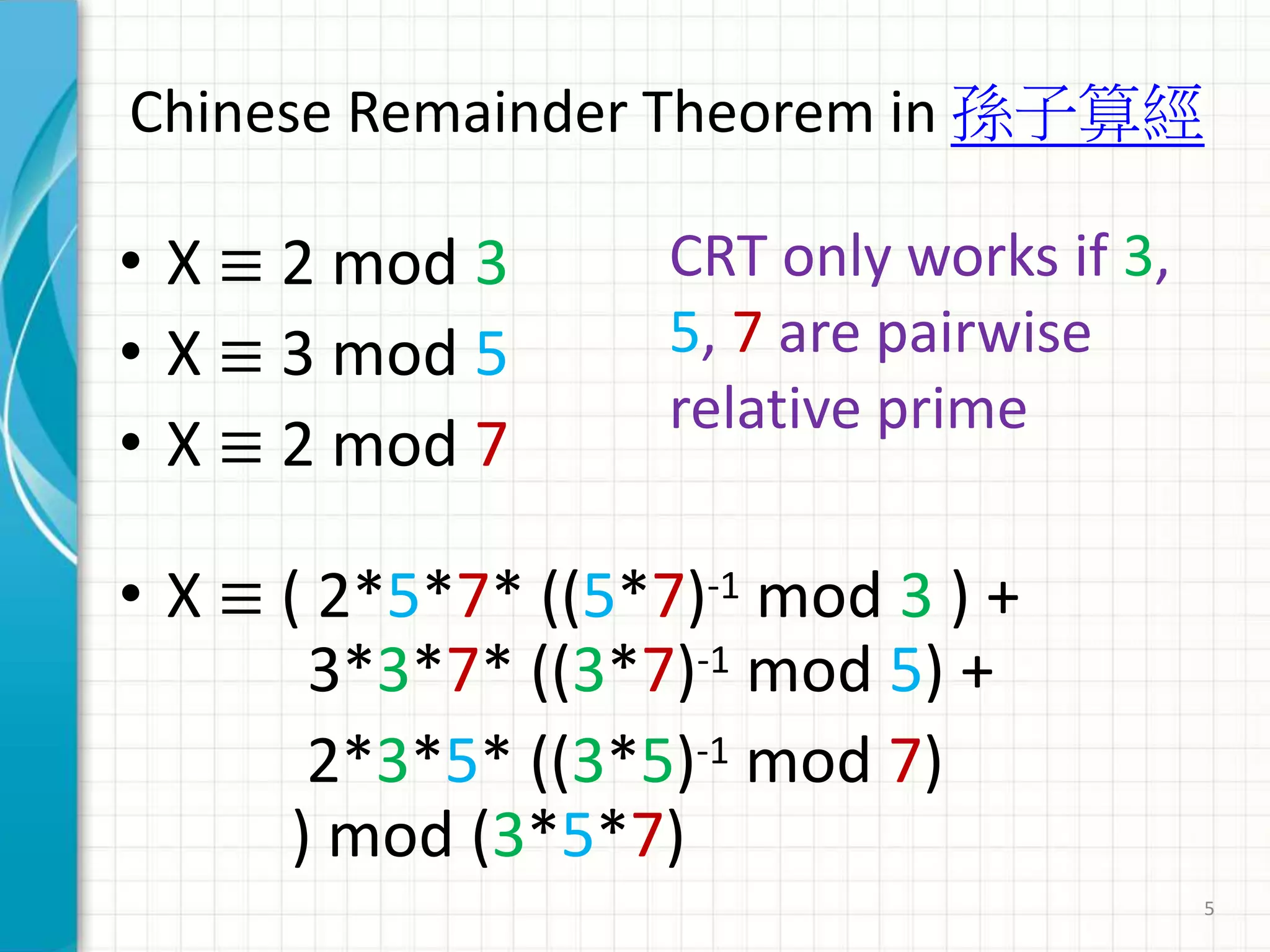
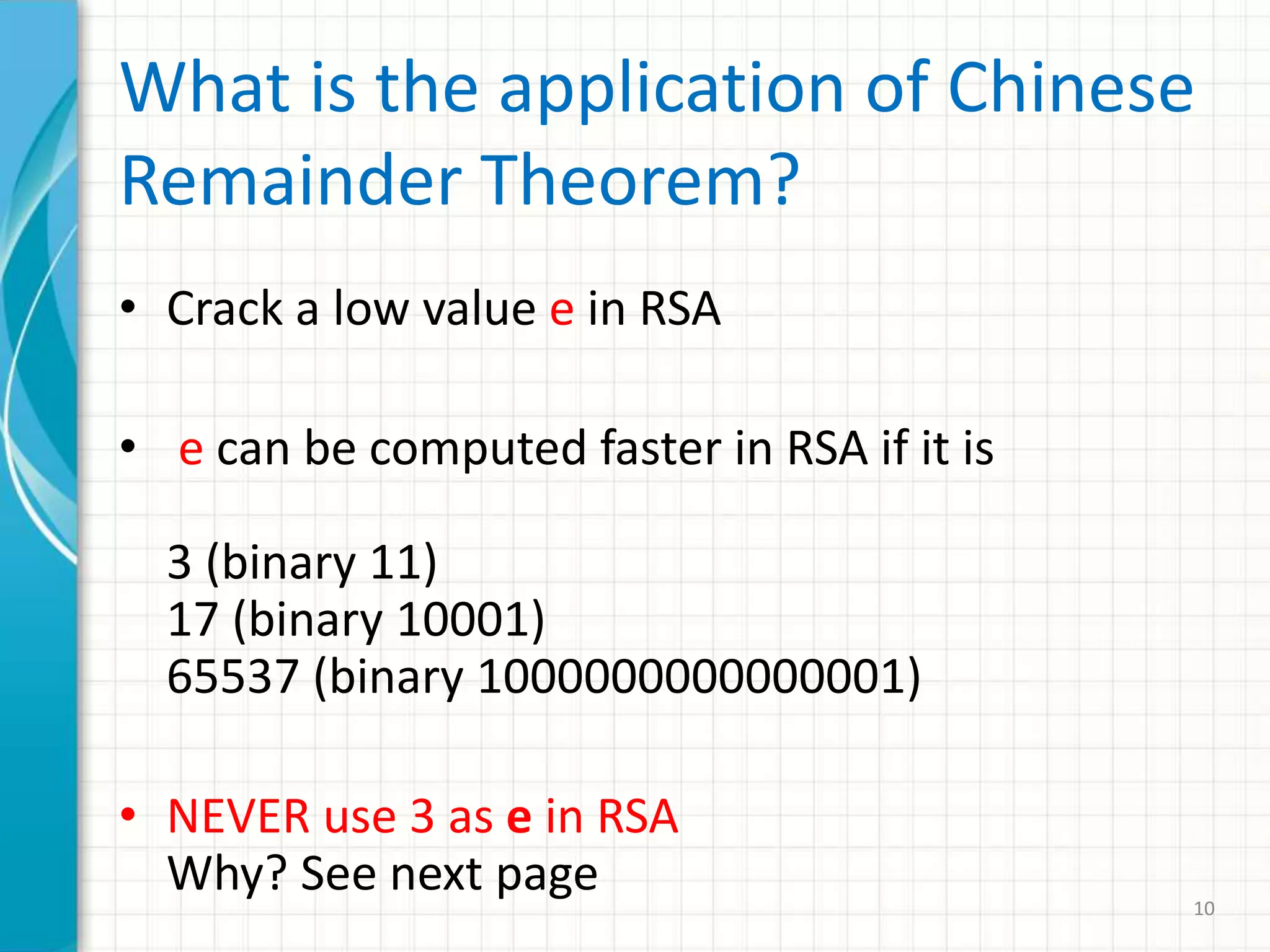
The document discusses the Chinese Remainder Theorem (CRT). It provides an example problem from the Sunzi Suanjing text dated between AD 300-470 involving finding an unknown number X given its remainders when divided by 3, 5, and 7. The CRT provides a formula to solve such systems of simultaneous congruences. The document also discusses applications of CRT in cryptography, including cracking low exponent RSA encryption and its use in general simultaneous modular equations.









![• Find 11-1 mod 3220 by Extended Euclidean Algorithm
• 3220 = 11 * 292 + 8 -> ( 8 = 3220 – 11 * 292 ) [1]
• 11 = 8 * 1 + 3 -> ( 3 = 11 – 8 * 1 ) [2]
• 8 = 3 * 2 + 2 -> ( 2 = 8 – 3 * 2 ) [3]
• 3 = 2 * 1 + 1 (First phase finish when the remainder is 1, start second phase)
• Reverse the steps by rearranging the equations
• 1 = 3 – 2 * 1 (using [3])
• 1 = 3 – (8-3*2) * 1
• 1 = 3 – 8 + 3 * 2
• 1 = 3 * 3 – 8 (using [2])
• 1 = (11-8*1) *3 – 8
• 1 = 3*11 - 8*3 – 8
• 1 = 3 * 11 – 8 * 4 (using [1])
• 1 = 3 * 11 – ( 3220 – 11 * 292 ) * 4 (Keep 11 and 3220 as two variables)
• 1 = 3 * 11 – 3220 * 4 + 4 * 11 * 292 (compute the other values)
• 1 = 11 * ( 3 + 4 * 292 ) – 3220 * 4
• 1 = 11 * 1171 – 3220 * 4 (Answer is 1171 )
11-1 mod 3220 = 1171
11*t = 3220*X+1 X any number < 11
13
It appears using Extended Euclidean Algorithm is
slower than tries and errors
In this special case because 11 is small and you only
need to try 10 times
If the value of Y in Y-1 mod M = R is large
Extended Euclidean Algorithm is much faster](https://image.slidesharecdn.com/chineseremaindertheorem-220403113907/75/Chinese_Remainder_Theorem-pptx-13-2048.jpg)
