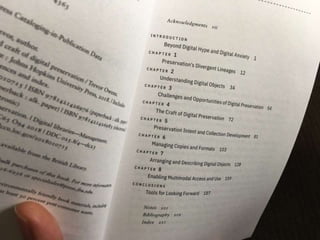
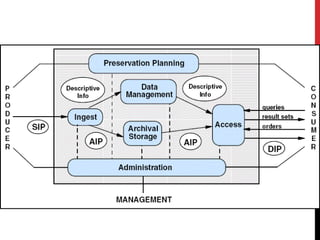
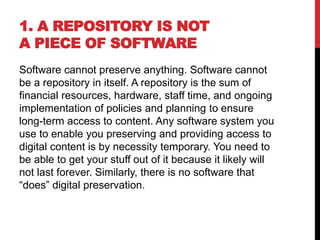
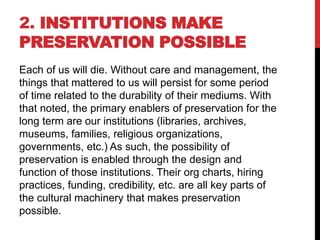
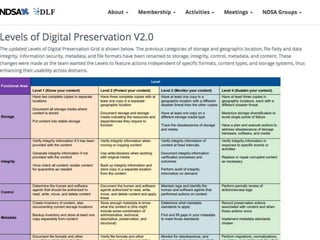
The document discusses the crucial elements of digital preservation, emphasizing that it involves ensuring enduring access to digital content through institutional support, ongoing work, and risk mitigation. It outlines 16 axioms of digital preservation, highlighting the complexities of digital objects and the need for well-structured approaches to curation. It also suggests practical steps to initiate effective digital preservation practices, urging organizations to prioritize actionable tasks over theoretical considerations.