how RFID is playing a role in smart technologies.
20150522_Woobe_Information Kit_Light

- Woobe is a new digital platform that uses biometric identification to allow for legally binding digital communications through dynamic fingerprint matching.
- It guarantees the identity of document authors, senders, receivers and ensures consent is given at every step. Documents are encrypted and only accessible to authorized individuals.
- Every transaction is authenticated and timestamped, providing a record for legal purposes if needed. Woobe aims to provide "virtual legality" and meets international standards for electronic signatures and data privacy by not storing personal data centrally.
Ce hv6 module 46 securing laptop computers

This module discusses securing laptop computers from physical and digital threats. It describes how laptops can be targeted for theft due to the sensitive data stored on them. Various security tools are presented to protect laptops such as locks, alarms, encryption software and tracking programs. Fingerprint and face recognition are biometric authentication methods covered. Best practices for organizations include using encryption, disabling unnecessary services and ports, securing physical access to laptops and installing tracking programs to recover stolen devices.
Access Control in Enterprises with Key2Share

Key2Share is a new solution for NFC-enabled Android smartphones that allows enterprise employees to access offices and other enterprise premises using digital access control tokens stored on their mobile phones. The Key2Share app utilizes Near Field Communication (NFC) technology, which enables the phone to emulate a contactless smartcard that can be used with standard contactless smartcard readers.
Converging CAS and DRM, David Bouteruche from Nagra

This document discusses the convergence of CAS (conditional access systems) and DRM (digital rights management) technologies. It notes that viewing habits are shifting to non-linear, multi-screen consumption. While CAS was designed for pay TV and DRM for PC/music, the lines are blurring as DRM takes on functions of CAS for OTT/live streaming. The document advocates an advanced and flexible DRM approach that can serve both traditional broadcast and multi-screen OTT delivery across multiple networks and devices.
Similar to GhostID - A document watermarking technology (20)
A Havoc Proof for Secure and Robust Audio Watermarking

A Havoc Proof for Secure and Robust Audio Watermarking
Innovation in the Anti-counterfeit Technology Solution Market

Innovation in the Anti-counterfeit Technology Solution Market
Converging CAS and DRM, David Bouteruche from Nagra

Converging CAS and DRM, David Bouteruche from Nagra
Recently uploaded
Unlock the Future of Search with MongoDB Atlas_ Vector Search Unleashed.pdf

Discover how MongoDB Atlas and vector search technology can revolutionize your application's search capabilities. This comprehensive presentation covers:
* What is Vector Search?
* Importance and benefits of vector search
* Practical use cases across various industries
* Step-by-step implementation guide
* Live demos with code snippets
* Enhancing LLM capabilities with vector search
* Best practices and optimization strategies
Perfect for developers, AI enthusiasts, and tech leaders. Learn how to leverage MongoDB Atlas to deliver highly relevant, context-aware search results, transforming your data retrieval process. Stay ahead in tech innovation and maximize the potential of your applications.
#MongoDB #VectorSearch #AI #SemanticSearch #TechInnovation #DataScience #LLM #MachineLearning #SearchTechnology
Columbus Data & Analytics Wednesdays - June 2024

Columbus Data & Analytics Wednesdays, June 2024 with Maria Copot 20
Programming Foundation Models with DSPy - Meetup Slides

Prompting language models is hard, while programming language models is easy. In this talk, I will discuss the state-of-the-art framework DSPy for programming foundation models with its powerful optimizers and runtime constraint system.
Artificial Intelligence for XMLDevelopment

In the rapidly evolving landscape of technologies, XML continues to play a vital role in structuring, storing, and transporting data across diverse systems. The recent advancements in artificial intelligence (AI) present new methodologies for enhancing XML development workflows, introducing efficiency, automation, and intelligent capabilities. This presentation will outline the scope and perspective of utilizing AI in XML development. The potential benefits and the possible pitfalls will be highlighted, providing a balanced view of the subject.
We will explore the capabilities of AI in understanding XML markup languages and autonomously creating structured XML content. Additionally, we will examine the capacity of AI to enrich plain text with appropriate XML markup. Practical examples and methodological guidelines will be provided to elucidate how AI can be effectively prompted to interpret and generate accurate XML markup.
Further emphasis will be placed on the role of AI in developing XSLT, or schemas such as XSD and Schematron. We will address the techniques and strategies adopted to create prompts for generating code, explaining code, or refactoring the code, and the results achieved.
The discussion will extend to how AI can be used to transform XML content. In particular, the focus will be on the use of AI XPath extension functions in XSLT, Schematron, Schematron Quick Fixes, or for XML content refactoring.
The presentation aims to deliver a comprehensive overview of AI usage in XML development, providing attendees with the necessary knowledge to make informed decisions. Whether you’re at the early stages of adopting AI or considering integrating it in advanced XML development, this presentation will cover all levels of expertise.
By highlighting the potential advantages and challenges of integrating AI with XML development tools and languages, the presentation seeks to inspire thoughtful conversation around the future of XML development. We’ll not only delve into the technical aspects of AI-powered XML development but also discuss practical implications and possible future directions.
Building Production Ready Search Pipelines with Spark and Milvus

Spark is the widely used ETL tool for processing, indexing and ingesting data to serving stack for search. Milvus is the production-ready open-source vector database. In this talk we will show how to use Spark to process unstructured data to extract vector representations, and push the vectors to Milvus vector database for search serving.
Webinar: Designing a schema for a Data Warehouse

Are you new to data warehouses (DWH)? Do you need to check whether your data warehouse follows the best practices for a good design? In both cases, this webinar is for you.
A data warehouse is a central relational database that contains all measurements about a business or an organisation. This data comes from a variety of heterogeneous data sources, which includes databases of any type that back the applications used by the company, data files exported by some applications, or APIs provided by internal or external services.
But designing a data warehouse correctly is a hard task, which requires gathering information about the business processes that need to be analysed in the first place. These processes must be translated into so-called star schemas, which means, denormalised databases where each table represents a dimension or facts.
We will discuss these topics:
- How to gather information about a business;
- Understanding dictionaries and how to identify business entities;
- Dimensions and facts;
- Setting a table granularity;
- Types of facts;
- Types of dimensions;
- Snowflakes and how to avoid them;
- Expanding existing dimensions and facts.
Your One-Stop Shop for Python Success: Top 10 US Python Development Providers

Simplify your search for a reliable Python development partner! This list presents the top 10 trusted US providers offering comprehensive Python development services, ensuring your project's success from conception to completion.
Choosing The Best AWS Service For Your Website + API.pptx

Have you ever been confused by the myriad of choices offered by AWS for hosting a website or an API?
Lambda, Elastic Beanstalk, Lightsail, Amplify, S3 (and more!) can each host websites + APIs. But which one should we choose?
Which one is cheapest? Which one is fastest? Which one will scale to meet our needs?
Join me in this session as we dive into each AWS hosting service to determine which one is best for your scenario and explain why!
Ocean lotus Threat actors project by John Sitima 2024 (1).pptx

Ocean Lotus cyber threat actors represent a sophisticated, persistent, and politically motivated group that poses a significant risk to organizations and individuals in the Southeast Asian region. Their continuous evolution and adaptability underscore the need for robust cybersecurity measures and international cooperation to identify and mitigate the threats posed by such advanced persistent threat groups.
Fueling AI with Great Data with Airbyte Webinar

This talk will focus on how to collect data from a variety of sources, leveraging this data for RAG and other GenAI use cases, and finally charting your course to productionalization.
Let's Integrate MuleSoft RPA, COMPOSER, APM with AWS IDP along with Slack

Discover the seamless integration of RPA (Robotic Process Automation), COMPOSER, and APM with AWS IDP enhanced with Slack notifications. Explore how these technologies converge to streamline workflows, optimize performance, and ensure secure access, all while leveraging the power of AWS IDP and real-time communication via Slack notifications.
5th LF Energy Power Grid Model Meet-up Slides

5th Power Grid Model Meet-up
It is with great pleasure that we extend to you an invitation to the 5th Power Grid Model Meet-up, scheduled for 6th June 2024. This event will adopt a hybrid format, allowing participants to join us either through an online Mircosoft Teams session or in person at TU/e located at Den Dolech 2, Eindhoven, Netherlands. The meet-up will be hosted by Eindhoven University of Technology (TU/e), a research university specializing in engineering science & technology.
Power Grid Model
The global energy transition is placing new and unprecedented demands on Distribution System Operators (DSOs). Alongside upgrades to grid capacity, processes such as digitization, capacity optimization, and congestion management are becoming vital for delivering reliable services.
Power Grid Model is an open source project from Linux Foundation Energy and provides a calculation engine that is increasingly essential for DSOs. It offers a standards-based foundation enabling real-time power systems analysis, simulations of electrical power grids, and sophisticated what-if analysis. In addition, it enables in-depth studies and analysis of the electrical power grid’s behavior and performance. This comprehensive model incorporates essential factors such as power generation capacity, electrical losses, voltage levels, power flows, and system stability.
Power Grid Model is currently being applied in a wide variety of use cases, including grid planning, expansion, reliability, and congestion studies. It can also help in analyzing the impact of renewable energy integration, assessing the effects of disturbances or faults, and developing strategies for grid control and optimization.
What to expect
For the upcoming meetup we are organizing, we have an exciting lineup of activities planned:
-Insightful presentations covering two practical applications of the Power Grid Model.
-An update on the latest advancements in Power Grid -Model technology during the first and second quarters of 2024.
-An interactive brainstorming session to discuss and propose new feature requests.
-An opportunity to connect with fellow Power Grid Model enthusiasts and users.
Generating privacy-protected synthetic data using Secludy and Milvus

During this demo, the founders of Secludy will demonstrate how their system utilizes Milvus to store and manipulate embeddings for generating privacy-protected synthetic data. Their approach not only maintains the confidentiality of the original data but also enhances the utility and scalability of LLMs under privacy constraints. Attendees, including machine learning engineers, data scientists, and data managers, will witness first-hand how Secludy's integration with Milvus empowers organizations to harness the power of LLMs securely and efficiently.
Introduction of Cybersecurity with OSS at Code Europe 2024

I develop the Ruby programming language, RubyGems, and Bundler, which are package managers for Ruby. Today, I will introduce how to enhance the security of your application using open-source software (OSS) examples from Ruby and RubyGems.
The first topic is CVE (Common Vulnerabilities and Exposures). I have published CVEs many times. But what exactly is a CVE? I'll provide a basic understanding of CVEs and explain how to detect and handle vulnerabilities in OSS.
Next, let's discuss package managers. Package managers play a critical role in the OSS ecosystem. I'll explain how to manage library dependencies in your application.
I'll share insights into how the Ruby and RubyGems core team works to keep our ecosystem safe. By the end of this talk, you'll have a better understanding of how to safeguard your code.
How to Interpret Trends in the Kalyan Rajdhani Mix Chart.pdf

A Mix Chart displays historical data of numbers in a graphical or tabular form. The Kalyan Rajdhani Mix Chart specifically shows the results of a sequence of numbers over different periods.
みなさんこんにちはこれ何文字まで入るの?40文字以下不可とか本当に意味わからないけどこれ限界文字数書いてないからマジでやばい文字数いけるんじゃないの?えこ...

ここ3000字までしか入らないけどタイトルの方がたくさん文字入ると思います。
TrustArc Webinar - 2024 Global Privacy Survey

How does your privacy program stack up against your peers? What challenges are privacy teams tackling and prioritizing in 2024?
In the fifth annual Global Privacy Benchmarks Survey, we asked over 1,800 global privacy professionals and business executives to share their perspectives on the current state of privacy inside and outside of their organizations. This year’s report focused on emerging areas of importance for privacy and compliance professionals, including considerations and implications of Artificial Intelligence (AI) technologies, building brand trust, and different approaches for achieving higher privacy competence scores.
See how organizational priorities and strategic approaches to data security and privacy are evolving around the globe.
This webinar will review:
- The top 10 privacy insights from the fifth annual Global Privacy Benchmarks Survey
- The top challenges for privacy leaders, practitioners, and organizations in 2024
- Key themes to consider in developing and maintaining your privacy program
HCL Notes and Domino License Cost Reduction in the World of DLAU

Webinar Recording: https://www.panagenda.com/webinars/hcl-notes-and-domino-license-cost-reduction-in-the-world-of-dlau/
The introduction of DLAU and the CCB & CCX licensing model caused quite a stir in the HCL community. As a Notes and Domino customer, you may have faced challenges with unexpected user counts and license costs. You probably have questions on how this new licensing approach works and how to benefit from it. Most importantly, you likely have budget constraints and want to save money where possible. Don’t worry, we can help with all of this!
We’ll show you how to fix common misconfigurations that cause higher-than-expected user counts, and how to identify accounts which you can deactivate to save money. There are also frequent patterns that can cause unnecessary cost, like using a person document instead of a mail-in for shared mailboxes. We’ll provide examples and solutions for those as well. And naturally we’ll explain the new licensing model.
Join HCL Ambassador Marc Thomas in this webinar with a special guest appearance from Franz Walder. It will give you the tools and know-how to stay on top of what is going on with Domino licensing. You will be able lower your cost through an optimized configuration and keep it low going forward.
These topics will be covered
- Reducing license cost by finding and fixing misconfigurations and superfluous accounts
- How do CCB and CCX licenses really work?
- Understanding the DLAU tool and how to best utilize it
- Tips for common problem areas, like team mailboxes, functional/test users, etc
- Practical examples and best practices to implement right away
Recently uploaded (20)
Unlock the Future of Search with MongoDB Atlas_ Vector Search Unleashed.pdf

Unlock the Future of Search with MongoDB Atlas_ Vector Search Unleashed.pdf
Programming Foundation Models with DSPy - Meetup Slides

Programming Foundation Models with DSPy - Meetup Slides
Building Production Ready Search Pipelines with Spark and Milvus

Building Production Ready Search Pipelines with Spark and Milvus
Your One-Stop Shop for Python Success: Top 10 US Python Development Providers

Your One-Stop Shop for Python Success: Top 10 US Python Development Providers
Choosing The Best AWS Service For Your Website + API.pptx

Choosing The Best AWS Service For Your Website + API.pptx
Ocean lotus Threat actors project by John Sitima 2024 (1).pptx

Ocean lotus Threat actors project by John Sitima 2024 (1).pptx
Let's Integrate MuleSoft RPA, COMPOSER, APM with AWS IDP along with Slack

Let's Integrate MuleSoft RPA, COMPOSER, APM with AWS IDP along with Slack
Generating privacy-protected synthetic data using Secludy and Milvus

Generating privacy-protected synthetic data using Secludy and Milvus
Introduction of Cybersecurity with OSS at Code Europe 2024

Introduction of Cybersecurity with OSS at Code Europe 2024
How to Interpret Trends in the Kalyan Rajdhani Mix Chart.pdf

How to Interpret Trends in the Kalyan Rajdhani Mix Chart.pdf
みなさんこんにちはこれ何文字まで入るの?40文字以下不可とか本当に意味わからないけどこれ限界文字数書いてないからマジでやばい文字数いけるんじゃないの?えこ...

みなさんこんにちはこれ何文字まで入るの?40文字以下不可とか本当に意味わからないけどこれ限界文字数書いてないからマジでやばい文字数いけるんじゃないの?えこ...
HCL Notes and Domino License Cost Reduction in the World of DLAU

HCL Notes and Domino License Cost Reduction in the World of DLAU
GhostID - A document watermarking technology
- 1. Technology Transfer Opportunity GhostID Watermarking Protect,Track or Fight and Prove Piracy over textual documents with invisible watermarks & Invisible signing of documents using watermarks SECURITY Viaccess-Orca GhostID Beside his long experience in video content protection, VO has developed some technologies in the electronic document protection field. Because this field is no more in its core strategy, VO is open to license or transfer GhostID technology. The assets for a sale or a license agreement are composed of web compliant libraries and a set of patents and patent applications worldwide (FR2993074, EP2870561, US9420143, CN104428778, TW201403369) Protect & Dissuade Robust, Invisible Steganography, Anti Copy/Paste property Patented Technology GhostID relies on a Viaccess-Orca exclusive patented technology worldwide (USA, Europe, China and South Korea)Track document leaks GhostID allows to track the leak source: any chunk of document can be used to easily identify either the traitor (company, individual, distributor, … ) or the original owner of the document Get document everywhere GhostID technology is portable and is compliant with any reading system without requiring the integration of a DRM system GhostID Protect Track Fight use case sample GhostID Applications Proof of document authenticity GhostID enables invisible signing of document to prove its integrity and its authenticity Transparent and invisible The GhostID technology does not alter the text rendering. This enables also a high level of compliancy with other layers of protection such as visible/invisible watermarking or DRM Fields of business You are either an editor, author, publisher, distributor or an electronic document platform vendor willing to protect a widely commercialized content, or a company willing to protect your assets… GhostID covers both online and offline documents 1 2 3 4 5 6
