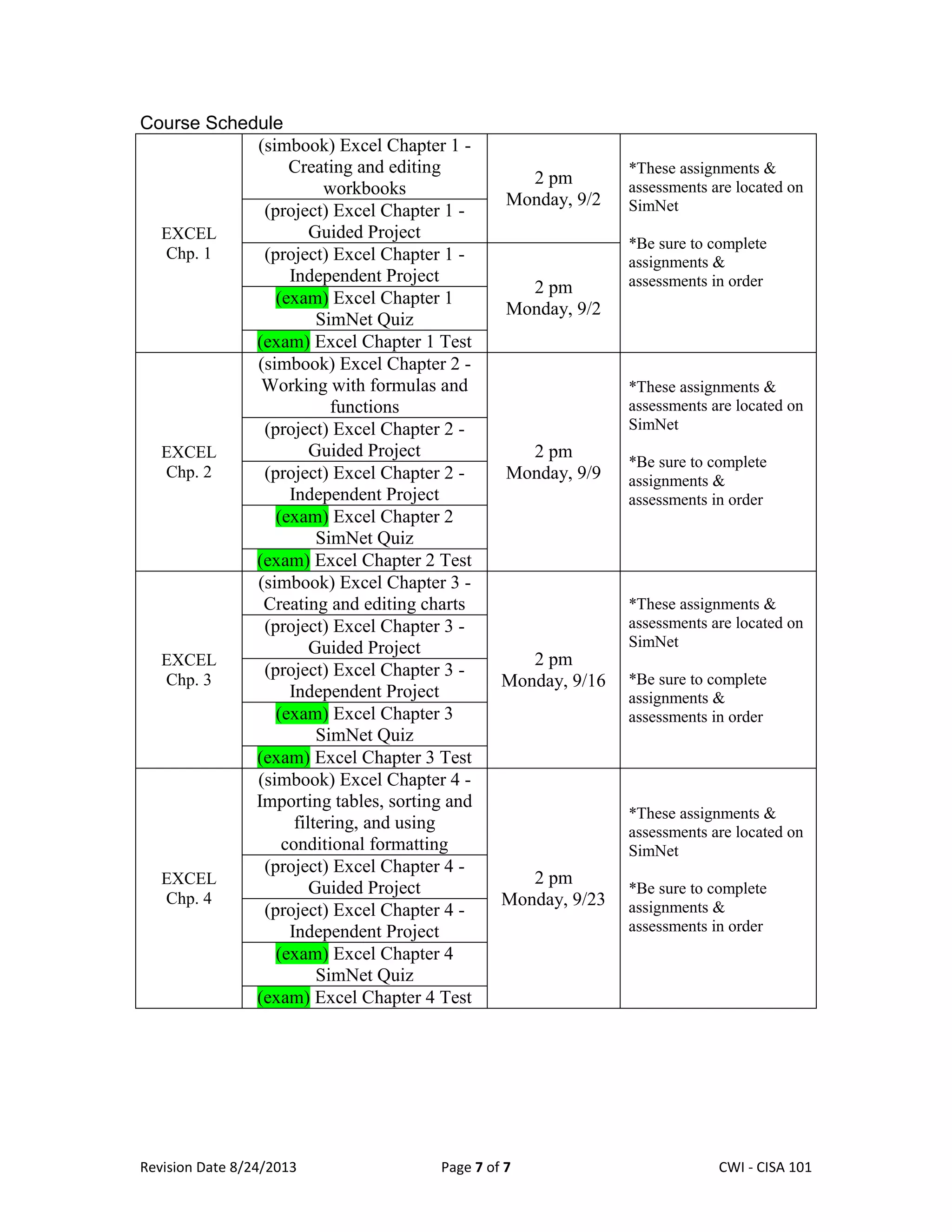
This one-credit course provides an introduction to spreadsheets using Microsoft Excel. The course will focus on basic spreadsheet skills like performing calculations, formatting cells, using functions, creating charts, filtering and sorting data, and conditional formatting. Students will complete assignments, projects, and assessments in SimNet to demonstrate proficiency in spreadsheet applications. A passing grade requires a score of at least 70% on each assessment and an average score of at least 70% on all assignments and projects.
![Revision Date 8/24/2013 Page 3 of 7 Lex Mulder– CWI - CISA 101
Course Focus
The CSA is comprised of four sections: General Computer Technology, Internet/Email, Word
processing, Spreadsheets, and Presentations using the (Microsoft) Office Suite applications.
Students will be required to demonstrate competency in all four sections prior to applying for
graduation from CWI.
This course will focus on Basic Computer Skills and Application Strategies. The software used for
the course will be the Operating System Windows 7, Internet Explorer 8, Microsoft Office 2013
(Word, Excel, and PowerPoint). The course is specifically designed to these programs. Office
Web Apps or Starter is not recommended.
COURSE OBJECTIVES AND OUTCOMES
Upon completion of this course, the student should be able to demonstrate:
1. Proficiency using Spreadsheet application software to perform basic computations and
formatting.
NOTE:More detailed Outcomes are listed in Appendix A.
Textbooks and Required Materials
ISBN 9781259188442- basic one module SimNet for Office 2013 access card WITH
printed Coulthard Computing Now Concepts text for $45 net to the bookstore
or
ISBN 9780077801328 – basic one module SimNet for Office 2013 access card- no print
option, $35 net to the bookstore
Minimum Software Requirements
MICROSOFT INTERNET EXPLORER 8.0 OR HIGHER
MICROSOFT WINDOWS 7
MICROSOFT OFFICE 2013: Many assignments are specific to Microsoft Office 2013and it
will be difficult, if not impossible, to complete these assignments in the same manner as the
text if you do not have access to Office 2013. All campus computers should contain Office
2013 so feel free to use them.
OTHER REQUIRED MATERIALS:Student will need a storage device of their choice(CISA faculty
advises that you use SkyDrive or a flash drive [also called a thumb drive or jump drive]) and a
notebook for notes.
Methods of Delivery
All assignments and tests will be completed online using SIMnet software and Blackboard.](https://image.slidesharecdn.com/cwisyllabuscisa115-fall-2013-lund-130824233225-phpapp02/75/Cwi-syllabus-cisa115-fall-2013-lund-3-2048.jpg)