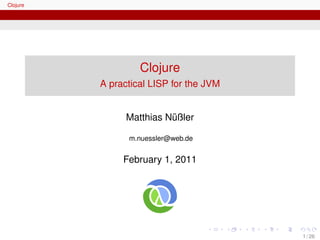
Clojure is a Lisp dialect designed for the Java Virtual Machine that focuses on functional programming and concurrency. It allows easy interoperability with Java code and provides persistent data structures and software transactional memory for writing concurrent programs that avoid deadlocks. The document provides an overview of Clojure's syntax, data structures, higher-order functions, Java interoperability features, and approach to concurrency through immutable objects and managed references.




![Clojure
The Clojure Language
Function definition
fn creates an (anonymous) function object
Similar to lambda in Scheme (and Ruby)
(fn [x] (* x x))
Or even shorter using a macro: #(* %1 %1)
Function object can be bound to a symbol
(def square (fn square [x] (* x x)))
(square 3) ; => 9
Clojure provides a convenient shortcut
def plus fn → defn
(defn square [x] (* x x))
8 / 26](https://image.slidesharecdn.com/clojure-mnuessler-110201110526-phpapp02/85/Clojure-A-practical-LISP-for-the-JVM-8-320.jpg)
![Clojure
The Clojure Language
Clojure Data Structures
Data type Example
Numbers 1, 3.14, 3/4, ...
Characters a b c
Strings "a string" → Clojure strings are Java strings
Regexps #""
Symbols a b c
Keywords :default :key
Lists (1 2 3)
Vectors [1 2 3]
Maps {:a 1, :b 2, :c 3}
Sets #{"red" "green" "blue"}
9 / 26](https://image.slidesharecdn.com/clojure-mnuessler-110201110526-phpapp02/85/Clojure-A-practical-LISP-for-the-JVM-9-320.jpg)
![Clojure
The Clojure Language
Higher Order Functions
Higher order functions functions use functions as parameters or
return values. Examples:
every?
filter
map
reduce
Factorial using reduce
1 (defn factorial [n]
2 (let [ numbers ( range 1 (+ 1 n))]
3 ( reduce * numbers )))
10 / 26](https://image.slidesharecdn.com/clojure-mnuessler-110201110526-phpapp02/85/Clojure-A-practical-LISP-for-the-JVM-10-320.jpg)


![Clojure
Java Interoperability
Calling Java from Clojure
Member Access
Invoking an instance method
1 (defn date-from-string [ date-string ]
2 (let [sdf ( SimpleDateFormat . " yyyy-MM-dd ")]
3 (. parse sdf date-string )))
Accessing a field
4 (def point (java.awt. Point . 10 20))
5 (.x point ) ; => 10
Invoking static methods
6 (Long/ parseLong " 12321 ")
7 ( Thread / sleep 3000)
13 / 26](https://image.slidesharecdn.com/clojure-mnuessler-110201110526-phpapp02/85/Clojure-A-practical-LISP-for-the-JVM-13-320.jpg)

![Clojure
Java Interoperability
Calling Java from Clojure
Calling multiple methods on a Java object
Long version
1 ( import ’(java.util Calendar ))
2 (defn the-past-midnight-1 []
3 (let [ calendar-obj ( Calendar / getInstance )]
4 (. set calendar-obj Calendar / AM_PM Calendar /AM)
5 (. set calendar-obj Calendar /HOUR 0)
6 (. set calendar-obj Calendar / MINUTE 0)
7 (. set calendar-obj Calendar / SECOND 0)
8 (. set calendar-obj Calendar / MILLISECOND 0)
9 (. getTime calendar-obj )))
15 / 26](https://image.slidesharecdn.com/clojure-mnuessler-110201110526-phpapp02/85/Clojure-A-practical-LISP-for-the-JVM-15-320.jpg)
![Clojure
Java Interoperability
Calling Java from Clojure
Calling multiple methods on a Java object
Shorter using the doto macro
1 (defn the-past-midnight-2 []
2 (let [ calendar-obj ( Calendar / getInstance )]
3 (doto calendar-obj
4 (. set Calendar / AM_PM Calendar /AM)
5 (. set Calendar /HOUR 0)
6 (. set Calendar / MINUTE 0)
7 (. set Calendar / SECOND 0)
8 (. set Calendar / MILLISECOND 0))
9 (. getTime calendar-obj )))
16 / 26](https://image.slidesharecdn.com/clojure-mnuessler-110201110526-phpapp02/85/Clojure-A-practical-LISP-for-the-JVM-16-320.jpg)
![Clojure
Java Interoperability
Calling Java from Clojure
Implementing interfaces / extending classes
With proxy
1 (defn action-listener [idx frei buttons ]
2 (proxy [java.awt. event . ActionListener ] []
3 ( actionPerformed [e]
4 (...))))
17 / 26](https://image.slidesharecdn.com/clojure-mnuessler-110201110526-phpapp02/85/Clojure-A-practical-LISP-for-the-JVM-17-320.jpg)
![Clojure
Java Interoperability
Calling Clojure from Java
Calling Clojure from Java
1 import clojure .lang.RT;
2 import clojure .lang.Var;
3
4 public class Driver {
5 public static void main( String [] args) throws Exceptio
6 RT. loadResourceScript (" clojure_script .clj");
7 Var report = RT.var("clj. script . examples ", " print-re
8 Integer result = ( Integer ) report . invoke ("Siva");
9 System .out. println ("[Java] Result : " + result );
10 }
11 }
18 / 26](https://image.slidesharecdn.com/clojure-mnuessler-110201110526-phpapp02/85/Clojure-A-practical-LISP-for-the-JVM-18-320.jpg)