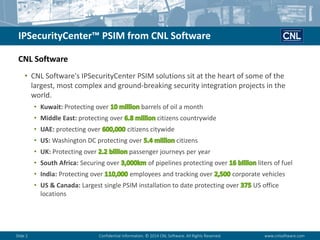
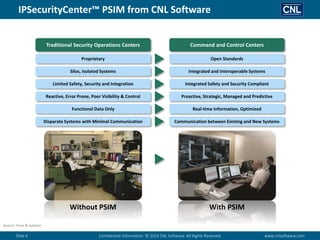
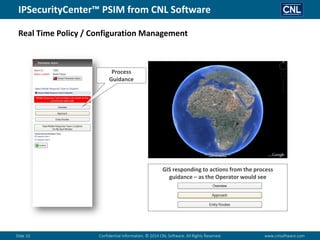
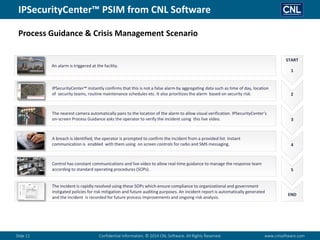
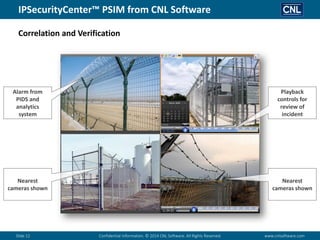
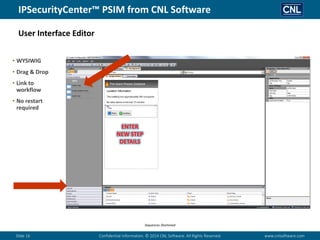
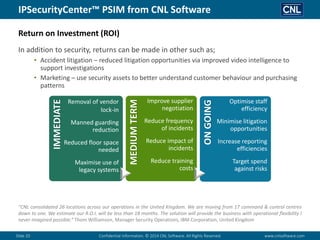
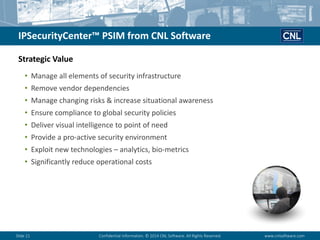
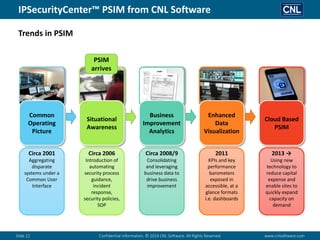
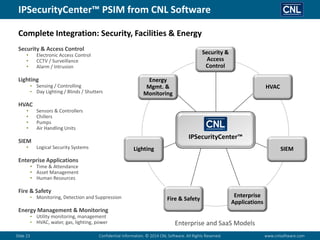
CNL Software's IP Security Center PSIM solutions integrate various security applications and devices, enabling comprehensive management of enterprise security operations. The software offers capabilities such as event collection, analysis, verification, and reporting, ultimately enhancing situational awareness and compliance with security policies. It is designed to optimize communication, reduce operational costs, and improve the efficiency of security systems across diverse market segments globally.