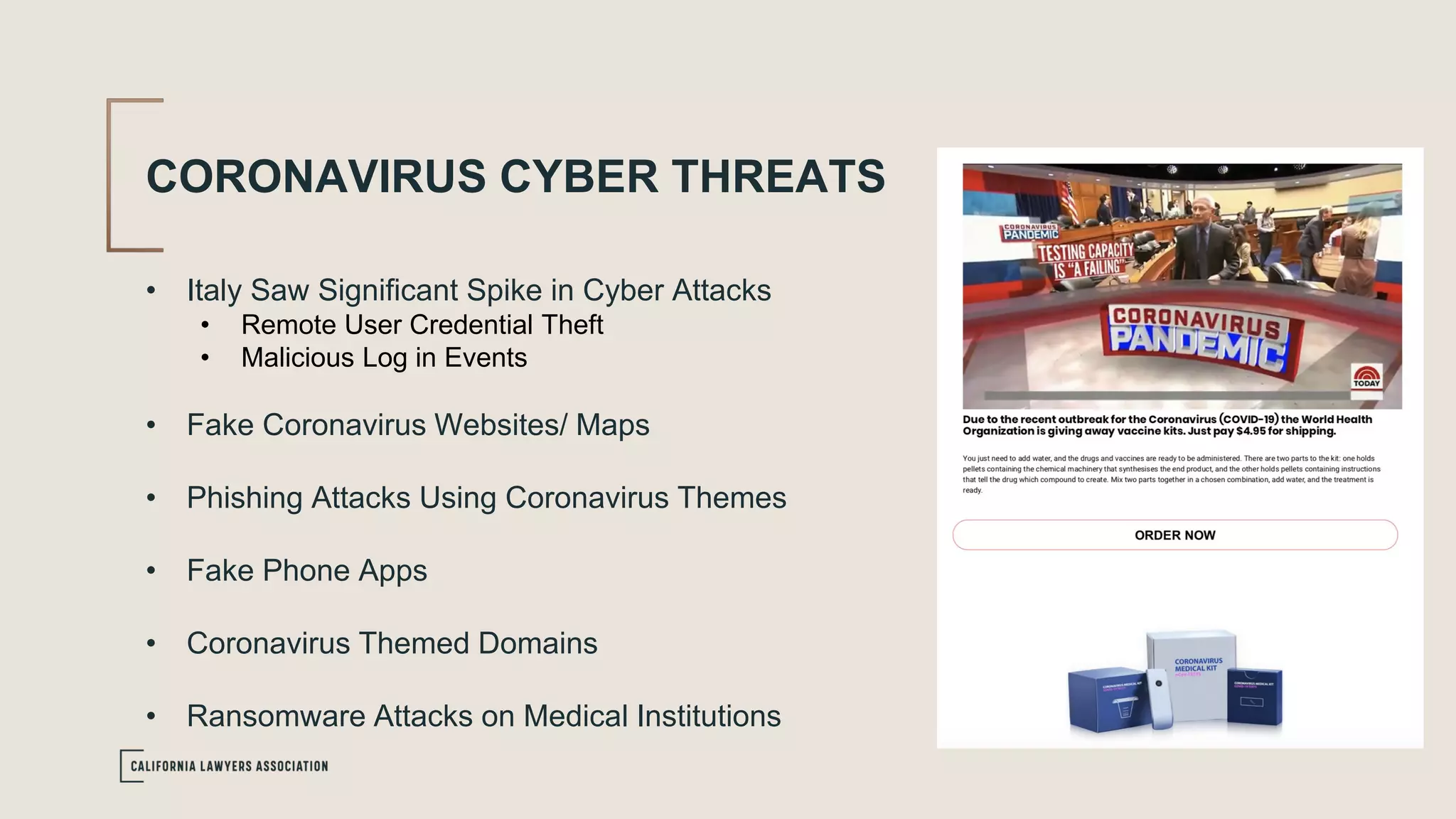
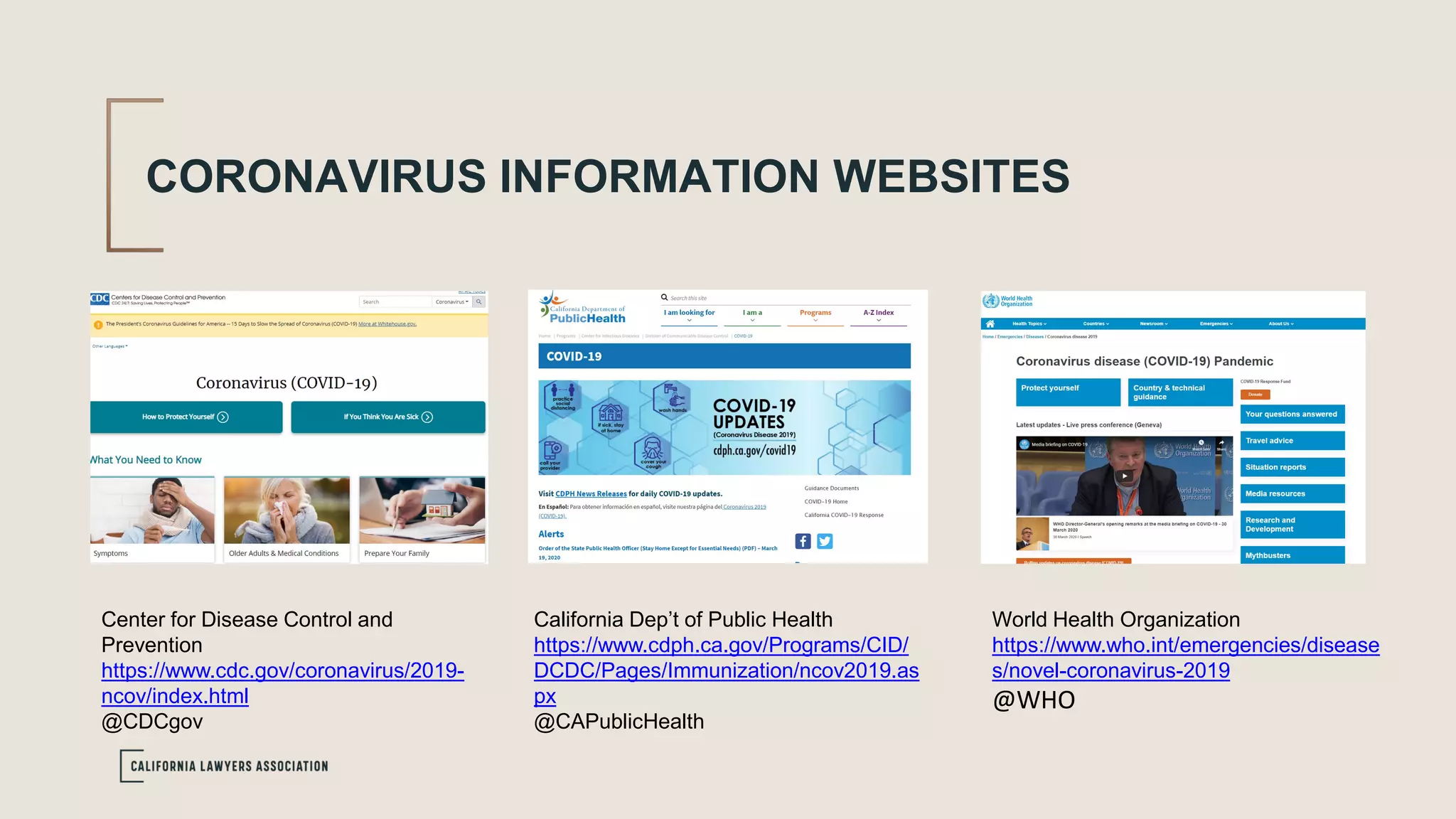
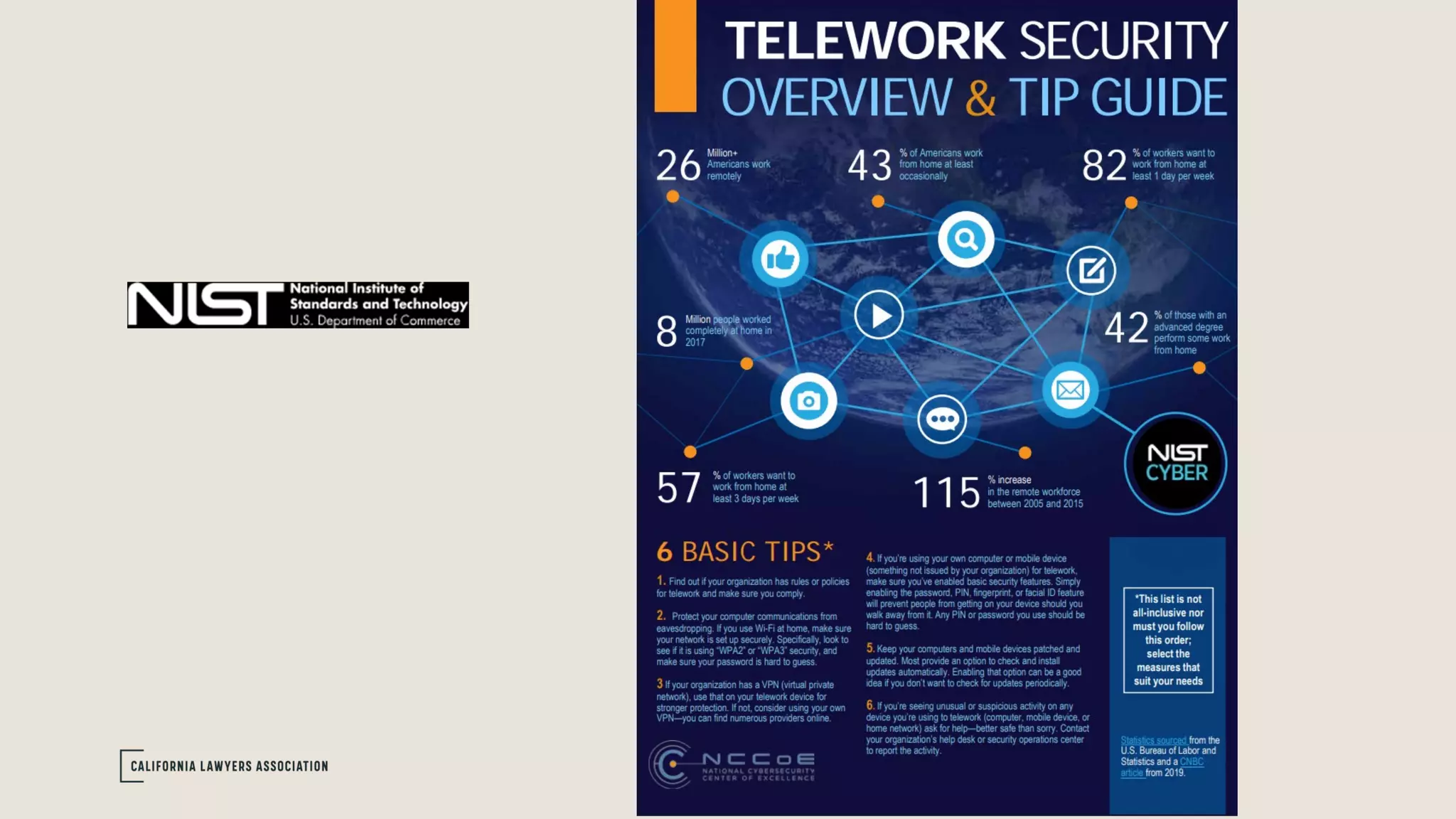
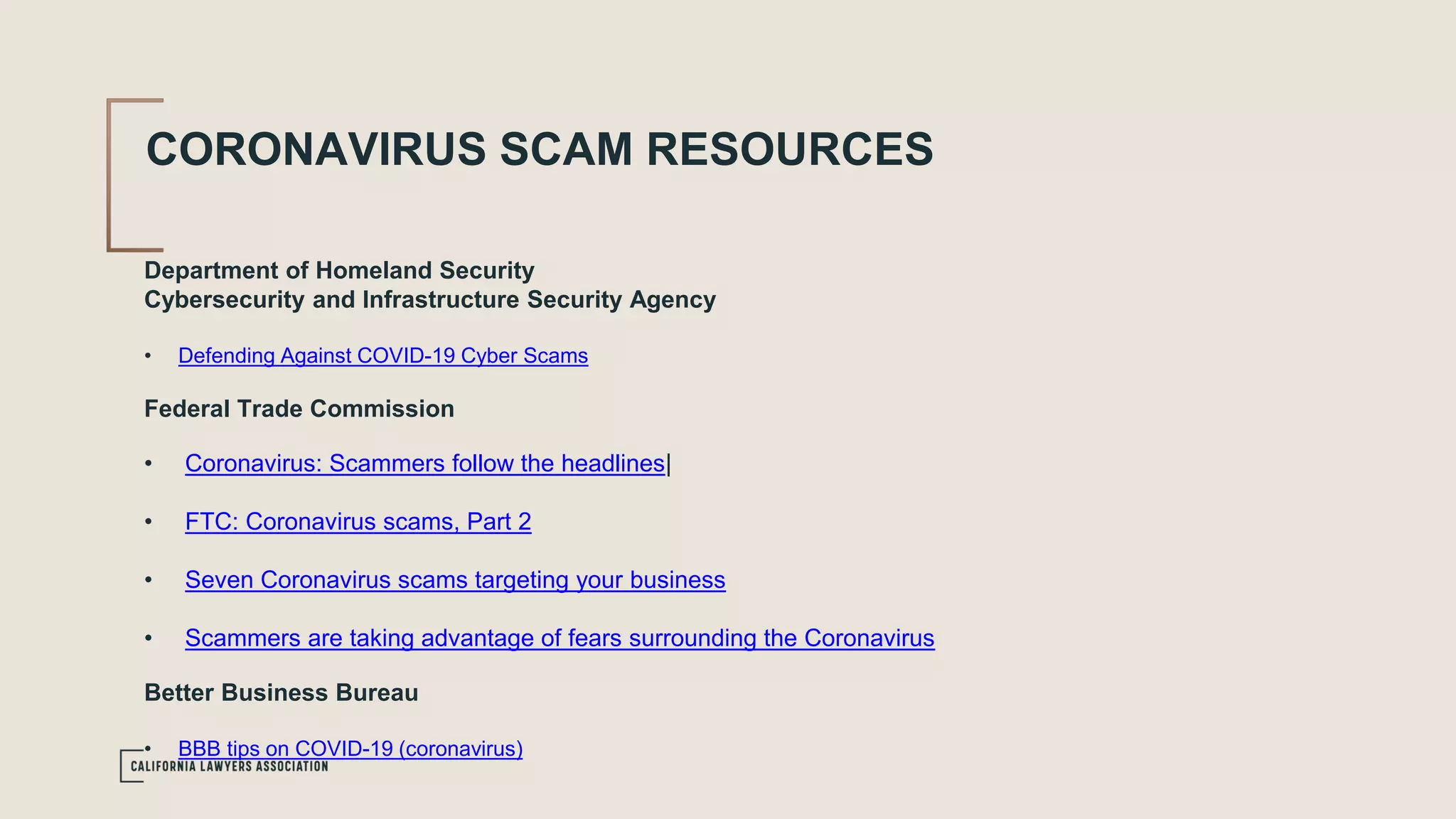
This document provides an overview and discussion of cybersecurity issues related to working from home during the COVID-19 pandemic. It discusses securing home networks and devices, protecting proprietary company information, training employees on cybersecurity best practices, and common cyber threats such as phishing scams taking advantage of coronavirus fears. Resources from government agencies and organizations are also included to help secure remote work environments and defend against cyberattacks.