Dp5
•
0 likes•395 views
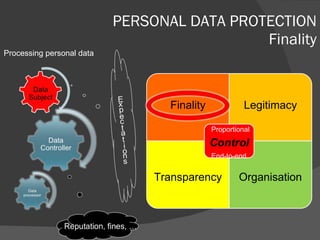
Data protection regulation is to a great extent purpose bound. Finality is the first pillar of the regulation.
Report
Share
Report
Share
Recommended
Exploring Data Privacy - SQL Saturday Louisville 2011

This is the slide deck from the presentation given at SQL Saturday event in Louisville, October 2011. A modified version of this presentation was given at the Indianapolis SQL Saturday in May 2011.
Data Breach In The Hospitality Industry

This document discusses how to protect organizations from data breaches. It outlines the importance of having a data breach response plan and taking proactive steps to prevent breaches from occurring. These include inventorying personal information, assessing breach risks, encrypting computers, conducting security assessments, and purchasing cyber insurance. The document notes that each personal record compromised in a breach costs about $201 on average and that many security leaders lose their jobs if they experience a public breach without having a documented response plan in place.
Privacy Discusssion GM667 Saint Mary's University of MN

This document discusses privacy and information privacy. It outlines four dimensions of privacy including privacy of the person, personal behavior, personal communications, and personal data. Information privacy is defined as a combination of communications and data privacy that allows individuals control over collection, distribution, use, solicitation, and storage of private information. Many current privacy laws and guidelines are based on eight principles developed by the OECD in 1980 around limiting collection and ensuring security, quality, transparency and individual participation regarding personal data.
Duncan hine input3_irm_and_outsourcing

The document discusses several issues related to information security risk management with data aggregation in the cloud. It notes that more data is being collected and combined from various sources, increasing privacy and security risks. As data sets grow extremely large, the potential damage from loss or misuse also increases greatly. Proper privacy and security controls need to be applied to the cloud to manage these emerging risks from large-scale data aggregation. Traditional risk management practices can still apply but need to be adapted to the new threat landscape.
5 Things You Must Do To Secure Sensitive Data 

This document discusses data democratization and the importance of managing metadata and privacy for data assets. It describes how most organizations have untapped data that can fuel innovation if managed properly. Effective data management involves embracing privacy by design, governing data using metadata, controlling access through policy, de-identifying sensitive data, and auditing all data usage. The PHEMI system is presented as a way to manage massive datasets safely and securely by tracing all data back to its origin, using rich access controls, and allowing different versions of data to be shown based on user authorization.
Identity Intelligence: From Reactionary Support to Sustained Enabler

This classified briefing discusses the evolution of the Department of Defense's identity intelligence capabilities from reactive support to sustained enablers. It provides an overview of past and present biometric capabilities fielded by DoD, including mobile identification technology, portable enrollment stations, and authoritative biometric databases. It also discusses the Identity Intelligence Project Office's role in defining policy, establishing data standards, and fostering information sharing to harmonize DoD identity intelligence requirements and integration. The briefing concludes by examining potential future directions, such as increased use of biometrics at borders and emphasis on fully illuminating identities through associated attributes.
GDPR – Data Portability

This document discusses individual rights under the GDPR, including the right to be informed, right to access data, right to rectification, right to erasure, right to restrict processing, right to object, and right to data portability. It provides details on the elements of data portability, specifying that it applies to personal data provided by the individual based on consent or contract, must be in a structured and machine readable format, excludes inferred data, and considers third party rights during transfer between controllers. The document also compares the process for an access request versus a data portability request, noting they have similar timelines and identification requirements but data portability applies only to automated personal data.
HCMUT IMP Computer Science 20 - E-Government from the view of Privacy

E-Government involves government agencies using technology like the internet to provide services to citizens. However, this raises privacy concerns as personal data from different government records and databases can be combined to create detailed profiles of individuals. The document discusses definitions of e-government and privacy, privacy laws in the US and Vietnam, and technical solutions used to preserve privacy in e-government like data perturbation and anonymization. It also summarizes a case study where medical records from Massachusetts were re-identified by combining them with voter records to find the medical information of the Governor at the time.
Recommended
Exploring Data Privacy - SQL Saturday Louisville 2011

This is the slide deck from the presentation given at SQL Saturday event in Louisville, October 2011. A modified version of this presentation was given at the Indianapolis SQL Saturday in May 2011.
Data Breach In The Hospitality Industry

This document discusses how to protect organizations from data breaches. It outlines the importance of having a data breach response plan and taking proactive steps to prevent breaches from occurring. These include inventorying personal information, assessing breach risks, encrypting computers, conducting security assessments, and purchasing cyber insurance. The document notes that each personal record compromised in a breach costs about $201 on average and that many security leaders lose their jobs if they experience a public breach without having a documented response plan in place.
Privacy Discusssion GM667 Saint Mary's University of MN

This document discusses privacy and information privacy. It outlines four dimensions of privacy including privacy of the person, personal behavior, personal communications, and personal data. Information privacy is defined as a combination of communications and data privacy that allows individuals control over collection, distribution, use, solicitation, and storage of private information. Many current privacy laws and guidelines are based on eight principles developed by the OECD in 1980 around limiting collection and ensuring security, quality, transparency and individual participation regarding personal data.
Duncan hine input3_irm_and_outsourcing

The document discusses several issues related to information security risk management with data aggregation in the cloud. It notes that more data is being collected and combined from various sources, increasing privacy and security risks. As data sets grow extremely large, the potential damage from loss or misuse also increases greatly. Proper privacy and security controls need to be applied to the cloud to manage these emerging risks from large-scale data aggregation. Traditional risk management practices can still apply but need to be adapted to the new threat landscape.
5 Things You Must Do To Secure Sensitive Data 

This document discusses data democratization and the importance of managing metadata and privacy for data assets. It describes how most organizations have untapped data that can fuel innovation if managed properly. Effective data management involves embracing privacy by design, governing data using metadata, controlling access through policy, de-identifying sensitive data, and auditing all data usage. The PHEMI system is presented as a way to manage massive datasets safely and securely by tracing all data back to its origin, using rich access controls, and allowing different versions of data to be shown based on user authorization.
Identity Intelligence: From Reactionary Support to Sustained Enabler

This classified briefing discusses the evolution of the Department of Defense's identity intelligence capabilities from reactive support to sustained enablers. It provides an overview of past and present biometric capabilities fielded by DoD, including mobile identification technology, portable enrollment stations, and authoritative biometric databases. It also discusses the Identity Intelligence Project Office's role in defining policy, establishing data standards, and fostering information sharing to harmonize DoD identity intelligence requirements and integration. The briefing concludes by examining potential future directions, such as increased use of biometrics at borders and emphasis on fully illuminating identities through associated attributes.
GDPR – Data Portability

This document discusses individual rights under the GDPR, including the right to be informed, right to access data, right to rectification, right to erasure, right to restrict processing, right to object, and right to data portability. It provides details on the elements of data portability, specifying that it applies to personal data provided by the individual based on consent or contract, must be in a structured and machine readable format, excludes inferred data, and considers third party rights during transfer between controllers. The document also compares the process for an access request versus a data portability request, noting they have similar timelines and identification requirements but data portability applies only to automated personal data.
HCMUT IMP Computer Science 20 - E-Government from the view of Privacy

E-Government involves government agencies using technology like the internet to provide services to citizens. However, this raises privacy concerns as personal data from different government records and databases can be combined to create detailed profiles of individuals. The document discusses definitions of e-government and privacy, privacy laws in the US and Vietnam, and technical solutions used to preserve privacy in e-government like data perturbation and anonymization. It also summarizes a case study where medical records from Massachusetts were re-identified by combining them with voter records to find the medical information of the Governor at the time.
Dp4

The document discusses key concepts regarding personal data protection including:
1) There are three main actors - data subjects, controllers who determine the purpose and means of processing personal data, and processors who process personal data on behalf of controllers.
2) Personal data refers to any information related to an identified or identifiable natural person. One person can have multiple data sets for different purposes or capacities.
3) Outsourcing of data processing to other bodies is allowed but controllers are responsible for ensuring security and confidentiality of personal data when transferred. The roles of different actors in cross-border data transfers are also discussed.
Dp3

The document discusses personal data protection, including the risks and advantages of processing personal data. It notes that privacy compliance can provide market advantages for data processing service providers. Various sanctions and damages are also mentioned relating to directly or indirectly not complying with data protection regulations, including criminal sanctions, administrative sanctions, civil sanctions, fines, and prohibiting further data processing. The document also briefly discusses the impact to reputation if data protection is not followed.
Dp2

Very broad scope of personal data protection applies to any information relating to an identified or identifiable natural person. Personal data can be directly or indirectly identifiable and includes information such as identification numbers, physical characteristics, communication data, geographical data, personal relationships, interests, and more. The processing of personal data involves any automated or manual operations performed on personal data according to specific criteria that permits easy access to the data, such as collection, recording, organization, storage, retrieval, disclosure, and deletion.
Can social media make or break your company?

The document discusses how social media can make or break a company or brand. It notes that social media is characterized by collective participation, transparency, persistence, and independence. It also identifies key players that engage on social media, including regulators, company management and users, customers, and pressure groups. The document uses examples like Nestle to illustrate how social media crises can occur and must be responded to honestly, correctly, and proportionately. It emphasizes that social media allows for two-way conversations rather than one-way communication and that perception is important. Overall, the document examines how social media needs to be integrated into companies and how managers should enter and participate in social media arenas.
Apertor california and-lv_strip

The report includes and analysis of the California economy and California's economic impact on the Las Vegas Strip.
Apertor chinese lodging-industry_growth

This document provides an overview and analysis of the growth of the Chinese lodging industry. Some of the key points made in the document include:
- RevPAR growth in Asia Pacific and China significantly outpaced growth in Europe and the US in 2010, with China seeing 37% year-over-year RevPAR growth.
- Major hotel companies like IHG, Marriott, and Starwood remain positive about growth prospects in Asia and China in the coming years.
- The Chinese lodging market is dominated by independent hotels and guesthouses but is seeing rapid growth of branded economy and upper-scale hotels.
- The economy hotel segment in particular has grown dramatically, led by several Chinese operators, and
Apertor las vegas locals casino market 1a

The document summarizes the outlook for the Las Vegas locals casino market, noting that:
1) Recent data and evidence suggests that optimism for a near-term recovery in the locals market is premature, as the market highly depends on the local economy which faces challenges from high unemployment, a weak housing market, and lack of job and population growth.
2) Core industry metrics like daily slot volume and win per slot have plummeted since late 2008 as the recession hit the local gaming and overall economy hard.
3) A recovery in the locals market will likely be slow and protracted given current negative trends and lack of visibility of improvements in the local economic factors that drive the market.
Gregg Carlson report sample Las Vegas Strip Ecosystem without pics

The Las Vegas Strip hotel market is facing significant changes with new hotel projects opening over the next few years, increasing supply by 11%. This will likely lead to shifts in the market shares held by different hotels. Top-tier hotels like Wynn may capture more business from mid-tier hotels, creating a "waterfall effect" down the chain. Lower-tier hotels risk negative returns and cash flows as their market share declines. The geography of development also matters - the north Strip faces stalled projects and weaker performance. The future remains unclear without stronger visitor growth to match the new supply.
Costco financial analysis may 2008 slideshare

The document provides an analysis of Costco Wholesale's recent performance and outlook. It summarizes that Costco reported strong same-store sales growth of 7-8% during the first four months of 2008 despite challenging economic conditions. Channel checks found Costco's local traffic held up well while other retailers saw weakness. The document maintains a positive long-term view of Costco given its consistent growth, strong membership renewal rates, and expansion plans to double its store count over 10 years. In the near term, the stock appears fully valued based on earnings estimates.
Privacy and care robots

Increasing use of robots in domestic and care situations - eg in hospital, to help the aged at home, etc - combined with the likelihood that robots may surveille and record both the humans they aid and the general environment - leads to a need to think about the privacy implications of use of robots as carers or caring aids.
Is More Data Always Better? The Legal Risks of Data Collection, Storage and U...

This document discusses the legal risks of data collection, storage, and use for marketing purposes. It notes that while data provides benefits, over-collection can pose privacy and legal issues. The document examines who collects data, what types of data are collected, why it's collected, and principles that govern collection. It also provides tips on minimizing risk, such as having a data governance plan, collecting only what is necessary, and being prepared in the event of a security breach. The overall message is that while data is valuable for business, collectors must respect privacy and limit their practices to authorized uses.
Polinter09

This document discusses the history and evolution of government surveillance programs in the United States from the 1990s through the 2000s. It describes programs like the Total Information Awareness Program (TIA) from 2002 that aimed to develop data mining techniques for counterterrorism but raised privacy concerns. It also discusses legal debates around warrantless wiretapping programs authorized after 9/11 under acts like the Patriot Act and their reauthorizations under Presidents Bush and Obama. Key issues included the scope of surveillance, oversight of programs, and balancing security with civil liberties and privacy.
Privacy and data protection primer - City of Portland

This is a Primer on Privacy and Data Protection presented at the Portland, Oregon City council on September 25, 2018
CSMFO 2012 Data Privacy in Local Government

This document provides an overview of data privacy for governmental organizations. It discusses what data privacy is, the risks associated with it such as identity theft, and common laws around data privacy including California state laws. It recommends that organizations take an inventory of their data, develop privacy policies and training, and ensure proper system monitoring and controls. The document emphasizes being proactive on data privacy issues.
Data Mining: Privacy and Concerns

Data mining involves extracting and analyzing large amounts of data to find patterns. While it provides benefits to companies, some view it as an invasion of privacy. There is little regulation in the US on data mining. The government has broad powers to collect data under laws like the Patriot Act. Data breaches have compromised over 800 million records, revealing sensitive personal information. Retailers use data mining to target customers, while gamers mine data to learn about new game content. More regulation may be needed to protect personal privacy as data mining becomes more widespread.
Unit 6 Privacy and Data Protection 8 hr

The document discusses privacy and data protection. It defines privacy as an individual's ability to control how and when personal information is shared with others. It outlines several international agreements that establish privacy as a universal human right. The document also discusses the three dimensions of privacy - personal, territorial, and informational - and basic privacy principles like transparency and purpose limitation.
Polinter09

This document summarizes the history and evolution of government surveillance and data collection programs related to counterterrorism efforts since the 1960s. It discusses early programs like COINTELPRO and the development of enabling technologies like databases, data mining, and facial recognition. It then outlines several post-9/11 US government programs aimed at identifying terrorists, the privacy and legal concerns they raised, and reasons for the cancellation of some programs.
General data protection

The document provides an overview of the General Data Protection Regulation (GDPR) which takes effect in May 2018. It defines personal data and special categories of personal data that require strict protection. GDPR places requirements on organizations that process personal data to protect privacy rights, ensure appropriate data use, and demonstrate compliance. It describes key data protection principles like lawfulness, purpose limitation, data minimization, accuracy, storage limitation, integrity and confidentiality, and accountability. The document outlines responsibilities of data controllers versus processors and the 12 steps for organizations to comply with GDPR.
Where In The World Is Your Sensitive Data?

Consumers rely on businesses to keep their personal information safe. Too few of those businesses are actively protecting that data. Here’s what’s gone wrong, and how businesses should be responding. Full blog here: http://bit.ly/1Jtzym5
All_you_need_to Know_About_the_Data_Privacy_Act.pdf

The document summarizes the key requirements for complying with the Philippines' Data Privacy Act of 2012. It outlines the structure and objectives of the law, as well as the obligations and penalties for personal information controllers and processors. The main compliance obligations include appointing a data protection officer, adhering to privacy principles when processing data, maintaining security of data, reporting breaches within 72 hours, and registering with the National Privacy Commission. Non-compliance could result in penalties such as fines and imprisonment.
Data protection guide

The Data Protection Act aims to protect individuals' personal data and privacy. It applies to most voluntary organizations that collect personal data. While the Act must be followed as it is law, there is flexibility in how organizations comply. The top priorities of the Act are preventing harm to individuals and respecting individuals. It focuses on protecting people, not just data itself. Personal data is any information relating to a living individual that identifies them. Most information that organizations collect about people, whether electronically or physically, will fall under the definition of personal data.
More Related Content
Viewers also liked
Dp4

The document discusses key concepts regarding personal data protection including:
1) There are three main actors - data subjects, controllers who determine the purpose and means of processing personal data, and processors who process personal data on behalf of controllers.
2) Personal data refers to any information related to an identified or identifiable natural person. One person can have multiple data sets for different purposes or capacities.
3) Outsourcing of data processing to other bodies is allowed but controllers are responsible for ensuring security and confidentiality of personal data when transferred. The roles of different actors in cross-border data transfers are also discussed.
Dp3

The document discusses personal data protection, including the risks and advantages of processing personal data. It notes that privacy compliance can provide market advantages for data processing service providers. Various sanctions and damages are also mentioned relating to directly or indirectly not complying with data protection regulations, including criminal sanctions, administrative sanctions, civil sanctions, fines, and prohibiting further data processing. The document also briefly discusses the impact to reputation if data protection is not followed.
Dp2

Very broad scope of personal data protection applies to any information relating to an identified or identifiable natural person. Personal data can be directly or indirectly identifiable and includes information such as identification numbers, physical characteristics, communication data, geographical data, personal relationships, interests, and more. The processing of personal data involves any automated or manual operations performed on personal data according to specific criteria that permits easy access to the data, such as collection, recording, organization, storage, retrieval, disclosure, and deletion.
Can social media make or break your company?

The document discusses how social media can make or break a company or brand. It notes that social media is characterized by collective participation, transparency, persistence, and independence. It also identifies key players that engage on social media, including regulators, company management and users, customers, and pressure groups. The document uses examples like Nestle to illustrate how social media crises can occur and must be responded to honestly, correctly, and proportionately. It emphasizes that social media allows for two-way conversations rather than one-way communication and that perception is important. Overall, the document examines how social media needs to be integrated into companies and how managers should enter and participate in social media arenas.
Apertor california and-lv_strip

The report includes and analysis of the California economy and California's economic impact on the Las Vegas Strip.
Apertor chinese lodging-industry_growth

This document provides an overview and analysis of the growth of the Chinese lodging industry. Some of the key points made in the document include:
- RevPAR growth in Asia Pacific and China significantly outpaced growth in Europe and the US in 2010, with China seeing 37% year-over-year RevPAR growth.
- Major hotel companies like IHG, Marriott, and Starwood remain positive about growth prospects in Asia and China in the coming years.
- The Chinese lodging market is dominated by independent hotels and guesthouses but is seeing rapid growth of branded economy and upper-scale hotels.
- The economy hotel segment in particular has grown dramatically, led by several Chinese operators, and
Apertor las vegas locals casino market 1a

The document summarizes the outlook for the Las Vegas locals casino market, noting that:
1) Recent data and evidence suggests that optimism for a near-term recovery in the locals market is premature, as the market highly depends on the local economy which faces challenges from high unemployment, a weak housing market, and lack of job and population growth.
2) Core industry metrics like daily slot volume and win per slot have plummeted since late 2008 as the recession hit the local gaming and overall economy hard.
3) A recovery in the locals market will likely be slow and protracted given current negative trends and lack of visibility of improvements in the local economic factors that drive the market.
Gregg Carlson report sample Las Vegas Strip Ecosystem without pics

The Las Vegas Strip hotel market is facing significant changes with new hotel projects opening over the next few years, increasing supply by 11%. This will likely lead to shifts in the market shares held by different hotels. Top-tier hotels like Wynn may capture more business from mid-tier hotels, creating a "waterfall effect" down the chain. Lower-tier hotels risk negative returns and cash flows as their market share declines. The geography of development also matters - the north Strip faces stalled projects and weaker performance. The future remains unclear without stronger visitor growth to match the new supply.
Costco financial analysis may 2008 slideshare

The document provides an analysis of Costco Wholesale's recent performance and outlook. It summarizes that Costco reported strong same-store sales growth of 7-8% during the first four months of 2008 despite challenging economic conditions. Channel checks found Costco's local traffic held up well while other retailers saw weakness. The document maintains a positive long-term view of Costco given its consistent growth, strong membership renewal rates, and expansion plans to double its store count over 10 years. In the near term, the stock appears fully valued based on earnings estimates.
Viewers also liked (9)
Gregg Carlson report sample Las Vegas Strip Ecosystem without pics

Gregg Carlson report sample Las Vegas Strip Ecosystem without pics
Similar to Dp5
Privacy and care robots

Increasing use of robots in domestic and care situations - eg in hospital, to help the aged at home, etc - combined with the likelihood that robots may surveille and record both the humans they aid and the general environment - leads to a need to think about the privacy implications of use of robots as carers or caring aids.
Is More Data Always Better? The Legal Risks of Data Collection, Storage and U...

This document discusses the legal risks of data collection, storage, and use for marketing purposes. It notes that while data provides benefits, over-collection can pose privacy and legal issues. The document examines who collects data, what types of data are collected, why it's collected, and principles that govern collection. It also provides tips on minimizing risk, such as having a data governance plan, collecting only what is necessary, and being prepared in the event of a security breach. The overall message is that while data is valuable for business, collectors must respect privacy and limit their practices to authorized uses.
Polinter09

This document discusses the history and evolution of government surveillance programs in the United States from the 1990s through the 2000s. It describes programs like the Total Information Awareness Program (TIA) from 2002 that aimed to develop data mining techniques for counterterrorism but raised privacy concerns. It also discusses legal debates around warrantless wiretapping programs authorized after 9/11 under acts like the Patriot Act and their reauthorizations under Presidents Bush and Obama. Key issues included the scope of surveillance, oversight of programs, and balancing security with civil liberties and privacy.
Privacy and data protection primer - City of Portland

This is a Primer on Privacy and Data Protection presented at the Portland, Oregon City council on September 25, 2018
CSMFO 2012 Data Privacy in Local Government

This document provides an overview of data privacy for governmental organizations. It discusses what data privacy is, the risks associated with it such as identity theft, and common laws around data privacy including California state laws. It recommends that organizations take an inventory of their data, develop privacy policies and training, and ensure proper system monitoring and controls. The document emphasizes being proactive on data privacy issues.
Data Mining: Privacy and Concerns

Data mining involves extracting and analyzing large amounts of data to find patterns. While it provides benefits to companies, some view it as an invasion of privacy. There is little regulation in the US on data mining. The government has broad powers to collect data under laws like the Patriot Act. Data breaches have compromised over 800 million records, revealing sensitive personal information. Retailers use data mining to target customers, while gamers mine data to learn about new game content. More regulation may be needed to protect personal privacy as data mining becomes more widespread.
Unit 6 Privacy and Data Protection 8 hr

The document discusses privacy and data protection. It defines privacy as an individual's ability to control how and when personal information is shared with others. It outlines several international agreements that establish privacy as a universal human right. The document also discusses the three dimensions of privacy - personal, territorial, and informational - and basic privacy principles like transparency and purpose limitation.
Polinter09

This document summarizes the history and evolution of government surveillance and data collection programs related to counterterrorism efforts since the 1960s. It discusses early programs like COINTELPRO and the development of enabling technologies like databases, data mining, and facial recognition. It then outlines several post-9/11 US government programs aimed at identifying terrorists, the privacy and legal concerns they raised, and reasons for the cancellation of some programs.
General data protection

The document provides an overview of the General Data Protection Regulation (GDPR) which takes effect in May 2018. It defines personal data and special categories of personal data that require strict protection. GDPR places requirements on organizations that process personal data to protect privacy rights, ensure appropriate data use, and demonstrate compliance. It describes key data protection principles like lawfulness, purpose limitation, data minimization, accuracy, storage limitation, integrity and confidentiality, and accountability. The document outlines responsibilities of data controllers versus processors and the 12 steps for organizations to comply with GDPR.
Where In The World Is Your Sensitive Data?

Consumers rely on businesses to keep their personal information safe. Too few of those businesses are actively protecting that data. Here’s what’s gone wrong, and how businesses should be responding. Full blog here: http://bit.ly/1Jtzym5
All_you_need_to Know_About_the_Data_Privacy_Act.pdf

The document summarizes the key requirements for complying with the Philippines' Data Privacy Act of 2012. It outlines the structure and objectives of the law, as well as the obligations and penalties for personal information controllers and processors. The main compliance obligations include appointing a data protection officer, adhering to privacy principles when processing data, maintaining security of data, reporting breaches within 72 hours, and registering with the National Privacy Commission. Non-compliance could result in penalties such as fines and imprisonment.
Data protection guide

The Data Protection Act aims to protect individuals' personal data and privacy. It applies to most voluntary organizations that collect personal data. While the Act must be followed as it is law, there is flexibility in how organizations comply. The top priorities of the Act are preventing harm to individuals and respecting individuals. It focuses on protecting people, not just data itself. Personal data is any information relating to a living individual that identifies them. Most information that organizations collect about people, whether electronically or physically, will fall under the definition of personal data.
IBM Smarter Commerce Florida 2014 The Furture of Privacy by Aurélie Pols & Bl...

In a data driven economy, analysts must be concerned with how data is collected, processed and subsequently used to improve online customer experiences, during those moments that matter.
Unlocking Value & Controlling Risk by #MindYourPrivacy
Does your company adequately manage and control the Data Life Cycle? Are you aware of European Privacy fines? Did the Target security breach that emanated through a 3rd party worry you and make you wonder about where to start?
data-privacy-egypt-what-you-need-know-en.pdf

This document provides a summary of key concepts in data privacy and compliance. It begins with an introduction to data privacy and why it is important. It then covers key definitions and principles, including what is considered personal and sensitive personal data. It explains the difference between data controllers and processors. It also outlines the rights of individuals and when personal data can be legally processed. Finally, it provides a 10 step approach to developing an effective data privacy program, including appointing a data protection officer, maintaining a personal data register, notifying individuals and responding to their requests.
Marshaling Data for Enterprise Insights

This article explains a 10-year vision for the US Department of Homeland Security in regards to marshaling data.
Privacy Presentation for SOCAP-3

Consumers care deeply about privacy but take few steps to protect themselves. Most Americans want control over their personal data and what is collected about them, yet few change their online behaviors to avoid tracking. Stolen identities and data records are frequently bought and sold on the dark web, with social security numbers sold for just $1. The average cost of a data breach for large companies is $6.5 million. As more devices and records are connected, privacy risks grow substantially without comprehensive privacy laws or protections.
The Operations Of The National Security Agency

The National Security Agency (NSA) has been a United States intelligence agency since 1952. It works under the Department of Defense to monitor communications and data from foreign intelligence sources around the world, including terrorist organizations. Many of the NSA's operations are secret, involving activities like electronic surveillance, phone record collection, and software hacking sanctioned by the government to protect national security. The agency uses these tactics to gather intelligence on foreign targets, though its surveillance of American citizens without warrants has also been controversial.
the Death of Privacy in Three Acts

1. The document discusses how data protection laws are meant to work based on principles of consent and transparency, but these principles are breaking down due to technological advances.
2. Ubiquitous computing and "ambient environments" make it difficult if not impossible to provide meaningful consent and transparency as data is collected invisibly and continuously in public.
3. Big data undermines the idea of consent by allowing for secondary uses of data that were not envisioned or consented to originally.
4. "Smart cities" combine issues of consent, ubiquitous data collection, and big data, posing challenges for how to protect individual privacy within a system aimed at social benefits through data.
The Death of Privacy in Three Acts

A brief account of the current state of EU data protection laws accompanied by the suggestion they face almost insuperable challenge from the combination of the illusory nature of consent in most online contracts; the rise of big data as a "treasure hunt"; and the rise oambient environments for data colelction (the "Internet of Things") where design imperatives push towards an absence of opportunities for informed specific consent.
Similar to Dp5 (20)
Is More Data Always Better? The Legal Risks of Data Collection, Storage and U...

Is More Data Always Better? The Legal Risks of Data Collection, Storage and U...
data privacy handbook: A starter guide to data privacy compliance

data privacy handbook: A starter guide to data privacy compliance
Privacy and data protection primer - City of Portland

Privacy and data protection primer - City of Portland
All_you_need_to Know_About_the_Data_Privacy_Act.pdf

All_you_need_to Know_About_the_Data_Privacy_Act.pdf
IBM Smarter Commerce Florida 2014 The Furture of Privacy by Aurélie Pols & Bl...

IBM Smarter Commerce Florida 2014 The Furture of Privacy by Aurélie Pols & Bl...
More from Tommy Vandepitte
DPIA template

This document provides a template for conducting a Data Protection Impact Assessment (DPIA) pursuant to Article 35 of the GDPR. The template includes sections for describing the processing project, assessing the need for a DPIA, detailing the nature and purposes of the processing, evaluating the legality of the processing based on the legal framework, analyzing inherent risks to data subjects, implementing data protection by design principles, assessing residual risks, and involving the data protection authority as needed.
Gegevensbescherming-clausule in (overheids)opdracht

Voorbeeld van een Nederlandstalige clausule die in een overheidsopdracht of Request for Proposal (RFP) kan worden ingesloten om alle verschillende mogelijke samenwerkingsvormen (joint controller, controller-to-controller of controller-to-processor) af te dekken of dat althans te pogen.
20190131 - Presentation Q&A on legislation's influence (on travel management)

Presentation given at the event organised by ACTE and BATM on 31 January 2019 addressing a few questions on the payments legislation that are relevant for travel and expense manager.
GDPR toegepast op huur-verhuur (Dutch)

Deze presentatie gaat in op de toepassing van de gegevensbeschermingswetgeving op verhuuractiviteiten.
Controller-to-processor agreements

A presentation given at the legal hackers meetup of 19 June 2018 on common issues with controller-to-processor agreements aka "data processor agreement" (DPA). We revisit the distinction controller v processor. We then look at the directly applicable duties for processors, which do not need to be inserted in a contract. Finally we look at the different mandatory and "forgotten" components of the agreement.
Gegevensbescherming makelaars

De slides van een presentatie voor makelaars in de verzekeringssector. Gepresenteerd op 12 juni 2018 voor de Kempische Verzekeringskring (https://www.kempischeverzekeringskring.be/activiteit/gdpr-wat-u-als-makelaar-nog-niet-wist/).
EEAS - Cultivate your data protection

This document discusses data protection in layers, including physical security of devices, using encryption and passwords, being wary of public WiFi networks, installing trusted applications only, enabling automatic updates, using two-factor authentication when possible, regularly changing passwords, having backups, and being aware of social engineering risks in public spaces. The key messages are to stay curious about data protection, think long-term about security, and accept that incidents may occur while reporting them to mitigate consequences.
Presentation for the LSEC GDPR event - 20171130

Presentation given on the experience of privacy design labs on the LSEC Belgium GDPR event of 30 November 2017.
Event page: https://www.leadersinsecurity.org/events-old/icalrepeat.detail/2017/11/30/186/-/gdpr-plan-to-be-ready-prepare-to-set-change-to-go-session-3-privacy-impact-assessment-scenario-planning-data-loss-management.html?filter_reset=1
Privacy Design lab page: https://sites.google.com/site/pbd20171106
Example of a privacy design jam by Facebook (Berlin 2017) : https://www.facebook.com/facebookbrussels/videos/1419793831400471/
Training privacy by design

A first draft of a training on privacy by design both as an international concept (stemming from Canada) and as a GDPR related concept (article 25).
GDPR voor steden en gemeenten (Dutch)

Hoe breng je de nieuwigheden van de Algemene Gegevensbeschermingsverordening (AGV) of General Data Protection Regulation (GDPR) aan bij jouw stad of gemeente? Dit is een voorbeeld van slidedeck.
GDPR project board deck (example)

This is an example of a deck for the decision makers (generally the board of directors) to first explain that data protection is a (reputational, legal, operational) risk that - like any other business risk needs to be managed. Then it allows for some explanation of the status of data protection (law) and the main novelties under the GDPR. It then highlights the main changes required in project mode and (later on, after the handover) in business-as-usual mode.
Extra reference to the Vlerick reference (because published after the publication of this slide deck): http://www.vlerick.com/en/programmes/management-programmes/digital-transformation/digital-transformation-insights/insight-1)
IS/DPP for staff #8 - Monitoring

An example of how the staff training on information security, data protection and privacy (IS/DPP) could look.
This part is on an aspect that overarches all previous ones: monitoring. It touches on both perspectives of staff involvement:
- staff works with the data, processes it, etc. and thus is the agent of the company
- the company, to show accountability, should set up a balanced way of controlling the staff, which per se involves processing personal data of the staff members
The slides come with notes that in short explain the visuals on the slides.
IS/DPP for staff #7 - Incidents

This document discusses incident response procedures for an organization. It outlines the roles of the Information Security Officer (ISO) and Data Protection Officer (DPO) in responding to incidents. It also mentions having emergency and business continuity procedures in place to handle high impact incidents. The document stresses the importance of identifying, notifying, and escalating incidents to the appropriate teams like the helpdesk, ISO, or DPO.
IS/DPP for staff #6 - Acceptable use

An example of how the staff training on information security, data protection and privacy (IS/DPP) could look.
This part is on the acceptable use of the companies (and sometimes also own) means. Each company should add what is appropriate for it.
The slides come with notes that in short explain the visuals on the slides.
IS/DPP for staff #5b - Passwords

An example of how the staff training on information security, data protection and privacy (IS/DPP) could look.
The part focusses on authentication, and more particularly on passwords.
The slides come with notes that in short explain the visuals on the slides.
IS/DPP for staff #5a - Access

An example of how the staff training on information security, data protection and privacy (IS/DPP) could look.
This part is on authorization and access rights, focussing on the staff's part in that.
The slides come with notes that in short explain the visuals on the slides.
IS/DPP for staff #3b - Data Classification

An example of how the staff training on information security, data protection and privacy (IS/DPP) could look.
This part is on data classification, drilling a bit deeper into confidentiality, integrity, availability (=CIA), privacy (=CAPI), traceability, and retention (=PATRIC), to be amended to meet the specific organisation's setup.
The slides come with notes that in short explain the visuals on the slides.
IS/DPP for staff #3a - Data

An example of how the staff training on information security, data protection and privacy (IS/DPP) could look.
This part is on the concept of data, reasons for protecting data, personal data and data processing.
The slides come with notes that in short explain the visuals on the slides.
IS/DPP for staff #2 - Why?

An example of how the staff training on information security, data protection and privacy (IS/DPP) could look.
This part is on the reason why we should live up to the rules of IS/DPP, from a "negative" perspective (what do we want to avoid?) and from a "positive" perspective (what do we want to accomplish?).
The slides come with notes that in short explain the visuals on the slides.
IS/DPP for staff #1 - intro

An example of how the staff training on information security, data protection and privacy (IS/DPP) could look.
This is an introduction explaining
- the difference between information security, data protection and privacy,
- the need and usefulness for staff engagement
The slides come with notes that in short explain the visuals on the slides.
More from Tommy Vandepitte (20)
Gegevensbescherming-clausule in (overheids)opdracht

Gegevensbescherming-clausule in (overheids)opdracht
20190131 - Presentation Q&A on legislation's influence (on travel management)

20190131 - Presentation Q&A on legislation's influence (on travel management)
Recently uploaded
Benner "Expanding Pathways to Publishing Careers"

This presentation was provided by Rebecca Benner, Ph.D., of the American Society of Anesthesiologists, for the second session of NISO's 2024 Training Series "DEIA in the Scholarly Landscape." Session Two: 'Expanding Pathways to Publishing Careers,' was held June 13, 2024.
Temple of Asclepius in Thrace. Excavation results

The temple and the sanctuary around were dedicated to Asklepios Zmidrenus. This name has been known since 1875 when an inscription dedicated to him was discovered in Rome. The inscription is dated in 227 AD and was left by soldiers originating from the city of Philippopolis (modern Plovdiv).
مصحف القراءات العشر أعد أحرف الخلاف سمير بسيوني.pdf

مصحف أحرف الخلاف للقراء العشرةأعد أحرف الخلاف بالتلوين وصلا سمير بسيوني غفر الله له
ISO/IEC 27001, ISO/IEC 42001, and GDPR: Best Practices for Implementation and...

Denis is a dynamic and results-driven Chief Information Officer (CIO) with a distinguished career spanning information systems analysis and technical project management. With a proven track record of spearheading the design and delivery of cutting-edge Information Management solutions, he has consistently elevated business operations, streamlined reporting functions, and maximized process efficiency.
Certified as an ISO/IEC 27001: Information Security Management Systems (ISMS) Lead Implementer, Data Protection Officer, and Cyber Risks Analyst, Denis brings a heightened focus on data security, privacy, and cyber resilience to every endeavor.
His expertise extends across a diverse spectrum of reporting, database, and web development applications, underpinned by an exceptional grasp of data storage and virtualization technologies. His proficiency in application testing, database administration, and data cleansing ensures seamless execution of complex projects.
What sets Denis apart is his comprehensive understanding of Business and Systems Analysis technologies, honed through involvement in all phases of the Software Development Lifecycle (SDLC). From meticulous requirements gathering to precise analysis, innovative design, rigorous development, thorough testing, and successful implementation, he has consistently delivered exceptional results.
Throughout his career, he has taken on multifaceted roles, from leading technical project management teams to owning solutions that drive operational excellence. His conscientious and proactive approach is unwavering, whether he is working independently or collaboratively within a team. His ability to connect with colleagues on a personal level underscores his commitment to fostering a harmonious and productive workplace environment.
Date: May 29, 2024
Tags: Information Security, ISO/IEC 27001, ISO/IEC 42001, Artificial Intelligence, GDPR
-------------------------------------------------------------------------------
Find out more about ISO training and certification services
Training: ISO/IEC 27001 Information Security Management System - EN | PECB
ISO/IEC 42001 Artificial Intelligence Management System - EN | PECB
General Data Protection Regulation (GDPR) - Training Courses - EN | PECB
Webinars: https://pecb.com/webinars
Article: https://pecb.com/article
-------------------------------------------------------------------------------
For more information about PECB:
Website: https://pecb.com/
LinkedIn: https://www.linkedin.com/company/pecb/
Facebook: https://www.facebook.com/PECBInternational/
Slideshare: http://www.slideshare.net/PECBCERTIFICATION
Level 3 NCEA - NZ: A Nation In the Making 1872 - 1900 SML.ppt

The History of NZ 1870-1900.
Making of a Nation.
From the NZ Wars to Liberals,
Richard Seddon, George Grey,
Social Laboratory, New Zealand,
Confiscations, Kotahitanga, Kingitanga, Parliament, Suffrage, Repudiation, Economic Change, Agriculture, Gold Mining, Timber, Flax, Sheep, Dairying,
Lifelines of National Economy chapter for Class 10 STUDY MATERIAL PDF

The chapter Lifelines of National Economy in Class 10 Geography focuses on the various modes of transportation and communication that play a vital role in the economic development of a country. These lifelines are crucial for the movement of goods, services, and people, thereby connecting different regions and promoting economic activities.
Wound healing PPT

This document provides an overview of wound healing, its functions, stages, mechanisms, factors affecting it, and complications.
A wound is a break in the integrity of the skin or tissues, which may be associated with disruption of the structure and function.
Healing is the body’s response to injury in an attempt to restore normal structure and functions.
Healing can occur in two ways: Regeneration and Repair
There are 4 phases of wound healing: hemostasis, inflammation, proliferation, and remodeling. This document also describes the mechanism of wound healing. Factors that affect healing include infection, uncontrolled diabetes, poor nutrition, age, anemia, the presence of foreign bodies, etc.
Complications of wound healing like infection, hyperpigmentation of scar, contractures, and keloid formation.
How to Make a Field Mandatory in Odoo 17

In Odoo, making a field required can be done through both Python code and XML views. When you set the required attribute to True in Python code, it makes the field required across all views where it's used. Conversely, when you set the required attribute in XML views, it makes the field required only in the context of that particular view.
BBR 2024 Summer Sessions Interview Training

Qualitative research interview training by Professor Katrina Pritchard and Dr Helen Williams
Pengantar Penggunaan Flutter - Dart programming language1.pptx

Pengantar Penggunaan Flutter - Dart programming language1.pptx
Philippine Edukasyong Pantahanan at Pangkabuhayan (EPP) Curriculum

(𝐓𝐋𝐄 𝟏𝟎𝟎) (𝐋𝐞𝐬𝐬𝐨𝐧 𝟏)-𝐏𝐫𝐞𝐥𝐢𝐦𝐬
𝐃𝐢𝐬𝐜𝐮𝐬𝐬 𝐭𝐡𝐞 𝐄𝐏𝐏 𝐂𝐮𝐫𝐫𝐢𝐜𝐮𝐥𝐮𝐦 𝐢𝐧 𝐭𝐡𝐞 𝐏𝐡𝐢𝐥𝐢𝐩𝐩𝐢𝐧𝐞𝐬:
- Understand the goals and objectives of the Edukasyong Pantahanan at Pangkabuhayan (EPP) curriculum, recognizing its importance in fostering practical life skills and values among students. Students will also be able to identify the key components and subjects covered, such as agriculture, home economics, industrial arts, and information and communication technology.
𝐄𝐱𝐩𝐥𝐚𝐢𝐧 𝐭𝐡𝐞 𝐍𝐚𝐭𝐮𝐫𝐞 𝐚𝐧𝐝 𝐒𝐜𝐨𝐩𝐞 𝐨𝐟 𝐚𝐧 𝐄𝐧𝐭𝐫𝐞𝐩𝐫𝐞𝐧𝐞𝐮𝐫:
-Define entrepreneurship, distinguishing it from general business activities by emphasizing its focus on innovation, risk-taking, and value creation. Students will describe the characteristics and traits of successful entrepreneurs, including their roles and responsibilities, and discuss the broader economic and social impacts of entrepreneurial activities on both local and global scales.
BÀI TẬP BỔ TRỢ TIẾNG ANH 8 CẢ NĂM - GLOBAL SUCCESS - NĂM HỌC 2023-2024 (CÓ FI...

BÀI TẬP BỔ TRỢ TIẾNG ANH 8 CẢ NĂM - GLOBAL SUCCESS - NĂM HỌC 2023-2024 (CÓ FI...Nguyen Thanh Tu Collection
https://app.box.com/s/y977uz6bpd3af4qsebv7r9b7s21935vdBeyond Degrees - Empowering the Workforce in the Context of Skills-First.pptx

Iván Bornacelly, Policy Analyst at the OECD Centre for Skills, OECD, presents at the webinar 'Tackling job market gaps with a skills-first approach' on 12 June 2024
Recently uploaded (20)
مصحف القراءات العشر أعد أحرف الخلاف سمير بسيوني.pdf

مصحف القراءات العشر أعد أحرف الخلاف سمير بسيوني.pdf
ISO/IEC 27001, ISO/IEC 42001, and GDPR: Best Practices for Implementation and...

ISO/IEC 27001, ISO/IEC 42001, and GDPR: Best Practices for Implementation and...
Level 3 NCEA - NZ: A Nation In the Making 1872 - 1900 SML.ppt

Level 3 NCEA - NZ: A Nation In the Making 1872 - 1900 SML.ppt
Lifelines of National Economy chapter for Class 10 STUDY MATERIAL PDF

Lifelines of National Economy chapter for Class 10 STUDY MATERIAL PDF
Film vocab for eal 3 students: Australia the movie

Film vocab for eal 3 students: Australia the movie
Pengantar Penggunaan Flutter - Dart programming language1.pptx

Pengantar Penggunaan Flutter - Dart programming language1.pptx
Philippine Edukasyong Pantahanan at Pangkabuhayan (EPP) Curriculum

Philippine Edukasyong Pantahanan at Pangkabuhayan (EPP) Curriculum
REASIGNACION 2024 UGEL CHUPACA 2024 UGEL CHUPACA.pdf

REASIGNACION 2024 UGEL CHUPACA 2024 UGEL CHUPACA.pdf
BÀI TẬP BỔ TRỢ TIẾNG ANH 8 CẢ NĂM - GLOBAL SUCCESS - NĂM HỌC 2023-2024 (CÓ FI...

BÀI TẬP BỔ TRỢ TIẾNG ANH 8 CẢ NĂM - GLOBAL SUCCESS - NĂM HỌC 2023-2024 (CÓ FI...
Beyond Degrees - Empowering the Workforce in the Context of Skills-First.pptx

Beyond Degrees - Empowering the Workforce in the Context of Skills-First.pptx
Dp5
- 1. PERSONAL DATA PROTECTION Finality Processing personal data Finality Legitimacy Transparency Organisation Proportional End-to-end
- 5. Source: Movie “The Game”
- 7. Source: Movie “Minority Report”
- 8. Source: Movie “You’ve got mail”
- 11. Source: Information Commissioner’s Office, UK
- 12. Source: Movie “Da Vinci Code”
Editor's Notes
- The controller(s) must ensure that personal data is: (a) processed fairly and lawfully; (b) collected for specified, explicit and legitimate purposes and not further processed in a way incompatible with those purposes. Further processing of data for historical, statistical or scientific purposes shall not be considered as incompatible provided that Member States provide appropriate safeguards; (c) adequate, relevant and not excessive in relation to the purposes for which they are collected and/or further processed; (d) accurate and, where necessary, kept up to date; every reasonable step must be taken to ensure that data which are inaccurate or incomplete, having regard to the purposes for which they were collected or for which they are further processed, are erased or rectified; (e) kept in a form which permits identification of data subjects for no longer than is necessary for the purposes for which the data were collected or for which they are further processed. Member States shall lay down appropriate safeguards for personal data stored for longer periods for historical, statistical or scientific use. 05/12/10