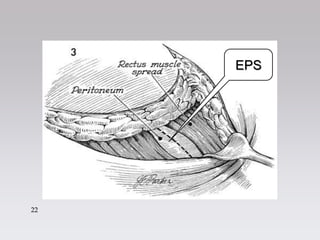
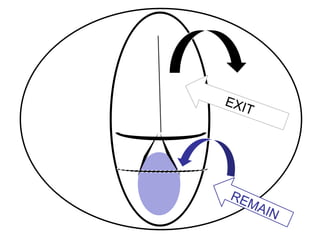
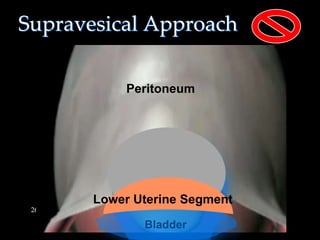
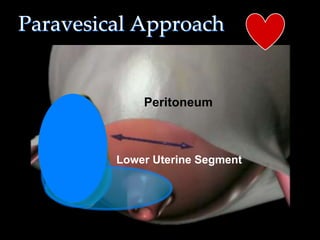
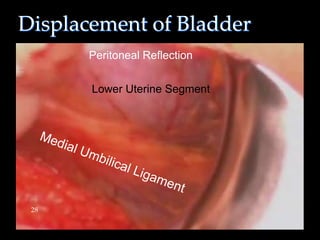
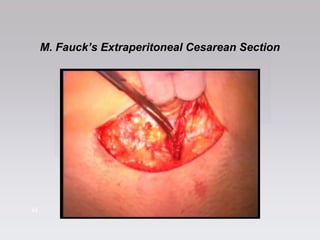
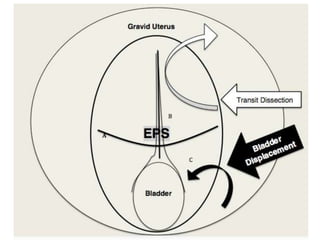
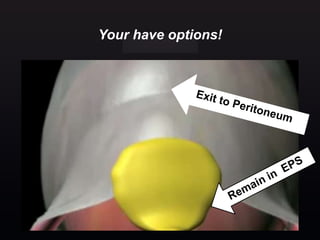
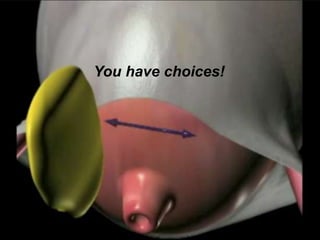
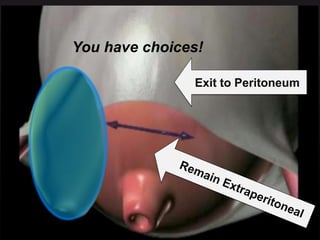
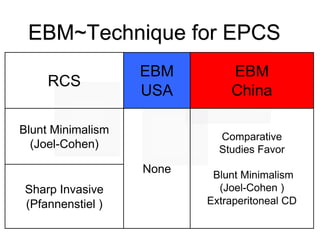
1) The document describes the operative technique for an extraperitoneal cesarean section.
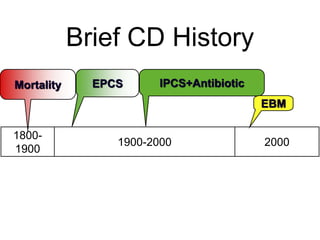
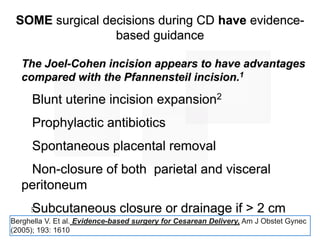
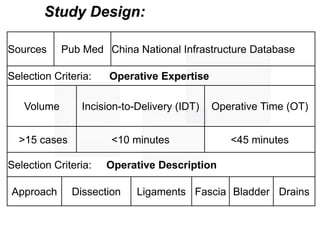
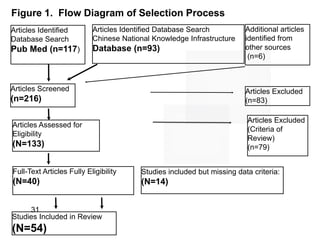
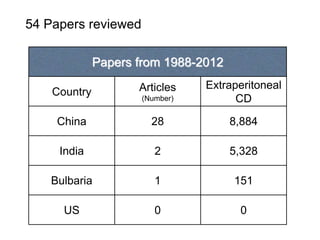
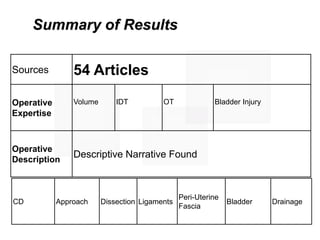
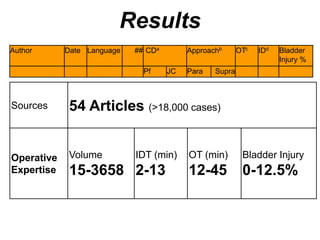
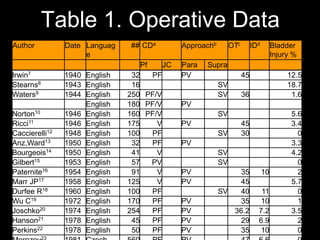
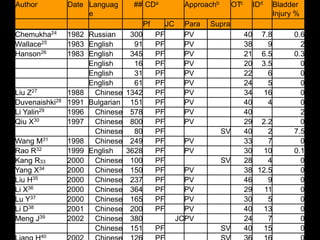
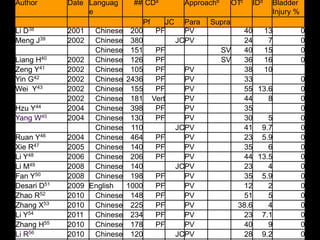
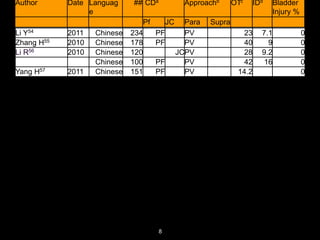
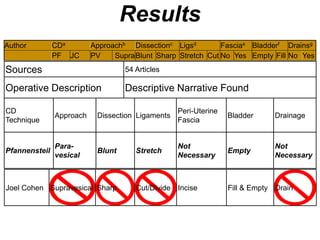
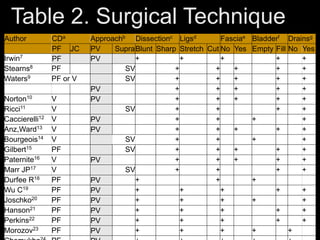
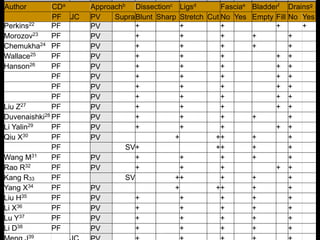
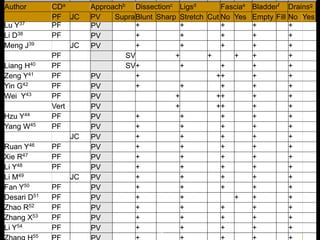
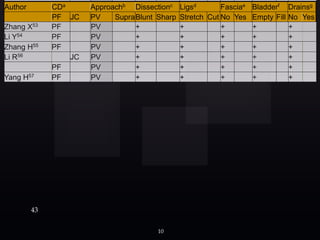
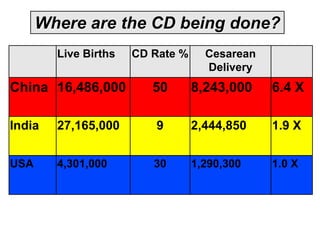
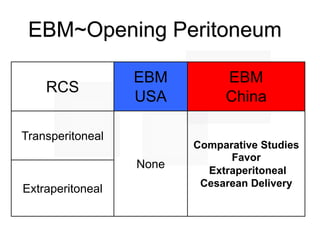
2) A review of over 54 studies from 1940-2012 including over 18,000 cesarean sections found that the extraperitoneal approach was commonly used with a Pfannensteil or Joel-Cohen incision.
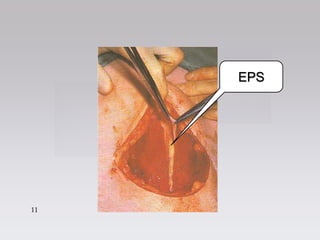
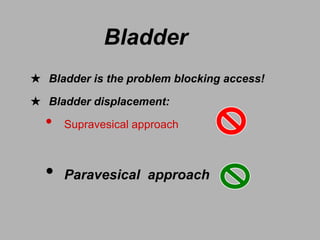
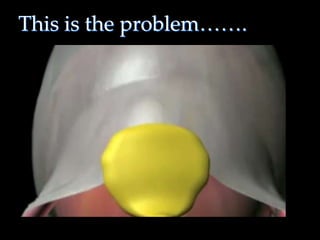
3) The technique typically involves blunt dissection of the bladder, ligation of vessels without cutting, and no need to empty or drain the bladder.