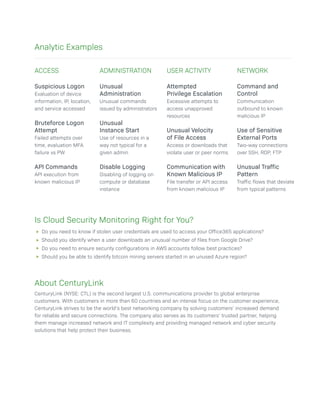
The document highlights the importance of cloud security monitoring for organizations rapidly adopting cloud services such as SaaS applications and platforms like AWS and Azure. It emphasizes the need for visibility into cloud activities and the implementation of best practice controls to mitigate risks and detect anomalies. CenturyLink is presented as a security partner that offers comprehensive monitoring solutions to protect enterprises from data breaches and misconfigurations.