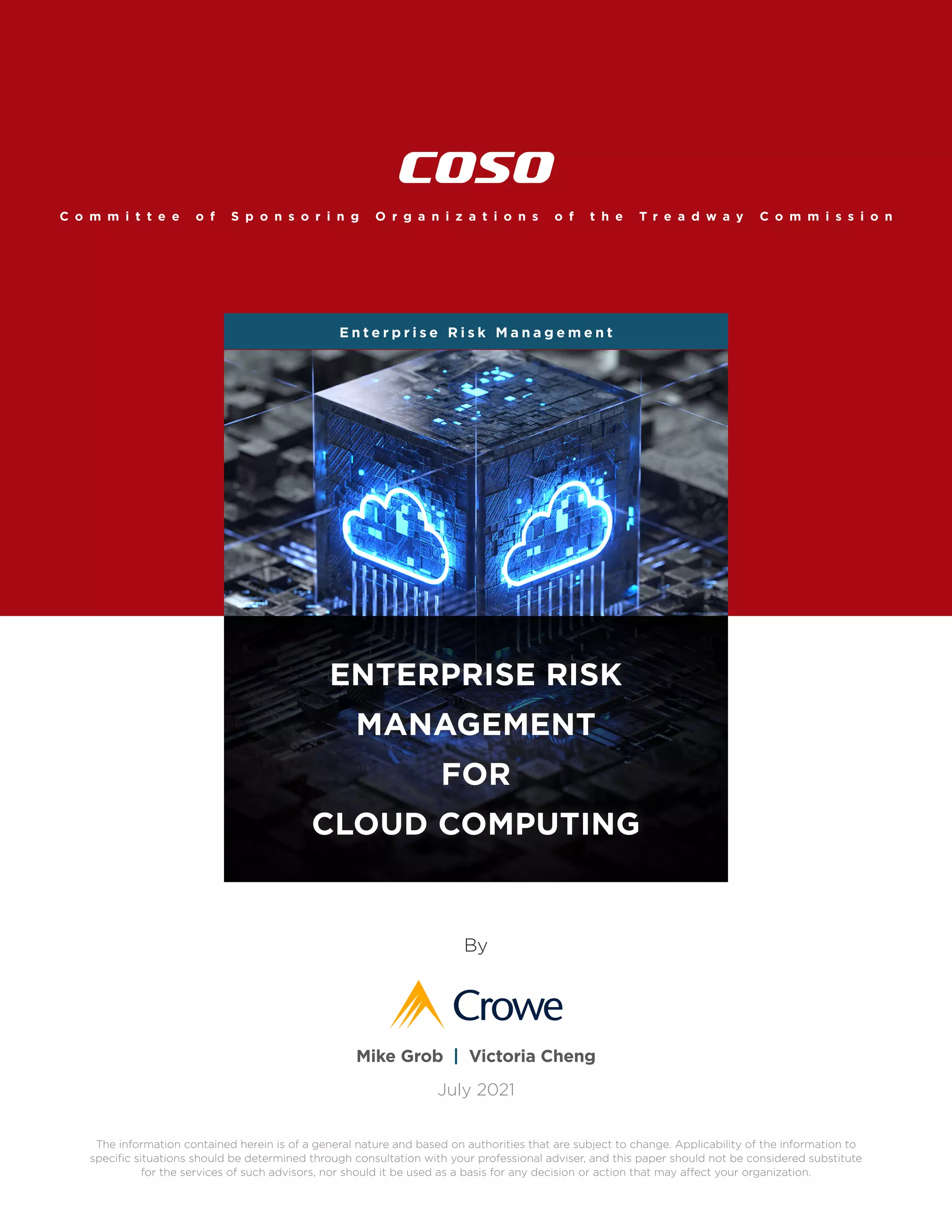
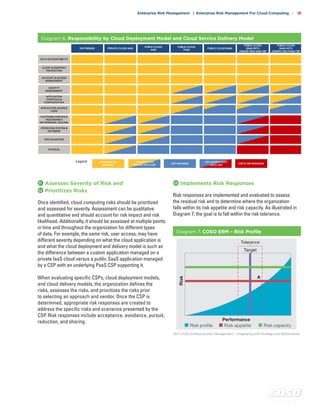
The document discusses enterprise risk management for cloud computing. It provides an overview of cloud computing and its growth. It then discusses how the COSO enterprise risk management framework can be applied to managing risks in a cloud computing environment. The framework includes five components - governance and culture, strategy and objective setting, performance, review and revision, and information communication and reporting. It examines each component and the principles within and provides guidance on how organizations can implement them for effective cloud computing risk management.