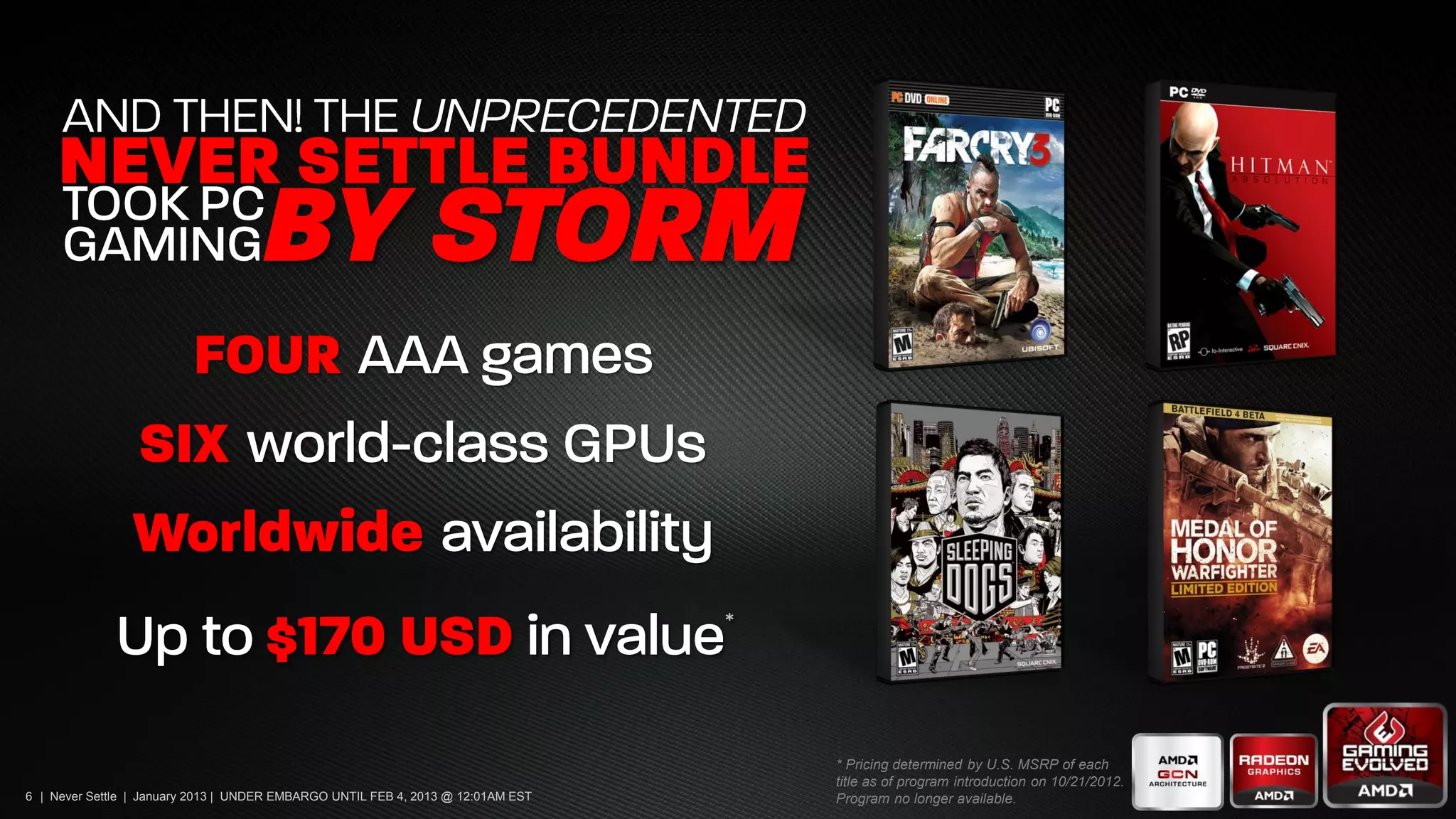
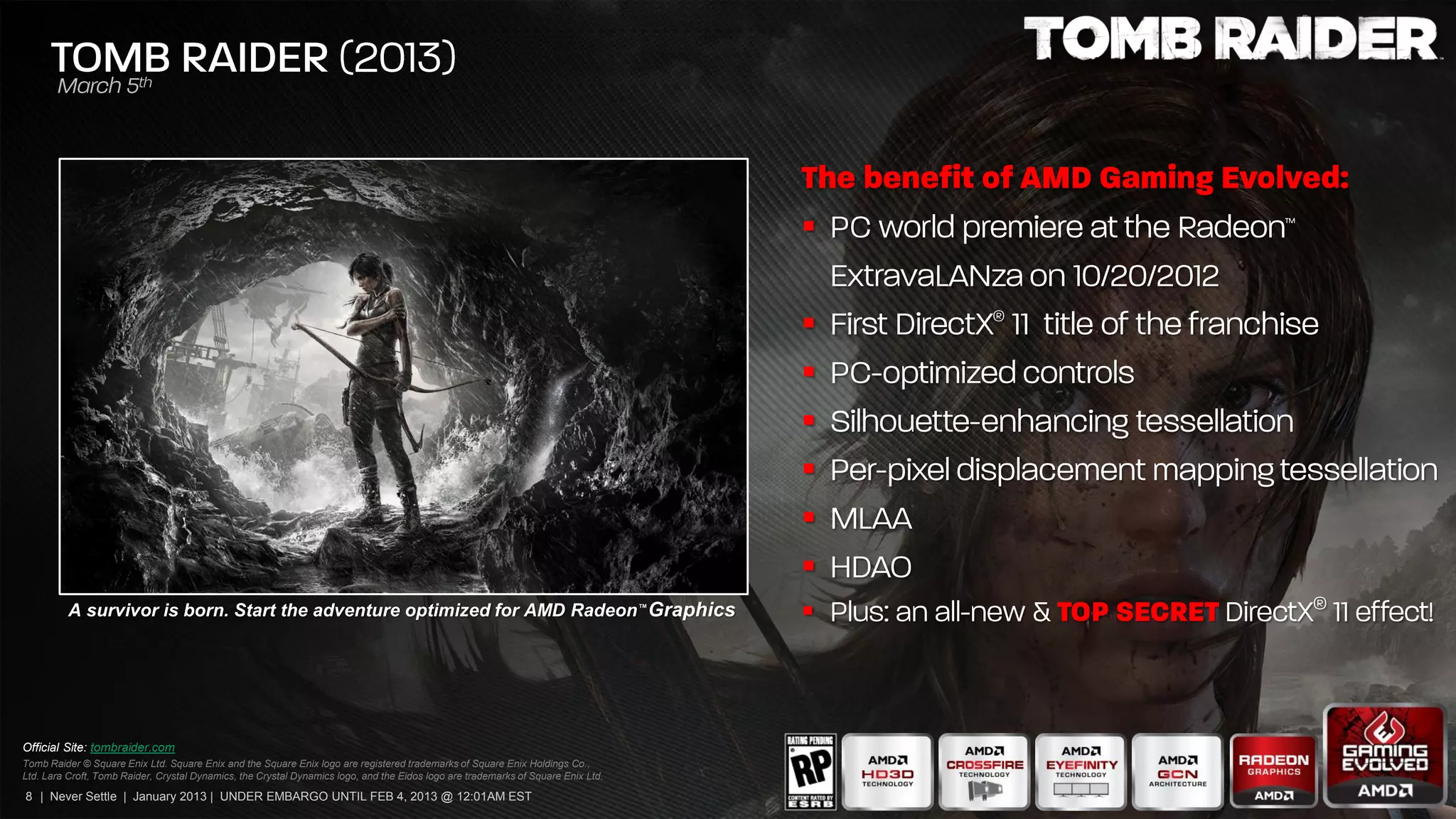
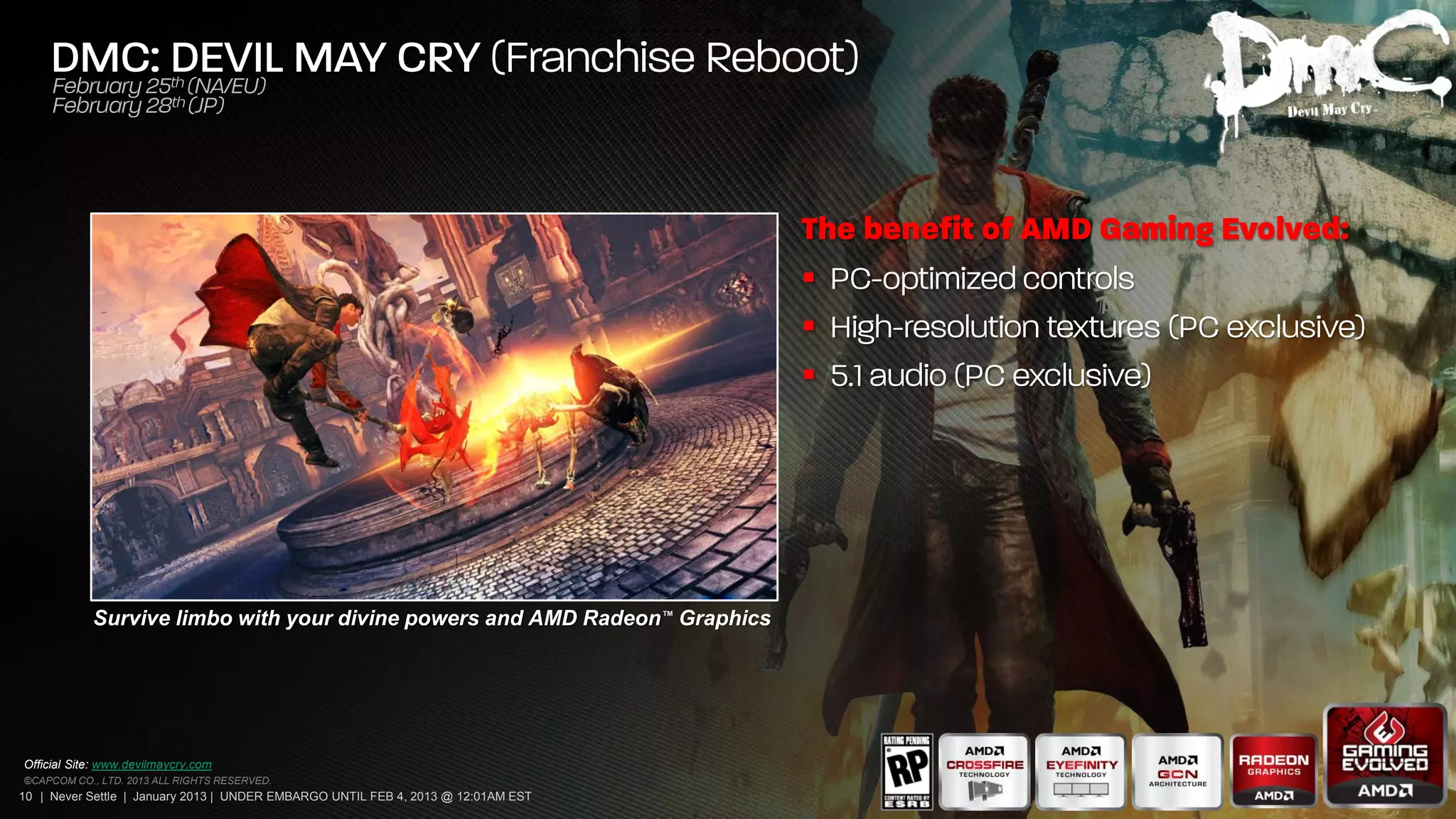
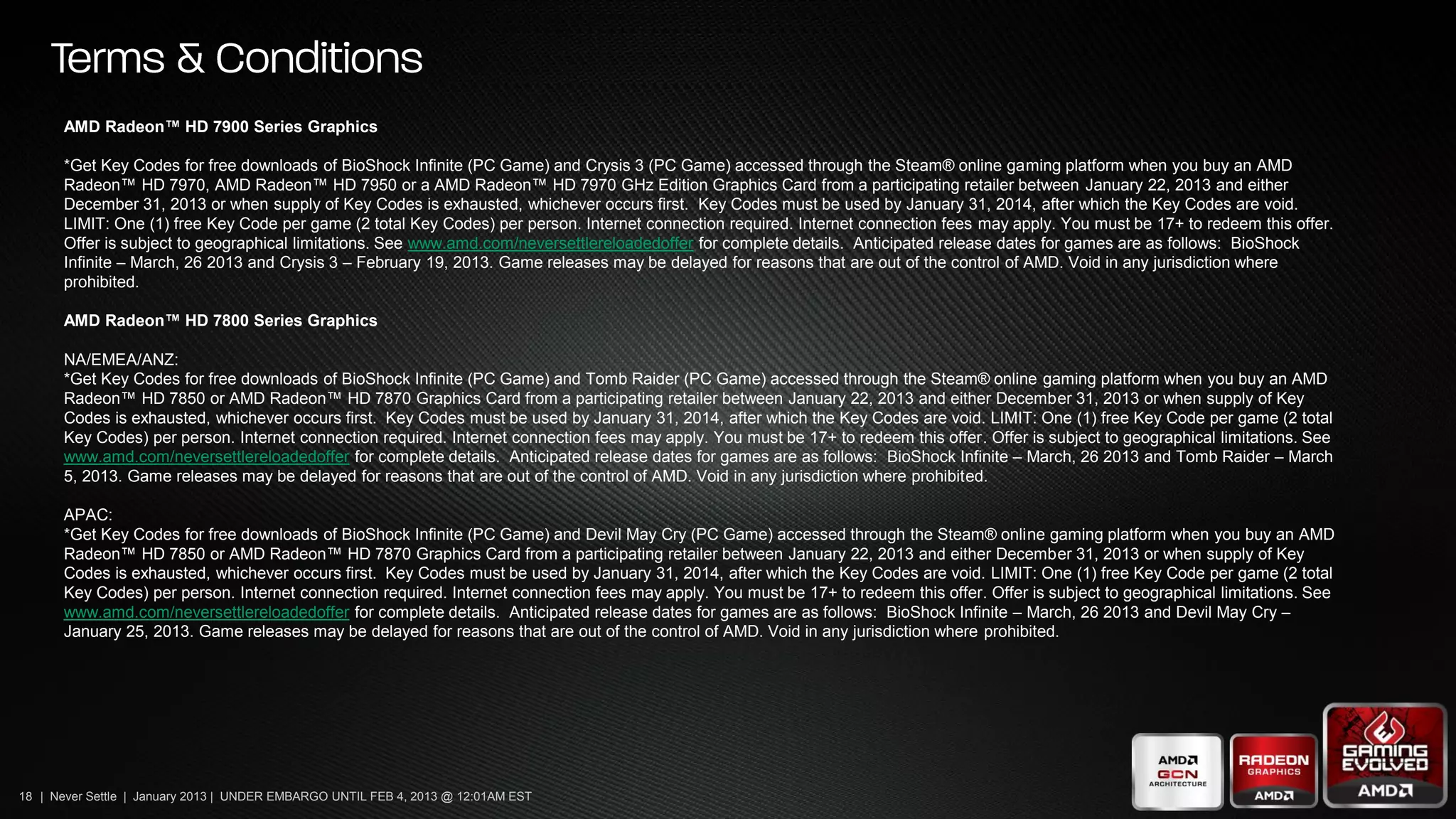
This document is a marketing deck from AMD dated January 2013 that is under embargo until February 4, 2013 at 12:01 AM EST. It promotes AMD Radeon graphics cards and offers free games with purchase, including Bioshock Infinite, Tomb Raider, Crysis 3, and Devil May Cry. Details on qualifying graphics cards and regions are provided. Legal disclaimers are included at the end.