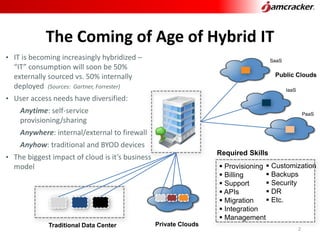
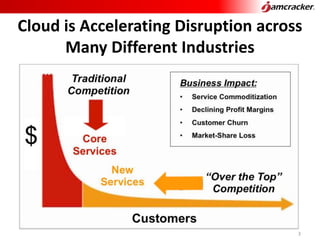
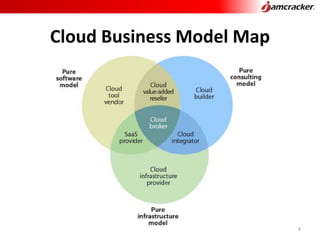
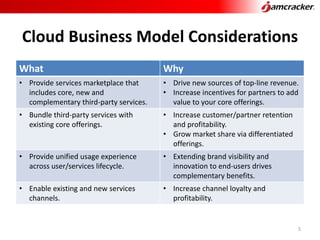
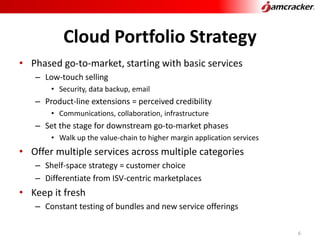
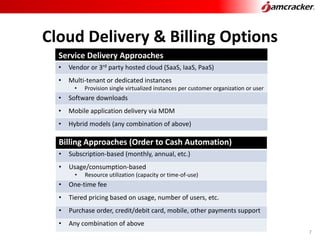
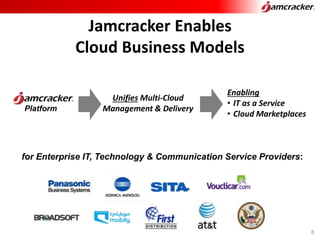
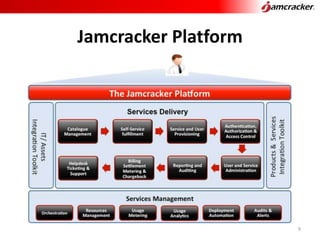
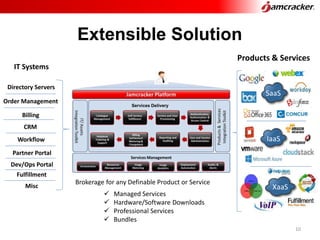
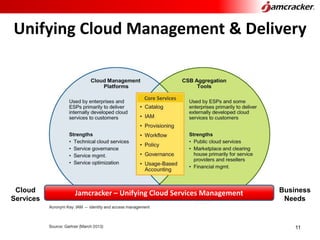
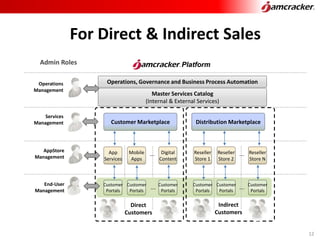
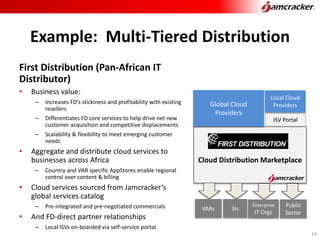
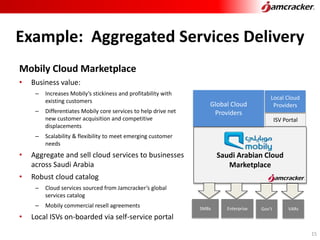
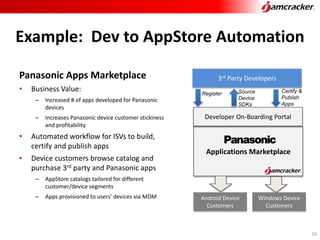
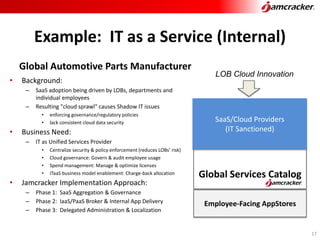
Jamcracker, Inc. provides a cloud commerce platform enabling hybrid IT solutions that support diverse user access and various business models. The platform facilitates 3rd party service brokerage, aggregation, and distribution across sectors, helping organizations adopt cloud services while managing governance and billing structures. Key features include a unified management system and tiered marketplaces for tailored service delivery to enhance profitability and customer retention.