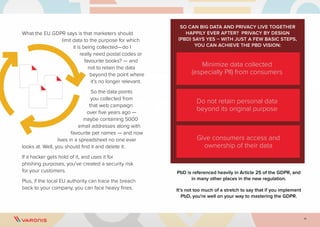
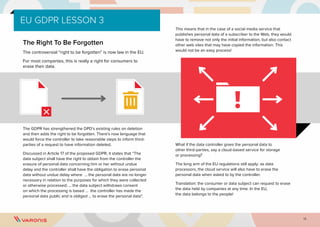
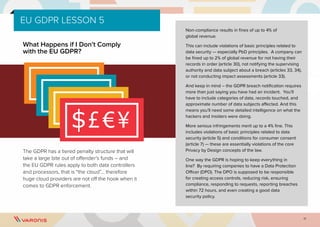
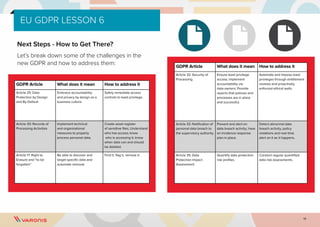
This practical guide outlines the key aspects of the EU General Data Protection Regulation (GDPR), emphasizing its importance for businesses, including compliance requirements, data protection by design, and the rights of individuals. The guide highlights significant principles like the right to be forgotten, breach notification obligations, and the regulation's extraterritorial application to non-EU companies handling data of EU citizens. Varonis offers software solutions to assist organizations in achieving GDPR compliance and recommends steps to mitigate risks associated with personal data processing.