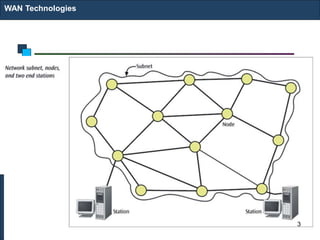
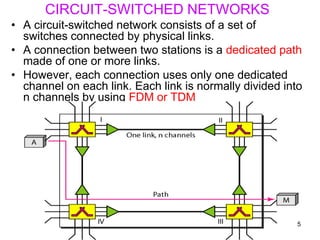
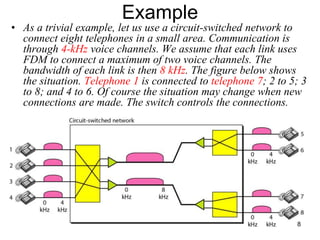
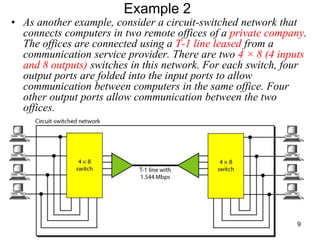
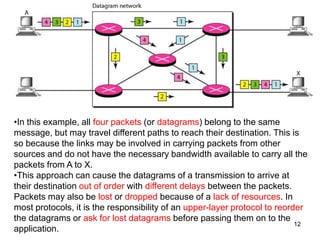
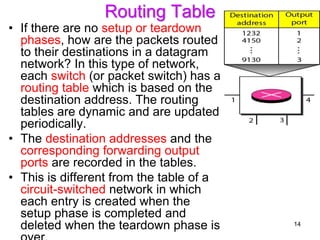
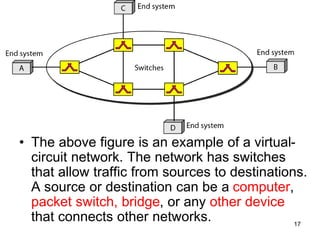
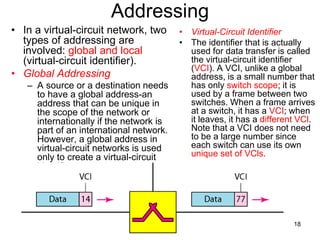
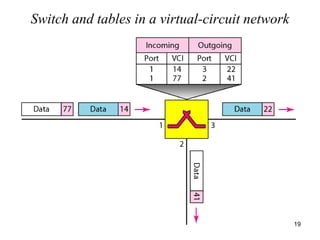
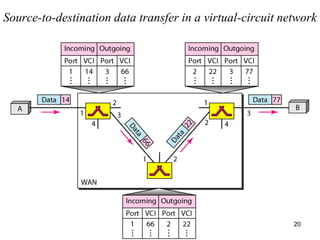
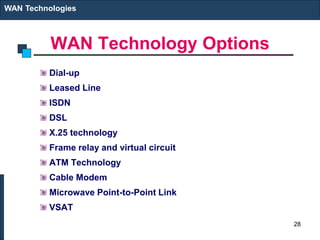
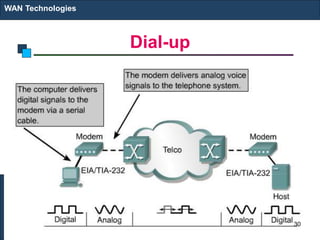
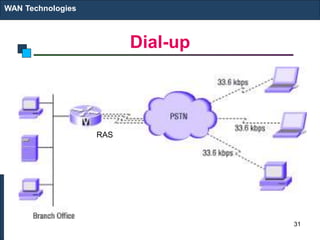
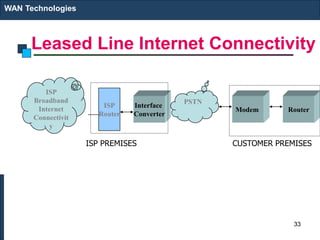
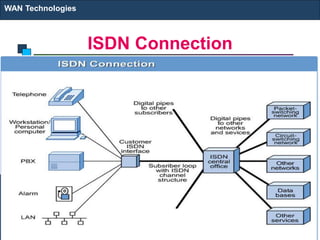
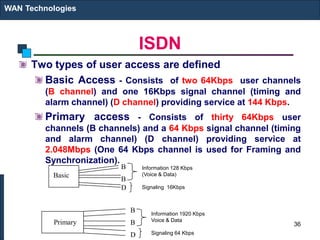
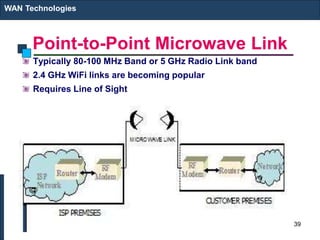
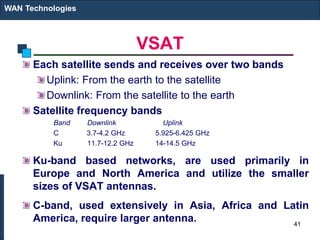
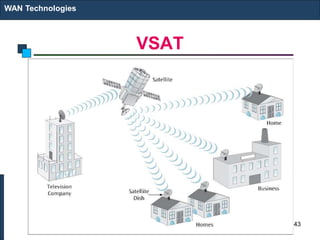
This document discusses wide area network (WAN) technologies. It begins by defining WAN characteristics such as interconnecting computers over long distances using various media. It then describes different WAN technologies including circuit-switched networks, packet-switched networks, and virtual circuit networks. Specific routing protocols and concepts are explained like distance vector routing, link state routing, static versus dynamic routing. The document concludes by listing various WAN technology options for connecting sites like dial-up, leased lines, frame relay, ATM, microwave links and satellite.