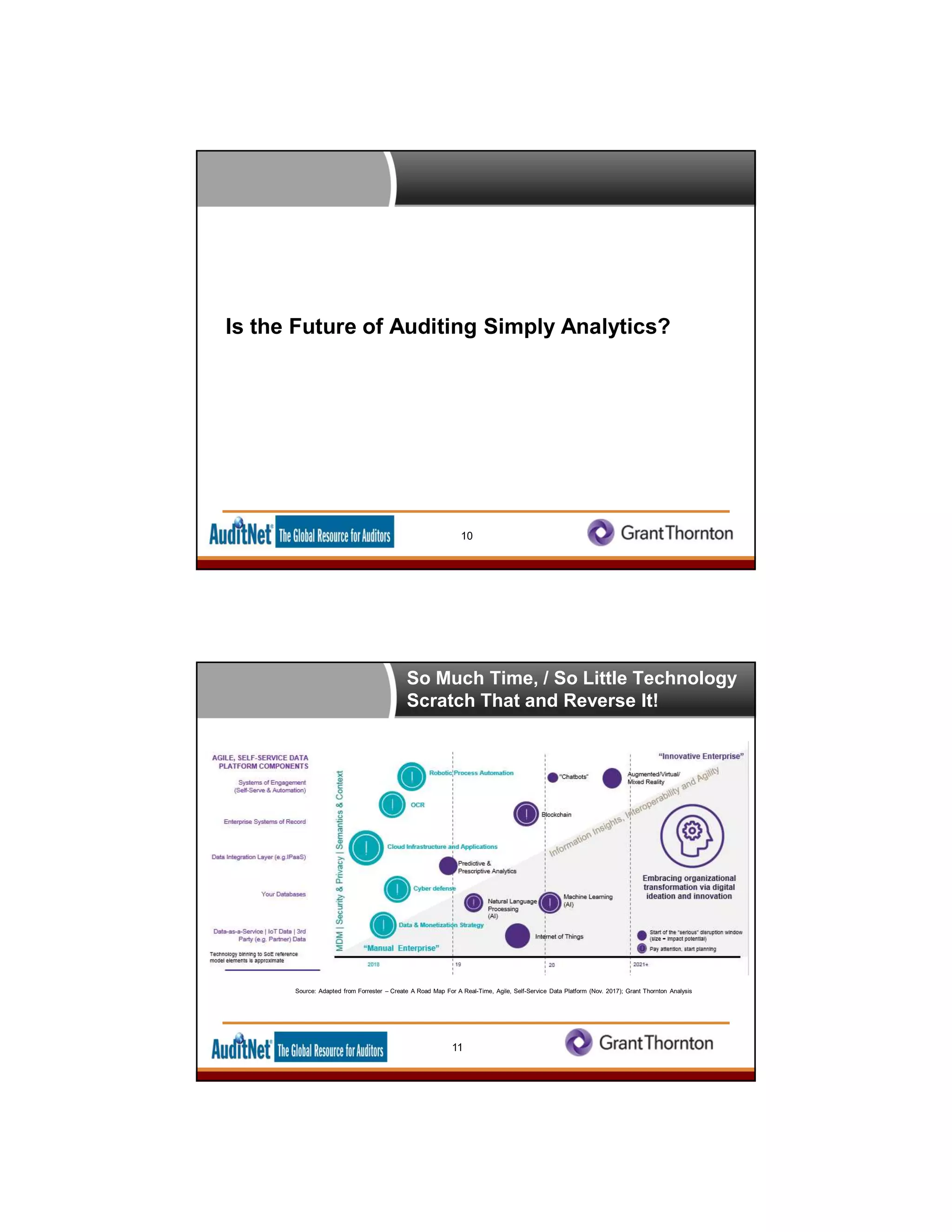
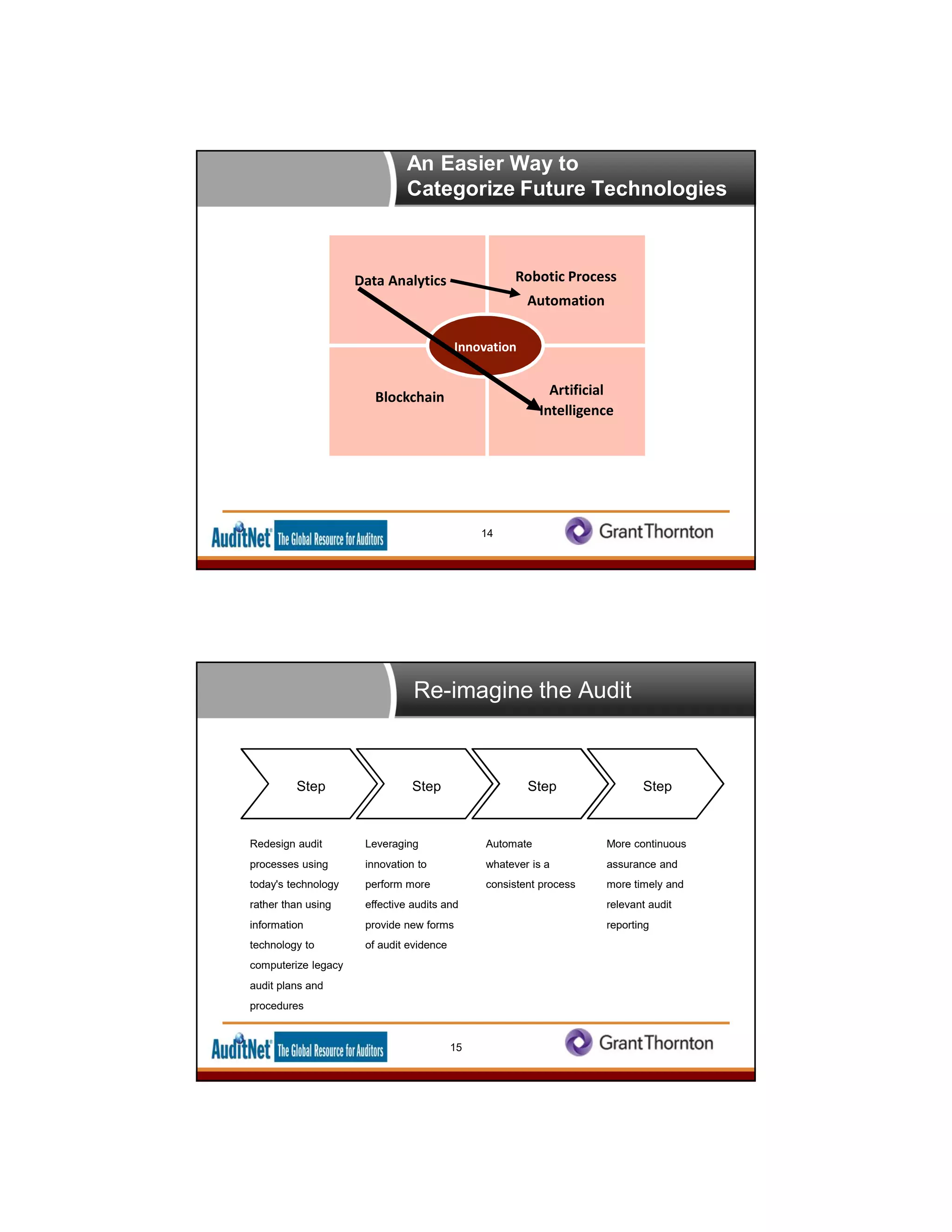
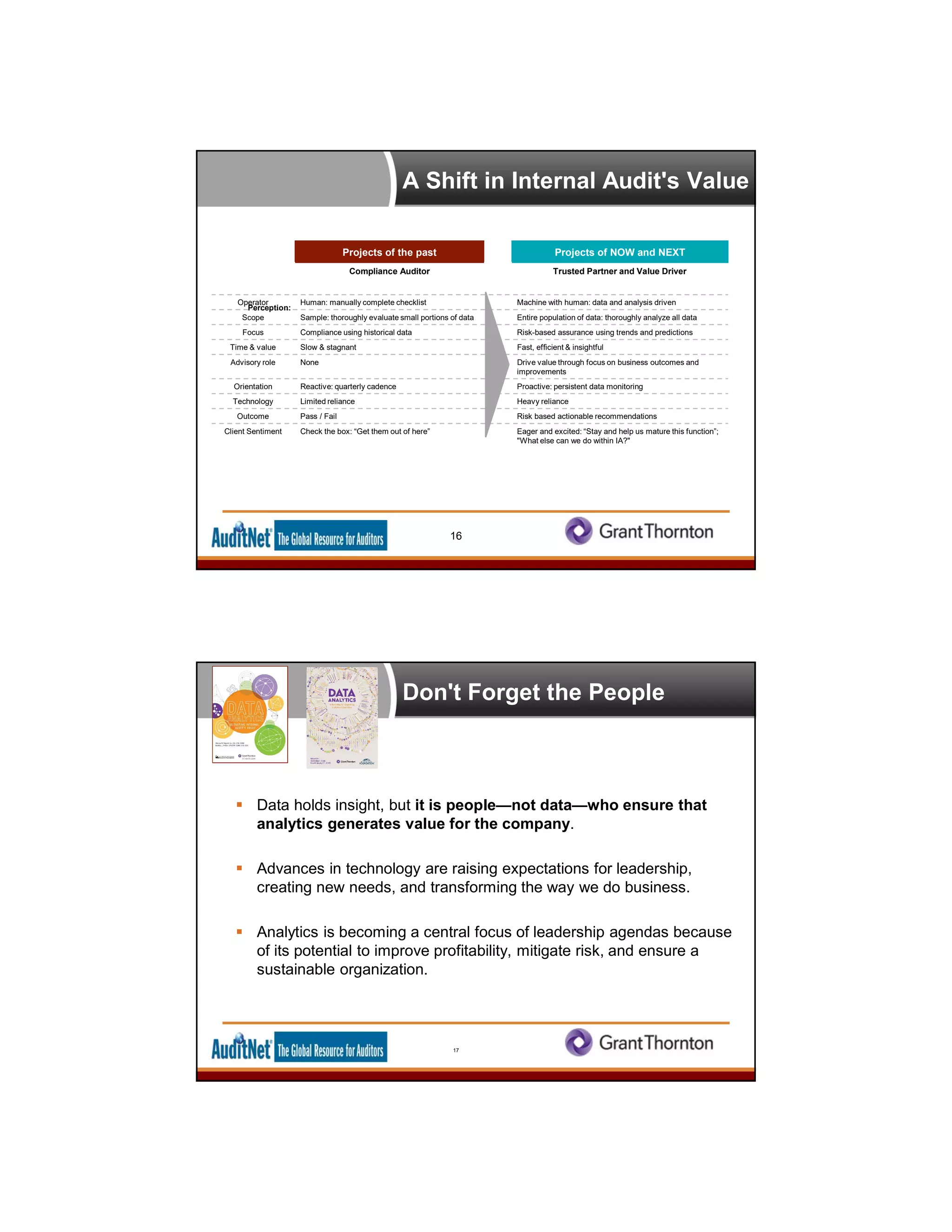
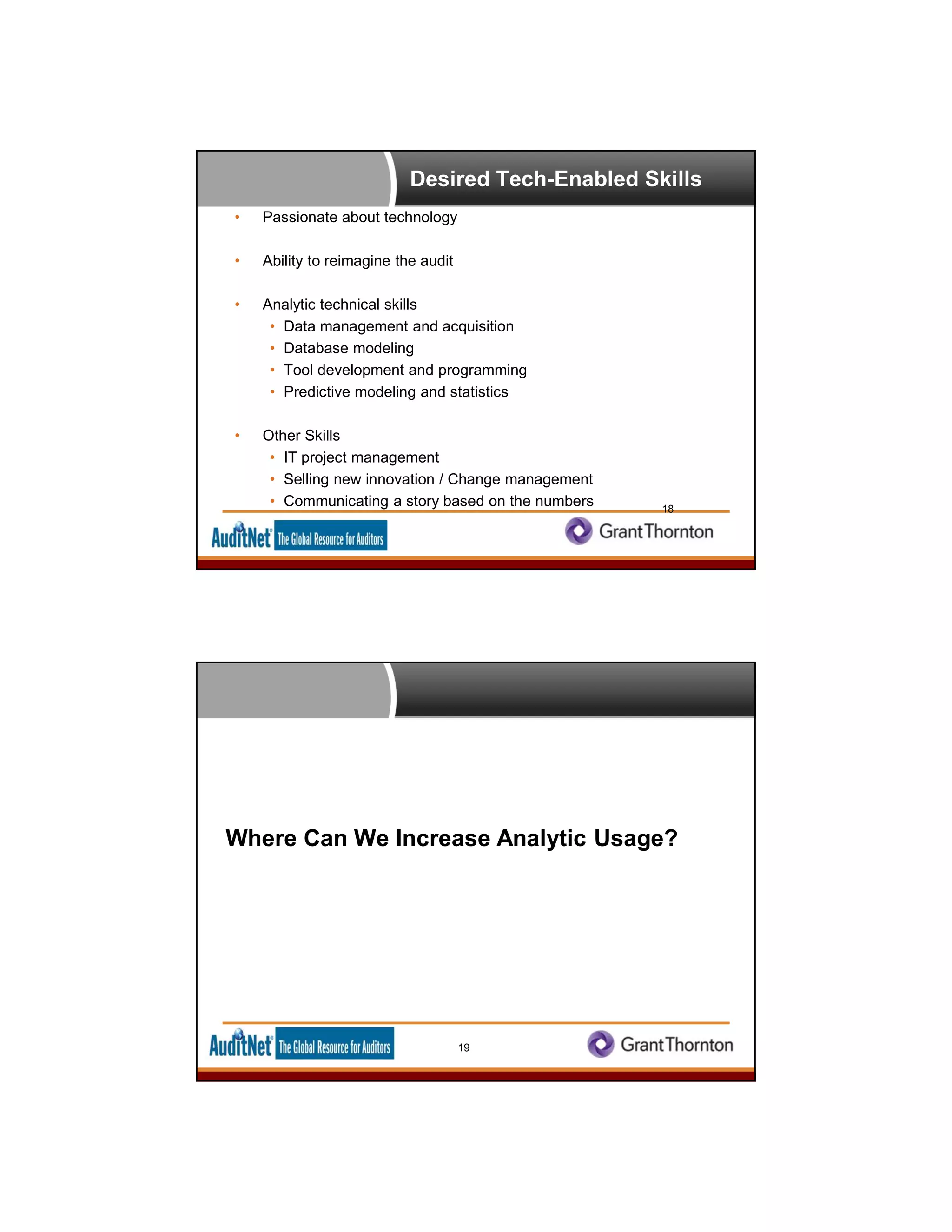
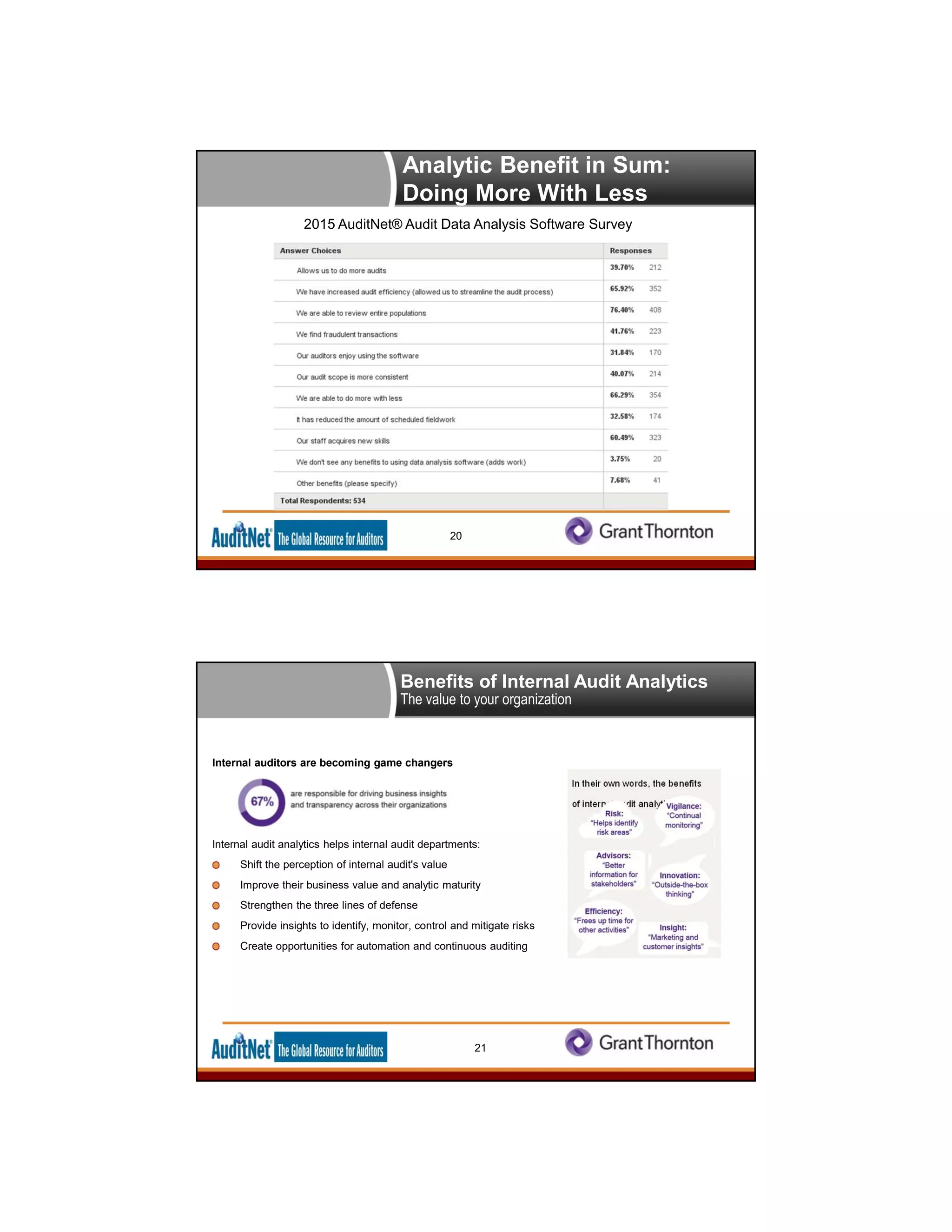
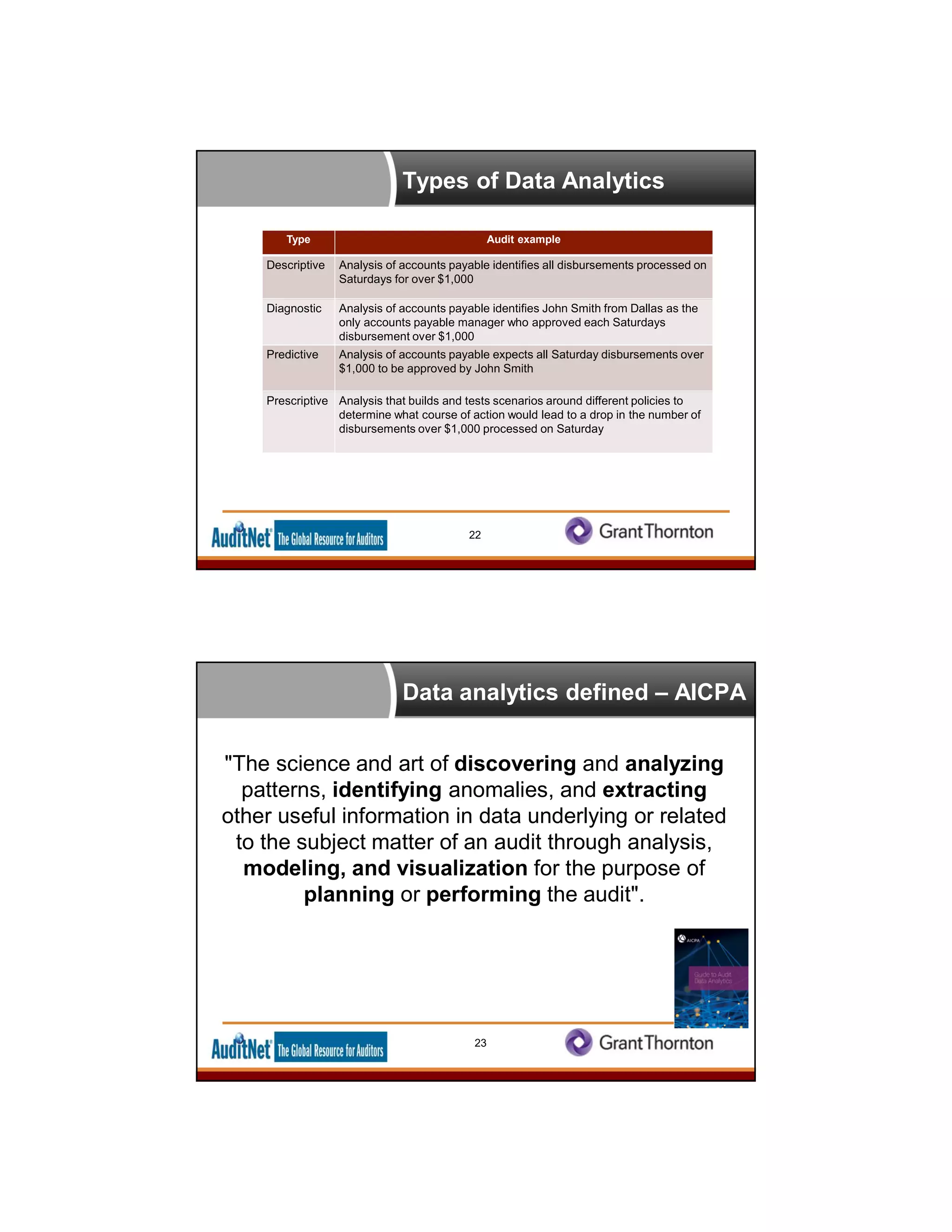
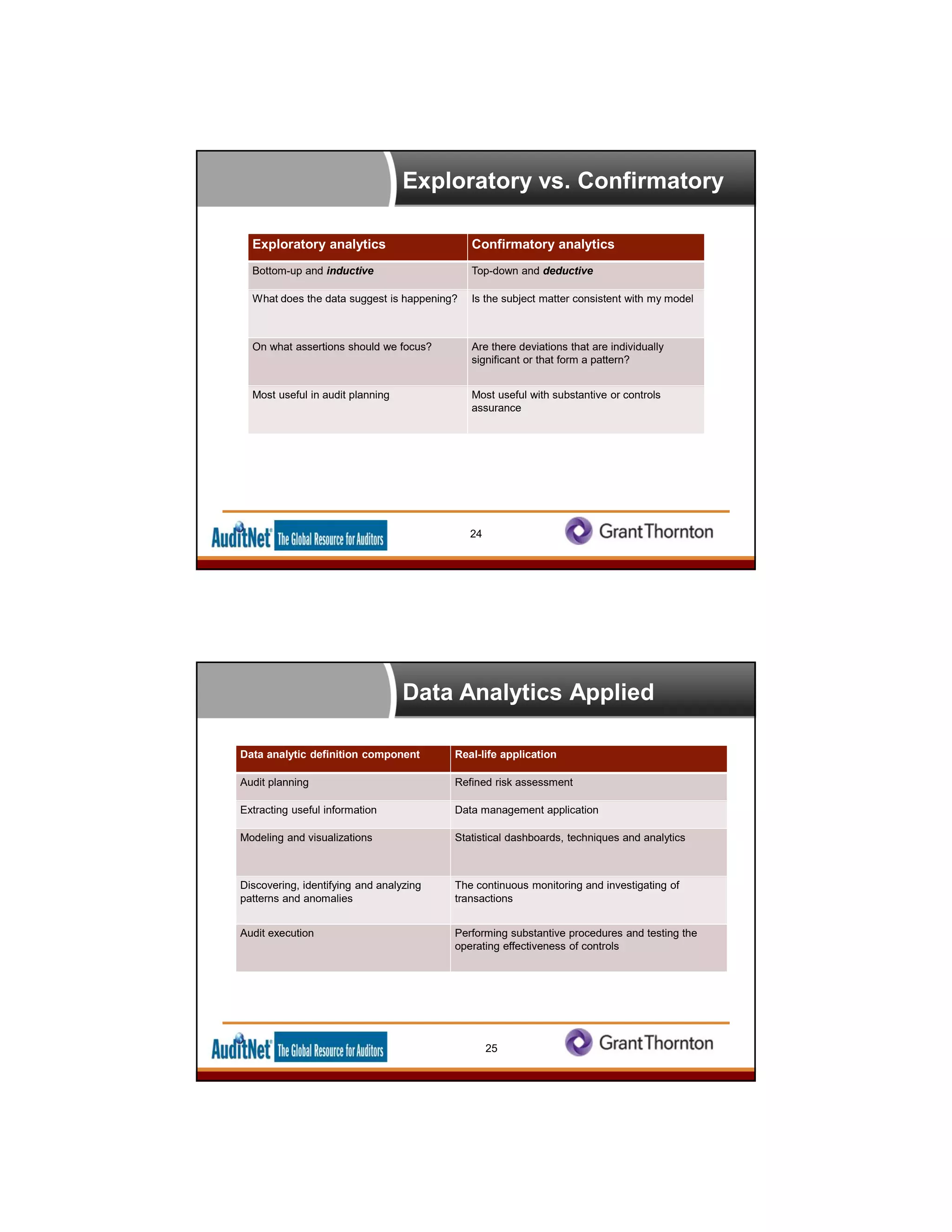
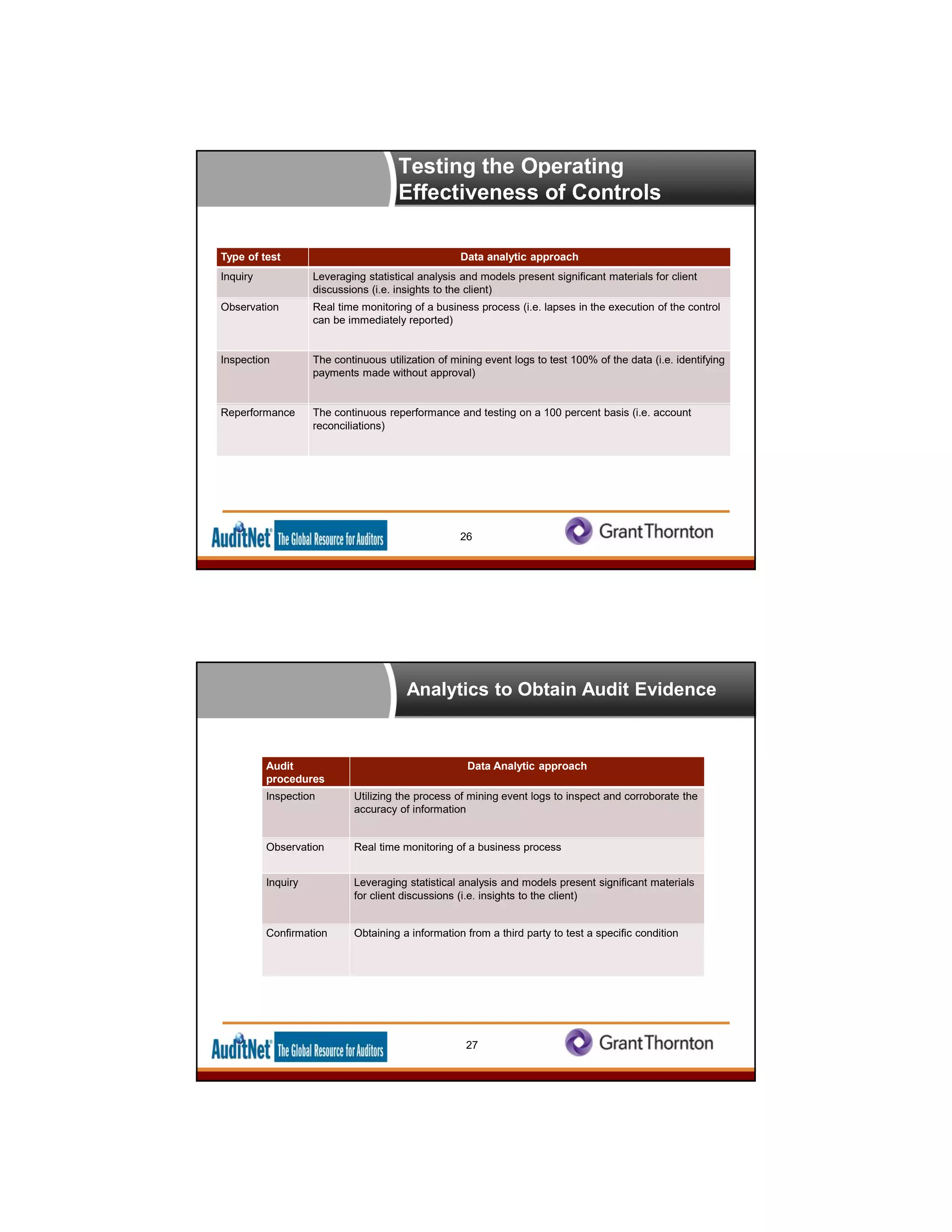
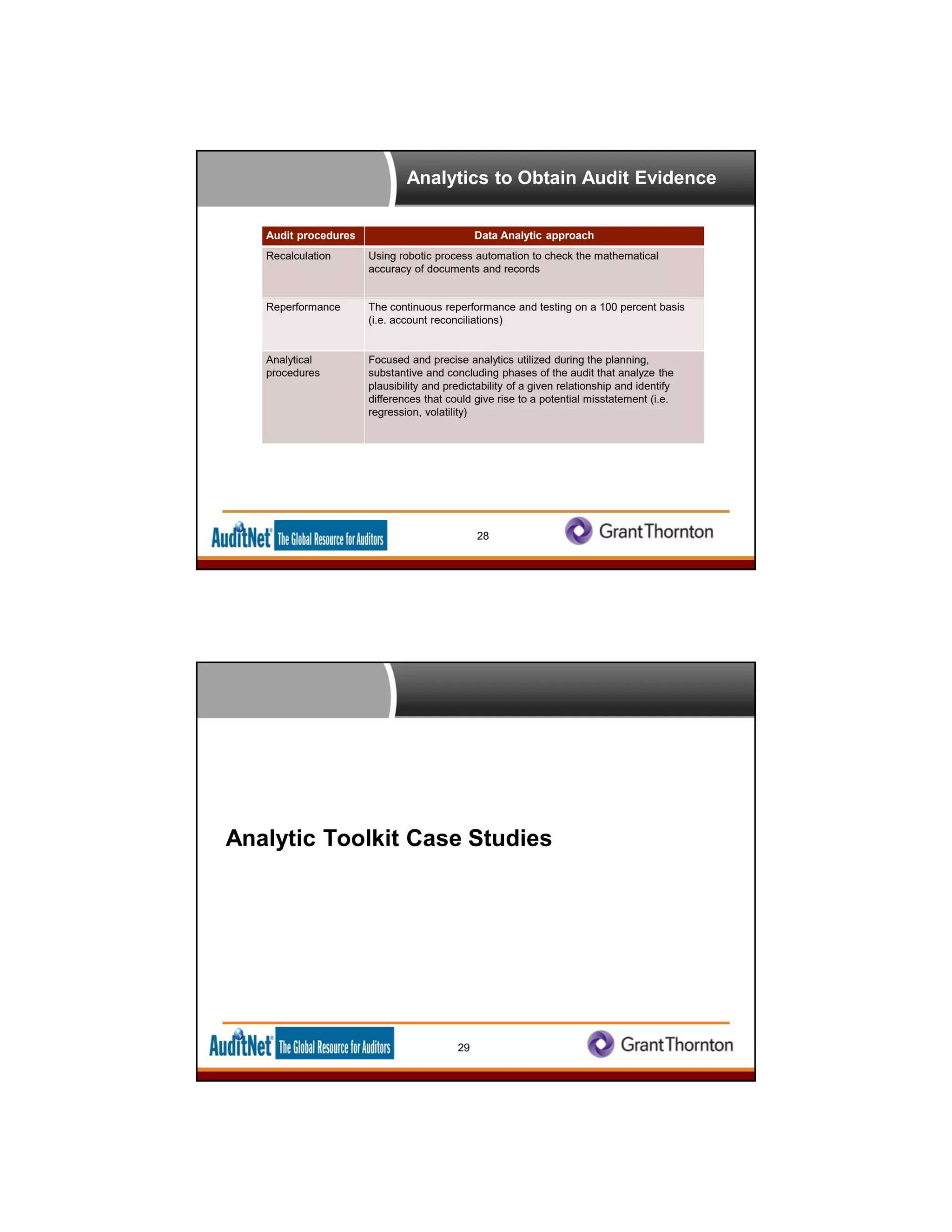
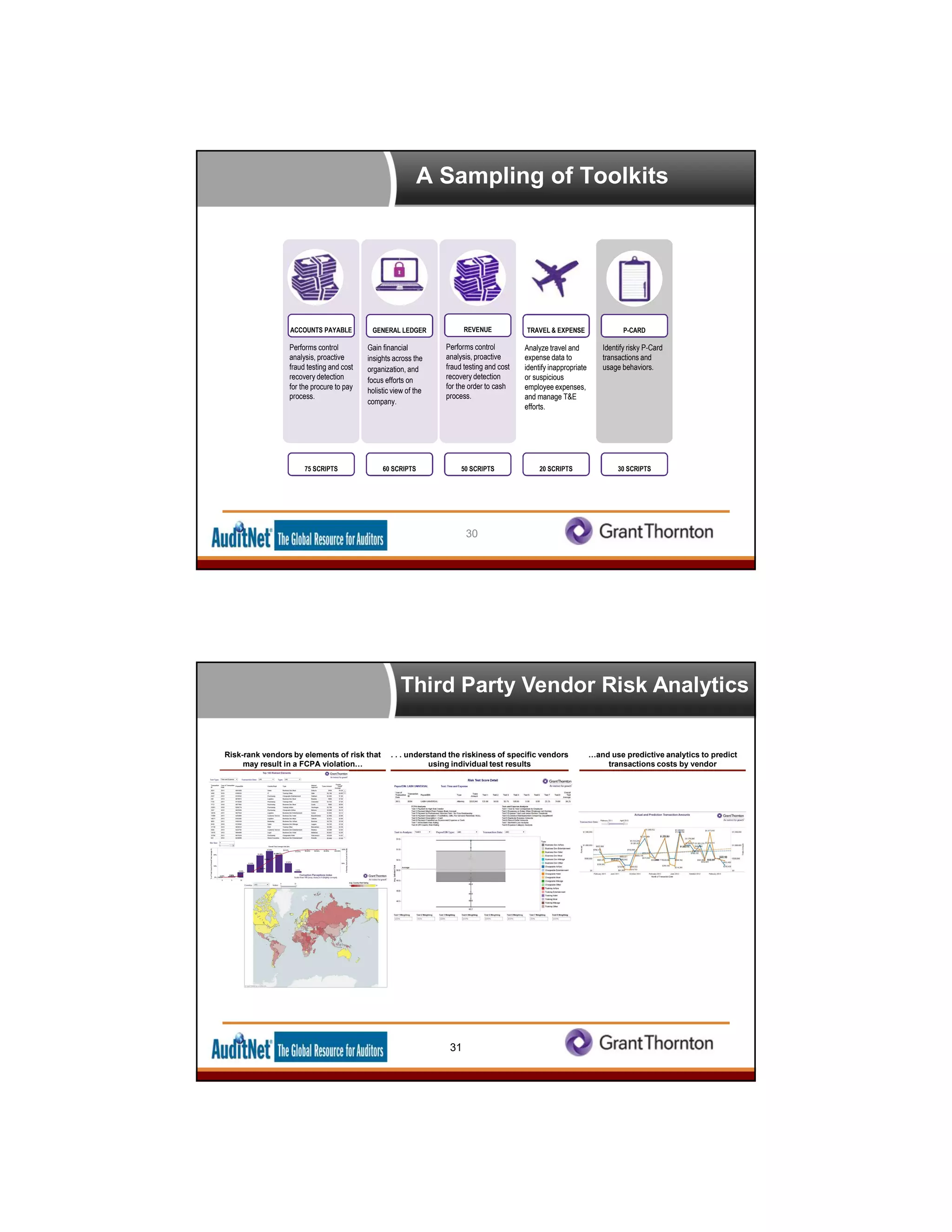
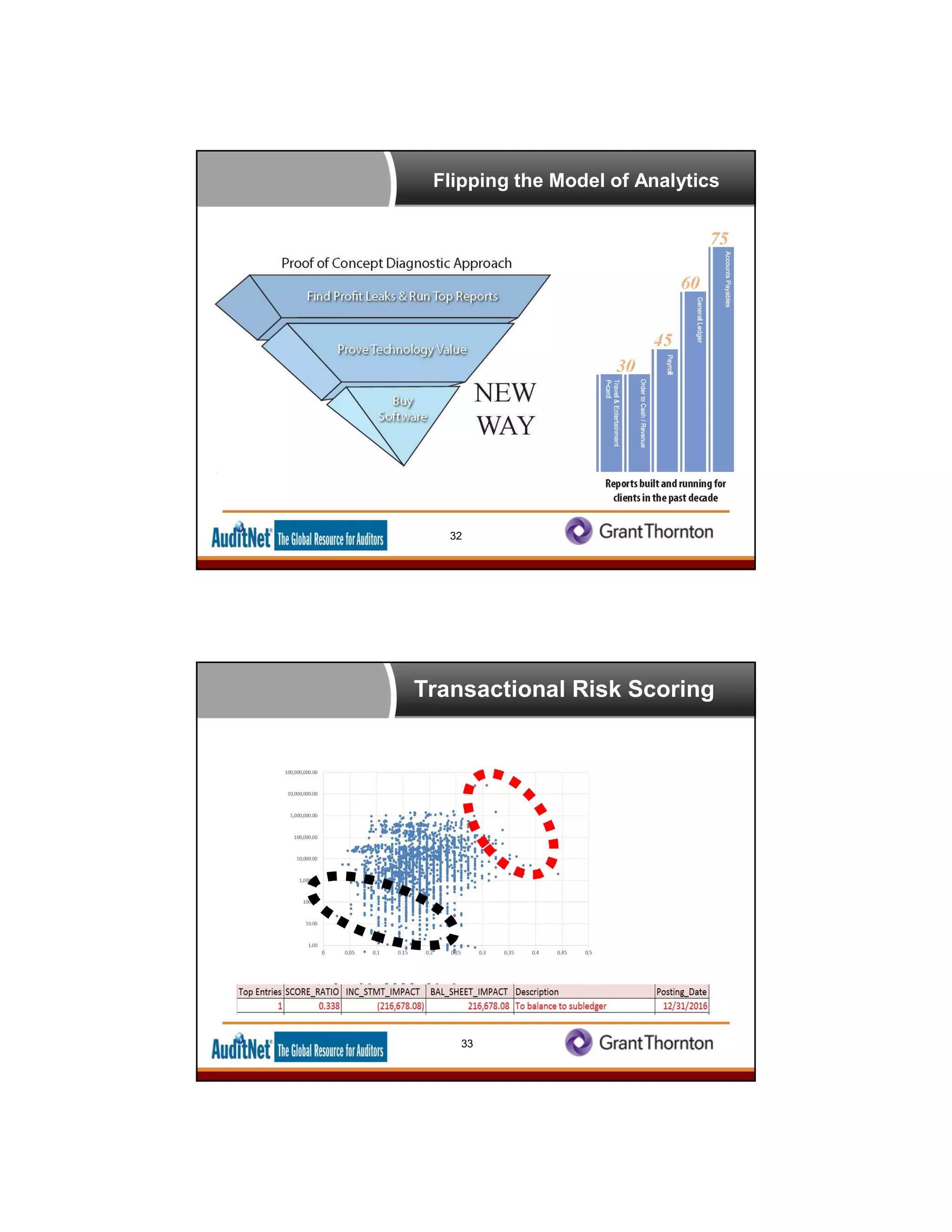
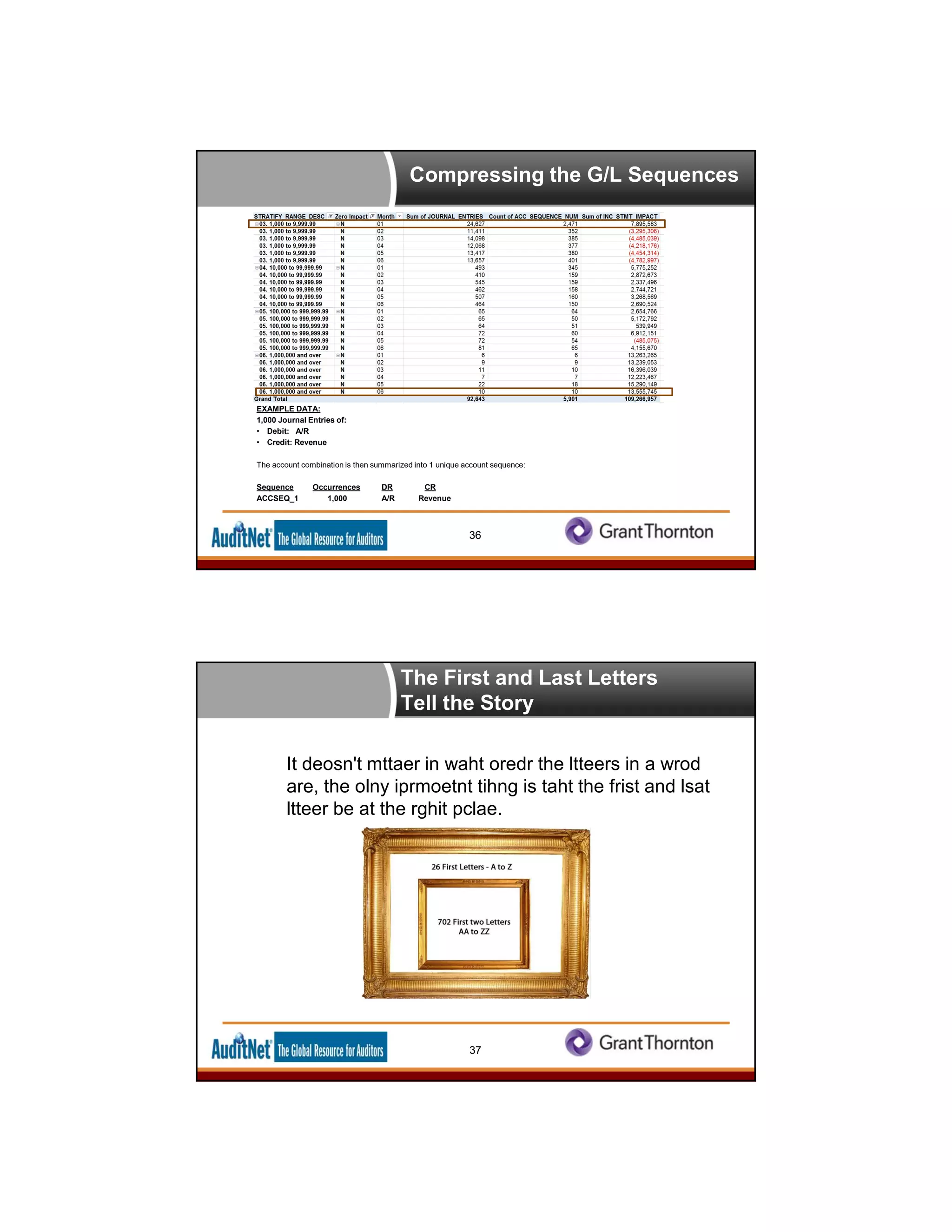
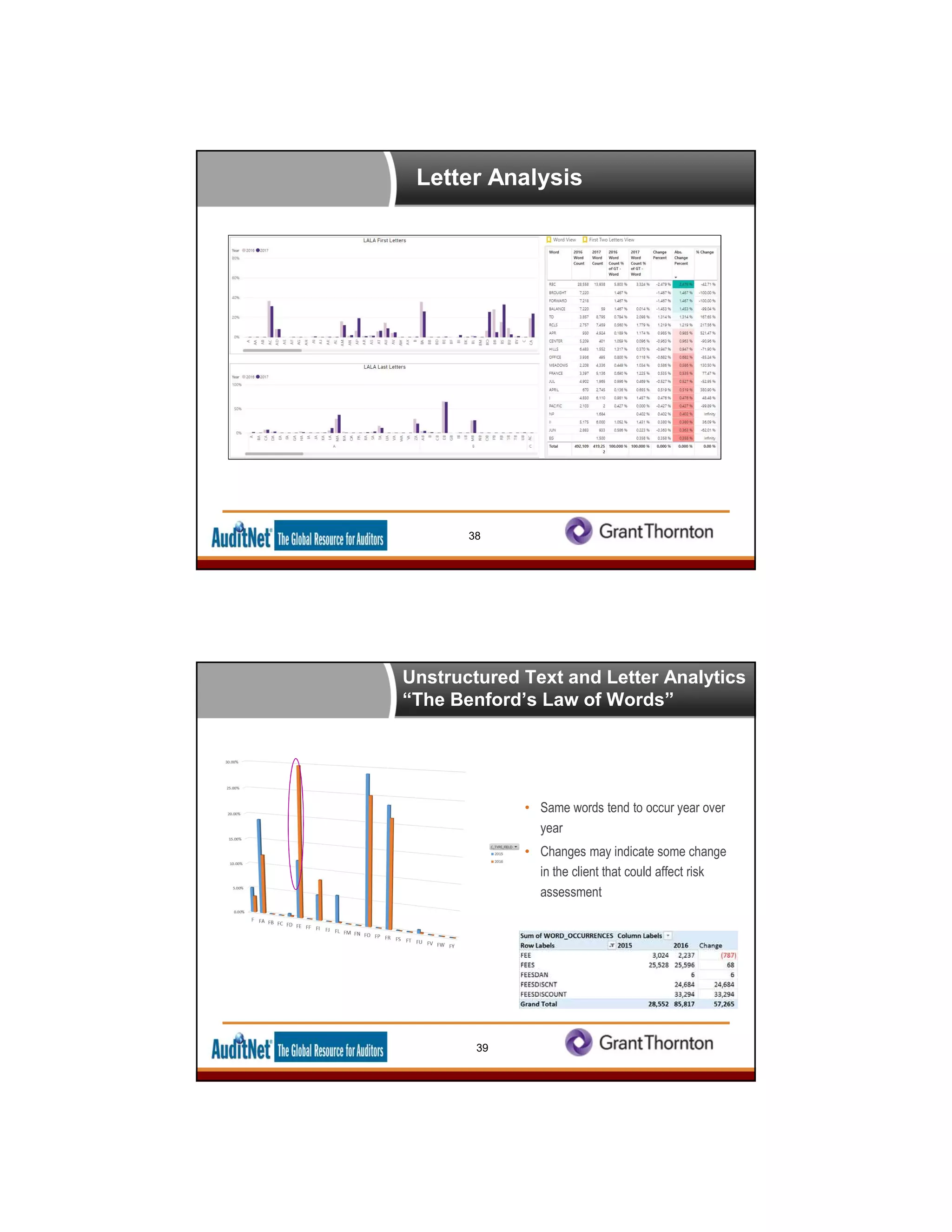
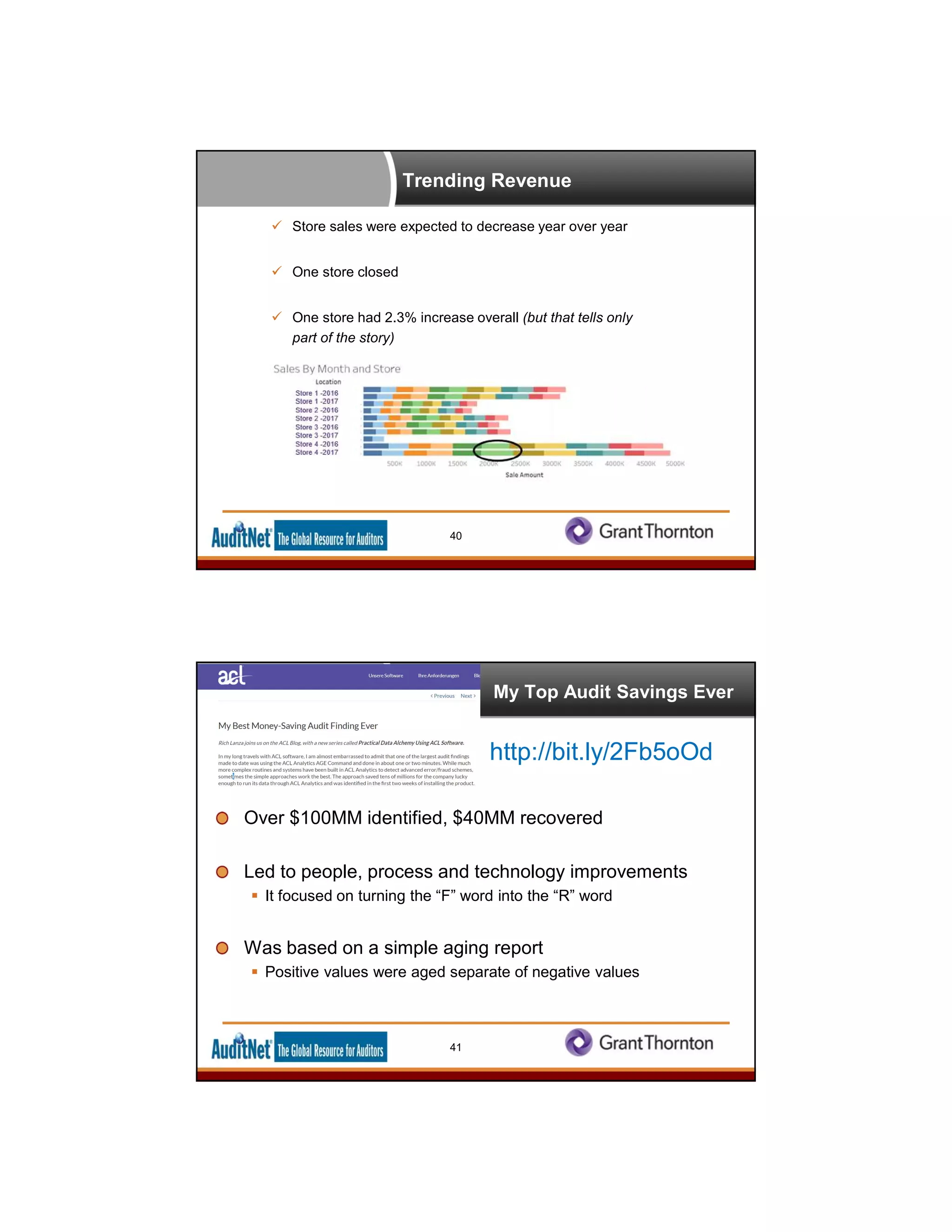
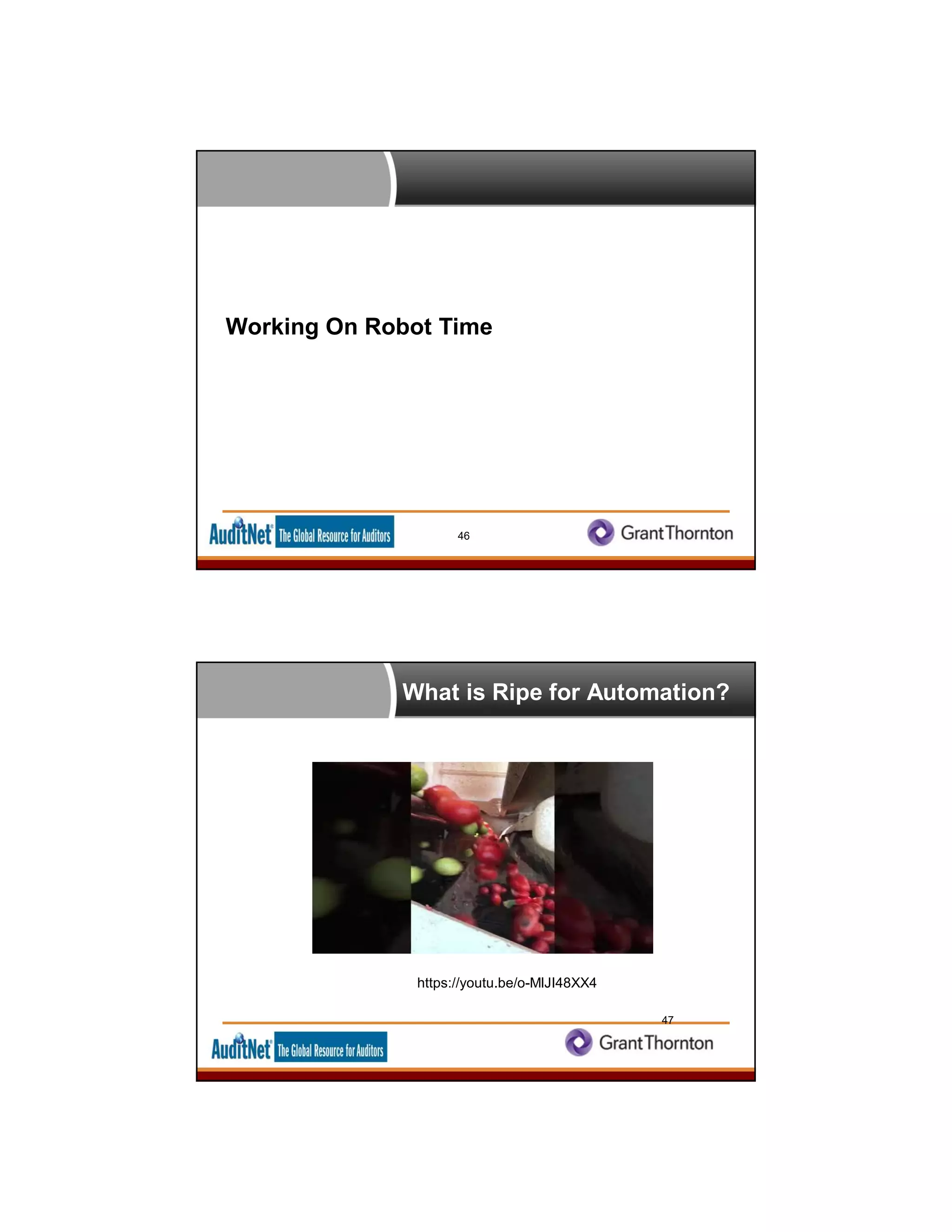
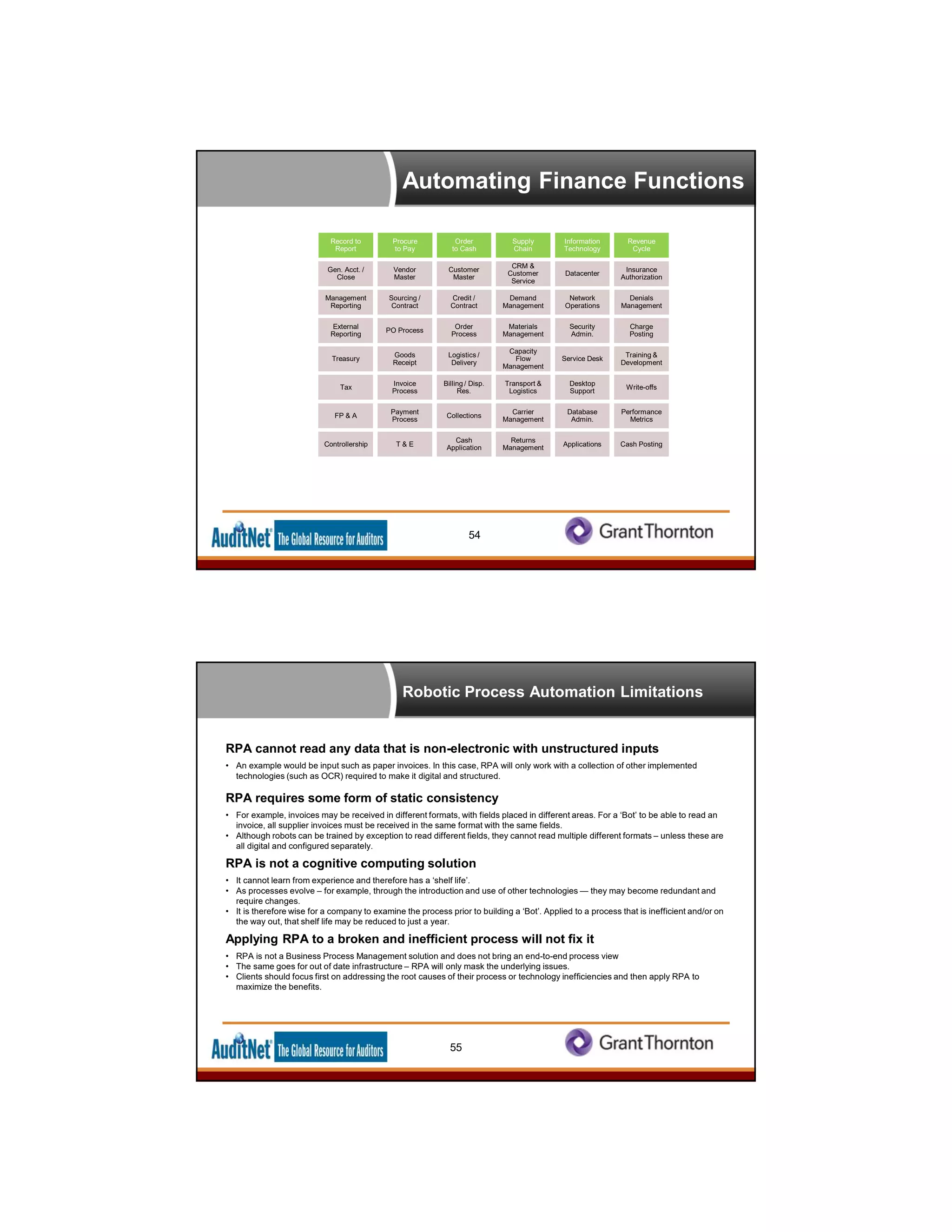
The document outlines the future of auditing and fraud detection, emphasizing the importance of data analytics in enhancing audit processes. It discusses the capabilities of AuditNet, a key resource for auditors, and highlights the need for continuous improvement and innovation in audit practices using technology. Various analytics methods and tools are presented, alongside the need for auditors to adapt to a data-driven environment to maximize their effectiveness.