Cyber security is important for government officials to safeguard against data theft and damage. The document provides recommendations for government officials to maintain cyber security, including:
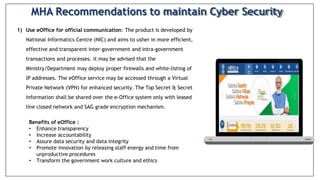
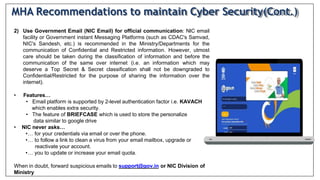
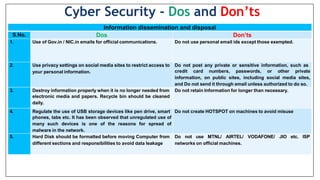
1. Use eOffice or government email for official communication and only share classified information over closed networks with encryption.
2. Use approved video conferencing solutions from government organizations and do not share classified information.
3. Avoid using digital assistant devices and turn off smart devices during classified meetings.
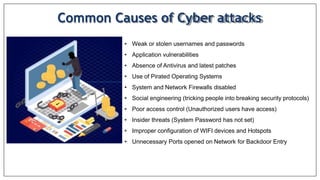
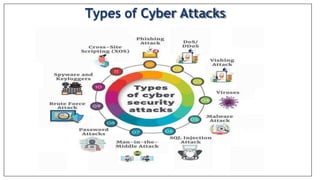
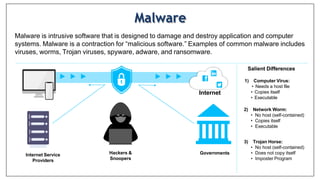
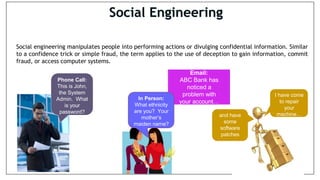
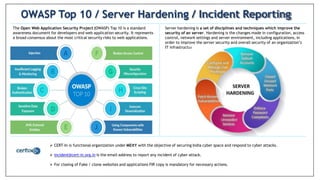
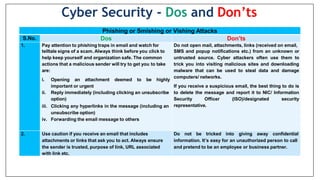
4. Be aware of common cyber attacks like phishing and understand server hardening against vulnerabilities.