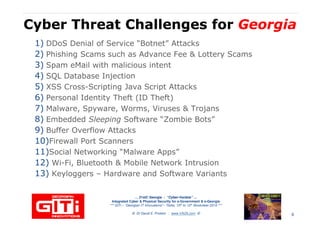
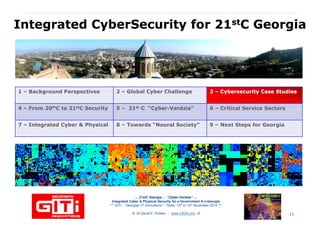
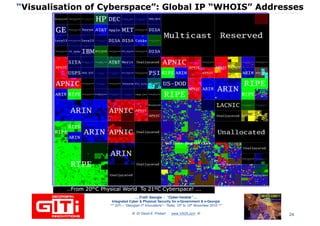
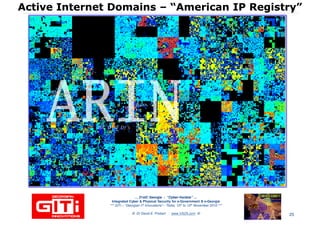
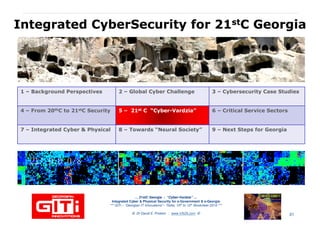
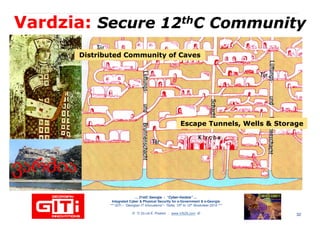
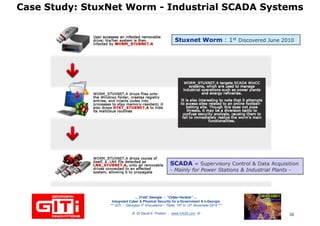
The document discusses the importance of integrated cyber and physical security in Georgia's e-government initiatives. It provides an overview of cybersecurity challenges, reviews national case studies, and proposes frameworks for enhancing Georgia's cybersecurity measures. Recommendations include upgrading critical infrastructure to international standards and fostering a cybersecurity culture across sectors.