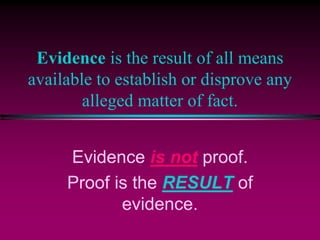
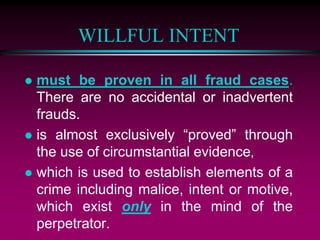
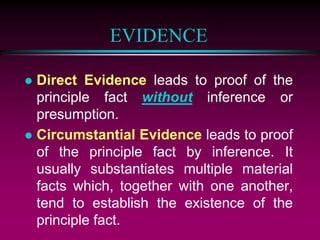
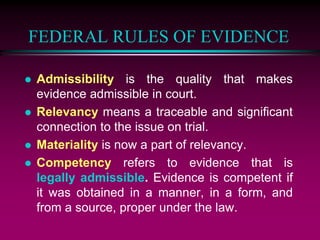
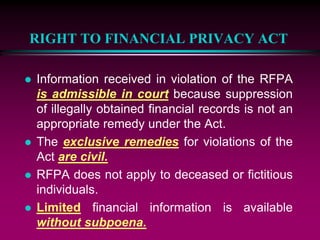
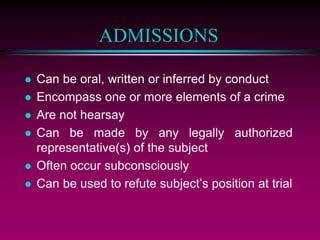
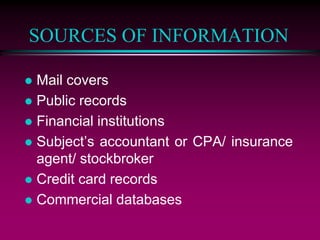
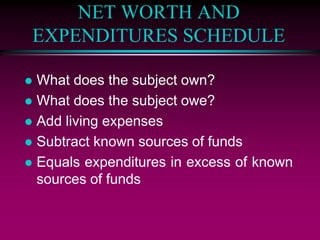
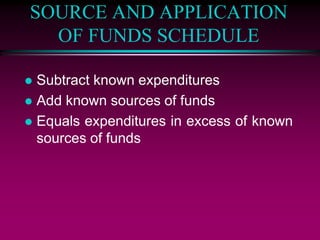
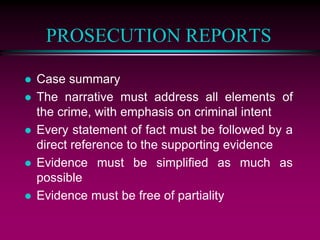
The document outlines the processes and principles related to financial evidence in legal contexts, including the types of evidence, rules of admissibility, and methods for establishing willful intent in fraud cases. It discusses the significance of direct and circumstantial evidence, the best evidence rule, and various sources of information pertinent to financial investigations. Additionally, it addresses legal aspects such as the government-informant privilege and the Right to Financial Privacy Act, emphasizing the necessity for precise documentation in prosecution reports.