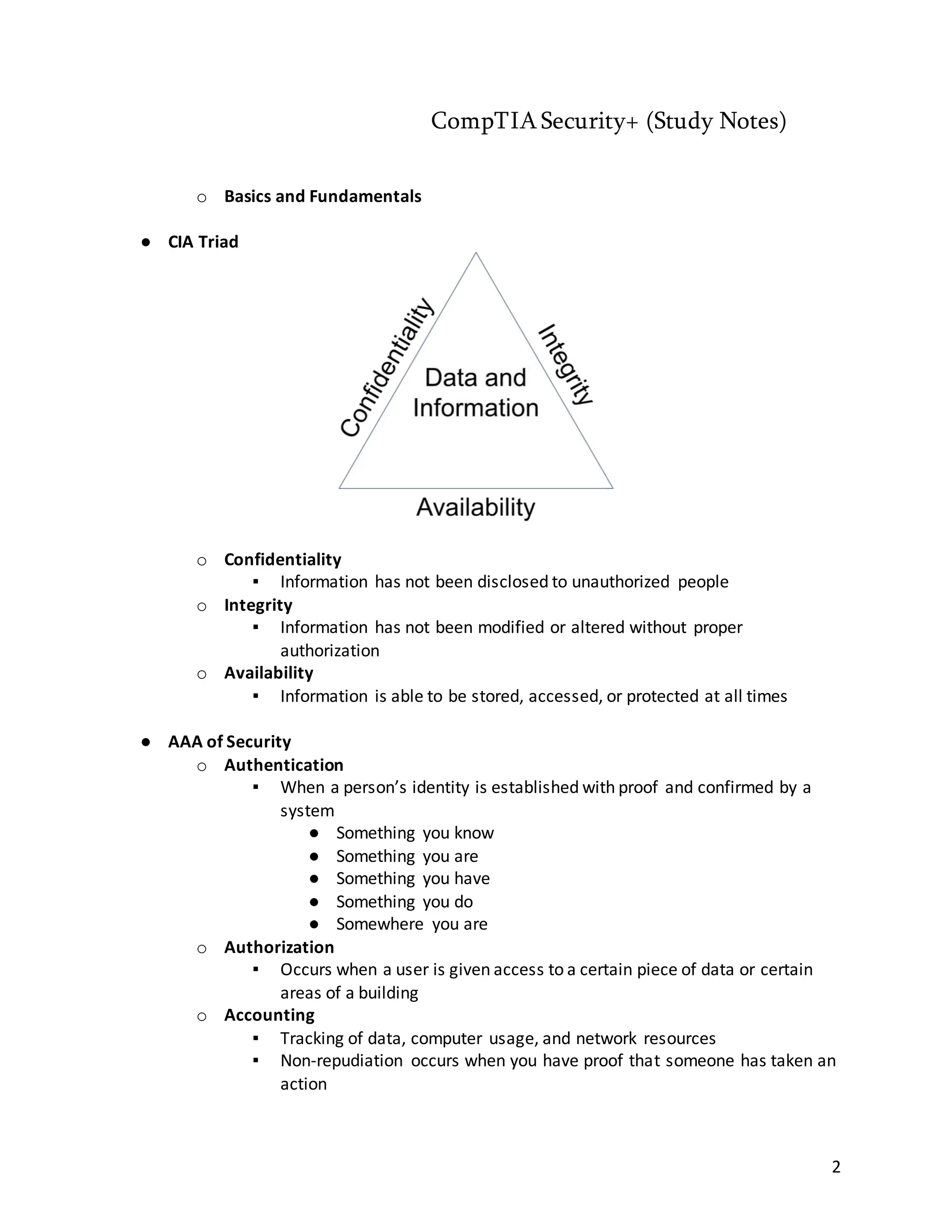
The document consists of comprehensive study notes for the CompTIA Security+ certification, detailing essential security concepts, threats, and mitigation strategies. It covers topics such as the CIA triad, various types of malware, hacker classifications, and security applications and practices necessary for protecting information systems. Additionally, it emphasizes the importance of user training, incident response, and securing mobile devices.