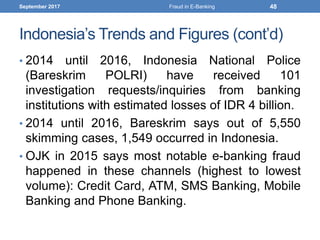
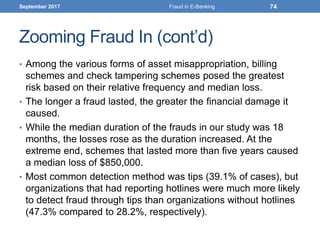
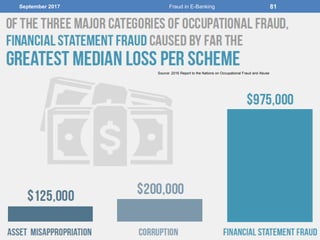
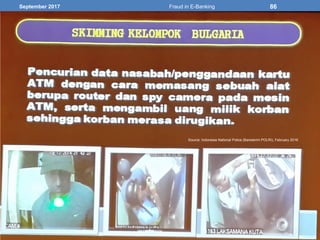
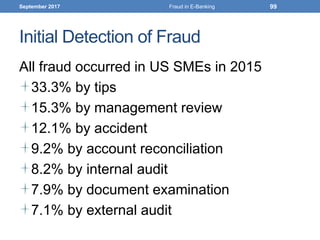
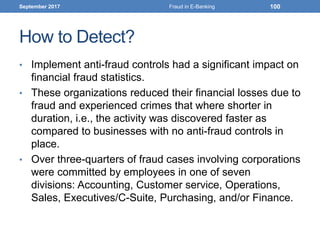
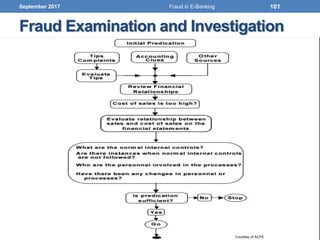
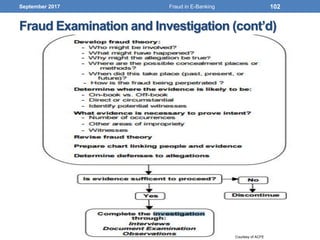
The document discusses the prevalence and impact of fraud within the electronic banking sector, outlining various definitions, types, and trends related to fraud. It highlights the significant costs of fraud, estimated at $72 billion annually, with a notable portion attributed to internal actors. Key areas of focus include the types of fraud occurring, methods of detection and investigation, and the importance of robust anti-fraud measures for organizations.


![September 2017
Source: IBM [1] UNODC Comprehensive Study on Cybercrime, 2013
23Fraud in E-Banking](https://image.slidesharecdn.com/dealingwithfraudinelectronicbankingsphereforparticipantv1-170916183855/85/Dealing-with-Fraud-in-E-Banking-Sphere-23-320.jpg)
![September 2017
Source: IBM
[2] FBI: Crime in the United States 2013
[3] United California Bank Robbery
[4] Center for Strategic and International Studies
24Fraud in E-Banking](https://image.slidesharecdn.com/dealingwithfraudinelectronicbankingsphereforparticipantv1-170916183855/85/Dealing-with-Fraud-in-E-Banking-Sphere-24-320.jpg)
![September 2017
Source: IBM [6] ESG: http://bit.ly/1xzTmUW
25Fraud in E-Banking](https://image.slidesharecdn.com/dealingwithfraudinelectronicbankingsphereforparticipantv1-170916183855/85/Dealing-with-Fraud-in-E-Banking-Sphere-25-320.jpg)