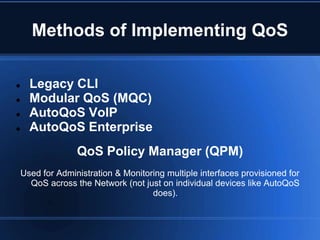
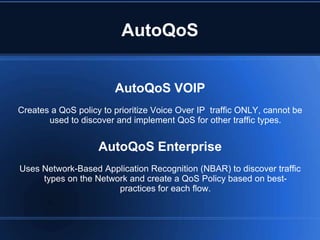
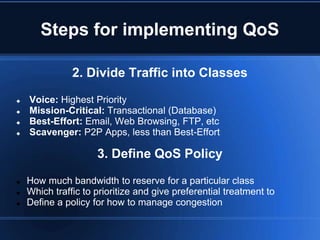
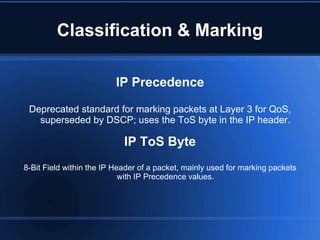
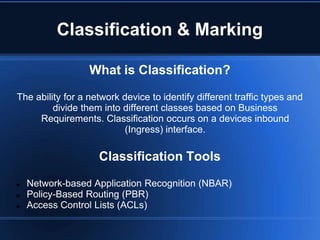
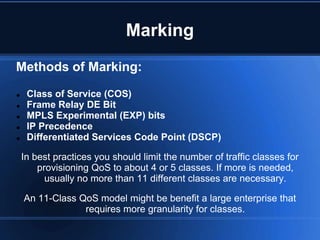
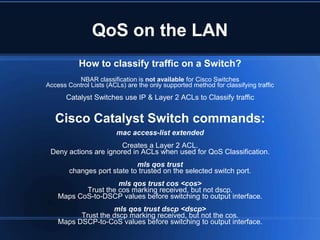
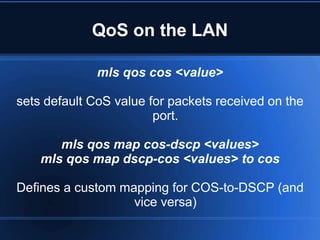
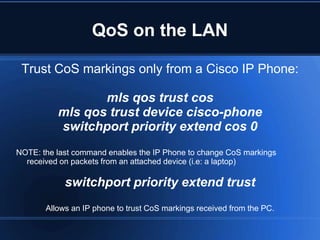
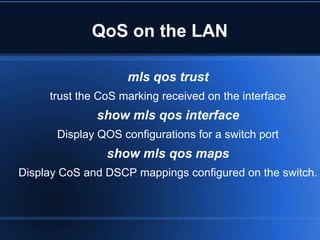
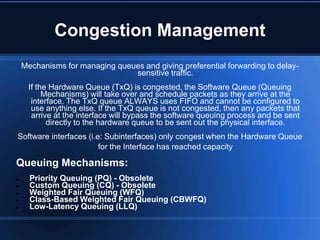
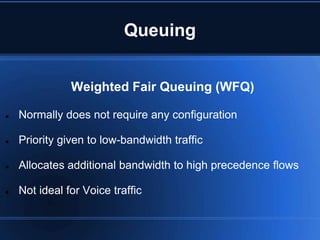
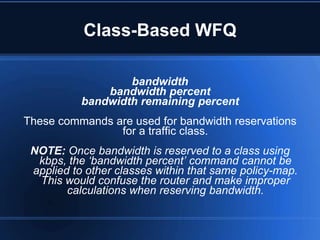
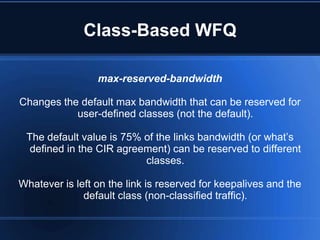
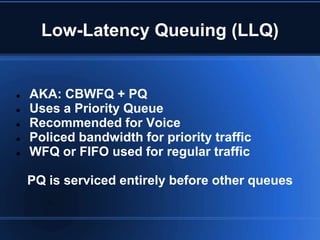
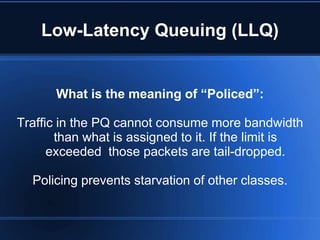
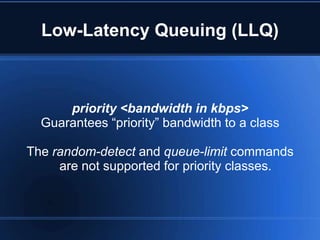
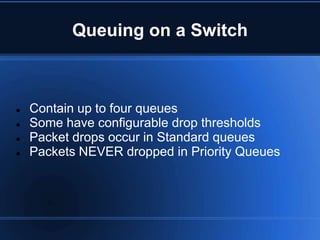
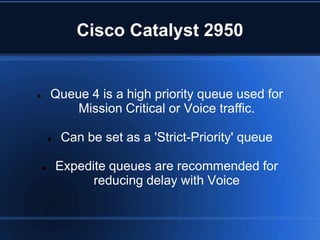
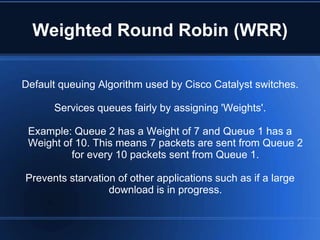
This document provides an overview of Cisco Quality of Service (QoS) methods and configuration. It discusses legacy CLI, Modular QoS CLI (MQC), and AutoQoS features for implementing QoS policies. It also covers traffic classification, marking, queuing mechanisms like weighted fair queuing (WFQ) and low-latency queuing (LLQ), and configuration of QoS on switches.