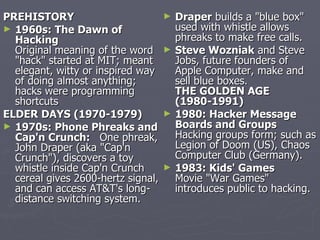
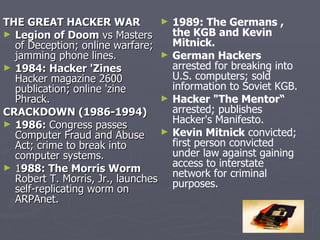
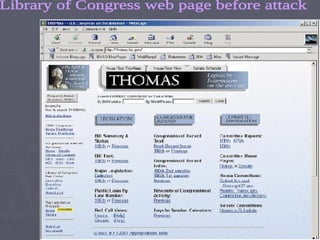
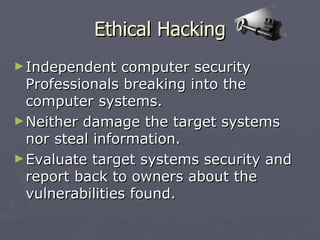
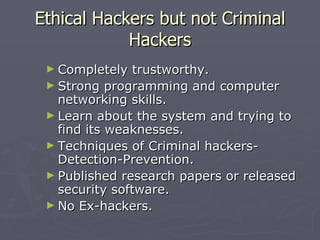
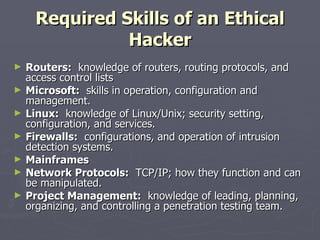
The document discusses the history and evolution of hacking from the 1960s to present day. It outlines key events such as the development of the "blue box" phone hack, formation of early hacker groups, and passage of anti-hacking laws. The document then defines ethical hacking as independent security professionals who evaluate systems for vulnerabilities without causing damage or stealing information. Ethical hackers require strong skills across various operating systems and protocols to thoroughly test systems from different attack perspectives.