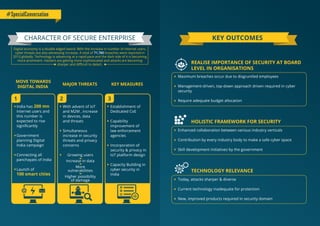
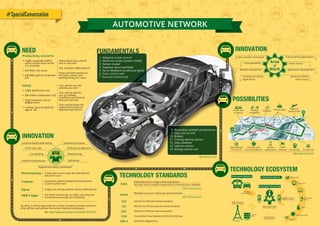
The 9th Nasscom-DSCI Annual Information Security Summit (AISS) held in December 2014 focused on strengthening perspectives on cyber security and privacy, bringing together key stakeholders for discussions on diverse issues in the field. The report outlines the challenges and advancements in cyber security, highlighting innovations such as the DSCI Certified Privacy Professional certification and the DSCI Innovation Box. Key insights from industry experts reveal the need for improved collaboration, resilience against cyber threats, and the importance of data security in building brand trust.