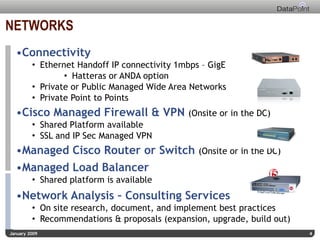
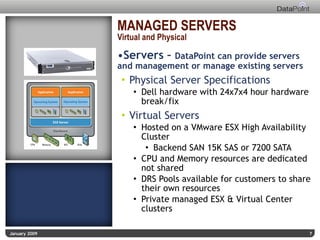
The document provides an overview of Datapoint's managed service offerings, highlighting managed networks, servers (both virtual and physical), and applications, with 24x7 live support. It details various connectivity options, redundancy through multiple data centers, and disaster recovery solutions. Additionally, it outlines management services for both Microsoft and Linux applications, along with custom monitoring services.