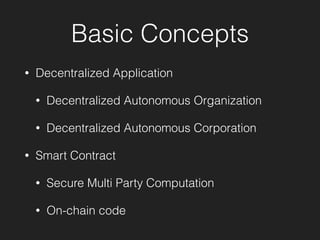
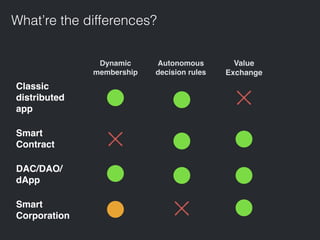
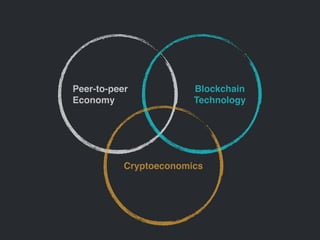
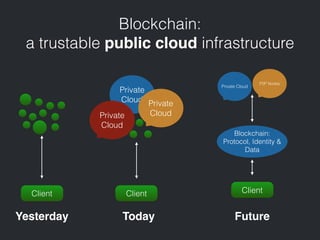
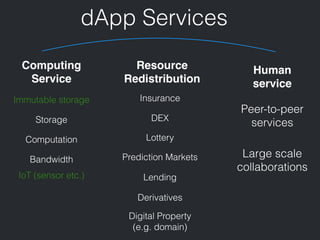
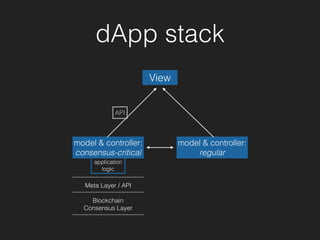
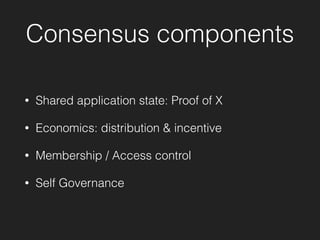
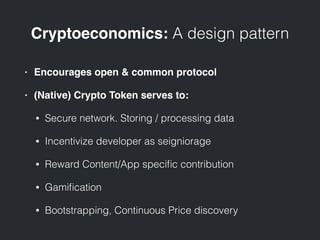
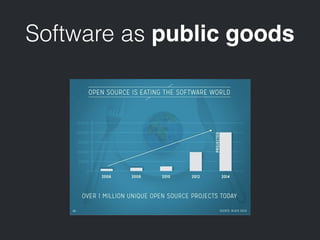
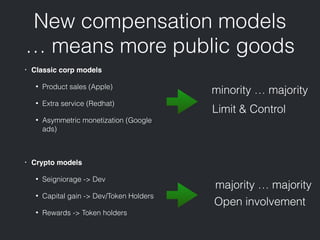
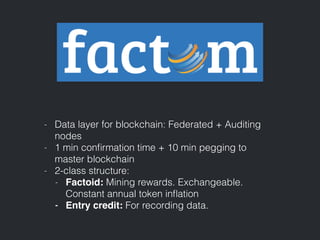
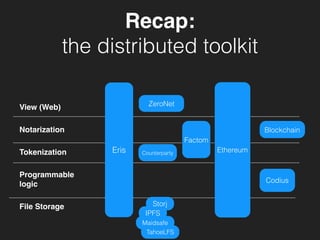
The document outlines key concepts related to decentralized applications (dApps), including decentralized autonomous organizations, smart contracts, and cryptoeconomics. It discusses the structure and functionality of blockchain technology, various application models, and emerging compensation models in the cryptocurrency ecosystem. Additionally, it announces upcoming demo events for project presentations related to distributed toolkits.