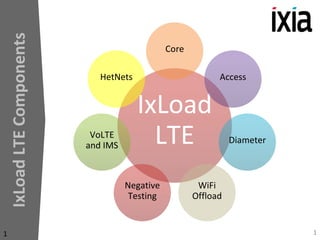
Diameter_Apr2014.pptx
- 3. Diameter Testing Scenarios •Diameter •Server Test •EPC Isolation •DRA 3
- 4. 4 Policy Server (PCRF) Testing • Emulation of the Policy Control Enforcement Function (PCEF) in the PDN-GW to benchmark PCRF performance – Measure transactions per second (TPS) with a minimum number of policy rules established – Increase policy rules to understand the impact on TPS performance – Measure the number of active subscriber sessions that can supported (capacity) SGi Rx Sy IMS Network PCEF/PDN- GW/EPC PCRF (DUT) OCS Sh HSS (AS) Gx Server Test
- 5. MME Isolation Testing MME/SGSN (DUT) S-GW S1-MME S6a S6d eNodeB ▪ Validate access control, security issues, and basic LTE mobility ▪ Simulate intra and inter eNodeB handovers, IRAT with RNC ▪ Test the scalability of next generation MME HSS S11 S4 RNC IuPS EPC Isolation
- 6. Diameter Routing Agent (DRA) PGW DRA (DUT) MME OCS/OFCS HSS ▪ Test the any-to-any Diameter node connectivity of the DRA ▪ Measure packet routing performance ▪ Measure load balancing, failover performance, and network congestion control ▪ Verify Diameter proxy/relay services (used in peering/roaming agreements) S6a Gz/Gy S6a Gz/Gy DRA
- 7. Interface Support 1. S6a - HSS and MME 2. S6d - HSS and SGSN 3. Gx - PCRF and PCEF 4. Ro/Gy - PCEF and OCS 5. S6b - AAA and PGW 6. Rx - CSCF and PCRF 7. STa - AAA and ANGW 8. Sh - HSS and AS 9. Cx - CSCF and HSS 10. Sy - OCS and PCRF 11. SWm – AAA and ePDG (Evolved Packet Data Gateway) 12. SWa - AAA and AN GW (Access Network GW for untrusted non-3GPP) 13. Rf/Gz - PGW and OFCS; OFCS and CSCF 14. Gr – SGSN and HLR 15. SGs – MME and VLR 16. S9 – V-PCRF and H-PCRF 17. SWx/Wx – AAA and HSS 18. S13/S13’ – MME and EIR; SGSN and EIR 19. Gxx (Gxc & Gxa) - SGW and PCRF; AN GW and PCRF 7
- 8. Performance on Ixia HW 8 40 Million Subscribers >400.000 Transactions per Second
- 9. VM based solution (sw only) 9 • It runs as a VM but it is not the IxVM product (VMware format, can be installed using VMware Player freeware); no Hypervisor • Performance is not guaranteed • Can run on the same machine as ixLoad Client or different one • Still needs ixLoad CPD Base PartNumber (925-5001)
- 10. Diameter Licensing • 3 components: – Interface (Client or Server): a-la-carte – TPS level – Total Number of Subscribers TPS and Subscribers are total, no restriction per interface or nodes. 10
- 11. Diameter Licensing – details • TPS licenses are checked out in 1k batches, Subscribers in 10k batches. Any number of users can run in parallel provided that aggregated sum of checked out licenses doesn’t exceed the total limit. E.g. for a 20k TPS: maximum 20 users can run in parallel tests each of 1k TPS. – Once TPS limit is reached, there’s a throttling mechanism in place; warning is displayed at run time in ixLoad Log window. – If Subscriber number is exceeded the user will not be able to run the test (apply config error) 11
- 12. What can be tested? ➢Functional testing: ➢Coordinated simulation across multiple interfaces or nodes ➢Negative scenarios ➢Conformance testing ➢Performance 12
- 13. Advanced Features - SmartEvents 13 ❑ Define behavior across the Diameter network, nodes and subscriber. ❖ Reacts to message content received ❖ Create dynamic subscriber behavior based on probabilities or external stimuli ❖ Realistic response to network or protocol failure conditions ❖ Ability to dynamically change overall test behavior ❖ Coordinate events from multiple applications ❑ Each subscriber flows through its own state machine. ❖ Subscribers can be grouped to align with traffic model.
- 14. SmartEventsTM: Volte call example 14 ❑ Use SmartEvents to simulate real world traffic profiles across multiple interfaces such as Gx & Rx Coordinate Gx and Rx, here we are able to verify CCA-I followed by starting an AAR on Rx. The Rx AAR will not be sent until the CCA-I is received. Verify the RAR is sent by the PCRF for the appropriate subscriber to insure the PCRF has signaled to the PGW to create a dedicated bearer channel. The order of the Rx AAA and Gx RAR can vary based on network conditions but can be handled by the SmartEvent state machine ❑ Coordinating multiple stateful interfaces such as Gx and Rx allows the user to verify the PAS or PCRF are properly handling and routing messages and transactions to the appropriate subscribers.
- 15. SmartEvents: Example 2 15 ❑ Conditional event handlers allow users to create real world traffic profiles Conditional event handler can use probability assignments that cause users to take action based on probabilities of occurrence assigned Subscribers will take a different path each time through the SmartEvents state machine based on the probability assignments, in this case 40% of subscribers will place a VoLTE call ❑ Conditional event handlers can be used many different ways including creating loops until a condition such as credit pool balance are met.
- 16. SmartAVPsTM 16 ❑ AVP customization and substitution ❑ Create/modify/remove any AVP in any Diameter Application Message ❑ Configure an AVP from scratch ❑ Include vendor-specific or other optional AVPs in Diameter messages ❑ Insert multiple AVPs inside an AVP (nested AVPs) ❑ Define proprietary signaling or corrupt AVPs for negative testing ❑ Possibility of being compatible with any 3GPP spec version ❑ Simulate scenarios that are not as per specification in order to address some custom/specific scenarios (eq EUTRAN simulation with UTRAN parameters) ❑ Support for subscriber specific-data as AVPs data through the use of „transparent-data” option e.g. IMSI, IMEI, MSISDN, public/private identity, IP address of the subscriber (IPv4 or IPv6). ❑ Inter-operability with any customer equipment
- 17. 17 Smart AVPs: Example 1
- 18. 18 Smart AVPs – Example 2 (Nested AVPs)
- 19. SmartAVPs: Example 3 19 ❑ Once the SmartAVP is defined users insert one or many into the SmartEvent state machine SmartAVPs are added into the state where users want them to occur
- 20. Diameter Protocol 20 ❖ Defined by RFC6733 ❖ All data delivered by the protocol is in the form of AVPs. ❖ Runs over TCP or SCTP The Diameter protocol provides the following facilities: ❖ Ability to exchange messages and deliver AVPs ❖ Capabilities negotiation ❖ Error notification ❖ Extensibility, required in [RFC2989], through addition of new applications, commands, and AVPs ❖ Basic services necessary for applications, such as the handling of user sessions or accounting
- 21. Diameter Protocol 21 Diameter is a client – server protocol BUT: • A Diameter node may act as an agent for certain requests while acting as a server for others. • Any node can initiate a request. In that sense, Diameter is a peer- to-peer protocol. • The Diameter protocol also supports server-initiated messages, such as a request to abort service to a particular user. • A Diameter client generates Diameter messages to request authentication, authorization, and accounting services for the user • A Diameter server performs authentication and/or authorization of the user and/or and accounting requests.
- 22. Why IxLoad Diameter? 1 Reason: Performance 22 Metric 1 Appliance Max Subscribers 16M Max Rate 400.000 Are you sure your DRA is strong enough? How do you really measure MME/PGW performance if the HSS/PCRF is slow? VoLTE makes it much worse!
- 23. VoLTE and Diameter • One single VoLTE call involves: – 5 Diameter nodes (DRA, HSS, OFCS, OCS, PCRF) – 3 EPC nodes (MME, PGW, CSCF) – 6 Diameter interfaces (S6a, Gx, Rx, Sh, Sy, Cx) • IxLoad is the only test tool that can run all the above in one single test, with coordinated simulation between multiple interfaces. 23
- 24. VoLTE and Diameter • VoLTE impact in Diameter signaling: – 1 VoLTE call triggers 13 Diameter messages (!!!) – Note: Attach/VoLTE call/Detach sequence triggers 30 Diameter messages 24 3 Million UEs BHCA Diameter Transactions per Second Nominal test 2.4M 20.000 Earthquake scenario (20x overload) 48M 410.000 Your VoLTE and Diameter test tools must scale appropriately!
- 25. Diameter - IxLoad vs Competition Area Performance IxLoad XT80v2 Competition Performance Max Subscribers 16M <5M Max Transactions 400K 400K Flexibility Can edit state machine YES YES Can create events for synchronization across interfaces YES NO Can add/remove/modify AVPs, including for specific message and/or state YES Partially 25
- 26. Diameter Roadmap 26 Date Feature set 4/15 Add support for Sd interface 6/30 EventViewer support for error reporting 6/30 Support for PerfectStorm HW 7/30 (in planning) Add support for AAA and 3GPP AAA Radius 9/30 (in planning) Add support for SLh, SLs, SLg interfaces