More Related Content
PPTX
ネットストーカー御用達OSINTツールBlackBirdを触ってみた.pptx PDF
PDF
PDF
NTT DATA と PostgreSQL が挑んだ総力戦 PDF
DynamoDBの初心者に伝えたい初めて触るときの勘所 PPTX
PDF
PDF
PostgreSQLアーキテクチャ入門(INSIGHT OUT 2011) What's hot
PDF
PDSを実現するにあたっての技術動向の紹介 (OAuth, OpenID Connect, UMAなど) PDF
PDF
PDF
PDF
MySQL 5.7 トラブルシューティング 性能解析入門編 PDF
PDF
PDF
PDF
Reactive Programming by UniRx �for Asynchronous & Event Processing PPTX
PDF
なんとなくOAuth怖いって思ってるやつちょっと来い PDF
PPTX
PDF
Reactive Webアプリケーション - そしてSpring 5へ #jjug_ccc #ccc_ef3 PDF
なぜ、いま リレーショナルモデルなのか(理論から学ぶデータベース実践入門読書会スペシャル) PDF
周辺知識から理解するMySQL の GIS機能 ~ClubMySQL #4 PDF
PDF
PDF
20190731 Black Belt Online Seminar Amazon ECS Deep Dive PDF
アプリ開発者、DB 管理者視点での Cloud Spanner 活用方法 | 第 10 回 Google Cloud INSIDE Games & App... Recently uploaded
PDF
TomokaEdakawa_職種と講義の関係推定に基づく履修支援システムの基礎検討_HCI2026 PDF
ST2024_PM1_2_Case_study_of_local_newspaper_company.pdf PDF
Team Topology Adaptive Organizational Design for Rapid Delivery of Valuable S... PDF
maisugimoto_曖昧さを含む仕様書の改善を目的としたアノテーション支援ツールの検討_HCI2025.pdf PDF
20260119_VIoTLT_vol22_kitazaki_v1___.pdf PDF
自転車ユーザ参加型路面画像センシングによる点字ブロック検出における性能向上方法の模索 (20260123 SeMI研) FIDOとWebAuthnとCTAPのはなし
- 1.
- 2.
自己紹介
• 鈴木 智(SatoshiSuzuki)
• 株式会社イードクトル
• Windows/ICカード/NFC/BLE/認証系
• いわゆるWebエンジニアではありません(汗
• Twitter @gebogebogeboge
• GitHub @gebogebogebo
• Qiita @gebo
– Follow Me
- 3.
- 4.
- 5.
- 6.
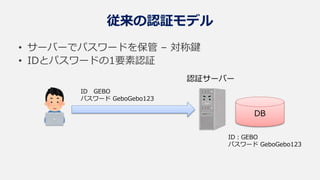
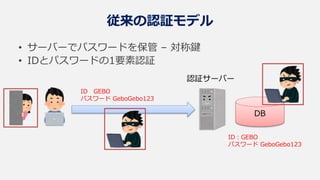
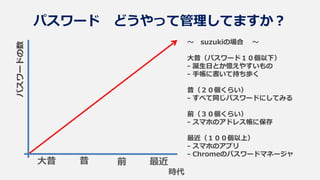
パスワードの数
時代
大昔 昔
~ suzukiの場合~
大昔(パスワード10個以下)
- 誕生日とか憶えやすいもの
- 手帳に書いて持ち歩く
昔(20個くらい)
- すべて同じパスワードにしてみる
前(30個くらい)
- スマホのアドレス帳に保存
最近(100個以上)
- スマホのアプリ
- Chromeのパスワードマネージャ
パスワード どうやって管理してますか?
前 最近
- 7.
- 8.
- 9.
- 10.
- 11.
- 12.
- 13.
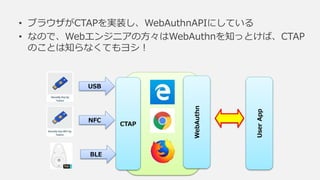
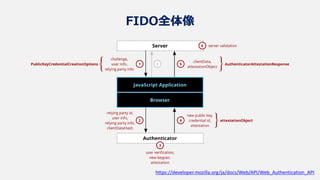
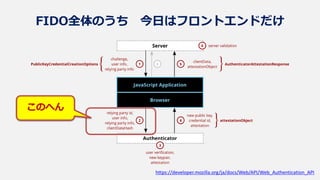
• 世界のパスワードの問題を解決するJavaScript
• FIDOAllianceとW3Cが策定
• 2019/3/4 W3C勧告
• Edge/Chrome/FireFoxが実装済み(Safariは間もなく?)
• Windows/Mac/Android対応(iOSは微妙)
というわけで WebAuthn
うぇぶ・おーすん / Web Authentication API
- 14.
- 15.
- 16.
- 17.
- 18.
- 19.
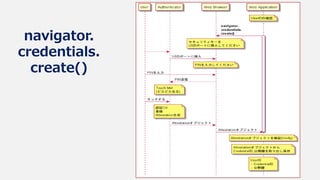
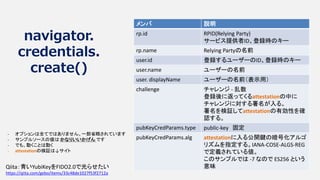
navigator.
credentials.
create()
var options ={
rp: {
id: location.host,
name: location.host,
},
user: {
id: new Uint8Array([129, 230, 232]),
name: "gebo",
displayName: "gebo",
},
challenge: window.crypto.getRandomValues(new Uint8Array(32)),
pubKeyCredParams: [
{
type: "public-key",
alg: -7, // cose_alg_ECDSA_w_SHA256,
},
],
}
// 認証にパスするとthenに入る
navigator.credentials.create({ "publicKey": options })
.then(function (attestation) {
// Success→attestationをVerifyし、中からCredentialID、公開鍵を取り出す
}).catch(function (err) {
// Error
});
Qiita:青いYubiKeyをFIDO2.0で光らせたい
https://qiita.com/gebo/items/33c48de1027f53f2712a
- 20.
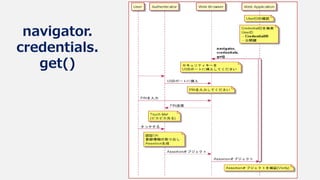
navigator.
credentials.
create()
メンバ 説明
rp.id RPID(RelyingParty)
サービス提供者ID、登録時のキー
rp.name Relying Partyの名前
user.id 登録するユーザーのID、登録時のキー
user.name ユーザーの名前
user. displayName ユーザーの名前(表示用)
challenge チャレンジ - 乱数
登録後に返ってくるattestationの中に
チャレンジに対する署名が入る。
署名を検証してattestationの有効性を確
認する。
pubKeyCredParams.type public-key 固定
pubKeyCredParams.alg attestationに入る公開鍵の暗号化アルゴ
リズムを指定する。IANA-COSE-ALGS-REG
で定義されている値。
このサンプルでは -7 なので ES256 という
意味
- オプションは全てではありません。一部省略されています
- サンプルソースの値は かなりいいかげん です
- でも、動くことは動く
- attestationの検証は↓サイト
Qiita:青いYubiKeyをFIDO2.0で光らせたい
https://qiita.com/gebo/items/33c48de1027f53f2712a
- 21.
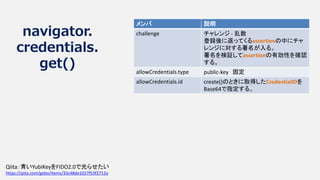
navigator.
credentials.
get()
let credentialId =create()で取得したものをセット;
var options = {
challenge: window.crypto.getRandomValues(new Uint8Array(32)),
allowCredentials: [
{
type: "public-key",
id: Base64toUint8Array(credentialId),
}
],
}
// 認証にパスするとthenに入る
navigator.credentials.get({ "publicKey": options })
.then(function (assertion) {
// Success
}).catch(function (err) {
// Error
});
Qiita:青いYubiKeyをFIDO2.0で光らせたい
https://qiita.com/gebo/items/33c48de1027f53f2712a
- 22.
navigator.
credentials.
get()
メンバ 説明
challenge チャレンジ- 乱数
登録後に返ってくるassertionの中にチャ
レンジに対する署名が入る。
署名を検証してassertionの有効性を確認
する。
allowCredentials.type public-key 固定
allowCredentials.id create()のときに取得したCredentialIDを
Base64で指定する。
Qiita:青いYubiKeyをFIDO2.0で光らせたい
https://qiita.com/gebo/items/33c48de1027f53f2712a
- 23.
- 24.
- 25.
- 26.
- 27.
- 28.
- 29.
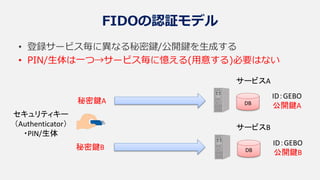
FIDOモデルの安全性
• 公開鍵が漏洩したら?
– 公開鍵でログインすることはできないので問題ない
•電子署名が漏洩したら?
– 毎回異なるチャレンジに対する署名なので問題ない
• 秘密鍵の管理は?
– 登録のたびに異なる秘密鍵を生成
– 秘密鍵はセキュリティキーの安全な領域で管理され、取り出すことができない
– 秘密鍵へのアクセスはPINまたは生体によって可能であり、署名作成の計算機能を利用するだけ
(アクセス=鍵を取り出すのではない)
– 一定回数のPIN誤りでロックされる
– これらの機能の実装を保証するFIDO Alliance認定ロゴ
- 30.
ところで CTAP
しーたっぷ /Client-To-Authenticator Protocol
• セキュリティキーとの通信プロトコル
• 仕様はFIDOAllianceが策定/公開
– Proposed Standard, January 30, 2019
– https://fidoalliance.org/specs/fido-v2.0-ps-20190130/fido-client-to-
authenticator-protocol-v2.0-ps-20190130.html
• HID/NFC/BLE
BioPassFIDO2
FEITIAN
MultiPass FIDO® Security Key
FEITIAN
- 31.
- 32.
- 33.
FIDOキーを使った試み on @Qiita
•WebAuthnぽいことができるWinデスクトップアプリ用ライブラリ
– WebAuthnModokiDesktopβ
– https://qiita.com/gebo/items/f6d3024f7e164ac0a195
• FIDO2セキュリティキーで電子署名をする試み
– https://qiita.com/gebo/items/0a08bc0e1aea6bc12c96
• FIDO2セキュリティキーでリモートデスクトップをする試み
– https://qiita.com/gebo/items/01b14279849c5fd399f7
- 34.
- 35.




![navigator.
credentials.
create()
var options = {
rp: {
id: location.host,
name: location.host,
},
user: {
id: new Uint8Array([129, 230, 232]),
name: "gebo",
displayName: "gebo",
},
challenge: window.crypto.getRandomValues(new Uint8Array(32)),
pubKeyCredParams: [
{
type: "public-key",
alg: -7, // cose_alg_ECDSA_w_SHA256,
},
],
}
// 認証にパスするとthenに入る
navigator.credentials.create({ "publicKey": options })
.then(function (attestation) {
// Success→attestationをVerifyし、中からCredentialID、公開鍵を取り出す
}).catch(function (err) {
// Error
});
Qiita:青いYubiKeyをFIDO2.0で光らせたい
https://qiita.com/gebo/items/33c48de1027f53f2712a](https://image.slidesharecdn.com/fidowebauthnctap-190613012120/85/FIDO-WebAuthn-CTAP-19-320.jpg)
![navigator.
credentials.
get()
let credentialId = create()で取得したものをセット;
var options = {
challenge: window.crypto.getRandomValues(new Uint8Array(32)),
allowCredentials: [
{
type: "public-key",
id: Base64toUint8Array(credentialId),
}
],
}
// 認証にパスするとthenに入る
navigator.credentials.get({ "publicKey": options })
.then(function (assertion) {
// Success
}).catch(function (err) {
// Error
});
Qiita:青いYubiKeyをFIDO2.0で光らせたい
https://qiita.com/gebo/items/33c48de1027f53f2712a](https://image.slidesharecdn.com/fidowebauthnctap-190613012120/85/FIDO-WebAuthn-CTAP-21-320.jpg)