This document discusses embedded C programming. It defines embedded C and compares it to conventional C and assembly programming. Key differences between embedded C and other languages include embedded C being microcontroller dependent rather than processor dependent, more portable code, and easier readability. Embedded C allows direct hardware access and optimization for limited embedded systems. The document outlines rules for developing optimized embedded C programs, including scope of variable declarations, function parameters, and register usage. Cross-compilers are used to compile embedded C code into executable hex files for microcontrollers.
![CREATING EXECUTABLE PROGRAMS, TEMPORARY
FILES,INCLUDE FILES AND LIBRARY FILES.
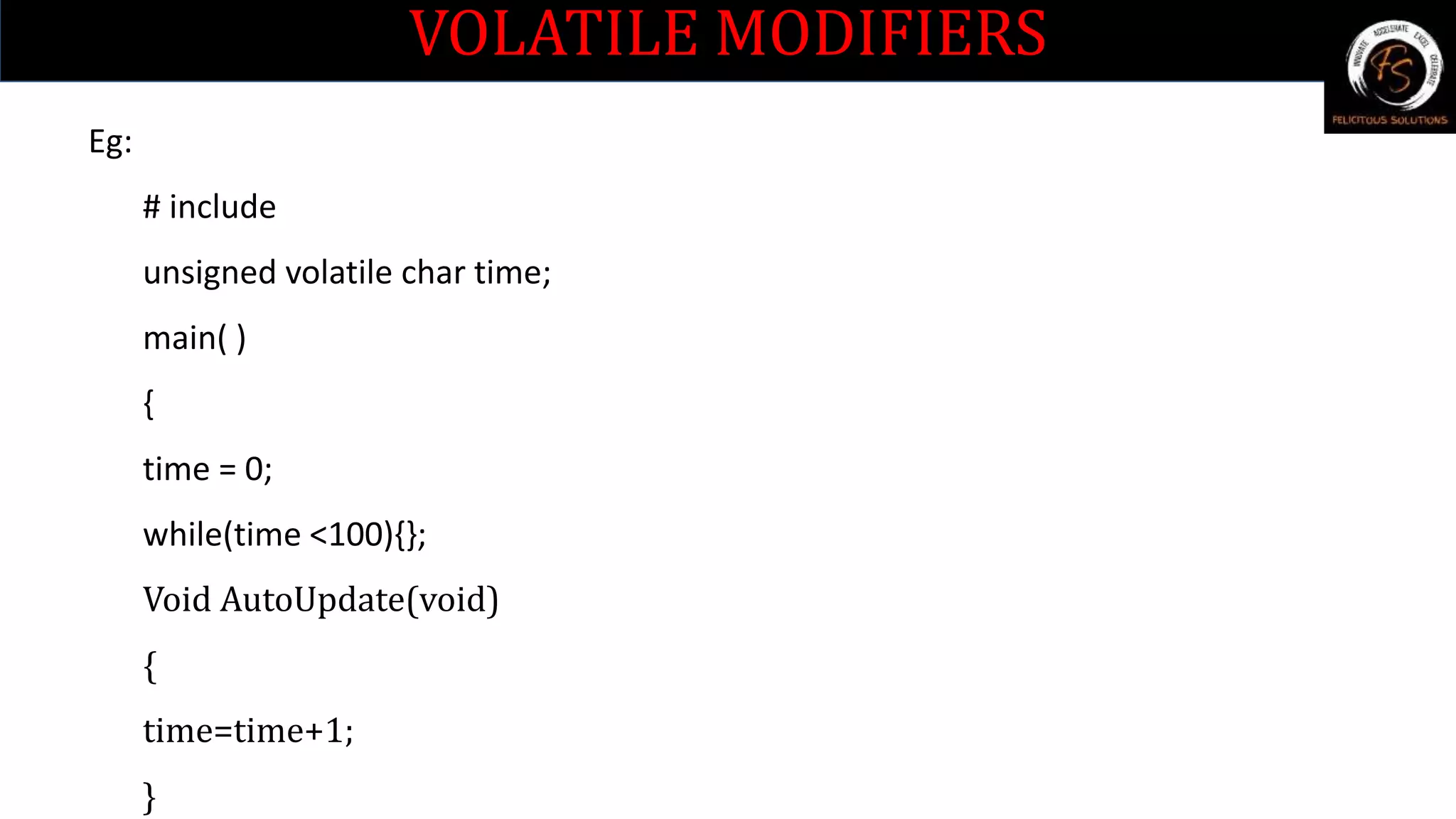
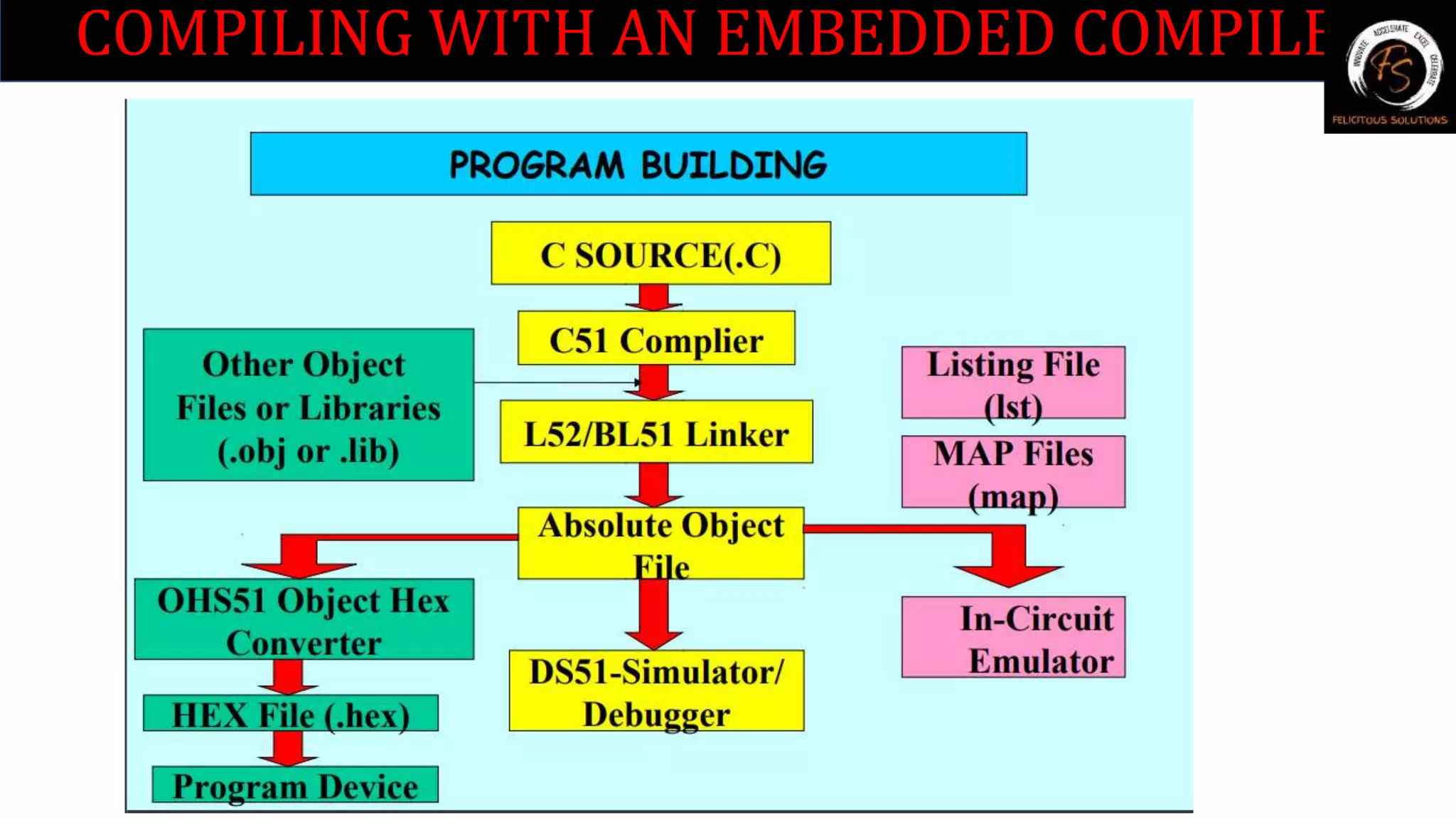
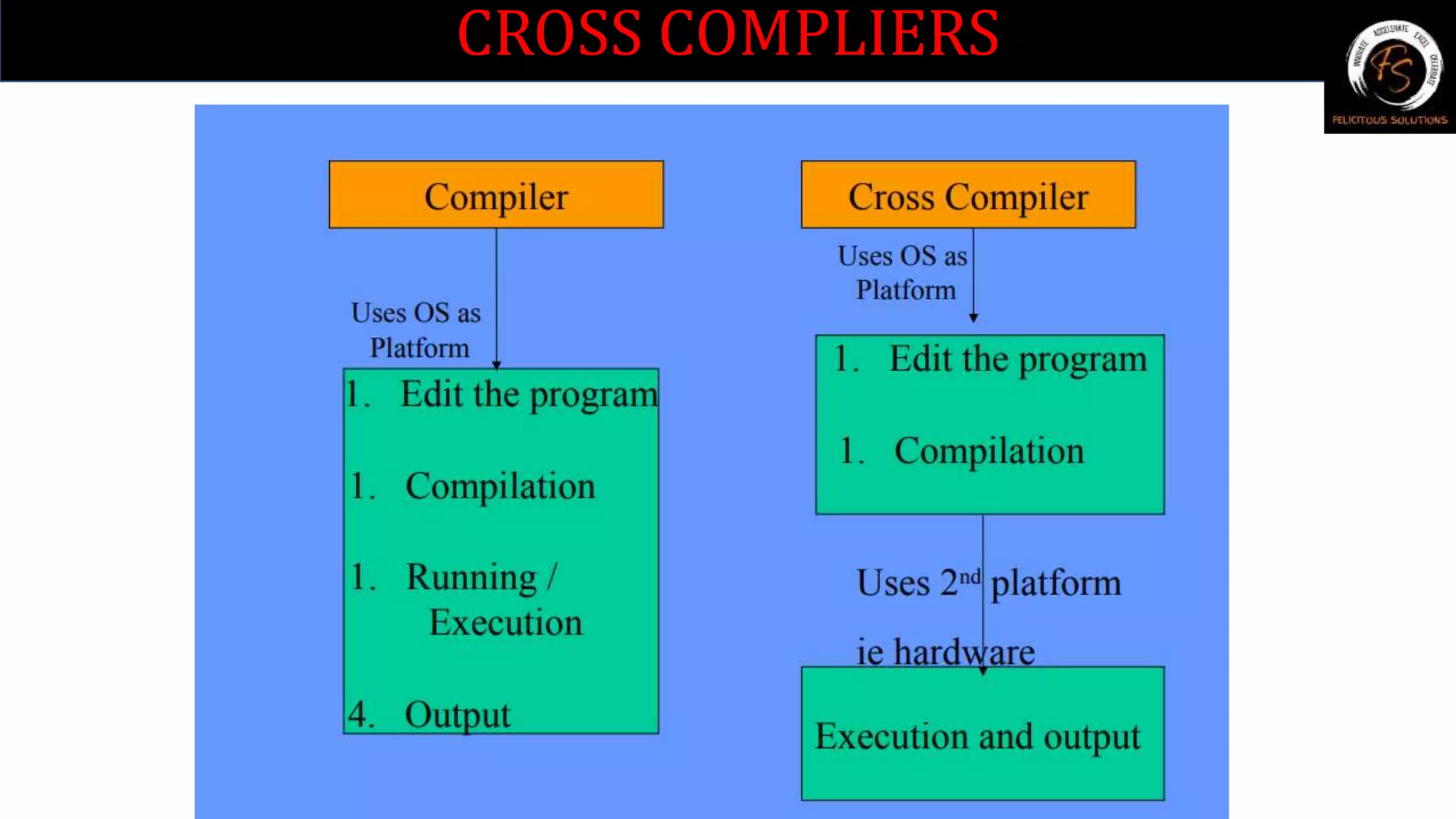
The C source code is compiled using c51 compiler by invoking C51.exe.
The command line is C51 source files [directives….] where Source files: is
the name of the source program to be compiled. Directive: are directives
to the compiler to control the function of the compiler
The source code is usually developed in C or assembly which are
executable programs.
C51 compiler generates a series of output files during compilation.
Basename.lst : (list file) these contain formatted source text with any
errors detected by the compiler .](https://image.slidesharecdn.com/embeddedc-220723071111-21996695/75/Embedded-C-pptx-25-2048.jpg)
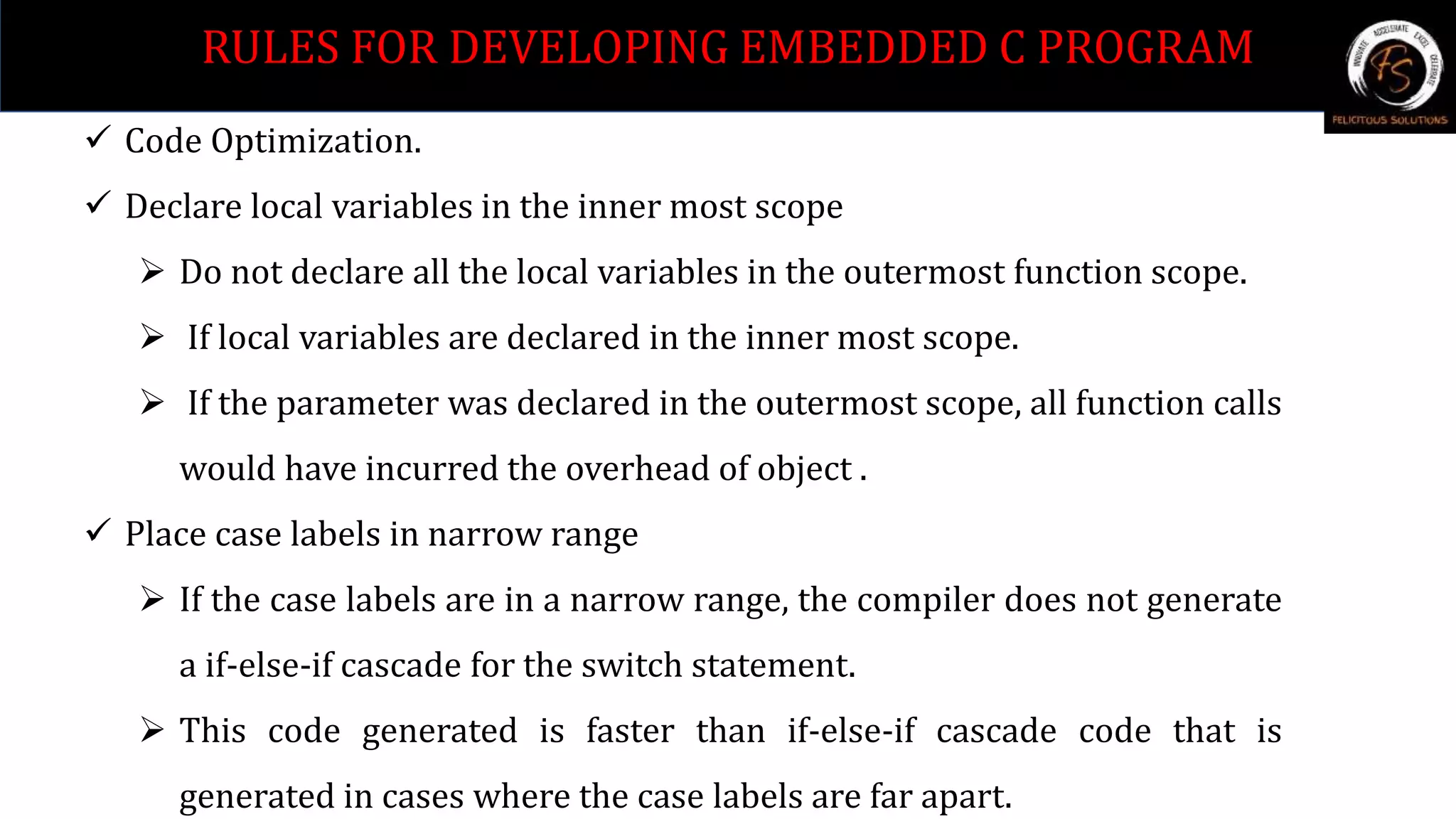
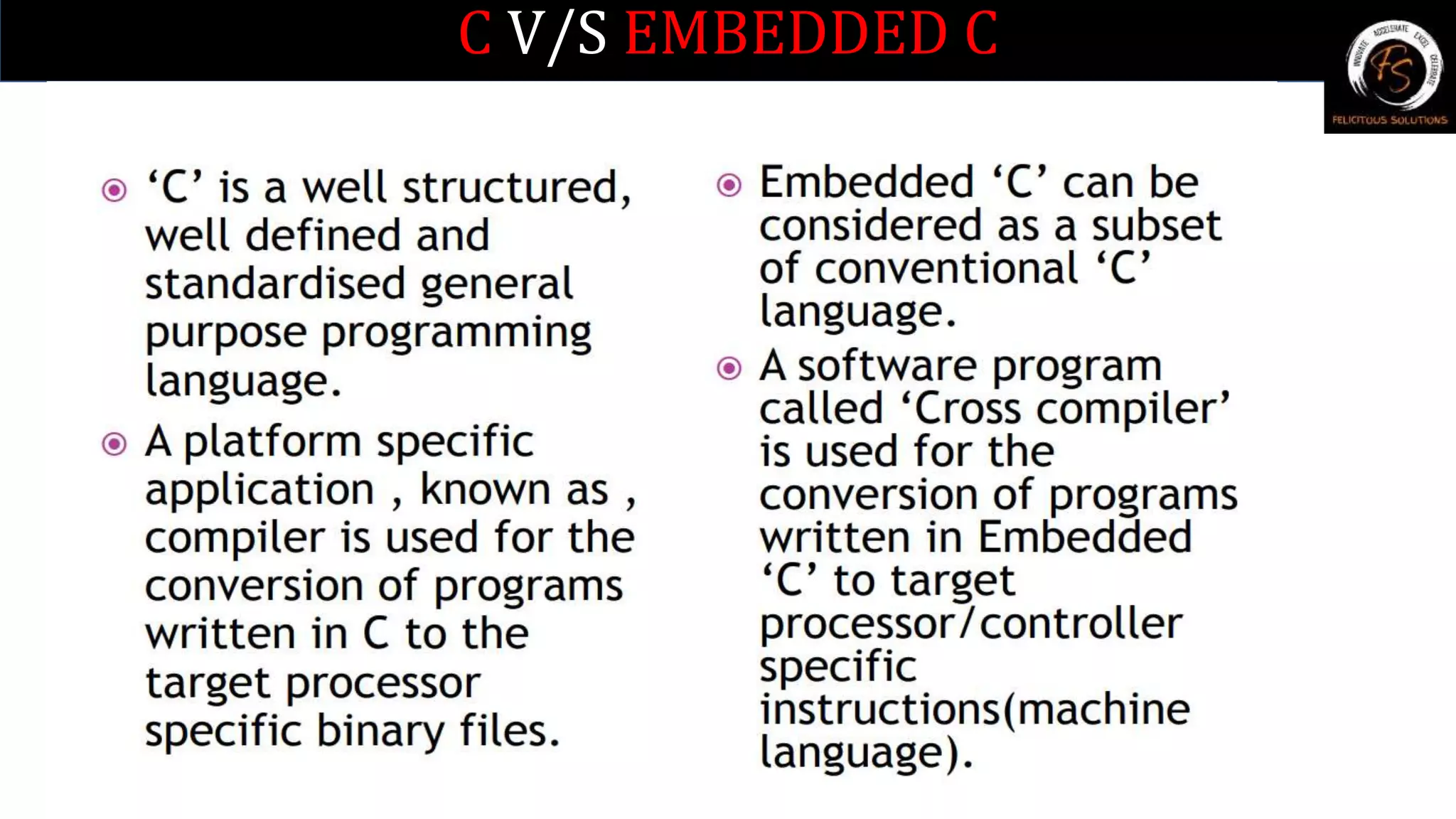
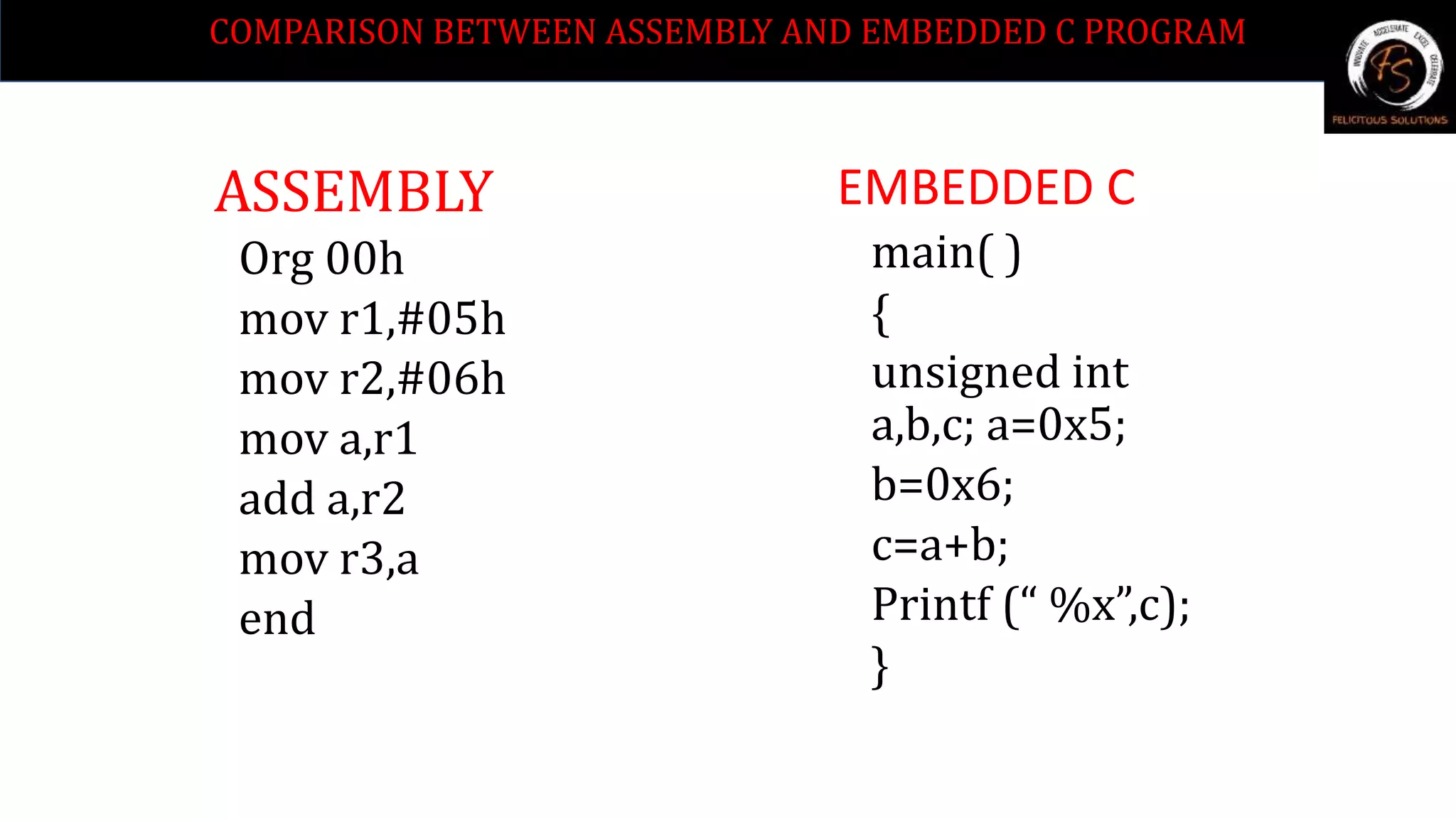
![ SFRS & Registers
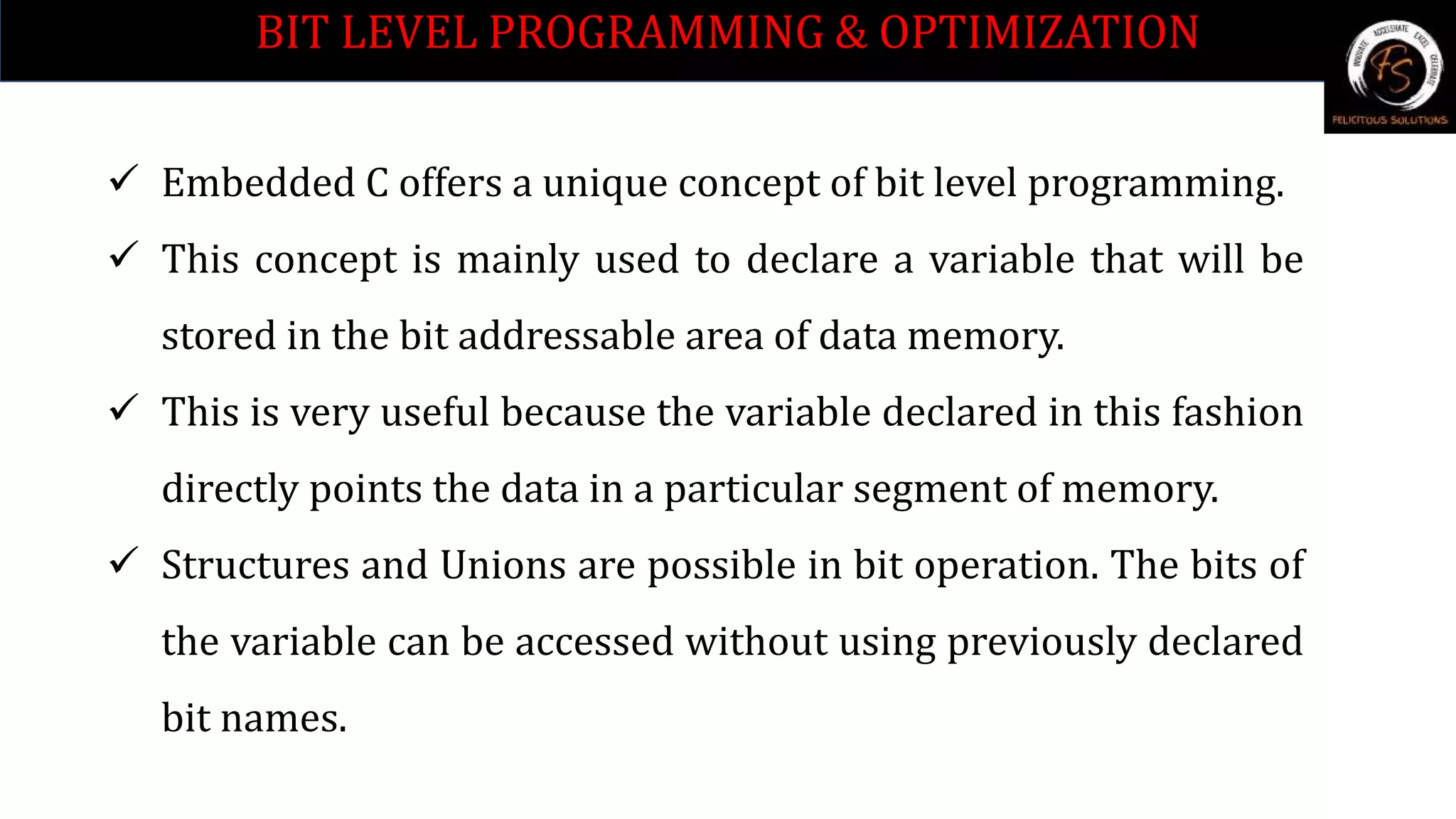
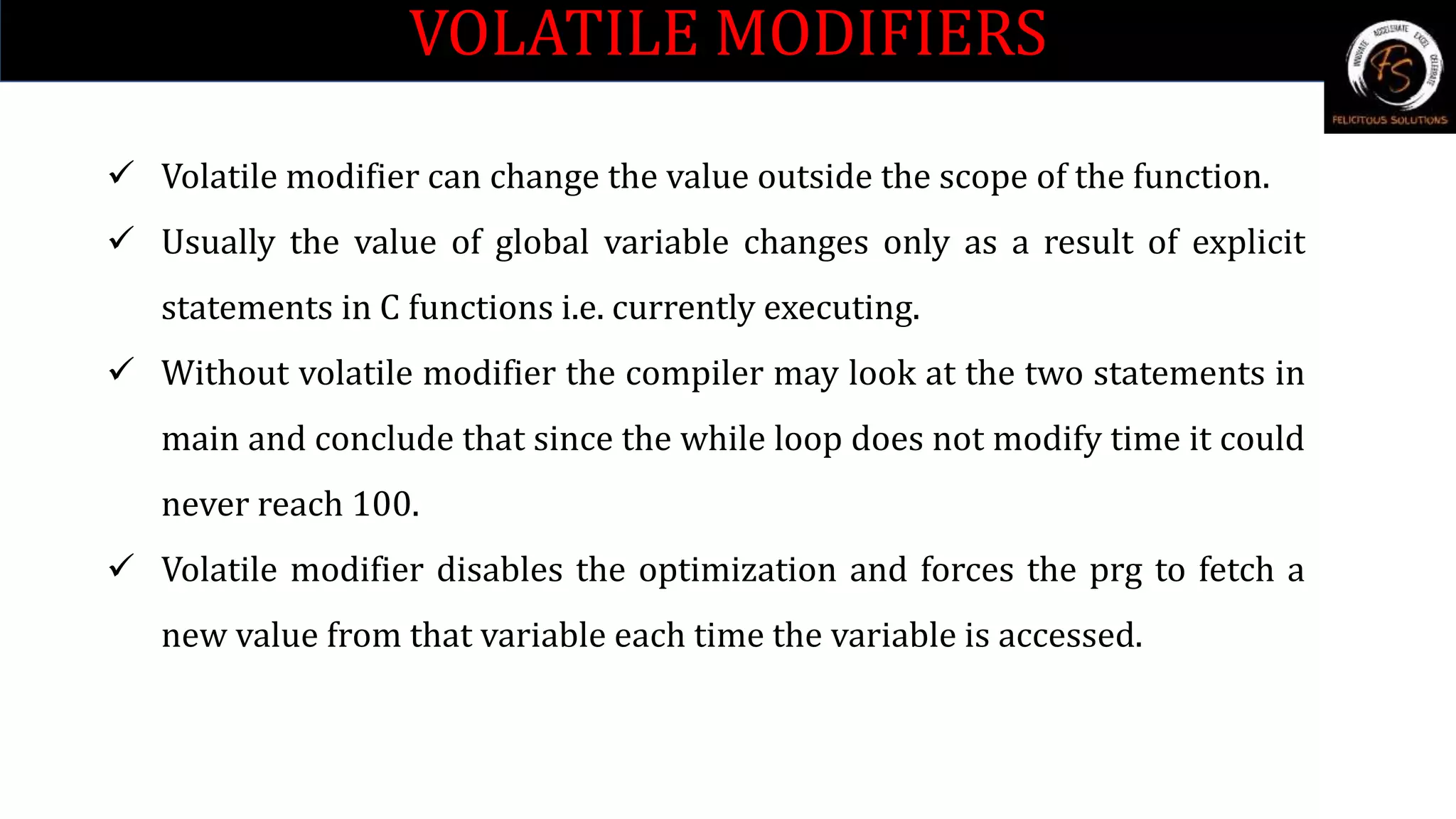
1. Use All the SFR’s in capital letters only.
2. Reduce the warnings in the program.
3. Make use of MACRO definitions in the program.
4. Always define the variables in the code memory by using the keyword
code in declaration.
5. Eg unsigned int code a[] = { };
6. Always define as unsigned type of declaration.
7. Make use of sbit definition for single bit declaration.
8. Eg sbit rs = P3^6;
RULES FOR DEVELOPING EMBEDDED C PROGRAM](https://image.slidesharecdn.com/embeddedc-220723071111-21996695/75/Embedded-C-pptx-32-2048.jpg)