Chapter-6.1---Communication-Apps-(SAMPLE).pdf
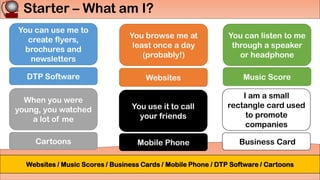
- 1. Starter – What am I? You can use me to create flyers, brochures and newsletters You browse me at least once a day (probably!) You can listen to me through a speaker or headphone When you were young, you watched a lot of me You use it to call your friends I am a small rectangle card used to promote companies DTP Software Websites Music Score Cartoons Mobile Phone Business Card Websites / Music Scores / Business Cards / Mobile Phone / DTP Software / Cartoons
- 2. IGCSE ICT Chapter 6 ICT Applications
- 3. • Identify a range of communication applications Must • Describe the use of internet telephony, including Voice over Internet Protocol (VoIP) Should • Evaluate the use of applications for public and corporate publications Could Learning Objectives 6.1 Communication applications
- 4. 1. Identify a range of communication applications 2. Describe the use of internet telephony, including Voice over Internet Protocol (VoIP) 3. Evaluate the use of applications for public and corporate publications L/A: To identify common hardware components in a computer system and how they function My Learning Objectives What is “Communication”? Write a definition in your booklets now! “the act of transferring information from one place, person or group to another.”
- 5. 1. Identify a range of communication applications 2. Describe the use of internet telephony, including Voice over Internet Protocol (VoIP) 3. Evaluate the use of applications for public and corporate publications L/A: To identify common hardware components in a computer system and how they function My Learning Objectives Mind Map Communication methods
- 6. 1. Identify a range of communication applications 2. Describe the use of internet telephony, including Voice over Internet Protocol (VoIP) 3. Evaluate the use of applications for public and corporate publications L/A: To identify common hardware components in a computer system and how they function My Learning Objectives Flyers, Posters, Brochures & Newsletters •Flyers and posters can be produced very easily using various software packages • Word processor • DTP (Desktop Publishing) •Images will be taken from the internet to use in the flyer or poster
- 7. 1. Identify a range of communication applications 2. Describe the use of internet telephony, including Voice over Internet Protocol (VoIP) 3. Evaluate the use of applications for public and corporate publications L/A: To identify common hardware components in a computer system and how they function My Learning Objectives Steps in creating a poster… 1. Open a word processor, DTP application 2. Create frames, boxes and text boxes 3. Take photos using a camera 4. Upload the images, scan photos, or download form the internet 5. Save photos to a file 6. Import or copy and paste into the document 7. Edit the photos and type the text required
- 8. 1. Identify a range of communication applications 2. Describe the use of internet telephony, including Voice over Internet Protocol (VoIP) 3. Evaluate the use of applications for public and corporate publications L/A: To identify common hardware components in a computer system and how they function My Learning Objectives Differences in each • Using your course books, identify the differences between a brochure, flyer and poster
- 9. 1. Identify a range of communication applications 2. Describe the use of internet telephony, including Voice over Internet Protocol (VoIP) 3. Evaluate the use of applications for public and corporate publications L/A: To identify common hardware components in a computer system and how they function My Learning Objectives Websites • Rather than producing flyers/posters by printing them this method of advertising requires the development of a website • Can develop themselves** • Must have their own team of developers • Need necessary hardware/software • Ensure it’s safe from hackers • EXPENSIVE! • Pay another company to do it
- 10. 1. Identify a range of communication applications 2. Describe the use of internet telephony, including Voice over Internet Protocol (VoIP) 3. Evaluate the use of applications for public and corporate publications L/A: To identify common hardware components in a computer system and how they function My Learning Objectives Task! Comparing Websites & Posters •Compare and contrast Websites to Paper advertising methods by listing 3 advantages and 3 disadvantages of using a Website to advertise
- 11. 1. Identify a range of communication applications 2. Describe the use of internet telephony, including Voice over Internet Protocol (VoIP) 3. Evaluate the use of applications for public and corporate publications L/A: To identify common hardware components in a computer system and how they function My Learning Objectives Task! Comparing Websites & Posters • Advantages • Can add sound, video, links and animation • Use of hotspots • Buttons to navigate and move around the website • Global audience • Can’t be thrown away or defaced • Easy to update rather than printing new versions • Disadvantages • Can be hacked / pharmed • Need to maintain website to keep it up to date • Necessary for the customer to have a computer and internet • Harder to hit target audience. Advertising requires skills
- 12. 1. Identify a range of communication applications 2. Describe the use of internet telephony, including Voice over Internet Protocol (VoIP) 3. Evaluate the use of applications for public and corporate publications L/A: To identify common hardware components in a computer system and how they function My Learning Objectives Task! Comparing Websites & Posters •Continue research into 3 other methods of advertising using ICT and make notes in your booklet
- 13. • Identify a range of communication applications Must • Describe the use of internet telephony, including Voice over Internet Protocol (VoIP) Should • Evaluate the use of applications for public and corporate publications Could Checkpoint 1
- 14. 1. Identify a range of communication applications 2. Describe the use of internet telephony, including Voice over Internet Protocol (VoIP) 3. Evaluate the use of applications for public and corporate publications L/A: To identify common hardware components in a computer system and how they function My Learning Objectives Internet Telephony (VoIP) • Method used to talk with people using the internet • Voice over Internet Protocol • Usually free (or cheaper) anywhere in the world if both computers have VoIP telephones • Webcam also used to provide video conferencing
- 15. • Identify a range of communication applications Must • Describe the use of internet telephony, including Voice over Internet Protocol (VoIP) Should • Evaluate the use of applications for public and corporate publications Could Checkpoint 2
- 16. 1. Identify a range of communication applications 2. Describe the use of internet telephony, including Voice over Internet Protocol (VoIP) 3. Evaluate the use of applications for public and corporate publications L/A: To identify common hardware components in a computer system and how they function My Learning Objectives Business Cards and letterheads • Business cards are used by companies for many reasons: • Professionalism • A brand awareness (advertises the company) • Legal reasons (if anyone takes legal action, they have proof of communication in letterheads) • Advertising their product/serivce • Safety for the consumer (larger than it is?) • More impact (company stands out)
- 17. 1. Identify a range of communication applications 2. Describe the use of internet telephony, including Voice over Internet Protocol (VoIP) 3. Evaluate the use of applications for public and corporate publications L/A: To identify common hardware components in a computer system and how they function My Learning Objectives Extension Task • Design your business card for Mr Jones
- 18. 1. Identify a range of communication applications 2. Describe the use of internet telephony, including Voice over Internet Protocol (VoIP) 3. Evaluate the use of applications for public and corporate publications L/A: To identify common hardware components in a computer system and how they function My Learning Objectives Plenary: Matching Task •Complete the matching activity in your booklets to show me what you’ve learned this lesson
- 19. • Identify a range of communication applications Must • Describe the use of internet telephony, including Voice over Internet Protocol (VoIP) Should • Evaluate the use of applications for public and corporate publications Could Let’s Review
- 20. 1. Identify a range of communication applications 2. Describe the use of internet telephony, including Voice over Internet Protocol (VoIP) 3. Evaluate the use of applications for public and corporate publications L/A: To identify common hardware components in a computer system and how they function My Learning Objectives Homework •None!