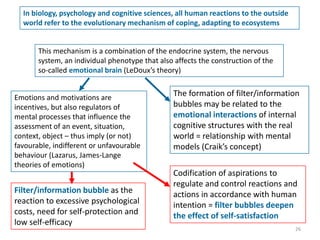
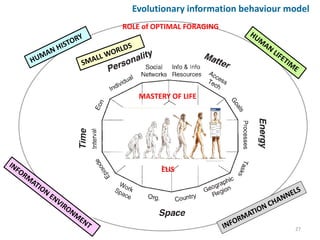
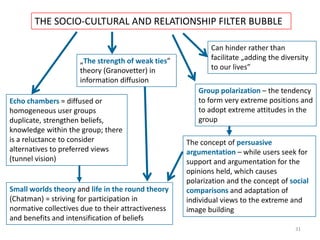
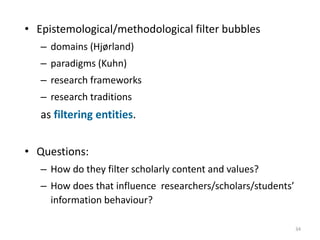
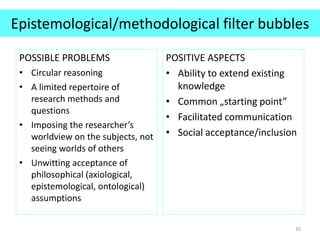
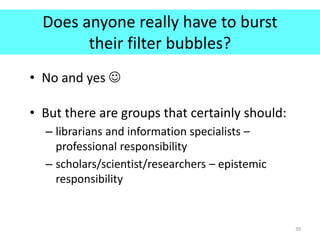
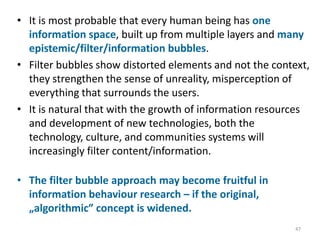
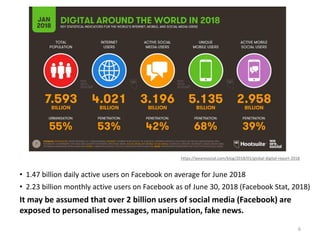
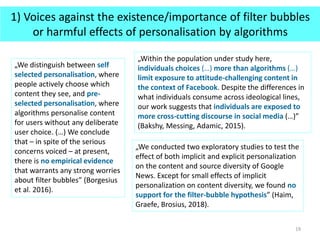
The document discusses the concept of filter bubbles and their potential relevance for information behavior research. It defines filter bubbles as the intellectual isolation that can occur when websites selectively present information to users based on their past behavior and location. This personalization may limit exposure to opposing viewpoints. However, some research has questioned whether strong filter bubbles actually exist or whether personalization has significant negative effects. The document also explores filter bubbles from psychological, socio-cultural, and epistemological perspectives and provides some suggestions for how to mitigate the effects of filter bubbles, such as developing critical thinking skills and using different search tools and engines.


![Scholarly publications on filter bubbles [1]
• Google Scholar – about 5430 results
• Scopus (in Title-Abstract-Keywords) – 21 results, from years
2012-2018
• Web of Science (all databases) in the Topic category – 17
results, from years 2011-2018
• Wiley Online Library – 40 results, from years 2011-2018
• LISTA Library, Information Science and Technology Abstracts –
13 results, from years 2011-2018
10
Query „filter bubble” AND internet, September 2018](https://image.slidesharecdn.com/filterbubbleandinfobehcisekkrakowskafinal2-181010163505/85/Filter-bubble-and-information-behaviour-ISIC-2018-keynote-speech-10-320.jpg)
![Scholarly publications on filter bubbles [2]
• Google Scholar – about 135 results
• Scopus (in Title-Abstract-Keywords) – 0 results
• Web of Science (all databases) in the Topic category – 0
results
• Wiley Online Library – 2 results, from years 2012-2018
• LISTA Library, Information Science and Technology
Abstracts – 1 result (Tran, Yerbury, 2015)
11
Query „filter bubble” AND („information behavior”
OR „information behaviour”), September 2018](https://image.slidesharecdn.com/filterbubbleandinfobehcisekkrakowskafinal2-181010163505/85/Filter-bubble-and-information-behaviour-ISIC-2018-keynote-speech-11-320.jpg)
![What is a filter bubble – in its narrow,
„algorithmic” sense? [1]
• The term „filter bubble” was coined
by Eli Pariser in his book The filter
bubble: what the internet is hiding
from you (2011), cited 2886 times
(Google Scholar)
• But – the problem itself had been
discussed earlier (e.g. Sunstein,
2001; 2007)
15](https://image.slidesharecdn.com/filterbubbleandinfobehcisekkrakowskafinal2-181010163505/85/Filter-bubble-and-information-behaviour-ISIC-2018-keynote-speech-15-320.jpg)
![What is a filter bubble – in its narrow,
„algorithmic” sense? [2]
„A filter bubble is the intellectual isolation that can occur when websites make
use of algorithms to selectively assume the information a user would want to
see, and then give information to the user according to this assumption.
Websites make these assumptions based on the information related to the user,
such as former click behavior, browsing history, search history and location. For
that reason, the websites are more likely to present only information that will
abide by the user's past activity.
A filter bubble, therefore, can cause users to get significantly less contact with
contradicting viewpoints, causing the user to become intellectually isolated.
Personalized search results from Google and personalized news stream from
Facebook are two perfect examples of this phenomenon.”
https://www.techopedia.com/definition/28556/filter-bubble
16](https://image.slidesharecdn.com/filterbubbleandinfobehcisekkrakowskafinal2-181010163505/85/Filter-bubble-and-information-behaviour-ISIC-2018-keynote-speech-16-320.jpg)
![Widening of the filter bubble concept [1]
• Three „layers” of filter bubbles – users lack
knowledge about
– the existence, way of working, or effects of filtering
algorithms and personalisation (Facebook, Google,
Twitter),
– more advanced search techniques within major
websites,
– the mere existence of (1) other search services and (2)
the Deep Web.
22](https://image.slidesharecdn.com/filterbubbleandinfobehcisekkrakowskafinal2-181010163505/85/Filter-bubble-and-information-behaviour-ISIC-2018-keynote-speech-22-320.jpg)
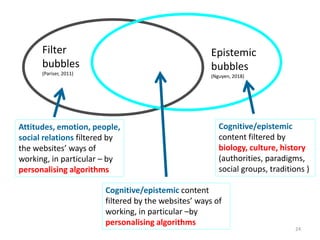
![Widening of the filter bubble concept [2]
• Filter bubbles and epistemic bubbles
• Information behaviour/seeking is not only
technology-driven and affected solely by cognitive
factors. It also has biological, political, psychological,
socio-cultural, and time-space determinants.
23](https://image.slidesharecdn.com/filterbubbleandinfobehcisekkrakowskafinal2-181010163505/85/Filter-bubble-and-information-behaviour-ISIC-2018-keynote-speech-23-320.jpg)