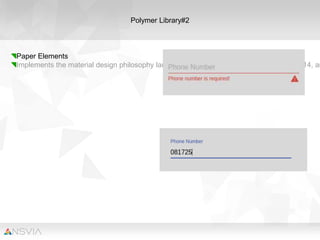
Polymer is a library that allows developers to build interfaces using Material Design. It reduces boilerplate code and provides core elements and paper elements to implement Material Design specifications. Polymer elements are built with web standards like HTML and CSS and allow developers to create complex single-page applications. Examples of apps built with Polymer include FoodTrack, a food truck locator, and Ele.io, a code editor for sharing Polymer elements.