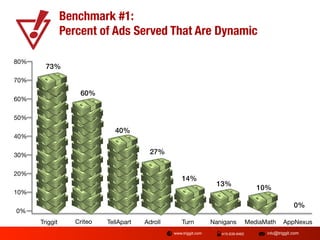
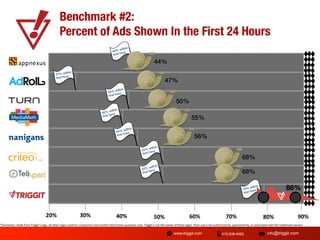
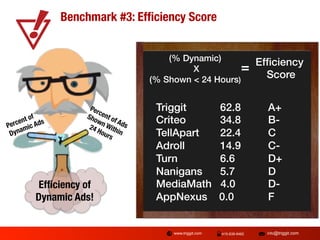
The document provides benchmarks for retargeting vendors, emphasizing the importance of dynamic ads and timely ad delivery. It shares data from over 100 advertisers, showing percentages of dynamic ads and those shown within 24 hours. The findings present a performance ranking of various vendors based on efficiency scores derived from dynamic ad metrics.