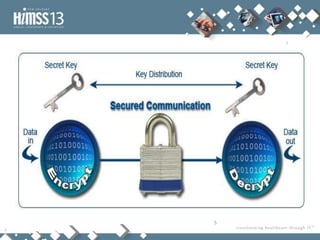
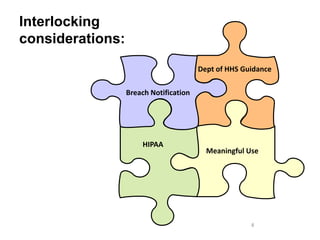
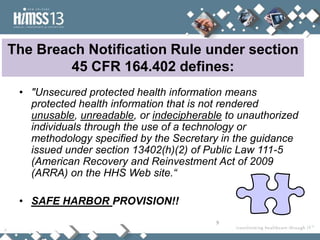
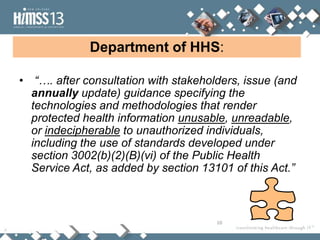
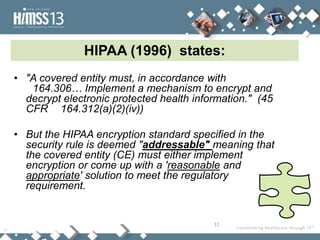
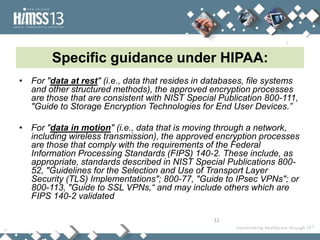
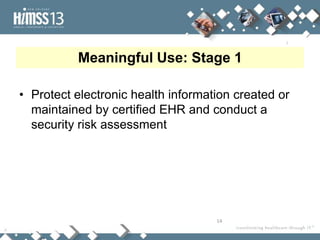
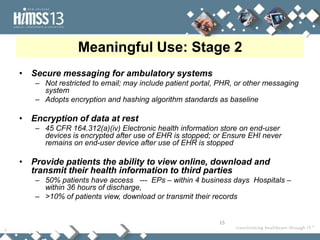
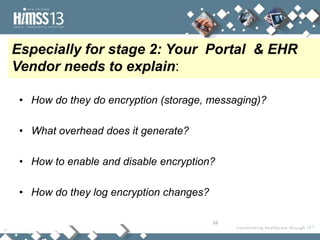
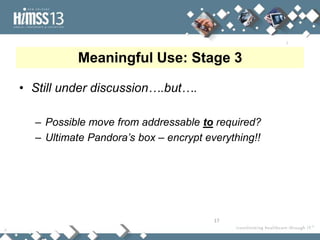
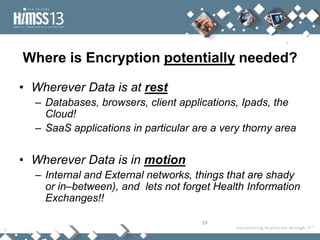
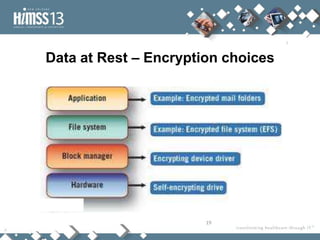
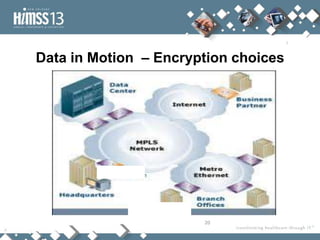
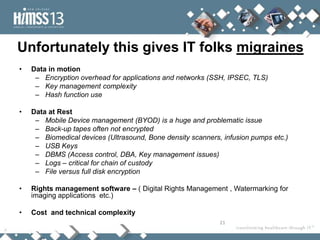
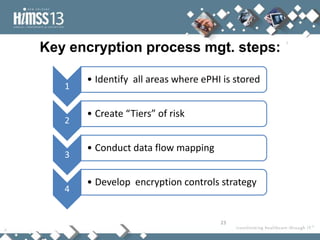
This document discusses the challenges of implementing encryption in healthcare organizations. It begins by defining encryption and outlining regulatory requirements around encryption from HIPAA, Breach Notification rules, and Meaningful Use standards. It then describes different types of encryption needed for data at rest and in motion. The document proposes a four step process for developing an encryption management strategy, including identifying where protected health information is stored, assessing risk levels, mapping data flows, and developing appropriate encryption controls. It emphasizes that encryption is not a panacea and recommends a risk-based approach that considers technical and cost factors.