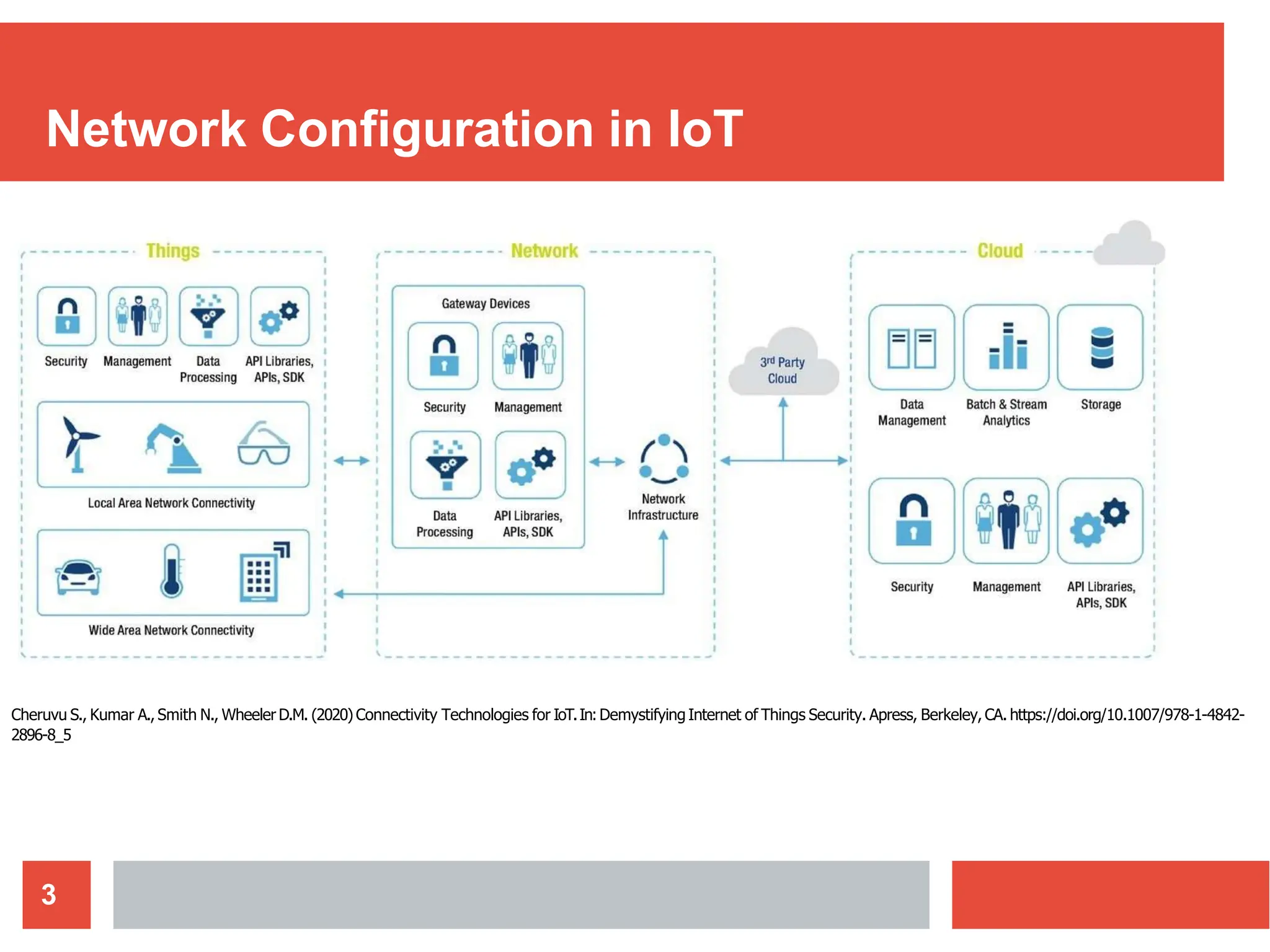
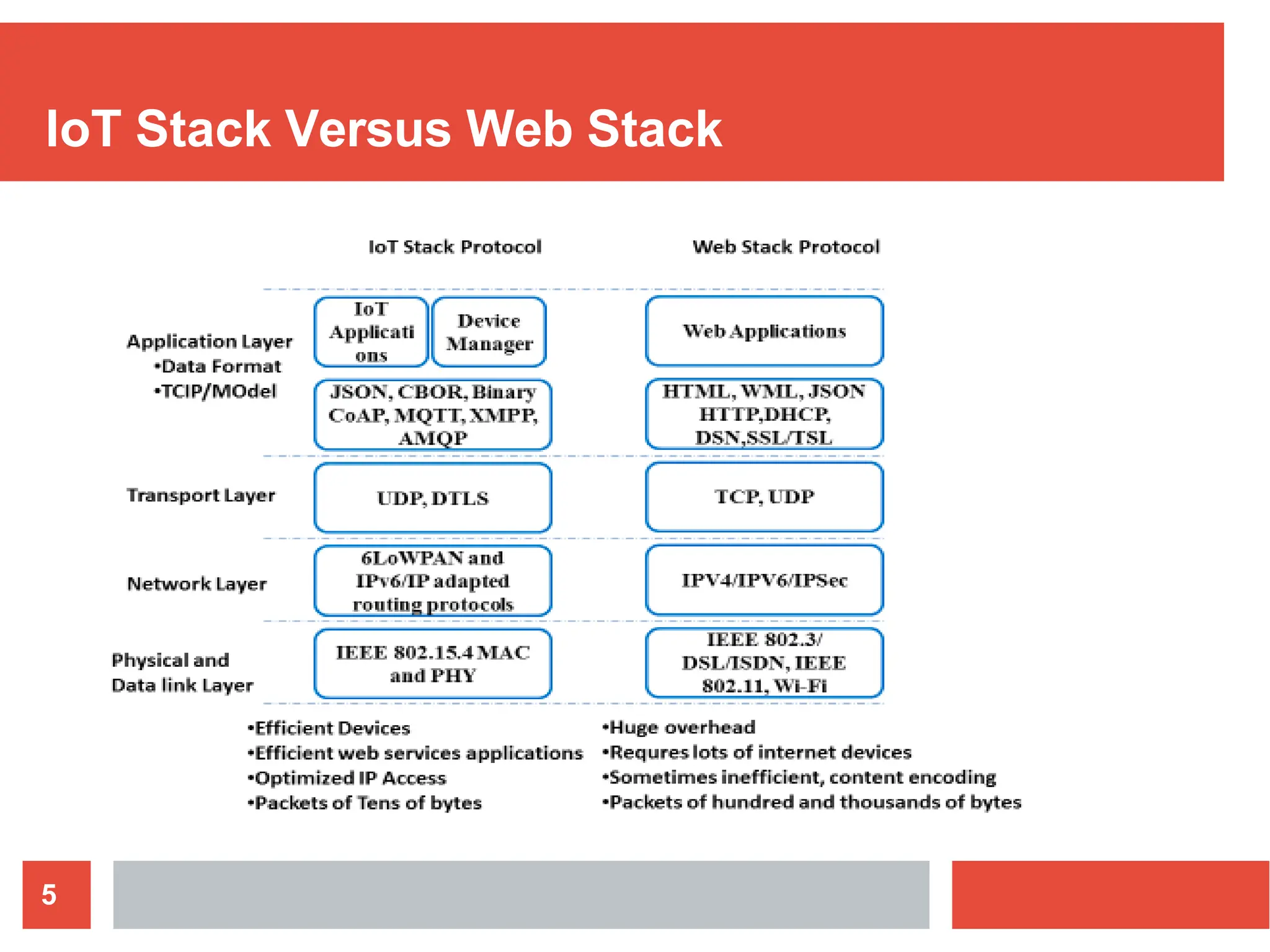
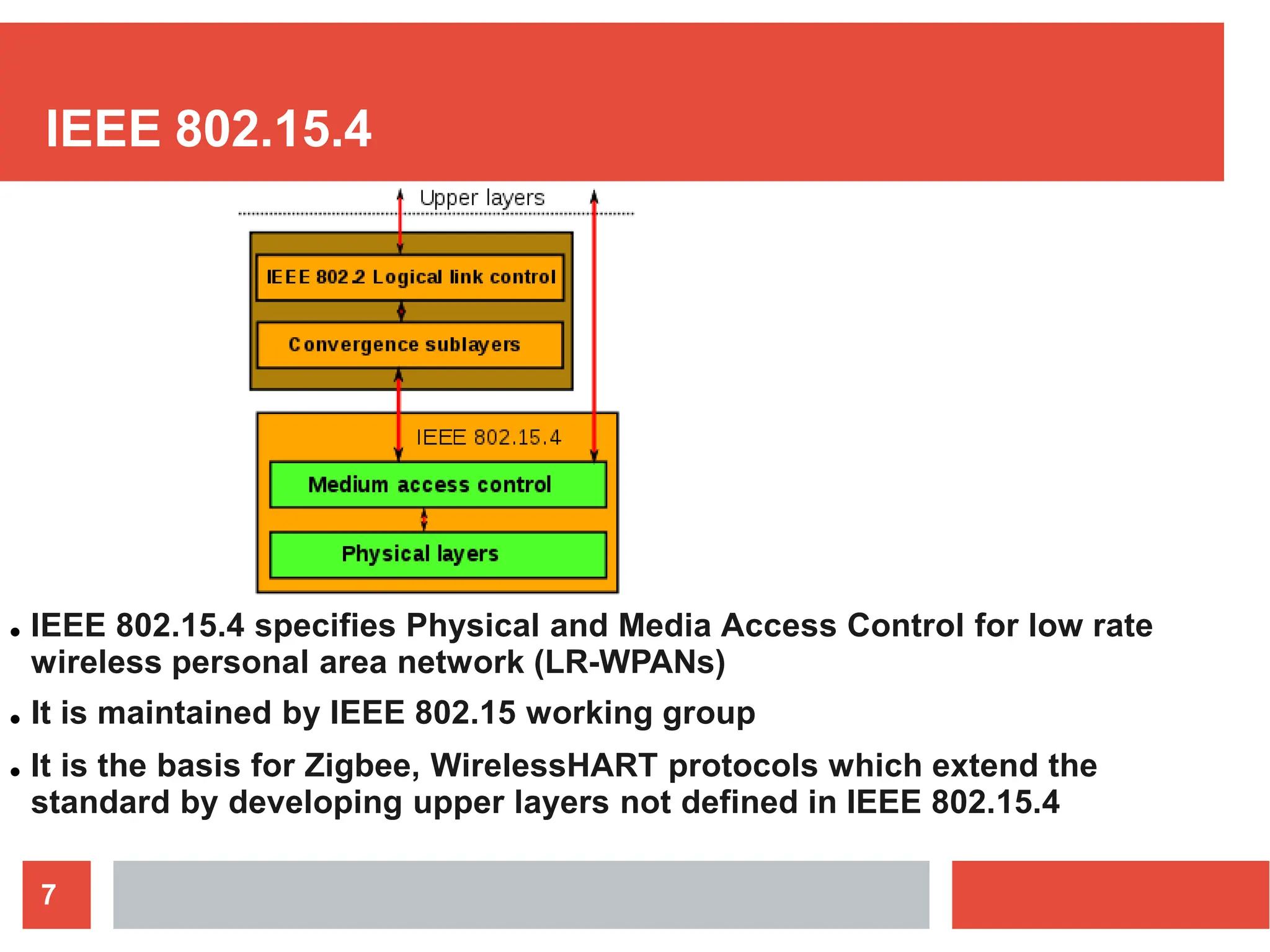
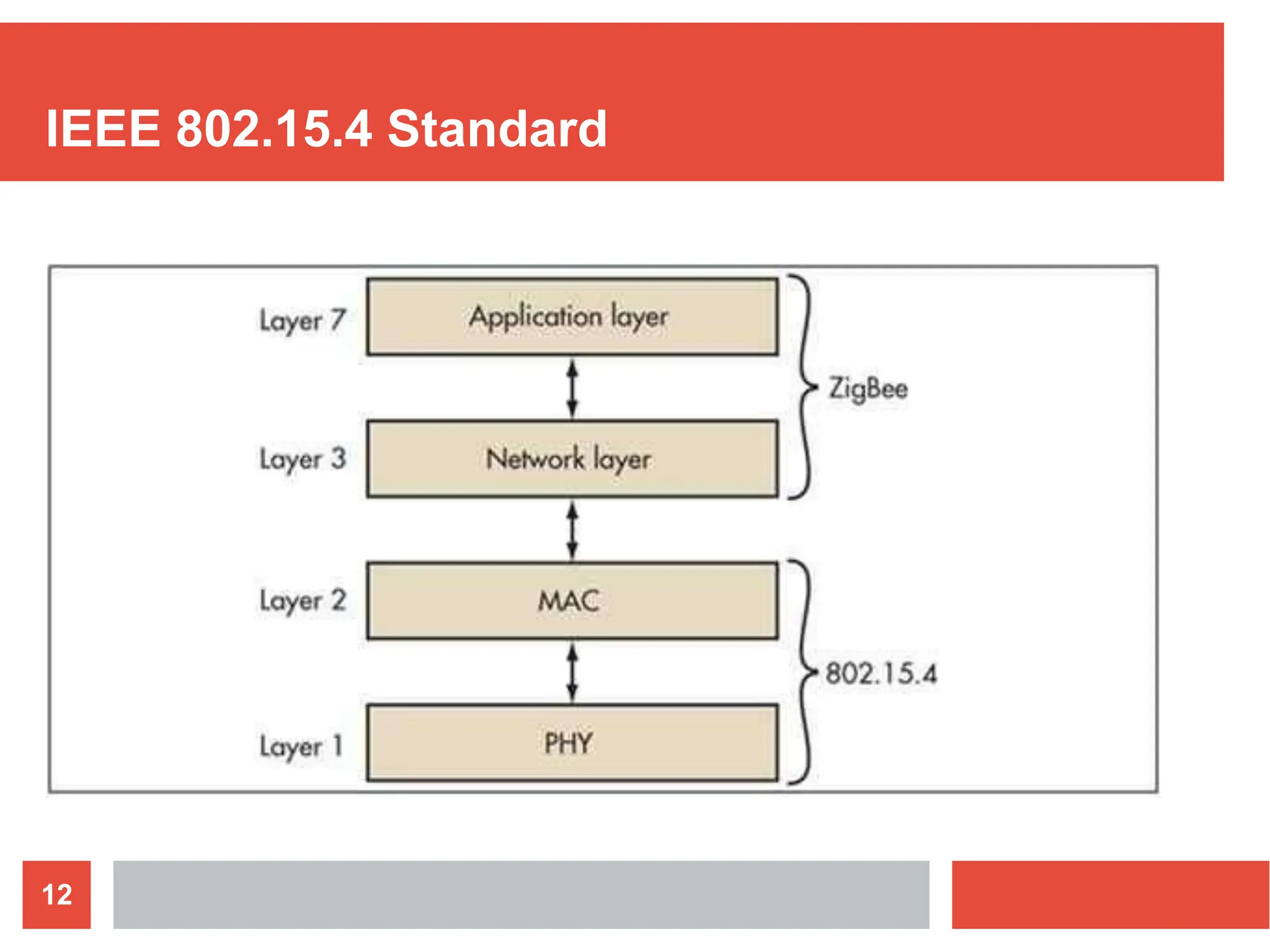
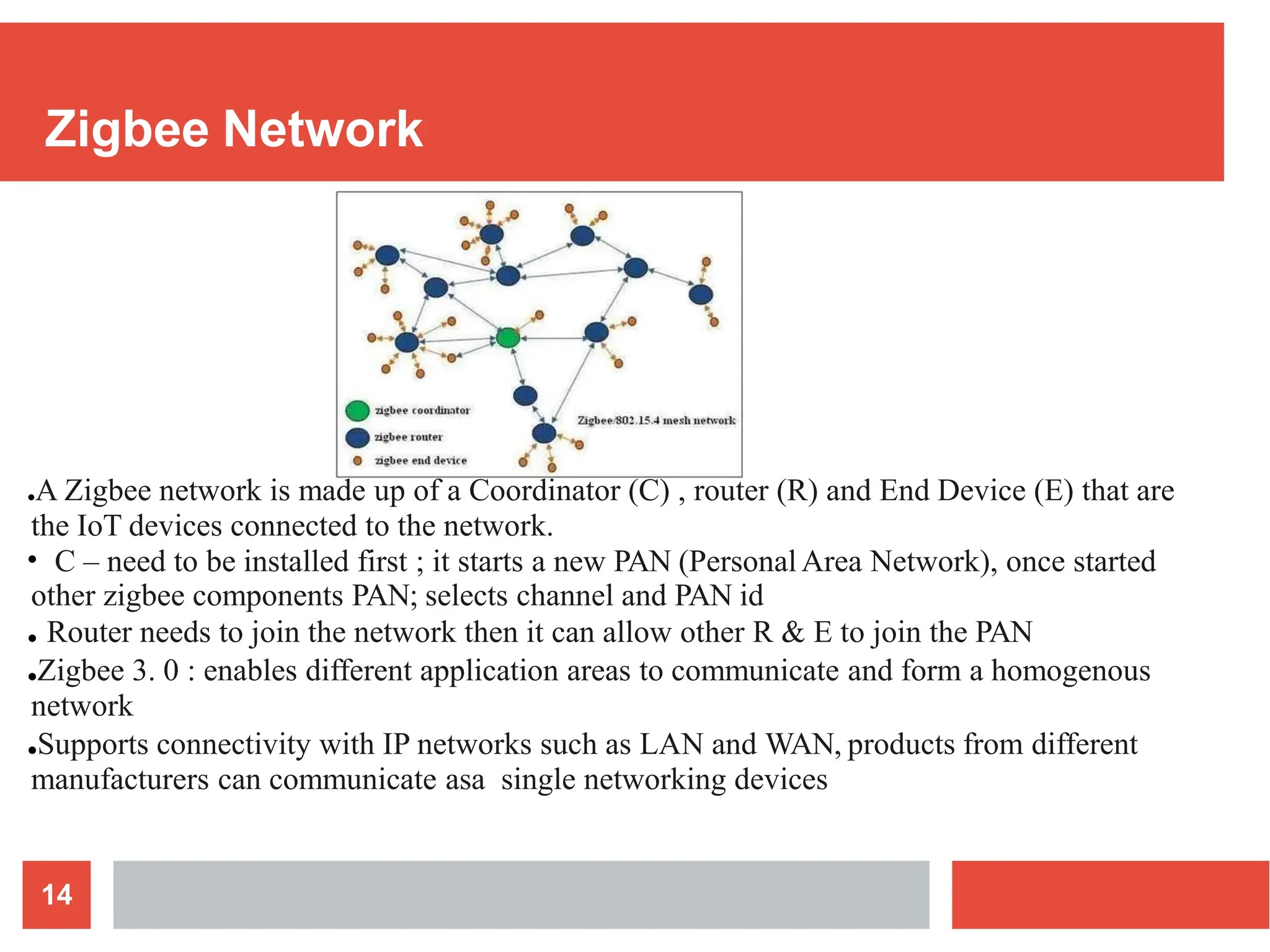
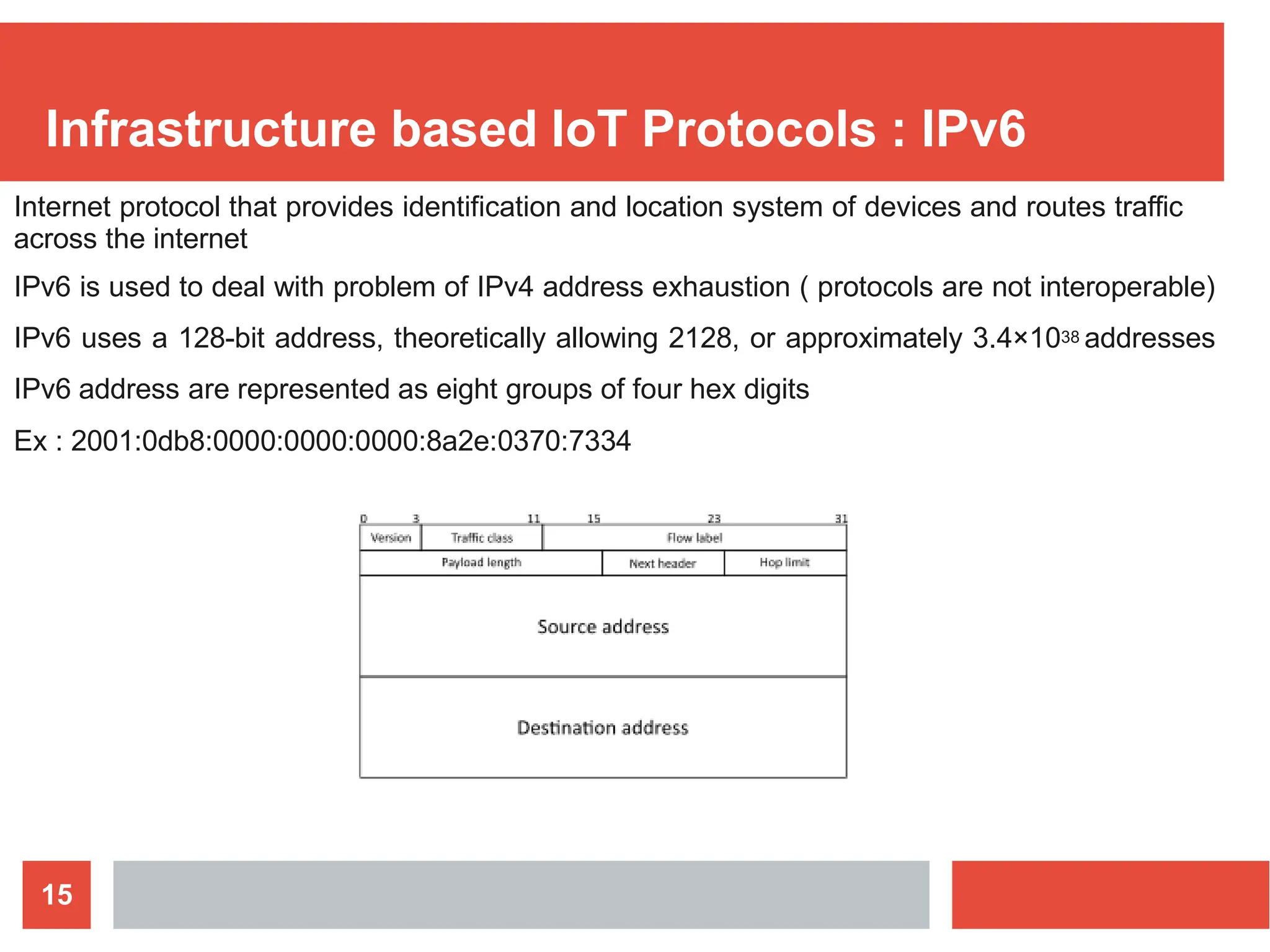
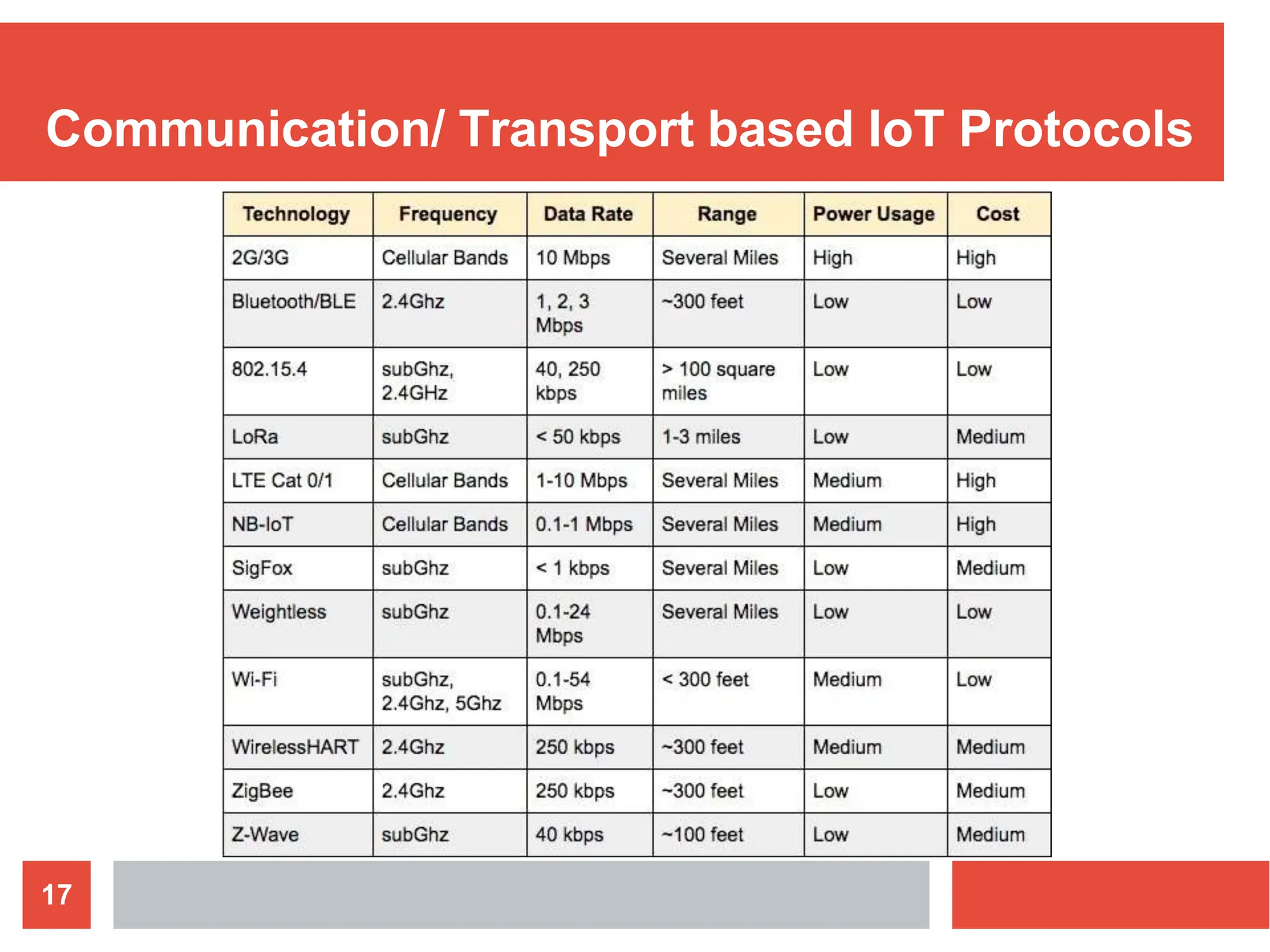
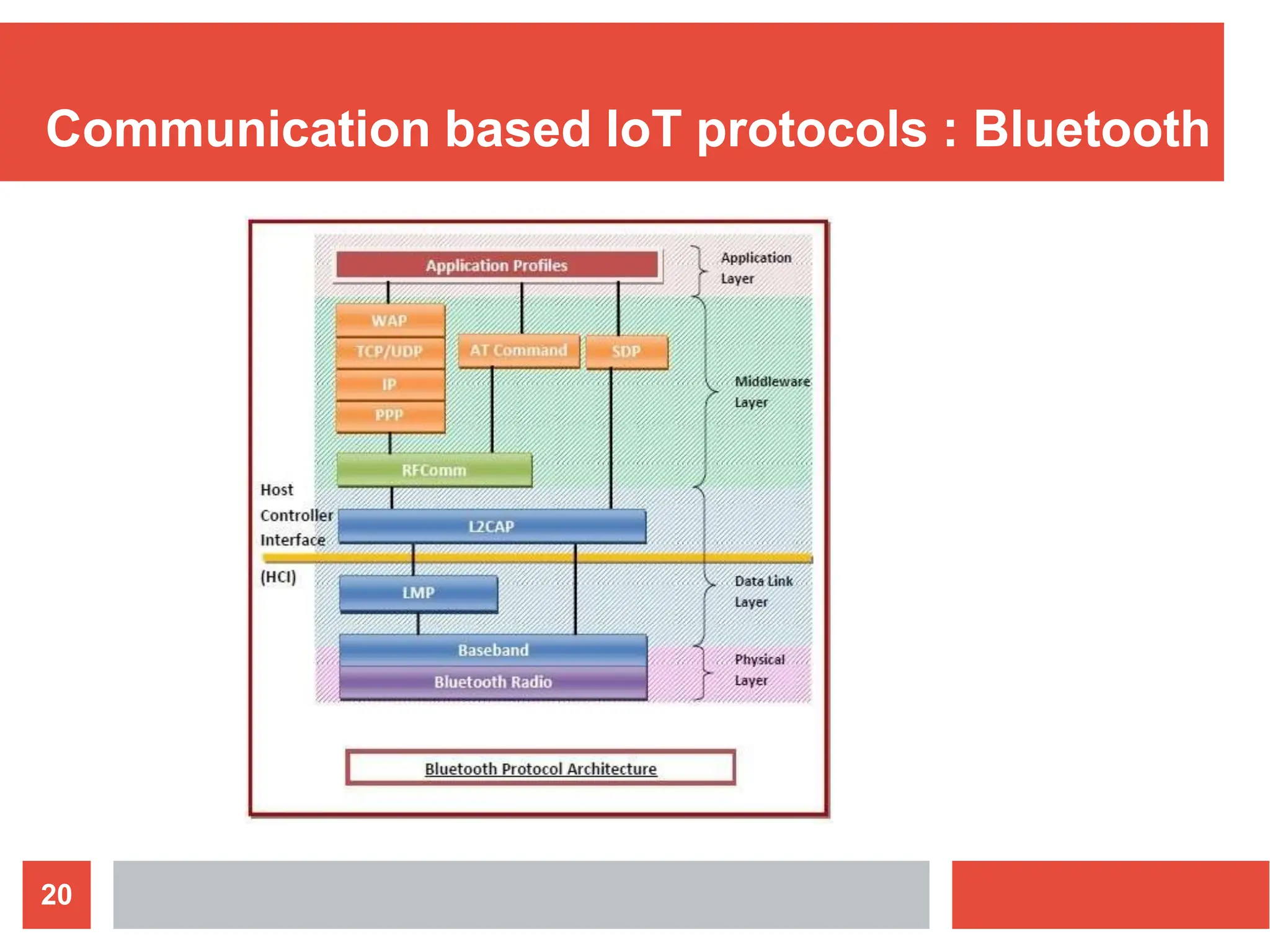
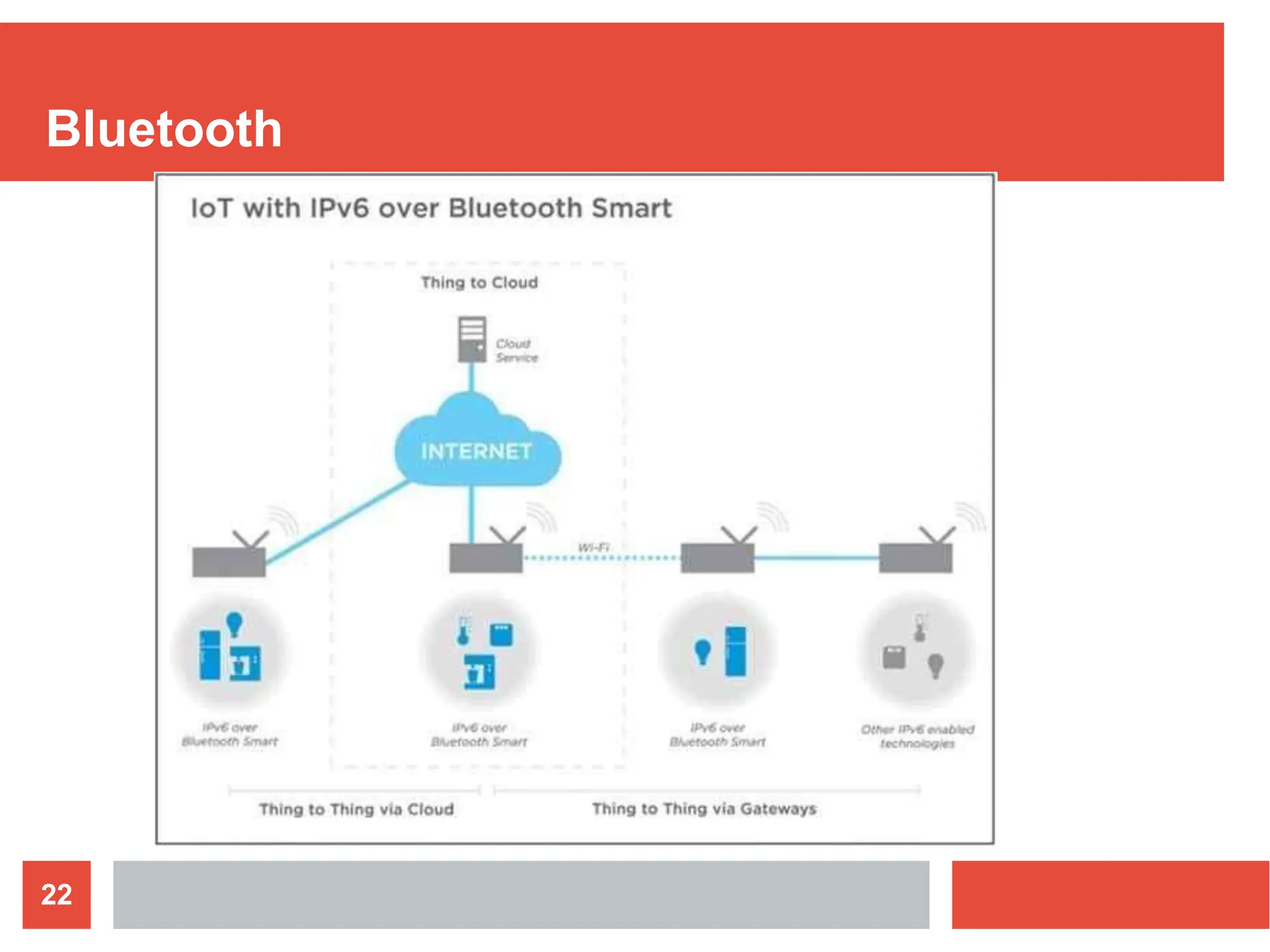
The document discusses various connectivity technologies for Internet of Things (IoT) devices. It begins by explaining that the choice of communication technology dictates hardware requirements and costs for IoT devices. It then covers network terminology like LAN, WAN, nodes and gateways. The document summarizes key IoT protocols including IEEE 802.15.4, Zigbee, IPv6, 6LoWPAN, WiFi and Bluetooth. It provides details on each protocol's features, applications, and how they enable communication at both the network and application layers for IoT. The document aims to explain the various connectivity options and standards that enable communication and networking for IoT devices.