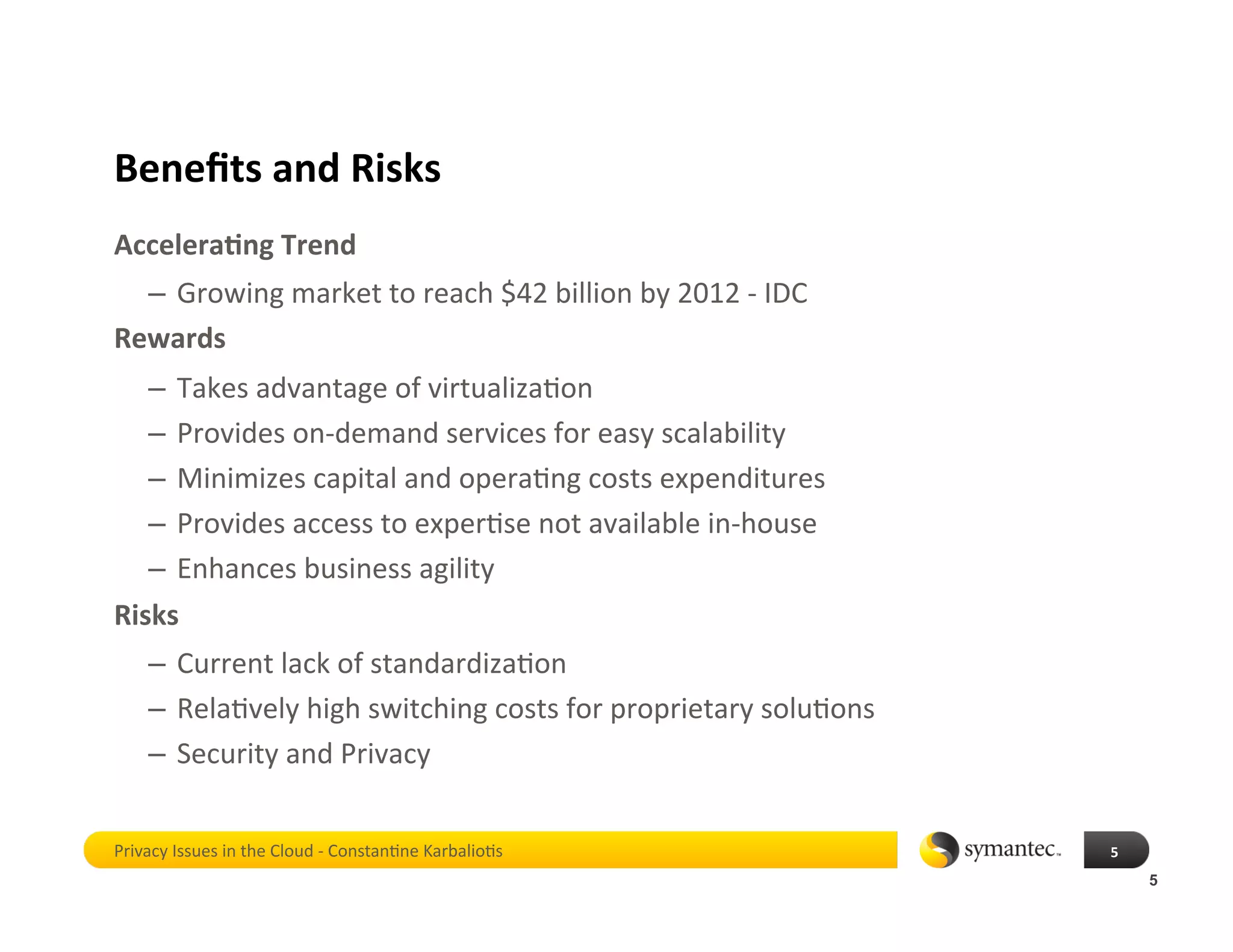
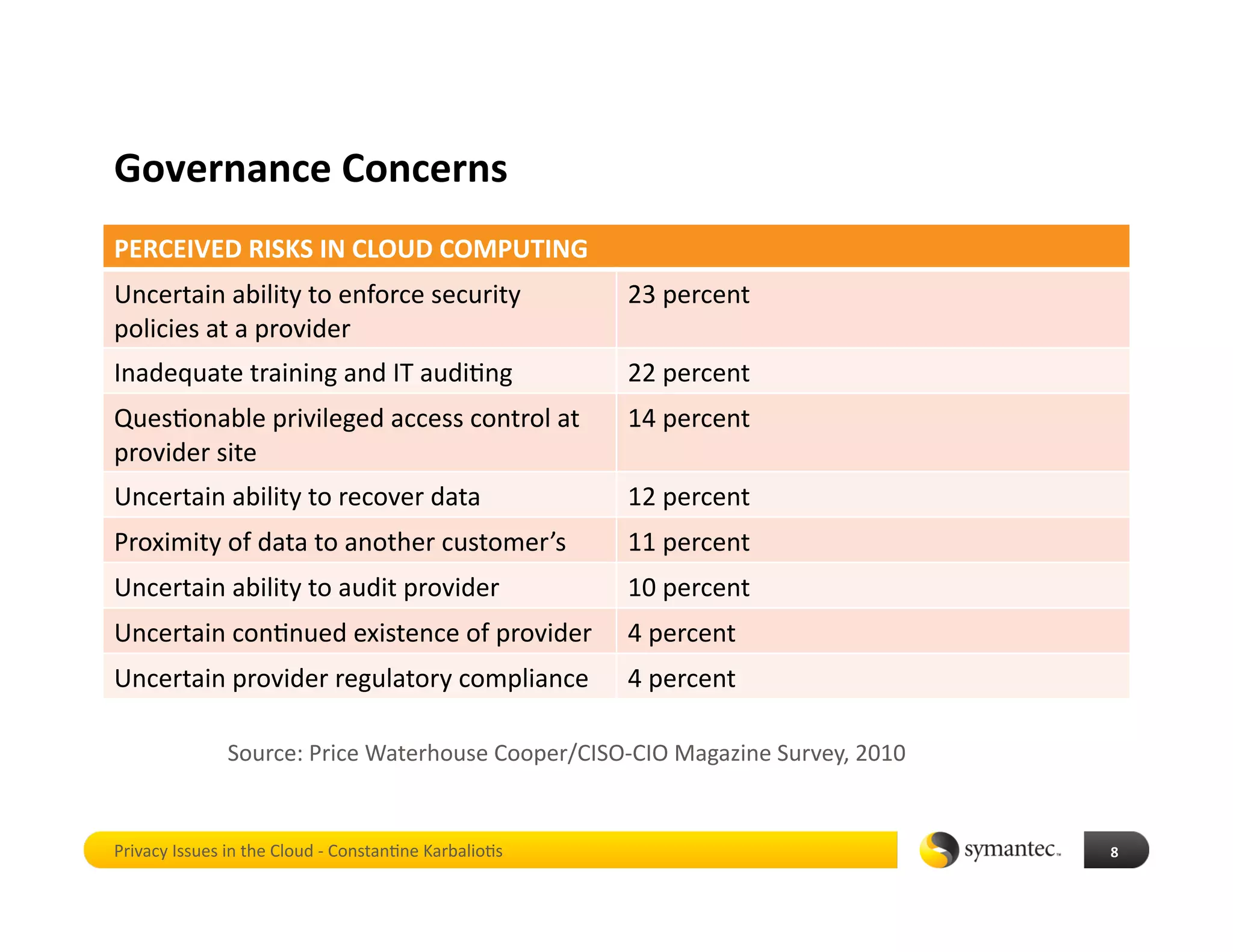
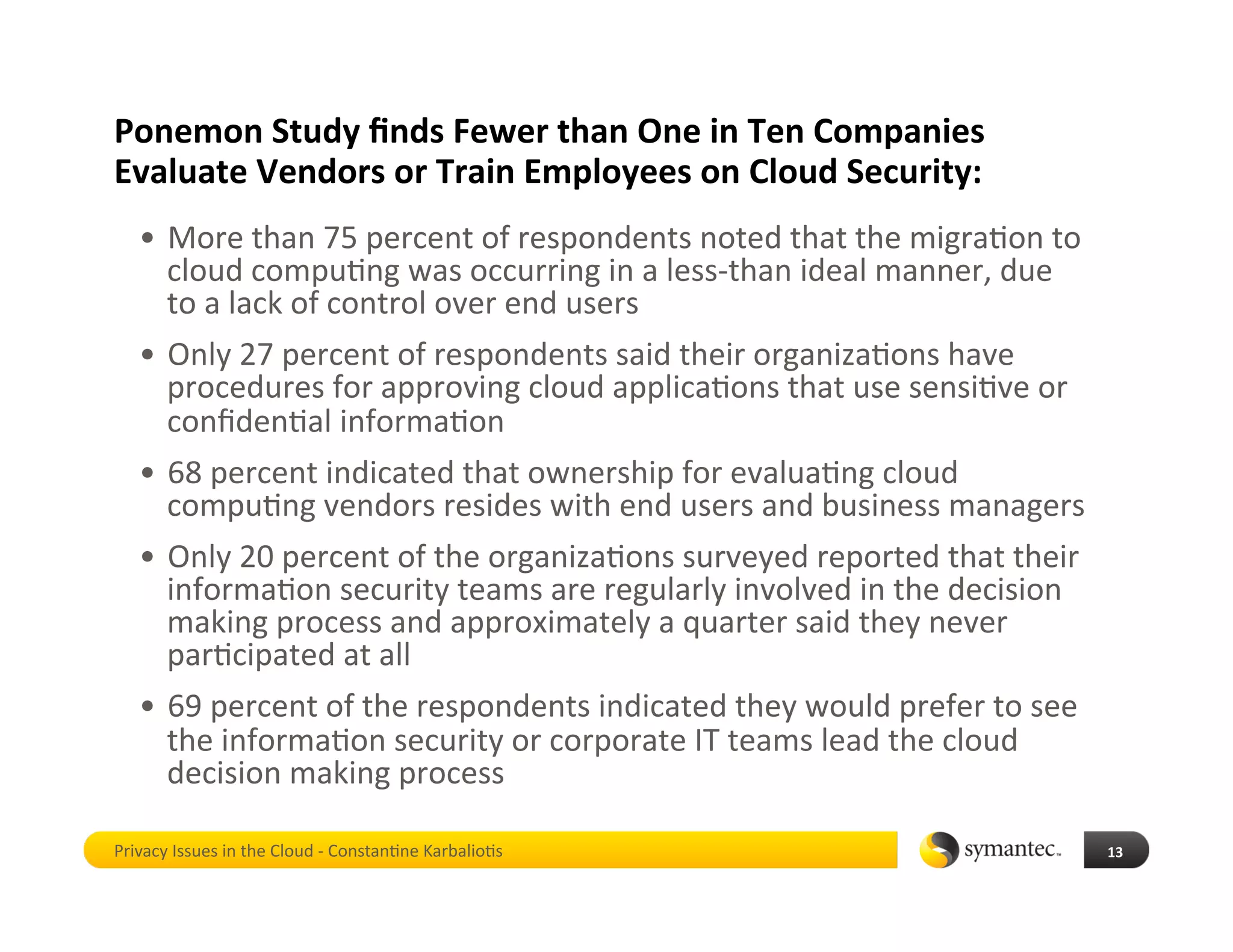
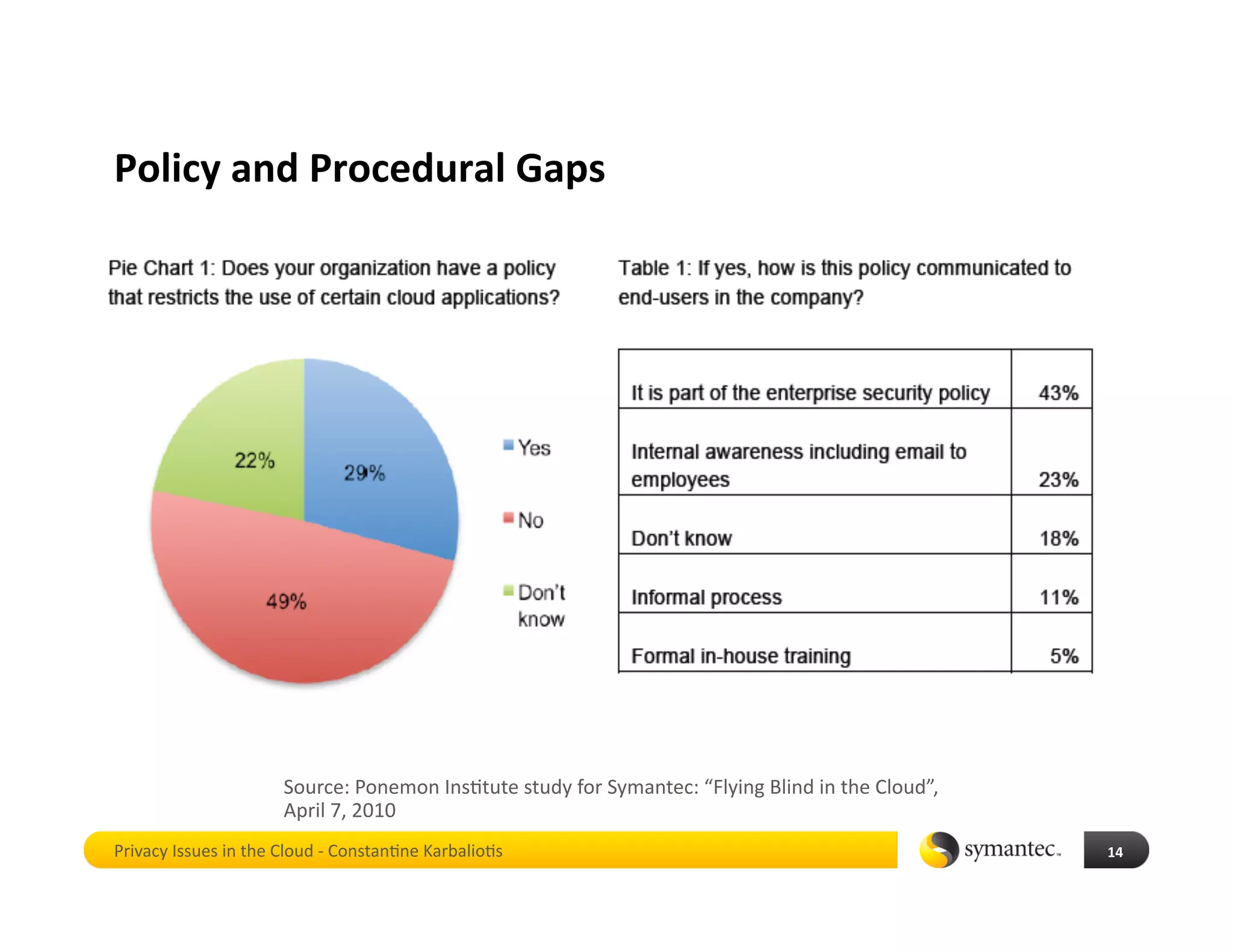
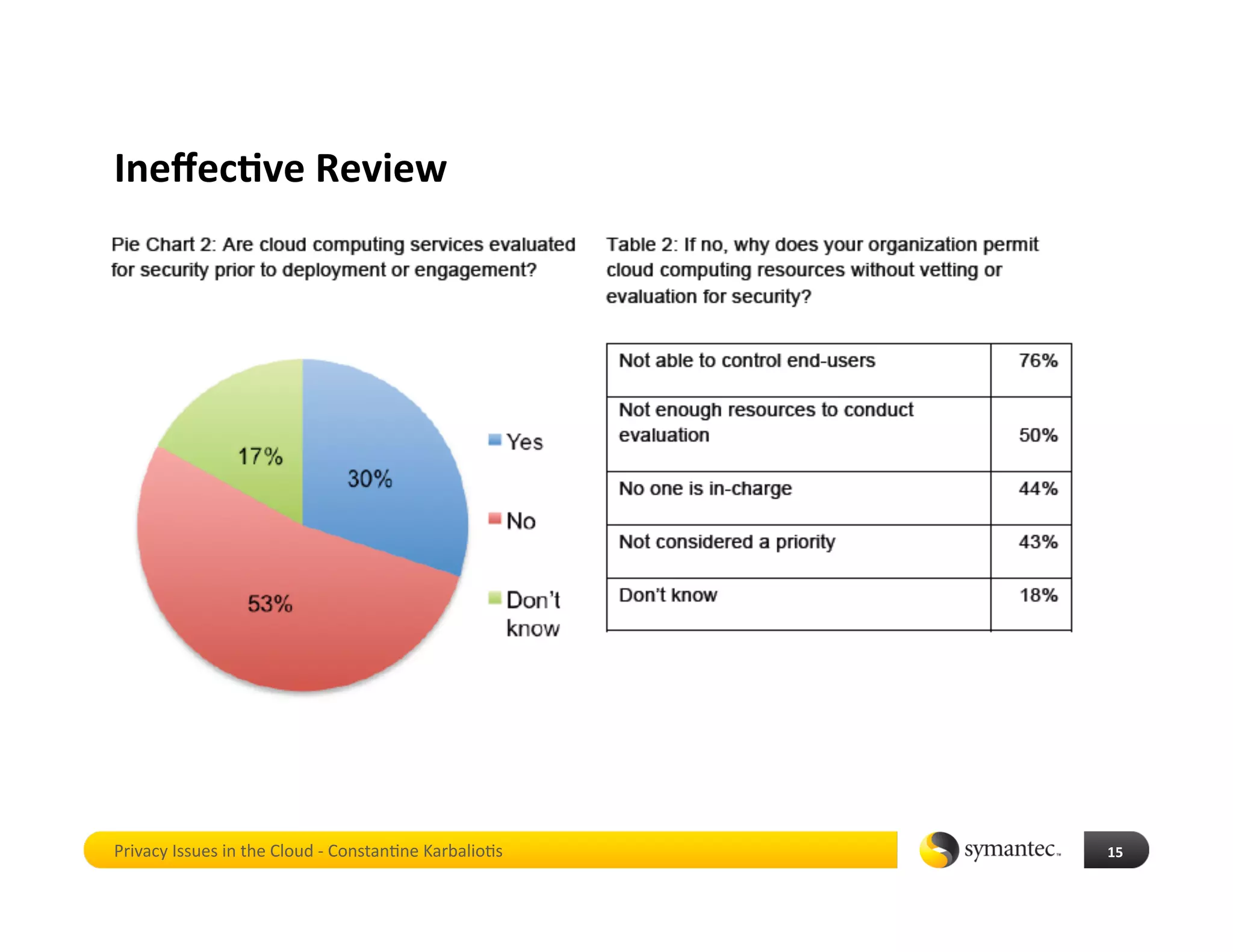
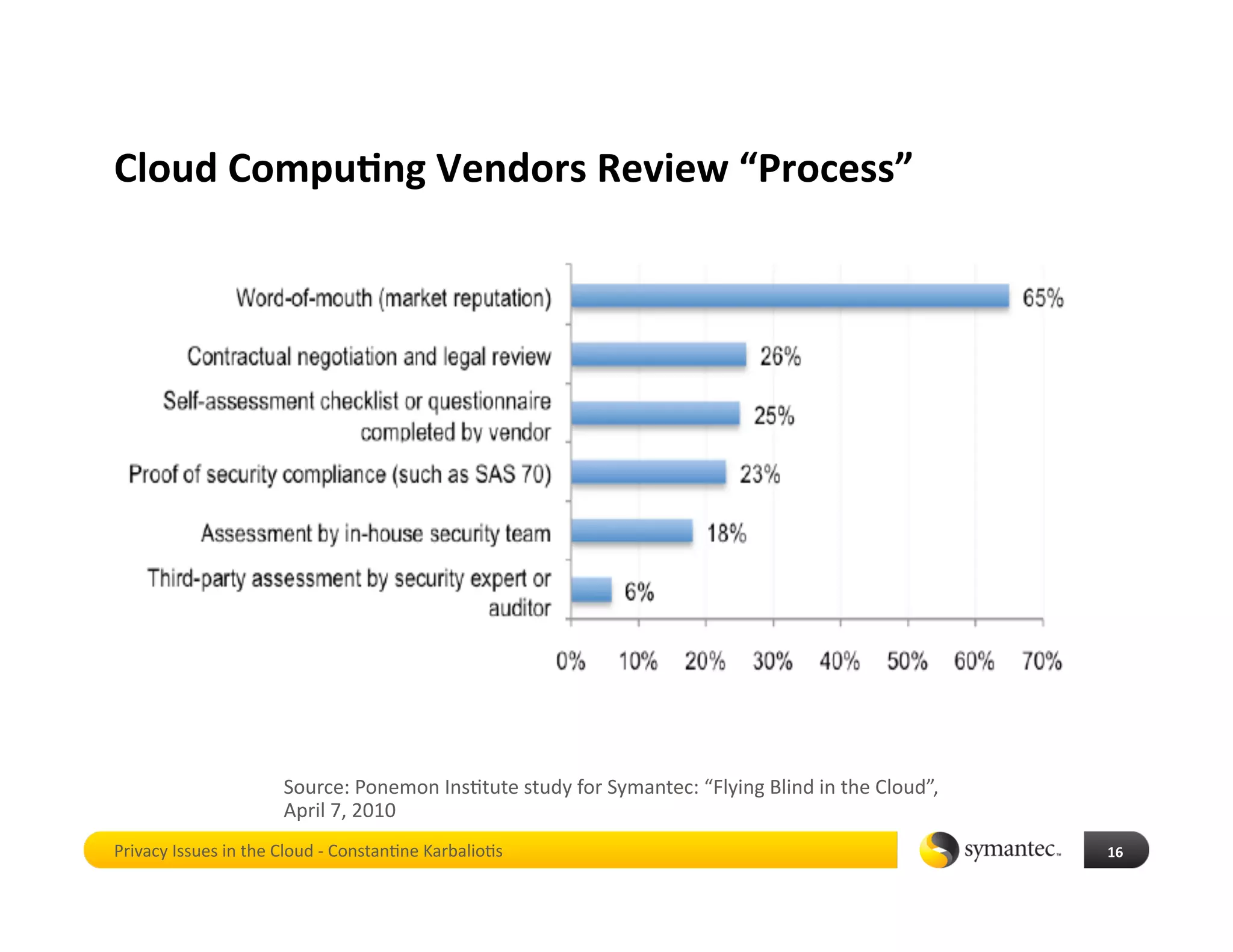
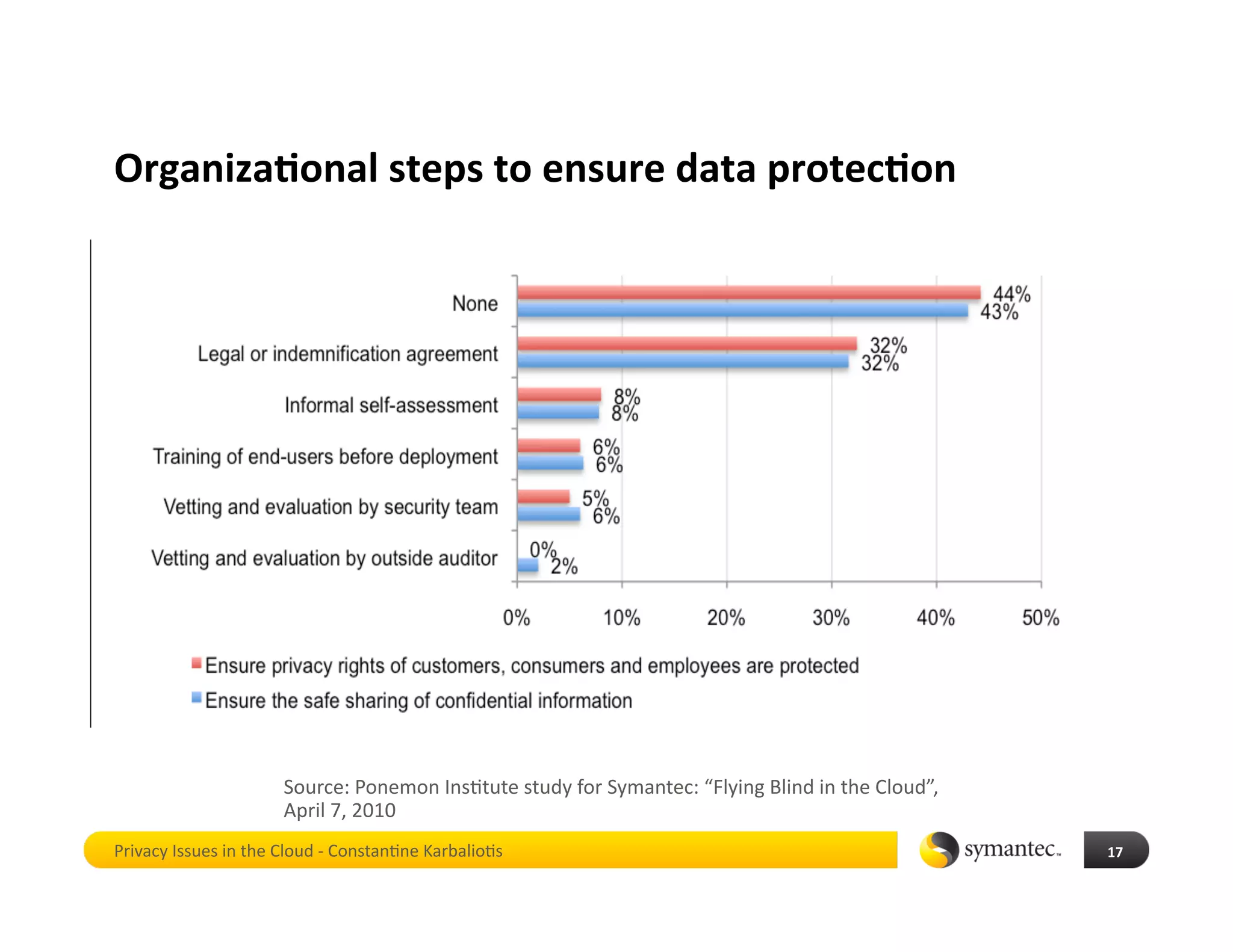
Constan4ne Karbalio4s gave a presenta4on to the Chief Privacy Officers Council on privacy issues in cloud compu4ng. He discussed that while cloud compu4ng provides benefits like cost savings and scalability, it also poses privacy and security risks if not properly governed. Research shows most organiza4ons are adop4ng cloud technologies without adequate vendor evalua4on, employee training, or privacy policies to protect sensi4ve data in the cloud. The real problem is that cloud migra4on is occurring in an ad hoc manner without proper oversight and controls, despite the growing use of cloud compu4ng by organiza4ons.