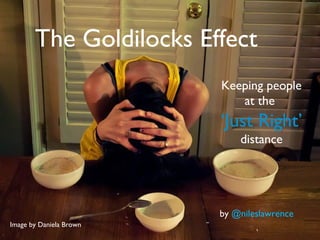
Flipbook-The Goldilocks Effect
•
3 likes•1,161 views
The document discusses how technology and social media allow people to feel constantly connected through mass communication, but this connection often isolates people and prevents meaningful human interaction. While social media gives the illusion of companionship, it lacks the demands and emotional elements of real relationships. As technology becomes the primary mode of communication, people interact less face-to-face and miss opportunities to understand each other on deeper levels. This trend risks making people unable to truly connect, trust one another, and engage in self-reflection.
Report
Share
Report
Share
Download to read offline
Recommended
Digital Relationships

This flipbook examines the positive effect that technology has on relationships
What will our relationship with technology look like

How will technology affect or imitate our relationships with people in the future? Will it become our new best friend or will it help us stay connected with our real friends?
Technology: Creating Positive Relationships

This flipbook examines the positive benefits of social media and technology usage in relationships.
Recommended
Digital Relationships

This flipbook examines the positive effect that technology has on relationships
What will our relationship with technology look like

How will technology affect or imitate our relationships with people in the future? Will it become our new best friend or will it help us stay connected with our real friends?
Technology: Creating Positive Relationships

This flipbook examines the positive benefits of social media and technology usage in relationships.
Social impact of technology presentation

Communication technology pushing us towards social isolation and neurosis
Technology and Social Interactions - Maya Mounayar 

This is my answer to the following question for IE business school application:
How do you imagine social interaction within 10 years, taking into consideration the impact of technology on human relations?
By Maya Mounayar
Inverge 08 From Telephone To Tweetup

This is the PowerPoint of a lightning talk given by Amber Case (@caseorganic) at Inverge: The Interactive Convergence Conference in Portland, Oregon on Sept 4+5th.
NOTE: This was a 10-minute compressed presentation.
From Telephone to Tweetup: an abbreviated history of technology and social exchange
The invention of the telephone ushered in an era of ‘on-demand’ social connection. These conversations were freeing, but were still limited to location and time. As communication technology matured, telephones became detached from their cords and were allowed to travel with their users. This detachment from location allowed conversation to happen in more times and more places.
As the amount of time and space between nodes of connection decreased, the intersection of rapid news methods such as blogging, mobile technology, and chatrooms begin to merge. This convergence allowed dramatic increases in the ability to rapidly convey information to others. Instead of engaging with one person at a time, many are now capable of talking at once. No where is this more prevalent than on Twitter. It has found ways to connect communities, stave off suburban isolation, and warn of earthquakes before medical help can access them.
The distance between individual and community will continue to decrease, and those products and services which decrease the amount of time and space it takes to create an action will be the most successful. Actions and devices will become lighter and lighter, and the social will continue to become more and more mobile. The convergence of various technologies will result in rapid learning and communication never imagined before.
http://inverge.com/featured-speakers/amber-case/
How do you imagine social interaction within 10 years, taking into considerat...

IE APPLICATION 2014/2015 MSc in Finance
Digital Engagement Presentation Blackburn 18 march

My Presentation from Local By Social 18 March 2011 Ewood Park.
Highly-Effective Relationships in a Technology-Driven World: An Impossible Po...

Dr John J Scherer & Amy Barnes, MBA, Kongres Biznes To Rozmowy 2013, NETIA
IE admissions essay: The Future of Social Interaction

This presentation is in response to the IE admissions essay question:
How do you imagine social interaction within 10 years, taking into consideration the impact of technology on human relations?
Digitization of life

Digital is not just about technology. Here’s how it is making an impact on the various aspects of our lives.
MEME culture and communications - Justine Toms

MEME culture and communications - Justine Toms, NBU May 2020
How do you imagine SOCIAL INTERACTION within 10 years, taking into considerat...

How do you imagine SOCIAL INTERACTION within 10 years, taking into considerat...Stephanie Heinemann Garza
IE Masters Application - Stephanie Heinemann GarzaReveal & Reduce the threat of Deep Fake Technology

We've moved from no concern over our privacy to unabashed openness back to an acute awareness of the value of how our actions can in-turn affect us when we give it up to corporations and platforms. There is an awakening to that responsibility in the mainstream due to Facebook data breaches and the vulnerability of it's systems to manipulation, not to mention awareness of how the algorithm works in filter bubbling. This potential context collapse is related to themes of trust, identity and reality - what is real and what is fake? Now there is the proliferation of 'Deep-fake' technology what can we do to protect ourselves against attacks on democracy and if we can longer tell the difference between counterfeit and authenticity where does that leave us?
More Related Content
What's hot
Social impact of technology presentation

Communication technology pushing us towards social isolation and neurosis
Technology and Social Interactions - Maya Mounayar 

This is my answer to the following question for IE business school application:
How do you imagine social interaction within 10 years, taking into consideration the impact of technology on human relations?
By Maya Mounayar
Inverge 08 From Telephone To Tweetup

This is the PowerPoint of a lightning talk given by Amber Case (@caseorganic) at Inverge: The Interactive Convergence Conference in Portland, Oregon on Sept 4+5th.
NOTE: This was a 10-minute compressed presentation.
From Telephone to Tweetup: an abbreviated history of technology and social exchange
The invention of the telephone ushered in an era of ‘on-demand’ social connection. These conversations were freeing, but were still limited to location and time. As communication technology matured, telephones became detached from their cords and were allowed to travel with their users. This detachment from location allowed conversation to happen in more times and more places.
As the amount of time and space between nodes of connection decreased, the intersection of rapid news methods such as blogging, mobile technology, and chatrooms begin to merge. This convergence allowed dramatic increases in the ability to rapidly convey information to others. Instead of engaging with one person at a time, many are now capable of talking at once. No where is this more prevalent than on Twitter. It has found ways to connect communities, stave off suburban isolation, and warn of earthquakes before medical help can access them.
The distance between individual and community will continue to decrease, and those products and services which decrease the amount of time and space it takes to create an action will be the most successful. Actions and devices will become lighter and lighter, and the social will continue to become more and more mobile. The convergence of various technologies will result in rapid learning and communication never imagined before.
http://inverge.com/featured-speakers/amber-case/
How do you imagine social interaction within 10 years, taking into considerat...

IE APPLICATION 2014/2015 MSc in Finance
Digital Engagement Presentation Blackburn 18 march

My Presentation from Local By Social 18 March 2011 Ewood Park.
Highly-Effective Relationships in a Technology-Driven World: An Impossible Po...

Dr John J Scherer & Amy Barnes, MBA, Kongres Biznes To Rozmowy 2013, NETIA
IE admissions essay: The Future of Social Interaction

This presentation is in response to the IE admissions essay question:
How do you imagine social interaction within 10 years, taking into consideration the impact of technology on human relations?
Digitization of life

Digital is not just about technology. Here’s how it is making an impact on the various aspects of our lives.
MEME culture and communications - Justine Toms

MEME culture and communications - Justine Toms, NBU May 2020
What's hot (20)
Technology and Social Interactions - Maya Mounayar 

Technology and Social Interactions - Maya Mounayar
How do you imagine social interaction within 10 years, taking into considerat...

How do you imagine social interaction within 10 years, taking into considerat...
Our Dependence on Technology is Causing Social Isolation

Our Dependence on Technology is Causing Social Isolation
Digital Engagement Presentation Blackburn 18 march

Digital Engagement Presentation Blackburn 18 march
Highly-Effective Relationships in a Technology-Driven World: An Impossible Po...

Highly-Effective Relationships in a Technology-Driven World: An Impossible Po...
IE admissions essay: The Future of Social Interaction

IE admissions essay: The Future of Social Interaction
Similar to Flipbook-The Goldilocks Effect
How do you imagine SOCIAL INTERACTION within 10 years, taking into considerat...

How do you imagine SOCIAL INTERACTION within 10 years, taking into considerat...Stephanie Heinemann Garza
IE Masters Application - Stephanie Heinemann GarzaReveal & Reduce the threat of Deep Fake Technology

We've moved from no concern over our privacy to unabashed openness back to an acute awareness of the value of how our actions can in-turn affect us when we give it up to corporations and platforms. There is an awakening to that responsibility in the mainstream due to Facebook data breaches and the vulnerability of it's systems to manipulation, not to mention awareness of how the algorithm works in filter bubbling. This potential context collapse is related to themes of trust, identity and reality - what is real and what is fake? Now there is the proliferation of 'Deep-fake' technology what can we do to protect ourselves against attacks on democracy and if we can longer tell the difference between counterfeit and authenticity where does that leave us?
Plugged Into Our Devices

A flipbook made for my FILM260 class on how our communication is being affected as we are plugged into our technological devices.
Connections Lost: The Damages of Textual Conversation and Multi-Communication

Digital Flipbook Assignment for FILM260
Tinder My life Away, An analysis of the Pros and Cons of social technolohgy

Tinder My life Away, An analysis of the Pros and Cons of social technolohgy
Parker 1Nameo ParkerProfessor MunroEnglish 102-10226 Oct.docx

Parker 1
Nameo Parker
Professor Munro
English 102-102
26 October 2017
Mobile Tech: Cellular Stranger Danger
It’s probably safe to say that most people can be accused of, more often than not, peering down towards their mobile phones fairly often throughout the day; to check for emails or status updates or simply, just pass the time. It would be an unusual sight to be practically anywhere, and not see someone looking down toward a mobile device. Not surprisingly, “[t]he average American spends nearly half a day staring at a screen;” nearly eleven hours each day is spent consuming media; astonishingly, this number was calculated on media usage only and didn’t include time spent texting or taking pictures (Howard). Perhaps one could admit, through the constant use of mobile devices, complacency is becoming the new norm. Personal contact, good listening skills and our physical/mental health are all affected by the incessant need to stay updated and connected.
In the 1800's, a railroad construction worker by the name of Phineas Gage, permanently damaged the left half of his brain, the frontal lobe, when a large iron rod pierced through his cheek and out of his skull: "Gage not only survived the incident but also apparently never fully lost consciousness" (Guidotti). Before the accident he was known as being "reliable, systematic, and hardworking;" after the incident and the damage to his frontal lobe, Gage became "impulsive" and neurotic in his behavior (Guidotti). At the time, physicians didn't realize that the frontal lobe is the area of the brain that is "responsible for decoding and comprehending social interactions;" it is through this area of the brain that we learn how to read numerous facial cues and personal flair that one exhibits when interacting with others (Margalit). In the early 1900's a psychosurgical procedure called the prefrontal lobotomy was first performed on humans. This "surgical operation separat[ed] the frontal brain lobes from the thalamus to relieve extreme anxiety" and was proclaimed a miracle cure for those suffering from mental disease (Shaffer). Some fifty years later the lobotomy became unpopular because "the operation caused mental deterioration" and would eventually be replaced with chemical versions of treatment; i.e., antipsychotic drugs, tranquilizers (Shaffer). Over time, scientist have begun to realize that when replacing real-life contact with symbols and text through a screen, the capabilities of the brains frontal lobe lose effectiveness; empathetic abilities dwindle and engaged interactions with real people become more and more difficult. Some addicted tech users have issues with depression and anxiety when having to interact with a real human being; through constant engagement with a screen and habitually less real-world interactions and relationships, we are losing our abilities to care, to understand, to feel emotion.
Is our desire to stay in touch and be in the know diminishing other aspects of our .
Similar to Flipbook-The Goldilocks Effect (19)
How do you imagine SOCIAL INTERACTION within 10 years, taking into considerat...

How do you imagine SOCIAL INTERACTION within 10 years, taking into considerat...
Reveal & Reduce the threat of Deep Fake Technology

Reveal & Reduce the threat of Deep Fake Technology
Connections Lost: The Damages of Textual Conversation and Multi-Communication

Connections Lost: The Damages of Textual Conversation and Multi-Communication
Tinder My life Away, An analysis of the Pros and Cons of social technolohgy

Tinder My life Away, An analysis of the Pros and Cons of social technolohgy
Is Technology Eroding Our Relationships? By: Dayna Hill

Is Technology Eroding Our Relationships? By: Dayna Hill
Parker 1Nameo ParkerProfessor MunroEnglish 102-10226 Oct.docx

Parker 1Nameo ParkerProfessor MunroEnglish 102-10226 Oct.docx
Recently uploaded
Leading Change strategies and insights for effective change management pdf 1.pdf

Leading Change strategies and insights for effective change management pdf 1.pdf
DevOps and Testing slides at DASA Connect

My and Rik Marselis slides at 30.5.2024 DASA Connect conference. We discuss about what is testing, then what is agile testing and finally what is Testing in DevOps. Finally we had lovely workshop with the participants trying to find out different ways to think about quality and testing in different parts of the DevOps infinity loop.
When stars align: studies in data quality, knowledge graphs, and machine lear...

Keynote at DQMLKG workshop at the 21st European Semantic Web Conference 2024
State of ICS and IoT Cyber Threat Landscape Report 2024 preview

The IoT and OT threat landscape report has been prepared by the Threat Research Team at Sectrio using data from Sectrio, cyber threat intelligence farming facilities spread across over 85 cities around the world. In addition, Sectrio also runs AI-based advanced threat and payload engagement facilities that serve as sinks to attract and engage sophisticated threat actors, and newer malware including new variants and latent threats that are at an earlier stage of development.
The latest edition of the OT/ICS and IoT security Threat Landscape Report 2024 also covers:
State of global ICS asset and network exposure
Sectoral targets and attacks as well as the cost of ransom
Global APT activity, AI usage, actor and tactic profiles, and implications
Rise in volumes of AI-powered cyberattacks
Major cyber events in 2024
Malware and malicious payload trends
Cyberattack types and targets
Vulnerability exploit attempts on CVEs
Attacks on counties – USA
Expansion of bot farms – how, where, and why
In-depth analysis of the cyber threat landscape across North America, South America, Europe, APAC, and the Middle East
Why are attacks on smart factories rising?
Cyber risk predictions
Axis of attacks – Europe
Systemic attacks in the Middle East
Download the full report from here:
https://sectrio.com/resources/ot-threat-landscape-reports/sectrio-releases-ot-ics-and-iot-security-threat-landscape-report-2024/
Unsubscribed: Combat Subscription Fatigue With a Membership Mentality by Head...

Unsubscribed: Combat Subscription Fatigue With a Membership Mentality by Head of Product, Amazon Games
AI for Every Business: Unlocking Your Product's Universal Potential by VP of ...

AI for Every Business: Unlocking Your Product's Universal Potential by VP of Product, Slack
UiPath Test Automation using UiPath Test Suite series, part 3

Welcome to UiPath Test Automation using UiPath Test Suite series part 3. In this session, we will cover desktop automation along with UI automation.
Topics covered:
UI automation Introduction,
UI automation Sample
Desktop automation flow
Pradeep Chinnala, Senior Consultant Automation Developer @WonderBotz and UiPath MVP
Deepak Rai, Automation Practice Lead, Boundaryless Group and UiPath MVP
The Art of the Pitch: WordPress Relationships and Sales

Clients don’t know what they don’t know. What web solutions are right for them? How does WordPress come into the picture? How do you make sure you understand scope and timeline? What do you do if sometime changes?
All these questions and more will be explored as we talk about matching clients’ needs with what your agency offers without pulling teeth or pulling your hair out. Practical tips, and strategies for successful relationship building that leads to closing the deal.
GDG Cloud Southlake #33: Boule & Rebala: Effective AppSec in SDLC using Deplo...

Effective Application Security in Software Delivery lifecycle using Deployment Firewall and DBOM
The modern software delivery process (or the CI/CD process) includes many tools, distributed teams, open-source code, and cloud platforms. Constant focus on speed to release software to market, along with the traditional slow and manual security checks has caused gaps in continuous security as an important piece in the software supply chain. Today organizations feel more susceptible to external and internal cyber threats due to the vast attack surface in their applications supply chain and the lack of end-to-end governance and risk management.
The software team must secure its software delivery process to avoid vulnerability and security breaches. This needs to be achieved with existing tool chains and without extensive rework of the delivery processes. This talk will present strategies and techniques for providing visibility into the true risk of the existing vulnerabilities, preventing the introduction of security issues in the software, resolving vulnerabilities in production environments quickly, and capturing the deployment bill of materials (DBOM).
Speakers:
Bob Boule
Robert Boule is a technology enthusiast with PASSION for technology and making things work along with a knack for helping others understand how things work. He comes with around 20 years of solution engineering experience in application security, software continuous delivery, and SaaS platforms. He is known for his dynamic presentations in CI/CD and application security integrated in software delivery lifecycle.
Gopinath Rebala
Gopinath Rebala is the CTO of OpsMx, where he has overall responsibility for the machine learning and data processing architectures for Secure Software Delivery. Gopi also has a strong connection with our customers, leading design and architecture for strategic implementations. Gopi is a frequent speaker and well-known leader in continuous delivery and integrating security into software delivery.
GraphRAG is All You need? LLM & Knowledge Graph

Guy Korland, CEO and Co-founder of FalkorDB, will review two articles on the integration of language models with knowledge graphs.
1. Unifying Large Language Models and Knowledge Graphs: A Roadmap.
https://arxiv.org/abs/2306.08302
2. Microsoft Research's GraphRAG paper and a review paper on various uses of knowledge graphs:
https://www.microsoft.com/en-us/research/blog/graphrag-unlocking-llm-discovery-on-narrative-private-data/
Transcript: Selling digital books in 2024: Insights from industry leaders - T...

The publishing industry has been selling digital audiobooks and ebooks for over a decade and has found its groove. What’s changed? What has stayed the same? Where do we go from here? Join a group of leading sales peers from across the industry for a conversation about the lessons learned since the popularization of digital books, best practices, digital book supply chain management, and more.
Link to video recording: https://bnctechforum.ca/sessions/selling-digital-books-in-2024-insights-from-industry-leaders/
Presented by BookNet Canada on May 28, 2024, with support from the Department of Canadian Heritage.
How world-class product teams are winning in the AI era by CEO and Founder, P...

How world-class product teams are winning in the AI era by CEO and Founder, Product School
From Siloed Products to Connected Ecosystem: Building a Sustainable and Scala...

From Siloed Products to Connected Ecosystem: Building a Sustainable and Scalable Platform by VP of Product, The New York Times
Epistemic Interaction - tuning interfaces to provide information for AI support

Paper presented at SYNERGY workshop at AVI 2024, Genoa, Italy. 3rd June 2024
https://alandix.com/academic/papers/synergy2024-epistemic/
As machine learning integrates deeper into human-computer interactions, the concept of epistemic interaction emerges, aiming to refine these interactions to enhance system adaptability. This approach encourages minor, intentional adjustments in user behaviour to enrich the data available for system learning. This paper introduces epistemic interaction within the context of human-system communication, illustrating how deliberate interaction design can improve system understanding and adaptation. Through concrete examples, we demonstrate the potential of epistemic interaction to significantly advance human-computer interaction by leveraging intuitive human communication strategies to inform system design and functionality, offering a novel pathway for enriching user-system engagements.
Mission to Decommission: Importance of Decommissioning Products to Increase E...

Mission to Decommission: Importance of Decommissioning Products to Increase Enterprise-Wide Efficiency by VP Data Platform, American Express
Neuro-symbolic is not enough, we need neuro-*semantic*

Neuro-symbolic (NeSy) AI is on the rise. However, simply machine learning on just any symbolic structure is not sufficient to really harvest the gains of NeSy. These will only be gained when the symbolic structures have an actual semantics. I give an operational definition of semantics as “predictable inference”.
All of this illustrated with link prediction over knowledge graphs, but the argument is general.
Smart TV Buyer Insights Survey 2024 by 91mobiles.pdf

91mobiles recently conducted a Smart TV Buyer Insights Survey in which we asked over 3,000 respondents about the TV they own, aspects they look at on a new TV, and their TV buying preferences.
Dev Dives: Train smarter, not harder – active learning and UiPath LLMs for do...

💥 Speed, accuracy, and scaling – discover the superpowers of GenAI in action with UiPath Document Understanding and Communications Mining™:
See how to accelerate model training and optimize model performance with active learning
Learn about the latest enhancements to out-of-the-box document processing – with little to no training required
Get an exclusive demo of the new family of UiPath LLMs – GenAI models specialized for processing different types of documents and messages
This is a hands-on session specifically designed for automation developers and AI enthusiasts seeking to enhance their knowledge in leveraging the latest intelligent document processing capabilities offered by UiPath.
Speakers:
👨🏫 Andras Palfi, Senior Product Manager, UiPath
👩🏫 Lenka Dulovicova, Product Program Manager, UiPath
GenAISummit 2024 May 28 Sri Ambati Keynote: AGI Belongs to The Community in O...

“AGI should be open source and in the public domain at the service of humanity and the planet.”
Recently uploaded (20)
Leading Change strategies and insights for effective change management pdf 1.pdf

Leading Change strategies and insights for effective change management pdf 1.pdf
When stars align: studies in data quality, knowledge graphs, and machine lear...

When stars align: studies in data quality, knowledge graphs, and machine lear...
State of ICS and IoT Cyber Threat Landscape Report 2024 preview

State of ICS and IoT Cyber Threat Landscape Report 2024 preview
Unsubscribed: Combat Subscription Fatigue With a Membership Mentality by Head...

Unsubscribed: Combat Subscription Fatigue With a Membership Mentality by Head...
AI for Every Business: Unlocking Your Product's Universal Potential by VP of ...

AI for Every Business: Unlocking Your Product's Universal Potential by VP of ...
UiPath Test Automation using UiPath Test Suite series, part 3

UiPath Test Automation using UiPath Test Suite series, part 3
The Art of the Pitch: WordPress Relationships and Sales

The Art of the Pitch: WordPress Relationships and Sales
GDG Cloud Southlake #33: Boule & Rebala: Effective AppSec in SDLC using Deplo...

GDG Cloud Southlake #33: Boule & Rebala: Effective AppSec in SDLC using Deplo...
Transcript: Selling digital books in 2024: Insights from industry leaders - T...

Transcript: Selling digital books in 2024: Insights from industry leaders - T...
How world-class product teams are winning in the AI era by CEO and Founder, P...

How world-class product teams are winning in the AI era by CEO and Founder, P...
From Siloed Products to Connected Ecosystem: Building a Sustainable and Scala...

From Siloed Products to Connected Ecosystem: Building a Sustainable and Scala...
Epistemic Interaction - tuning interfaces to provide information for AI support

Epistemic Interaction - tuning interfaces to provide information for AI support
Mission to Decommission: Importance of Decommissioning Products to Increase E...

Mission to Decommission: Importance of Decommissioning Products to Increase E...
Neuro-symbolic is not enough, we need neuro-*semantic*

Neuro-symbolic is not enough, we need neuro-*semantic*
Smart TV Buyer Insights Survey 2024 by 91mobiles.pdf

Smart TV Buyer Insights Survey 2024 by 91mobiles.pdf
Dev Dives: Train smarter, not harder – active learning and UiPath LLMs for do...

Dev Dives: Train smarter, not harder – active learning and UiPath LLMs for do...
GenAISummit 2024 May 28 Sri Ambati Keynote: AGI Belongs to The Community in O...

GenAISummit 2024 May 28 Sri Ambati Keynote: AGI Belongs to The Community in O...
Flipbook-The Goldilocks Effect
- 1. The Goldilocks Effect Keeping people at the ‘Just Right’ distance Image by Daniela Brown by @nileslawrence
- 2. Technology allows us to constantly connect with many people at the same time Image by ipmatth
- 3. Technology keeps us connected, but traps us in individual bubbles Image by gnomeza
- 4. “The more connected we become the more likely we are to be Image by LB London alone” -Michelle Atagana
- 5. We hide our true self only showing the ‘ideal’ on Facebook & Twitter Image by Brittany Greene
- 6. But human relationships are Image by J+B=Us messy sporadic and
- 7. Real conversation accounts for tone, allows for understanding at a deeper level, and seeing from a different point of view Image by Zombies-eat-flesh
- 8. With no emotional interaction, technology even changes who we are... Image by Johan Larssom
- 9. We expect communication to be quick, simple, and synced Image by eschipul
- 10. We are becoming unable to truly connect, build trust, and in turn self reflect Image by Grizdave
- 11. People are in their own worlds and are actively avoiding real conversation Image by Sean Dreilinger
- 12. When people are unable to connect, they turn less and less to people and more to technology Image by BenSpark
- 13. In January 2013, Facebook had 1.06+ billion monthly users Image by Owenwbrown 618+ million were daily active users Source: Facebook passes 1.06 billion monthly active users, 680 million mobile users, and 618 million daily users
- 14. Constant tweets and Facebook updates reflect our need to be heard Image by Johan Larssom
- 15. Technology relationships mislead us to believe we have real relationships Image by gfpeck “I share therefore I am”
- 16. “We seem increasingly drawn to technologies that provide the illusion of companionship without the demands of relationship” –Sherry Tuckle Image by h.koppdelaney
- 17. Technology becomes our method of choice even for important conversations. Image by Darwin70
- 18. "A full-scale apology means I know I've hurt you, I get to see that in your eyes, You get to see that I'm uncomfortable, and with that, the compassion response kicks in.” -Sherry Turkle texting “I’m sorry” and hitting send bypasses the human interaction Image by Ahmad Chaudhary1
- 19. As time goes on, we communicate less with people and more with technology. Image by DavidShutter
- 20. We mass communicate and miss out on the Image by Quinn Anya emotions in front of us...
- 21. Image by tribes Even telephone use is dying. - Pew Institute 188 Billion text messages were sent monthly in the U.S. in 2010 Souce: We never talk any more: The problem with text messaging Image by tribes
- 22. Though connected, we are alone.... Image by prayitno
- 23. Image by Lucy Takakura Text Research References: 1. http://www.nytimes.com/2012/04/22/opinion/sunday/the- flight-from-conversation.html?pagewanted=all&_r=0 2. http://memeburn.com/2012/04/the-goldilocks-effect- connected-but-alone-ted-video/ 3. http://www.bitrebels.com/social/how-social-media-is- making-us-awkward-infographic/ 4. http://www.sysomos.com/insidetwitter/sixdegrees/ 5. http://larryborsato.com/blog/2012/04/the-goldilocks- effect/ 6. http://thenextweb.com/facebook/2013/01/30/facebook- passes-1-06-billion-monthly-active-users-680-million- mobile-users-and-618-million-daily-users/ 7. http://www.cnn.com/2012/08/31/tech/mobile/problem- text-messaging-oms
